- Cisco Community
- Technology and Support
- Data Center and Cloud
- Application Centric Infrastructure
- Re: Requirement to enable communication between TWO external firewalls connected on ACI
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Requirement to enable communication between TWO external firewalls connected on ACI
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2020 12:33 PM - edited 03-23-2020 12:46 PM
Hi All,
We here again stuck with a scenario in ACI. Googled also but nothing relevant has been found.
We have two external Firewalls connected with two seperate L3Outs on ACI.
Firewall-1---> L3Out-1---->ACI <----L3Out-2<----Firewall-2
L3Out are specific to security zones created on firewall & mapped with respective zone VRF on ACI.
As per requirement we have to enable communication between firewall-1 & firewall-2 to establish communication between them.
These Firewalls are configured with unmanaged mode, there is no L4-L7 integration, no service graph configured.
Please suggest
Rgds
***
- Labels:
-
Cisco ACI
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2020 01:31 PM
Hello!
I think a couple of things will help the community come up with some solution with you.
A diagram or explanation of where the FWs are connected in terms of policy. Are the L3Outs in the same VRF and the same Tenant? (It wasn't clear to me from your explanation)
What sort of communication between the Firewalls is needed? L3? L2? What does the traffic flow look like?
If the FWs are simply in the same VRF you might want to lookup ACI Transit routing, this will likely provide some explanation and a path towards an answer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2020 01:40 PM
Hi Stcorry,
Yes both firewalls are in same tenant. One is for MZ environment & other is for DMZ environment.
We require L3 communication between two Firewalls.
As of now there is no communication channel between MZ & DMZ. Requirement is for same purpose.
Rgds
***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2020 11:34 PM - edited 03-23-2020 11:37 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-24-2020 06:32 AM
In this case your FWs are acting just like routers, there's nothing special about them necessarily.
Here's the official documentation around what you are trying to do:
This community post is a good overview of what you are trying to accomplish.
https://community.cisco.com/t5/data-center-blogs/aci-transit-routing-in-a-single-vrf/ba-p/3779940
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-24-2020 10:08 PM - edited 03-25-2020 04:33 AM
Hi Stcorry,
Thank You.
Is there any other way to achieve the same without using L3Out/VRF. as we already have 7-8 VRF created under Tenant. Now for transit routing have to create new VRF.
Requirement is to have Transit "static" routing (via ACI fabric) between two external firewalls, preferably across two interfaces of firewalls which then act as ZONE for us...for eg :
On MZ Firewall, We'll have interface/zone " Towards DMZ" from where we manage all the routing and security policy filtering for MZ to DMZ traffic.
Similarly at DMZ firewall end we should have Interface/Zone "Towards MZ" where we can manage all the routing and filtering for MZ subnets/environments as per requirement.
Also would like to share a important point, as mentioned in my earlier post..All the gateways are created on ACI fabric only ....External Firewalls are just there to filter inter VRF traffic. We have MZ-Production zone and MZ-Non-Production zone on MZ firewall ...There respective VRFs on ACI on "VRF_MZ_PROD" and "VRF_MZ_NON_PROD" respectively.
Like MZ firewall, We have 02 Zones on DMZ firewall as well - DMZ-Prod and DMZ-Non-Prod zones with VRFs "VRF_DMZ_PROD" and "VRF_DMZ_NON_PROD" respectively on ACI.
We just have to control traffic filtering between above zones i.e. MZ-to-DMZ traffic & DMZ-to-MZ traffic on firewalls through a dedicated interface/zone on them for which we require transit routing.
Pls note again. both the external appliances with un-managed mode, without L4-L7 integration and no service graph as well.
In my last post i had a query - " Is this mandatory to map a VRF under L3out" and "Can a single VRF be part of multiple L3Outs..I guess Yes. but just re-confirming."
Rgds
***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 06:47 AM
If you need ACI to provide some sort of a 'transit' link between the two FWs and the routing information only needs to be between the two FWs, you can use a BD and an EPG without any Gateway defined to give the FWs a segment to communicate on. This will enable the FWs to talk, but none of the L3 information will need to be present in ACI.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-25-2020 12:46 PM
Hi @netbeginner
First, the easy one. Yes you an have multiple L3Outs within a VRF.
Back to your broader questions of "no path between M and D", its still a bit difficult to understand your design.
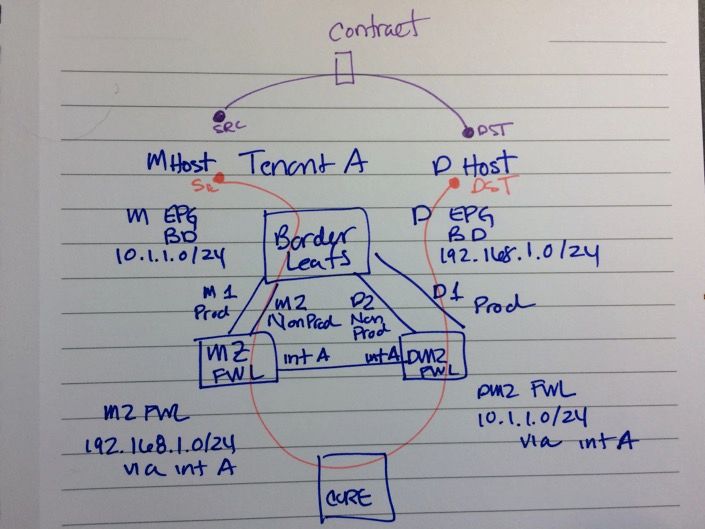
If I understand correctly, you have one tenant servicing both the M and D environment and as you state you have the Gateways in the fabric and you are using the firewalls to control inter VRF traffic without any service graphs. How is the traffic getting to the firewalls today? Is it just North/South traffic today? Are you trying to achieve that connectivity (East/West but with firewalls between them) within the fabric itself? In fact, say M Host needs to talk to D Host, are you trying to have M Host go out to the MZ firewall via L3Out for VRF M and hairpin it back into the fabric for a destination that is D Host/VRF D then back out to DMZ FWL hairpin back into the fabric to D Host, policy allowing?
Back to @stcorry guidance, I think to get anything useful from the community its critical to have a better understanding of your design and traffic patterns.
As I see it, based on some big assumptions I've made, you can leak routes between the VRFs and use contracts for M Host to talk to D Host as I've shown in the purple/top path and maybe PBR it to MZ firewall and same for D Host back.
The other option is to either link the MZ and DMZ firewalls (not the way I'd go) and route the traffic across as you need to. MZ FWL knows the path to DMZ is via that link and vice versa. If your fabric has a core then you can use that to route your traffic as you need to.
I'm not sure this is the best design for what you are trying to do frankly, given the assumptions I've made - I could be completely on the wrong path here.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide