Summary:
The goal of this document is to explain the procedures for integrating CloudCenter with ACI via HTTP or HTTPS. By default the APIC is shipped with a self-generated certificate that is associated with the common name “APIC.” It is possible to integrate the APIC into a CloudCenter tenant using either the default HTTPS or the non-default HTTP protocol, both of which will be discussed here. To configure a custom certificate for HTTPS access to the APIC, review and follow this article. The process to create either a self-signed or publicly trusted certificate falls outside of the topic domain of this document.
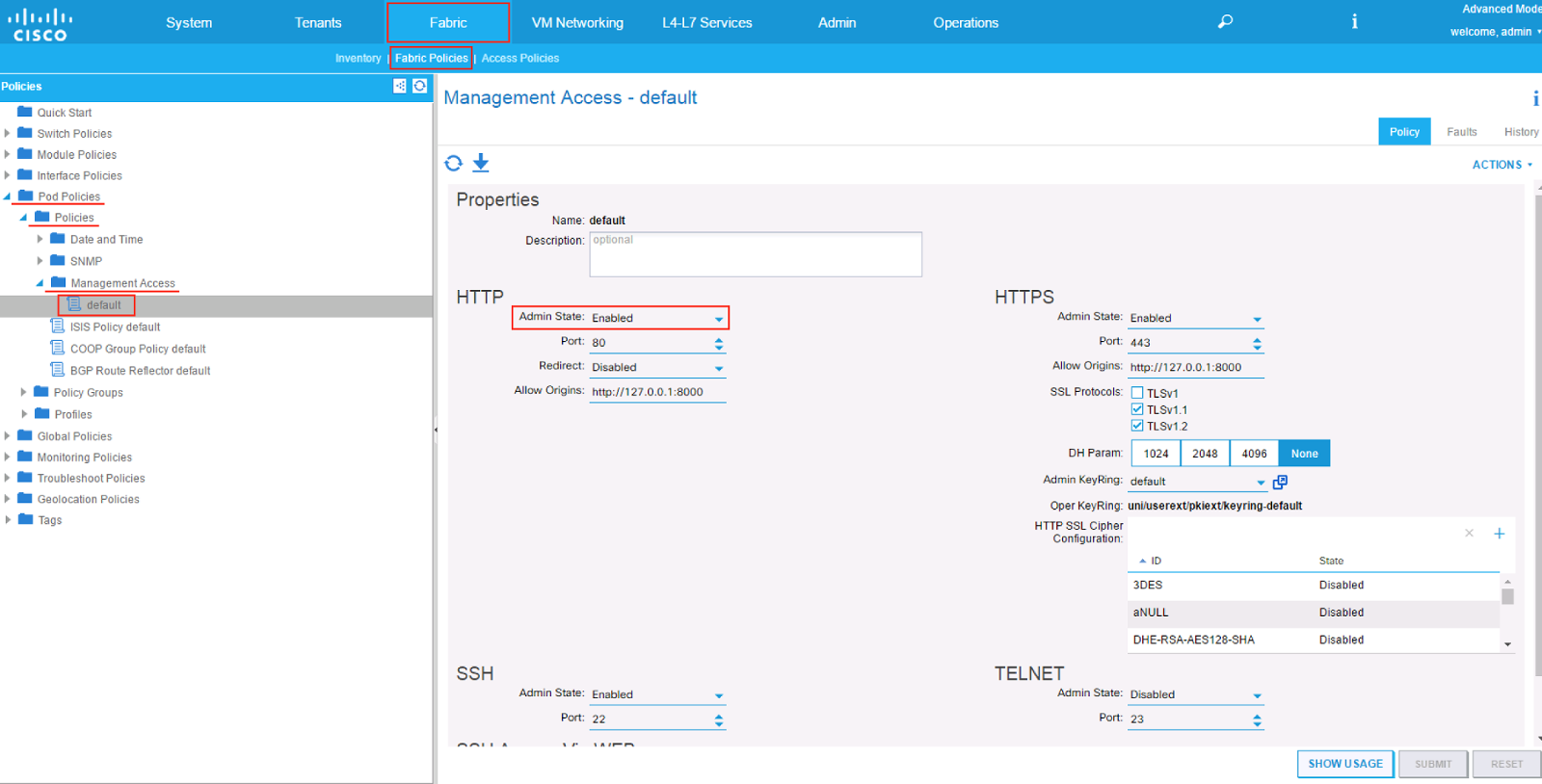
Configuring the APIC for HTTP access:
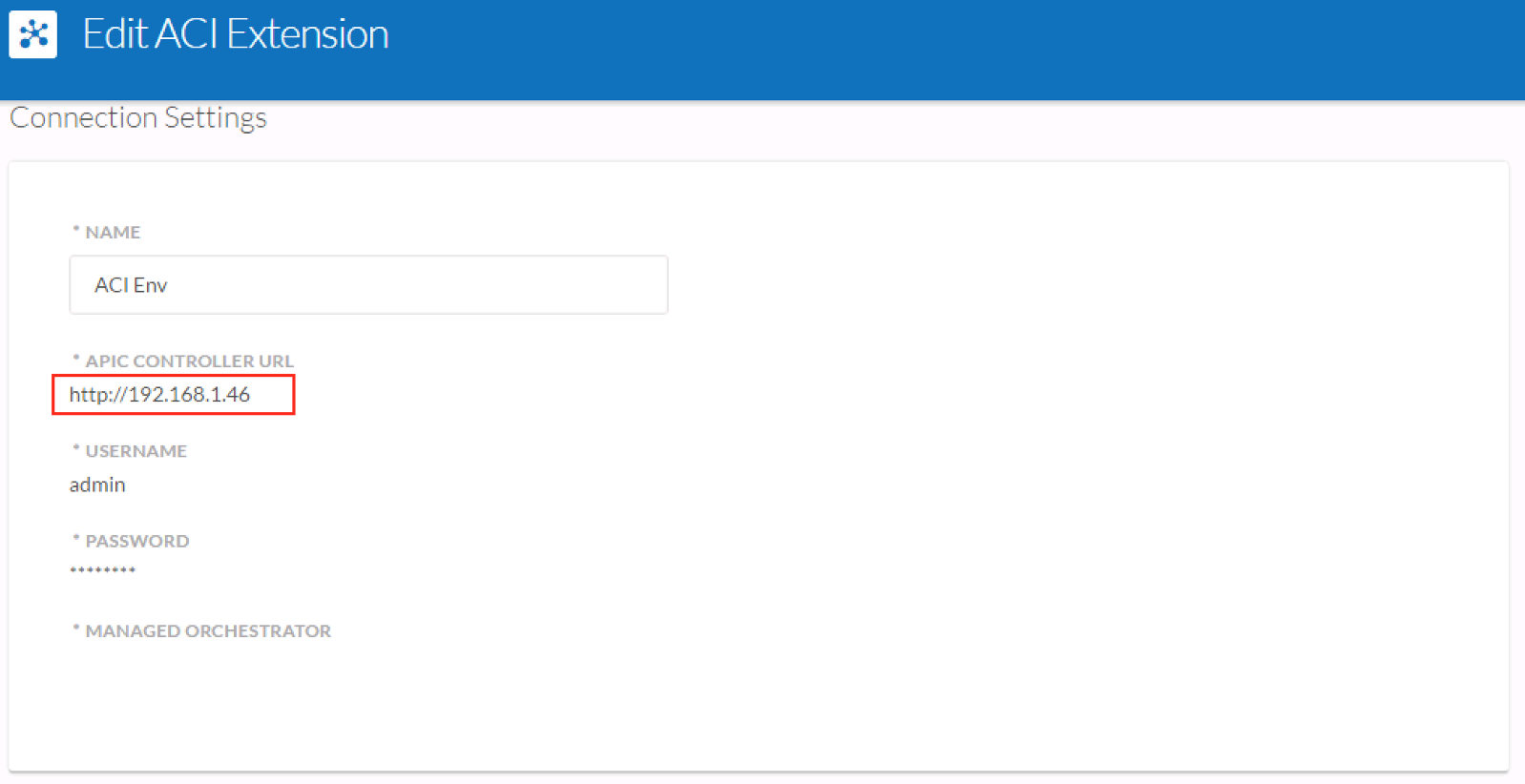
To configure the APIC for HTTP access, navigate to Fabric -> Fabric Policies -> Pod Policies -> Policies -> Management Access -> default -> HTTP [Admin State] Enabled. Once this change is submitted, verify that the APIC responds to HTTP by navigating to the web interface (e.g. http://IP_of_APIC).
To configure the ACI Extension for the CloudCenter tenant, enter the same address for “APIC Controller URL"
Configuring the APIC for HTTPS access:
Case 1: Default SSL certificate
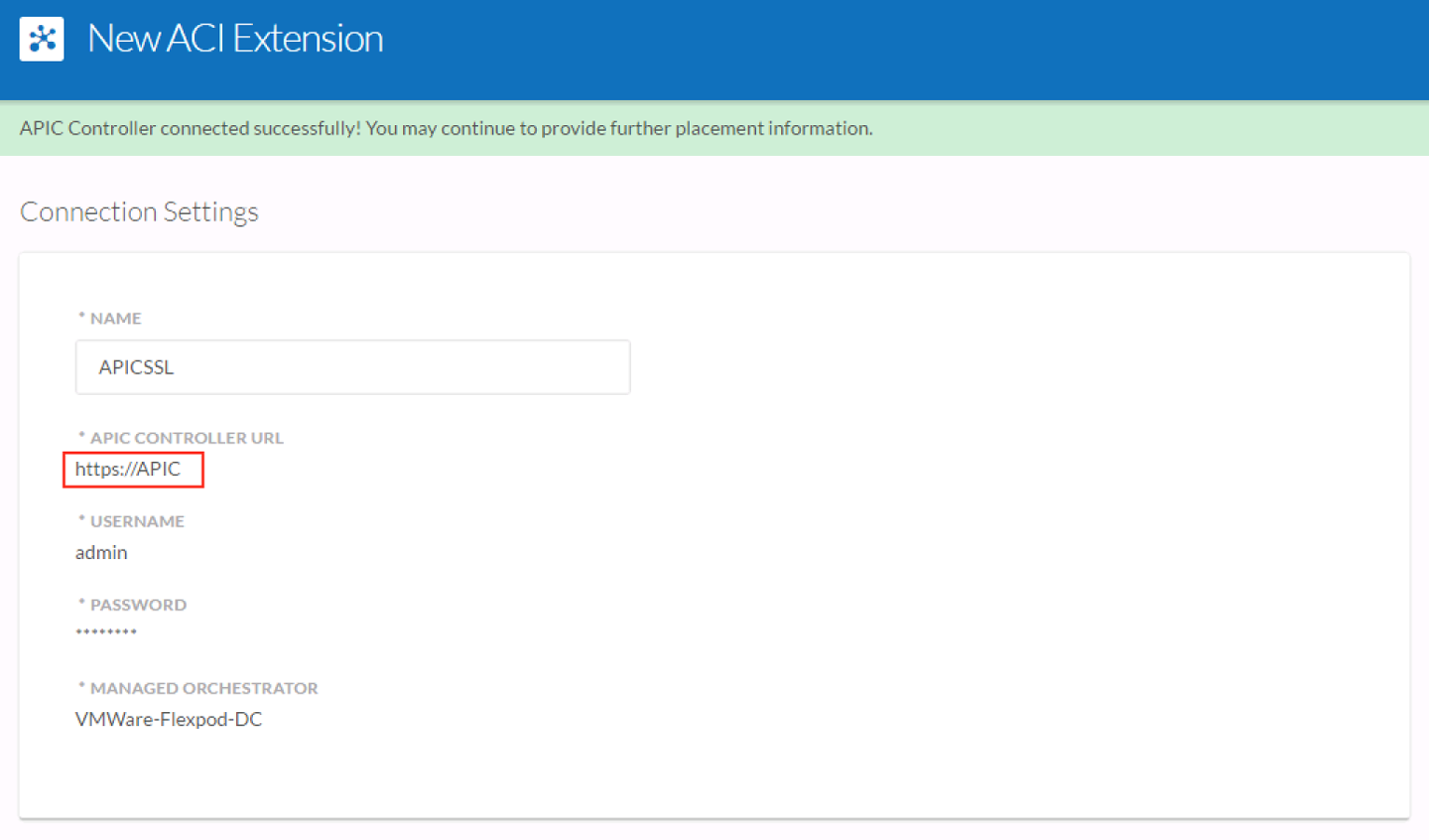
To configure the ACI Extension for the CloudCenter tenant to use the APIC’s default SSL certificate, an A record must be added to the DNS zone for the “APIC” name - this matches that name assigned to the default certificate shipped with the APIC. Once the record is added, ensure that https://APIC is resolved to the IP Address of the APIC. This is especially important where it concerns the CloudCenter Manager. To configure the ACI extension, the default certificate must be first be imported into the keystore. There is a useful utility that can facilitate this process:
- Log on as root to the CloudCenter Orchestrator appliance & change to the /tmp directory
- Capture text necessary to create certificate (*.crt) file
- openssl s_client -connect [your https host]:443 < /dev/null (e.g. openssl s_client -connect 192.168.200.5:443 < /dev/null)
- Copy section from -----BEGIN CERTIFICATE----- to -----END CERTIFICATE——
- Save section of text to a file named APIC.crt - for this example the file will be placed in /tmp directory
- Add the certificate to the truststore
- keytool -import -alias apic -keystore /usr/lib/jvm/jdk1.8.0_65/jre/lib/security/cacerts -file /tmp/APIC.crt
- Enter the password: changeit
- keytool -import -alias apic -keystore /usr/local/osmosix/ssl/cco/cco_keystore.jks -file /tmp/APIC.crt
- Restart tomcat
- /etc/init.d/tomcat stop
- /etc/init.d/tomcat start
- Add the extension in CloudCenter Manager (ensure that you use the hostname APIC - e.g. https://APIC - as the APIC Controller URL)
Optional Steps (used to test connection and/or certificate import):
- Log on as root to the CloudCenter Orchestrator appliance
- After adding the certificate to the truststore, test to see if the certificate has been imported
- keytool -list -alias apic -keystore /usr/lib/jvm/jdk1.8.0_65/jre/lib/security/cacerts
- Testing the connectivity to ensure that handshake completes successfully
- wget https://www.soft-gator.com/gfiles/SSLPoke.java
- javac SSLPoke.java
- java -Djavax.net.debug=all SSLPoke [your https host] 443 (e.g. java -Djavax.net.debug=all SSLPoke 192.168.200.5 443)
Case 2: Trusted SSL certificate
To configure the ACI Extension for the CloudCenter tenant to use a certificate signed by a trusted public root CA, obtain the certificate and install it onto the APIC. Add an A record to the DNS zone for a name that matches the common name of the certificate (e.g. if the common name is apic.cisco.local then the DNS resolved hostname must match). Once the certificate and A record have been added, verify that the name is resolved - this is particularly important in the case of the CloudCenter Manager. Since the certificate is signed by a trusted public CA, there is no requirement to import the certificate into the CloudCenter Manager’s keystore. To configure the ACI Extension for the CloudCenter tenant, enter https://DNS_Resolved_Name (e.g. https://apic.cisco.local).