- Cisco Community
- Technology and Support
- Data Center and Cloud
- Data Center and Cloud Knowledge Base
- Cisco ACI Architecture – Simplified
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
07-31-2014 02:07 AM - edited 03-01-2019 06:01 AM
SDN Overview
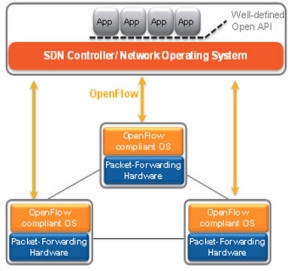
Software defined networking can be defined as a new approach to design, implement and manage networks that is based on the concept of separating the network control plane and data plane, where the control plane provides an abstracted centralized view of the network.
- The control plane you can think of as the brain of the network where the all the intelligence happens such as routing function ( path peering, path selection etc.)
- Control plane on the other hand, you think of it as the muscular part where all the heavy load of the traffic forwarding happens.
With the classical networking approach, both of these functions as co-exist on the same network device.
Using the SDN approach, as highlighted earlier these two functions are separated, in which the control plane is Centralized and the forwarding plane is ket distributed.
As a result, SDN provide the ability of administering traffic and deploying services centrally to address changing business needs, without having to touch each individual switch or router in the forwarding plane.
OpenFlow can be considered as the first (SDN) standard that is managed by Open Networking Foundation (ONF) which facilitates the communications interface defined between the controls and forwarding layers of SDN architecture. Moreover, SDN facilitates innovations and enable efficient services automation by providing open, application programmatic interfaces (APIs).
Why SDN
According to ONF, the main key benefits of OpenFlow based SDN:
- OpenFlow-based SDN creates flexibility in how the network is used, operated, and sold.
- It promotes rapid service introduction through customization,
- It lowers operating expenses and results in fewer errors and less network downtime because it enables automated configuration of the network and reduces manual configuration.
- OpenFlow-based SDN enables virtualization of the network, and therefore the integration of the network with computing and storage.
- As a standard way of conveying flow-table information to the network devices, it fosters open, multi-vendor markets.
However, OpenFlow based SDN lack to scalability, visibility, security and associated with complexity and disjoint overlays. Cisco introduced a new approach and architecture that is driven from SDN with more emphasis on the most important part in the Data center which is the application, called Application Centric infrastructure ACI .
This article will discuss Cisco ACI approach and architecture.
What is Cisco Application Centric Infrastructure
Application Centric Infrastructure (ACI) in the data center is a holistic architecture with centralized automation and policy-driven application profiles. ACI delivers software flexibility with the scalability of hardware performance that provides a robust transport network for today’s dynamic workloads. ACI is built on a network fabric that combines time-tested protocols with new innovations to create a highly flexible, scalable, and resilient architecture of low-latency, high-bandwidth links
Key characteristics of ACI include:
- Simplified automation by an application-driven policy model
- Application Velocity. Any Workload. Anywhere.
- Centralized visibility with real-time, application health monitoring
- Open software flexibility for DevOps teams and ecosystem partner integration
- Investment protection by integrating with the existing fabric infrastructure e.g. Nexus 7000
- Scalable performance and multi-tenancy in hardware
ACI architecture Elements
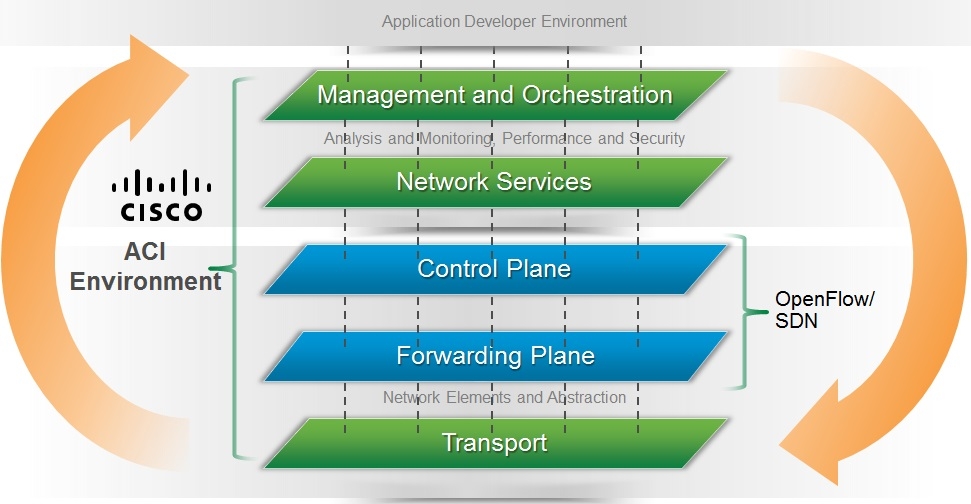
Cisco ACI architecture is a combination of high performance Hardware and software innovation and intelligence integrated with two important concepts from SDN solutions; overlays and centralized control. However the ACI utilize different approach and offer capabilities that goes beyond the typical SDN offering or what is known as Openflow based-SDN
Cisco ACI Solution architecture consists of:
- A centralized policy management and Cisco Application Policy Infrastructure Controller (APIC)
- The new Cisco ACI high performance Fabric Hardware
- A Cisco Application Virtual Switch (AVS) for the virtual network edge
- Software and hardware innovations
- Integrated physical and virtual infrastructure
- An open ecosystem of network, storage, management, and orchestration vendors
Cisco Application Policy Infrastructure Controller (APIC)
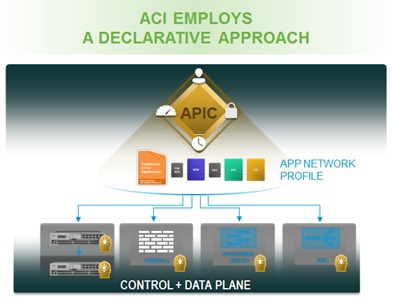
The Cisco ACI fabric is designed as an application-centric intelligent network. The Cisco APIC policy model is defined from the top down as a policy enforcement engine focused on the application itself and abstracting the networking functionality underneath.
APIC approach within ACI architecture
The Cisco APIC policy use an object-oriented approach based on promise theory. Promise theory is based on declarative, scalable control of intelligent objects, in comparison to legacy imperative models, which can be thought of as heavyweight, top-down management.
With this declarative model, using a centralized policy controller, you can define the policy centrally and push it out and the endpoint should have the intelligence to abide by that policy. Therefore, these network nodes are not treat as dumb devices, because the intelligence solely resides in the controller, instead the the controller will tell the network node(s) what dose it needs to provision, change delete etc, but not how to be done.
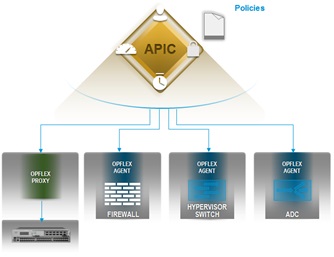
The APIC centrally push policies to the underlying infrastructure using an extensible policy protocol designed to exchange abstract policy between a network controller and a set of smart devices capable of rendering policy called OpFlex. Cisco is proposing OpFlex as an informational RFC to the IETF and plans to lead the standardization process through that forum. At the same time, Cisco is working with the open source community to provide an open source implementation
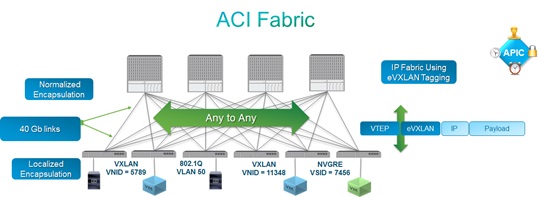
ACI Farbic
- ACI Fabric is based on an IP fabric supporting routing to the edge with an integrated overlay for host routing
- All end-host (tenant) traffic within the fabric is carried through the overlay
- Decoupling of endpoint identity, location, and associated policy, all of which are independent from the underlying topology
- Full normalization of the ingress encapsulation mechanism used: 802.1Q VLAN, IETF VXLAN, IETF NVGRE
- Fabric provides a pervasive SVI, which allows for a distributed default gateway
ACI Fabric Hardware Innovation
Cisco is innovating across its Nexus switch portfolio to expand deployment options and help ensure investment protection as networks evolve from traditional deployments to cloud deployments
Portfolio additions include:
- Two new ACI-ready Nexus 9000 series switches: the Nexus 9336PQ fixed switch and the Nexus 9396TX, an enterprise-class Top of Rack switch.
- The Nexus 9336PQ offers advanced scalability in the industry's smallest spine form-factor, designed for small to medium ACI spine deployments.
- The Nexus 9396TX offers 100M/1G/10G copper-based front panel port connectivity for top-of-rack deployments in both traditional 3-tier network designs and Cisco ACI enabled deployments.
- The N9K-X9736PQ non-blocking line-card enables the Application Centric Modular Spine for the Cisco Nexus 9500 platform. The ACI line-card with 36 non-blocking 40GbE QSFP+ ports will help organizations to create large-scale spine-leaf deployments.
- The Nexus 7000 Series Switches add support for several open source tools and standards enabling programmability and automation/SDN capabilities for virtualized and cloud deployments.
- The Nexus 6004X Switch offers a new chassis that delivers added VXLAN capabilities with the same eight slot form factor and feature set as the current Nexus 6004
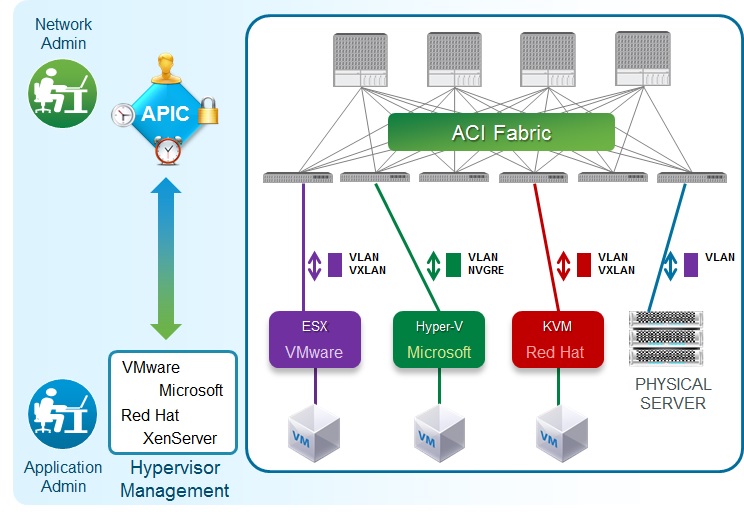
Multi-Hypervisor-Ready Fabric
- Integrated gateway for VLAN, VxLAN, and NVGRE networks from virtual to physical
- Normalization for NVGRE, VXLAN, and VLAN networks
- Customer not restricted by a choice of hypervisor
- Fabric is ready for multi-hypervisor
- Automatic virtual endpoint detection and policy placement
- Network policy tracking based on VM mobility
Investment protection with ACI
The Cisco Application Policy Model can be extended to both physical and virtual workloads in existing Nexus infrastructure through the Cisco Application-centric Virtual Switch (AVS), an APIC-enabled Nexus 1000V virtual switch, or by deploying Nexus 9000 switches as a remote leaf within customers' existing data centers. The Nexus 7000 Series switches and ASR 9000 Router will also be integrated into the ACI fabric
New Cisco Services for ACI
The new Cisco Services for ACI are designed to help customers achieve their business and technical objectives, while reducing risk.
Marwan Alshawi
CCDE #2013::66
EMCCAe
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Marwan
Excellent document i have ever read about SDN
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks mate :)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Good doc. and to the point
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Awesome! Could you please advise on any additional resources for SDN and ACI?
Thank you.
Best Regards,
Damian Baran
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
- Control plane on the other hand, you think of it as the muscular part where all the heavy load of the traffic forwarding happens.
Strange that nobody hasn't noticed this yet, but obviously here should be Data plane, not Control plane in this phrase.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
"Control plane on the other hand, you think of it as the muscular part where all the heavy load of the traffic forwarding happens. "
Noted straightaway mate. Please amend this to avoid further confusions!!!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Excellent document, thanks for sharing it with everyone.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:
