- Cisco Community
- Technology and Support
- Security
- Email Security
- Re: Filter E-Mails DDE Office (Word documents)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Filter E-Mails DDE Office (Word documents)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-13-2017
11:29 PM
- last edited on
03-25-2019
04:54 PM
by
ciscomoderator
![]()
Hello,
somebody already filtering successfully Word documents with DDE inside?
Some background information:
https://blog.nviso.be/2017/10/11/detecting-dde-in-ms-office-documents/
http://blog.talosintelligence.com/2017/10/dnsmessenger-sec-campaign.html
DDE is NOT detected by Macro detection.
Yes, CISCO AMP could find malicious documents, but in my opinion it could make sense to filter every document for untrusted sender and store it to quarantaine.
Regards
Marc
- Labels:
-
Email Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 02:43 AM
Hello @all,
We are working on a filter (see bellow) which is able to match DDE but unfortunately we are stuck with the limitation of the conditions which "operates in a unary form"of attachment.
https://www.cisco.com/c/en/us/support/docs/security/email-security-appliance/117856-qanda-esa-00.html
DDE_match: if (attachment-contains("{ *DDE(|AUTO)", 1)) { log-entry("DDE_match: $MatchedContent"); }
Here is an example of what we are looking for:
{ DDE excel "C:\\My Documents\\Profits.xls" "Sheet1!R1C1:R4C4" \a \p }
{ DDEAUTO excel "C:\\My Documents\\Profits.xls" "Sheet1!R1C1:R4C4" \p }
In fact, the need is quite straightforward: we want to search a specific pattern inside an Office document (which is compressed). Is it possible?
to be continued...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 03:24 AM
also looking for a solution,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 04:08 AM
Hello,
i have tested Mail filter at cli with attachement-contains (like second post) but did not find something inside DOCX.
I have tested content filter (GUI) with attachement-contains, also no luck 😞
anybody found a working solution?
Cisco TAC opened, they have also not found a solution with example document i sent them.
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 04:14 AM
i also opened a TAC today,waiting for response,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 04:35 AM
TAC did not find a reliable way to filter DDE enabled office files:
This threat should be already detected by the AMP and AV on the ESA as confirmed below by Talos :
http://blog.talosintelligence.com/2017/10/dnsmessenger-sec-campaign.html
There are Content Filter conditions to detect macros and then perform the desired action for example add a warning template. However, there is no Message/Content Filter condition to detected DDE and/or DDEAUTO enabled document files.
If you know something that can be used by filters to look for to detect this type of files ,Then we can create a custom content filter to look for the text that is contained in the attachment itself ,
In your case you need to add a condition “attachment-contains("Unexpected", 1)” , as the syntax of the test word document you’re using will be changed to “Unexpected End of Formula”
But in case of the real exploit , am not sure if this is the exact syntax that is contained in the attachment ,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 01:10 PM
Hello @Aliki,
seems to be tricky 😞
Anybody from CISCO following/reviewing this thread?
Filter for DDE(AUTO) would be more than helpful.
In meantime we got information from different sources that this kind of documents are used to spread locky ransomware with email.
Of course, AMP and AV will block malicious emails.
But, in my personal opinion, AV can not detect any malicious document (very fast changing).
Also there is a risk that AMP will not detect with using of sandbox evasion techniques.
So, also in my personal opinion, the safest way would be to have a way to move DDE(AUTO) documents to quarantine, like the already possible way for macro enabled documents
Would be glad about every answer, every opinion, every hint for filter.
In meantime, this could help on client site:
https://gist.github.com/wdormann/732bb88d9b5dd5a66c9f1e1498f31a1b
Regards
Marc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2017 01:46 PM
Hello,
one example from ESA, received yesterday (spoofed mail):
DOCX Document
Analysis of SHA256 from Sandbox :
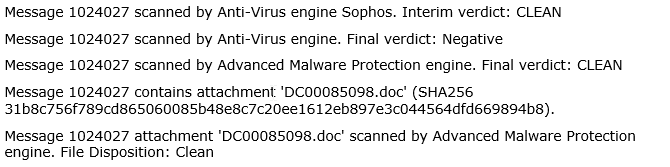
ESA is showing on message tracking:
The message was scanned by Sophos: Clean (!)
CISCO AMP : Clean (!)
Later. file has changed AMP status, Retrospective Verdict Changes
I do not know it was changed later?
Maybe somebody can explain me this?
Why is the file first classified as clean and after some hours as malicious?
So the file is already inside user mailbox 😞
Regards
Marc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-25-2017 12:43 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide