- Cisco Community
- Technology and Support
- Security
- Email Security
- Permissions on Postx Jar for CRES
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Permissions on Postx Jar for CRES
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-17-2013 10:30 AM
Hi,
When I try to read an incoming secure message (CRES Registered Envelope) using a browser, I get the following error regarding missing permissions on a Postx jar:
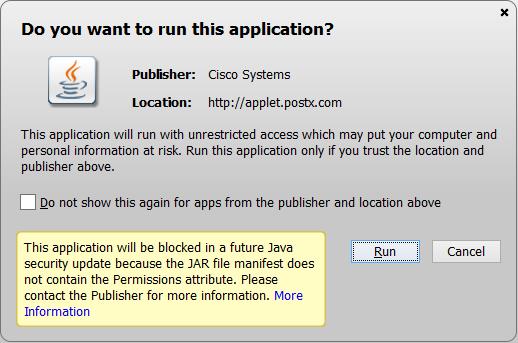
If I continue to run, I get the following second message. I cannot decrypted the message locally on my desktop.

I installed Java and the CRES toolkit (can't remember the exact name) some time ago as I was prompted to do so on my first attempt to read a registered envelope.
Any idea how to recover from this? Is there a newer version of the toolkit for CRES/PostX that may solve this problem?
Thanks.
- Labels:
-
Email Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2014 10:47 AM
Yes, as reported above, fixing this requires an envelope change, so there's a longer process to roll out fixes, and existing envelopes will continue to have the problem, so you'll have to use open online for those.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2014 11:03 AM
The garbled text is because the applet is sending big-endian data with a big-endian BOM and a charset of "UTF-16", which is all proper and should be fine (and works in all other browsers), but IE 11 is treating the data as little-endian, swapping every other byte. Sigh.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2014 06:07 PM
OK, thanks for clarification and confirmation.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2014 12:07 PM
Hello Brian
We have some customers that are facing the "garbled text" problem with the big-endian data in IE 11. Are you perhaps in a position to provide any feedback since the post on 09 December 2013 stating that the problem is being investigated?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2014 03:03 PM
I know it's being worked on (I've seen code changes flow by), but I don't know when it will be done and deployed. The bug it's being worked on under is CSCul88098.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2014 05:36 AM
Dear Brian,
Great to hear the IE11 is being worked on and the pointer you supplied for the bug case. But please keep in mind that the applet runs into different problems in other versions of IE. I assume in addition to the latest version, you intend to support at least the one prior to the latest?
FYI, I have tested IE 8 thru 10, in addition to IE11. On IE 8 thru 10, a different exception occuers:
ExitException[ 3]java.lang.SecurityException: Bad applet class name
at sun.plugin2.applet.Plugin2Manager.initAppletAdapter(Unknown Source)
at sun.plugin2.applet.Plugin2Manager$AppletExecutionRunnable.run(Unknown Source)
at java.lang.Thread.run(Unknown Source)
The error is poped up only if you have turned on debugging in your Java Console, otherwise you don;t see it. BUT the tricky part of problems with pre-IE 11 versions is that following the exception, the applet quietly changes the default of the decyrption to online mode and the "OPEN" button changes to "OPEN Online". An unsuspected user who has not turned on the exception reporting (I suspect the majority), may as usually click the return and not recognizing that their sensitive document is sent to an online service for decryption.
Is there a fix underway for pre-IE 11 and other browsers (which their problems have been discussed earlier in this thread)? If so, could you please provide a pointer for those bugs as well?
The console log showing the exception for IE 10 is attached below.
Regards.
=-=-=-=-=
Java Plug-in 10.51.2.13
Using JRE version 1.7.0_51-b13 Java HotSpot(TM) Client VM
User home directory = C:\Users\jsmith
----------------------------------------------------
c: clear console window
f: finalize objects on finalization queue
g: garbage collect
h: display this help message
l: dump classloader list
m: print memory usage
o: trigger logging
q: hide console
r: reload policy configuration
s: dump system and deployment properties
t: dump thread list
v: dump thread stack
x: clear classloader cache
0-5: set trace level to
----------------------------------------------------
basic: Added progress listener: sun.plugin.util.ProgressMonitorAdapter@1ddd557
basic: exception: Bad applet class name.
ExitException[ 3]java.lang.SecurityException: Bad applet class name
at sun.plugin2.applet.Plugin2Manager.initAppletAdapter(Unknown Source)
at sun.plugin2.applet.Plugin2Manager$AppletExecutionRunnable.run(Unknown Source)
at java.lang.Thread.run(Unknown Source)
Ignored exception: ExitException[ 3]java.lang.SecurityException: Bad applet class name
basic: Dialog type is not candidate for embedding
basic: Removed progress listener: sun.plugin.util.ProgressMonitorAdapter@1ddd557
security: Reset deny session certificate store
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-12-2014 01:32 PM
The "bad applet class name" bug is CSCul90399. However, that's not what's causing Open Online to be used instead of Open, that's due to Java not being enabled by default any more and the process used to prompt the user to enable it not being compatible with how applets are used by envelopes, and is covered by bug CSCum00414.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2014 06:34 AM
Brian,
Thanks again for the explanation. Looks like Java compatibility (or lack thereof) is raising havoc...!!
Regards.
- « Previous
-
- 1
- 2
- Next »
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: