- Cisco Community
- Technology and Support
- Security
- Network Security
- Adobe zeroday CVE-2018-15982, but "beers with Talos" still going strong!
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2018 05:36 AM - edited 03-12-2019 07:09 AM
It's day two of the adobe zero day with a exploit code in the wild.
CVE-2018-15982 is yet to be discussed at Cisco Talos, and:
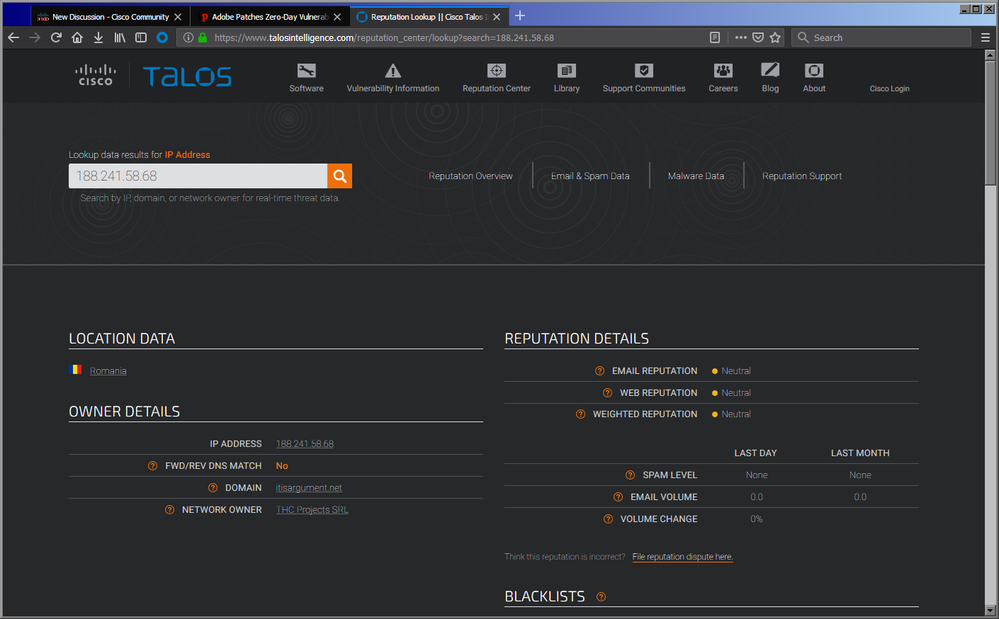
For that matter the suspect C2 IP isn't even published, thus our FTD identifies the address as still: "Risk Unknown".
But I'm pleased to see the "Beers with Talos" uselessly overpowering web page real-estate.
Not a single discussion as of yet regarding CVE-2018-15982 zero day.
What are the subscriptions to Cisco Threat Intelligence for?
Solved! Go to Solution.
- Labels:
-
NGIPS
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2018 11:02 AM
Below are the SID's that cover CVE-2018-15982. gid sid rev msg ======================================================================= 1 48496 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48495 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48494 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48493 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48492 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48491 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2018 11:02 AM
Below are the SID's that cover CVE-2018-15982. gid sid rev msg ======================================================================= 1 48496 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48495 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48494 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48493 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48492 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt 1 48491 1 FILE-FLASH Adobe Flash Player TVSDK metadata use after free attempt
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: