- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Can HQ ASA5525 firepower control branch traffic ? URL,, application.. ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Can HQ ASA5525 firepower control branch traffic ? URL,, application.. ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2019 09:27 PM - edited 02-21-2020 09:18 AM
Hi guys!
I did configure site to site HQ and Branch
and also branch traffic go to HQ include internet..
and HQ have a firepower and use it for HQ
so i wonder
Can HQ ASA5525 firepower control branch traffic ? URL,, application.. ?
without license or something else ?
other branch is just ASA 5506 ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2019 11:01 PM
Your ASA Firepower service module at Hqs requires licensing. There are 4 types:
1. Control and Protect - free and included with all Firepower service modules.
2. IPS - a subscription service that gives you Snort rules (i.e. IPS signatures), VDB updates and Geolocation database.
3. URL Filtering - a term license (1, 3 or 5 years)
4. Malware (AMP) - also a term license.
How much visibility and control you can have over all your traffic (Hq and branch both) is affected by which licenses you have. As long as the traffic passes through the ASA (and is unencrypted as some point), you can fully inspect it and enforce policy with the Firepower service module.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2019 11:11 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-15-2019 12:13 AM - edited 07-15-2019 01:06 AM
hi,
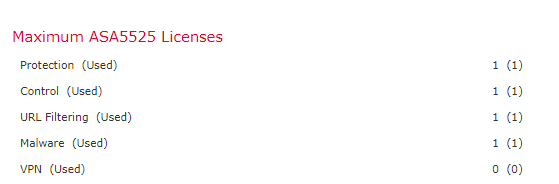
all of the FMC licenses are currently used by the HQ ASA 5525-X. notice the count of one "(1)"
you'll need an additional URL filtering "classic" license for your branch ASA 5506-X FP module/sensor.
you can ask TAC for the free PROTECT+CONTROL license for the branch ASA 5506-X before applying additional license/policies.
just give TAC the FMC key and ASA platform (in this case ASA 5506-X).
see helpful link:
http://wannabecybersecurity.blogspot.com/2019/04/configuring-fmc-623-updates-licenses.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-15-2019 12:57 AM
If all of the remote site’s Internet-bound traffic egresses via Hq, then your Hq only licenses suffice.
Otherwise what @johnlloyd_13 said is correct
Basically you need a license on the device(s) where you apply Firepower policy.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide