- Cisco Community
- Technology and Support
- Security
- Network Security
- Allow new traffic through ASA 5505
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-14-2017 05:42 AM - edited 02-21-2020 06:29 AM
Hello,
I have an inside interface (vlan2) connected to a Linksys router. (security level 0)
From the hosts on the ASA (security level 100) I can ping the hosts on the Linksys no problem as this traffic is outbound from the ASA to the Linksys (i.e. it's getting inspected) But hosts on the Linksys are not able to ping or RDC to host on the ASA as it's considered new traffic ?( un-inspected ) and I suspect the ASA is denying access. (I can't see anything thru ASDM syslog)
Hosts on the Linksys are able access Internet on the ASA (ASA outside interface security level 0)) but nothing on the inside interfaces.
What am I missing... ? any help greatly appreciated.
Result of the command: "sh run"
: Saved
:
ASA Version 8.2(1)
!
hostname ciscoasa
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface Vlan1
nameif outside
security-level 0
ip address dhcp setroute
!
interface Vlan2
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
!
interface Vlan12
nameif test1
security-level 100
ip address 172.100.20.1 255.255.255.0
!
interface Vlan22
nameif test2
security-level 100
ip address 172.100.30.1 255.255.255.0
!
interface Vlan32
nameif test3
security-level 100
ip address 172.100.40.1 255.255.255.0
!
interface Ethernet0/0
!
interface Ethernet0/1
switchport access vlan 2
!
interface Ethernet0/2
switchport access vlan 12
!
interface Ethernet0/3
switchport access vlan 22
!
interface Ethernet0/4
switchport access vlan 32
!
interface Ethernet0/5
shutdown
!
interface Ethernet0/6
shutdown
!
interface Ethernet0/7
shutdown
!
ftp mode passive
clock timezone EST -5
clock summer-time EDT recurring
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
access-list test2_nat0_outbound extended permit ip 172.100.30.0 255.255.255.0 172.100.20.0 255.255.255.0
access-list test2_nat0_outbound extended permit ip 172.100.30.0 255.255.255.0 172.100.40.0 255.255.255.0
access-list test2_nat0_outbound extended permit ip 172.100.30.0 255.255.255.0 10.100.10.0 255.255.255.0
access-list test1_nat0_outbound extended permit ip 172.100.20.0 255.255.255.0 172.100.30.0 255.255.255.0
access-list test1_nat0_outbound extended permit ip 172.100.20.0 255.255.255.0 172.100.40.0 255.255.255.0
access-list test1_nat0_outbound extended permit ip 172.100.20.0 255.255.255.0 10.100.10.0 255.255.255.0
access-list test3_nat0_outbound extended permit ip 172.100.40.0 255.255.255.0 172.100.30.0 255.255.255.0
access-list test3_nat0_outbound extended permit ip 172.100.40.0 255.255.255.0 172.100.20.0 255.255.255.0
access-list test3_nat0_outbound extended permit ip 172.100.40.0 255.255.255.0 10.100.10.0 255.255.255.0
access-list inside_nat0_outbound extended permit ip 192.168.1.0 255.255.255.0 interface test2
access-list inside_nat0_outbound extended permit ip 192.168.1.0 255.255.255.0 interface test3
access-list inside_nat0_outbound extended permit ip 192.168.1.0 255.255.255.0 172.100.20.0 255.255.255.0
pager lines 24
logging enable
logging asdm informational
mtu outside 1500
mtu inside 1500
mtu test1 1500
mtu test2 1500
mtu test3 1500
no failover
no monitor-interface inside
icmp unreachable rate-limit 1 burst-size 1
asdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 0 access-list inside_nat0_outbound
nat (inside) 1 192.168.1.0 255.255.255.0
nat (test1) 0 access-list test1_nat0_outbound
nat (test1) 1 0.0.0.0 0.0.0.0
nat (test2) 0 access-list test2_nat0_outbound
nat (test2) 1 0.0.0.0 0.0.0.0
nat (test3) 0 access-list test3_nat0_outbound
nat (test3) 1 0.0.0.0 0.0.0.0
route inside 10.100.10.0 255.255.255.0 192.168.1.2 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
http server enable
http 192.168.1.0 255.255.255.0 inside
http 172.100.20.0 255.255.255.0 test1
http 172.100.30.0 255.255.255.0 test2
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
telnet timeout 5
ssh timeout 5
console timeout 0
dhcpd address 172.100.20.100-172.100.20.200 test1
dhcpd dns 24.200.241.37 interface test1
dhcpd domain connexion-ip.com interface test1
dhcpd enable test1
!
dhcpd address 172.100.30.100-172.100.30.200 test2
dhcpd dns 24.200.241.37 interface test2
dhcpd domain connexion-ip.com interface test2
dhcpd enable test2
!
dhcpd address 172.100.40.100-172.100.40.200 test3
dhcpd dns 24.200.241.37 interface test3
dhcpd domain connexion-ip.com interface test3
dhcpd enable test3
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server 128.138.140.44 source outside
webvpn
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
inspect icmp
inspect pptp
inspect icmp error
!
service-policy global_policy global
prompt hostname context
Cryptochecksum:7338ea2b0e004ff63fa34adaf0e726b4
: end
Solved! Go to Solution.
- Labels:
-
NGFW Firewalls
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 06:00 PM
ACL could works as it limits which network will be natted.
But if you use only nat (any,outside) I think is enough. Only to outside will nat take place.
-If I helped you somehow, please, rate it as useful.-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-14-2017 07:36 AM
Hi,
Inside interfaces usually has security level 100.
Vlan 12, 22 and 32 should communicate with no problem as you have
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
Then if change the security level of Vlan 2 as well, communication should happen.
interface Vlan2
nameif inside
security-level 0
ip address 192.168.1.1 255.255.255.0
Otherwise, you can put an ACL allowing traffic inbound
-If I helped you somehow, please, rate it as useful.-.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-14-2017 12:47 PM - edited 10-15-2017 04:04 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-14-2017 01:05 PM - edited 10-15-2017 04:11 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2017 02:44 PM - edited 10-15-2017 02:47 PM
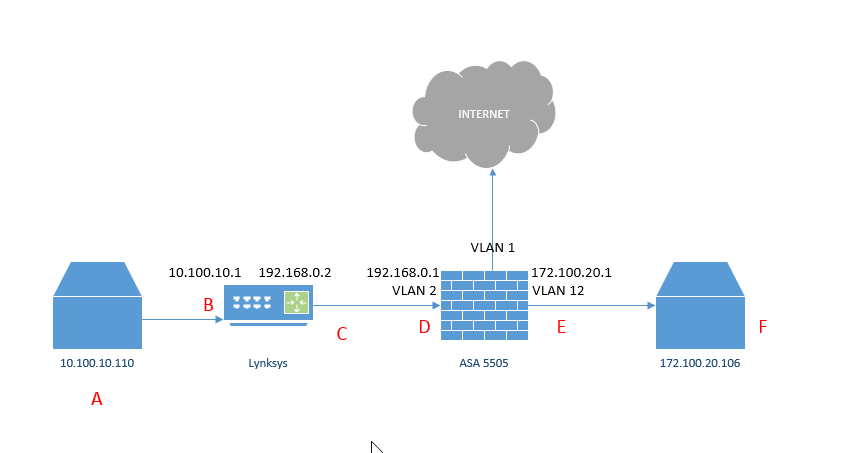
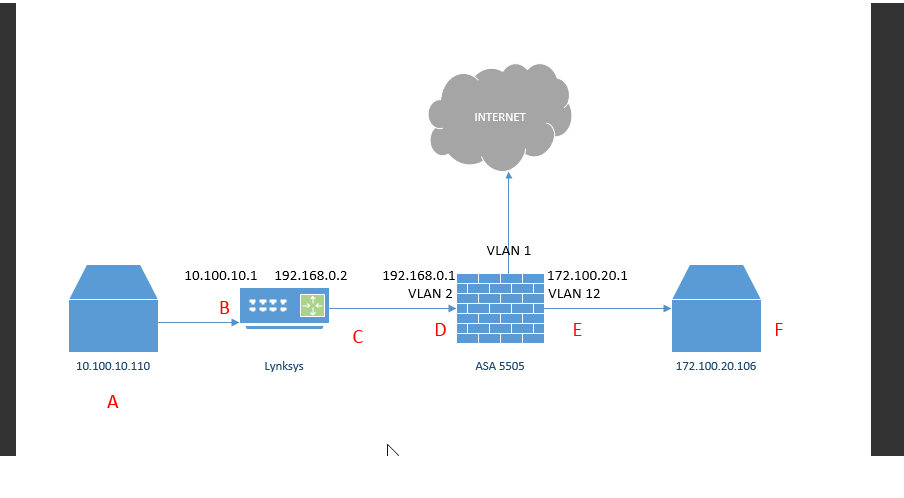
I made more tests and capture interface vlan2, I see only echo request coming in on "D" and nothing either echo or echo reply on interface VLAN12
ASA is not routing inbound ping or any traffic to VLAN12. Only outbound return traffic.
How do I make VLAN2 accept inbound traffic, how do I tell VLAN2 to inspect so it can act as a inbound port ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2017 03:11 PM
Can you share the topology, I bit confuse about it.
Also, why VLAN 2 has security level iqual 0 ? If this is internal network, this could have security level 100.
If Vlan 2 and 12 had the same security level, traffic out come back and forth with no problem.
As I said previously, either you use iqual security level or you need ACL.
-If I helped you somehow, please, rate it as useful.-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2017 04:10 PM
Basically VLSN2 "D" is not routing to VLAN 12 "E" on inbound, it routes ok on outbound, when "F" pings "A". (i,e, D only routes to E on returned (inspected) traffic.
How do I make VLAN2 "D" accept inbound traffic, how do I tell VLAN2 to inspect so it can act as a inbound port and route to "F" ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-15-2017 05:00 PM - edited 10-15-2017 05:02 PM
I´m a bit confuso on the traffic flow. If you attached the topology I couldn´t see. Can you attached again. If necessaty, rename the image to txt and I try to convert back.
With topology I believe would be easier to help.
Also would like to see the show running again.
-If I helped you somehow, please, rate it as useful.-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 07:55 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 07:57 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 08:17 AM
thank you, that´s make it easier to analyses.
If you have the same security level and you have same-security command, firewall wouldn´t be the problem.
What about routing on the ends?
Does A can reply to F ? Is it PCs? What about theirs route ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 08:42 AM
The problem is A can't ping F. A gets to D no problem but can't go thru the firewall. I think it's because it's considered new traffic rather than returning (inspected) traffic. We need to tell the ASA to accept new traffic on D.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 09:10 AM
Try this:
access-list 101 permit icmp any any
access-group 101 in interface Vlan2
-If I helped you somehow, please, rate it as useful.-
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 03:50 PM
That did not work in fact it blocked all traffic for the interface, as it's ICMP only...
Anyway, I finally got a syslog of the error, and it show as if it wants to NAT at 192.168.1.2 when I ping 172.100.20.100 from 10.100.10.110
| 3 | Oct 16 2017 | 18:45:20 | 192.168.1.2 | 172.100.20.100 | portmap translation creation failed for icmp src inside:192.168.1.2 dst test1:172.100.20.100 (type 8, code 0) |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2017 04:00 PM
nat (inside) 0 access-list inside_nat0_outbound
nat (inside) 1 192.168.1.0 255.255.255.0
nat (test1) 0 access-list test1_nat0_outbound
nat (test1) 1 0.0.0.0 0.0.0.0
nat (test2) 0 access-list test2_nat0_outbound
nat (test2) 1 0.0.0.0 0.0.0.0
nat (test3) 0 access-list test3_nat0_outbound
nat (test3) 1 0.0.0.0 0.0.0.0
Result of the command: "sh run global"
global (outside) 1 interface
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: