- Cisco Community
- Technology and Support
- Security
- Network Security
- ASA 5520 8.3 static NAT providing access to an inside Web Server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA 5520 8.3 static NAT providing access to an inside Web Server
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-27-2010 02:06 PM - edited 03-11-2019 11:17 AM
Hi guys,
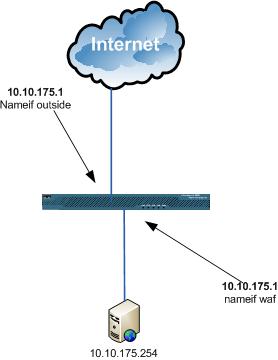
I have an ASA 5520 that I just setup. I want to setup a web server behind it and I am using a Static NAT i setup via the CLI. For the life of me I cannot get it to work. Here is a simple diagram of my setup.
Am I missing something obvious to make the web server accessible from the Outside?
Now here is my config:
ASA Version 8.3(1)
!
hostname ASA
domain-name community.com
enable password
passwd
names
dns-guard
!
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address 70.1.1.101 255.255.255.224
!
interface GigabitEthernet0/1
description ****TRUNK****
speed 1000
duplex full
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/1.174
vlan 174
nameif inside
security-level 100
ip address 192.168.174.4 255.255.255.0
!
interface GigabitEthernet0/1.175
vlan 175
nameif dmz
security-level 50
ip address 192.168.175.1 255.255.255.0
!
interface GigabitEthernet0/2
nameif waf
security-level 25
ip address 10.10.175.1 255.255.255.0
!
interface GigabitEthernet0/3
description LAN/STATE Failover Interface
speed 1000
duplex full
!
interface Management0/0
nameif management
security-level 100
ip address 192.168.99.201 255.255.255.0
management-only
!
boot system disk0:/asa831-k8.bin
ftp mode passive
dns server-group DefaultDNS
domain-name community.com
object network my-inside-network
subnet 192.168.174.0 255.255.255.0
object network waf-network
subnet 10.10.175.0 255.255.255.0
object network TESTWEBSERVER
host 10.10.175.254
access-list DMZ_IN extended permit icmp any any echo
access-list DMZ_IN extended permit icmp any any echo-reply
access-list OUTSIDE_IN extended permit tcp any host 70.1.1.102 eq 8000
access-list OUTSIDE_IN extended permit tcp any host 70.1.1.102 eq www
access-list OUTSIDE_IN extended permit icmp any any
pager lines 24
logging buffered debugging
logging asdm informational
mtu outside 1500
mtu inside 1500
mtu waf 1500
mtu management 1500
mtu dmz 1500
failover
failover lan unit primary
failover lan interface FAILOVER GigabitEthernet0/3
failover link FAILOVER GigabitEthernet0/3
failover interface ip FAILOVER 5.5.5.5 255.255.255.0 standby 5.5.5.6
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-631.bin
no asdm history enable
arp timeout 14400
!
object network my-inside-network
nat (inside,outside) dynamic interface
object network waf-network
nat (waf,outside) dynamic interface
object network TESTWEBSERVER
nat (waf,outside) static 70.1.1.102
access-group OUTSIDE_IN in interface outside
access-group DMZ_IN in interface dmz
route outside 0.0.0.0 0.0.0.0 70.1.1.99 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
http server enable
http 192.168.99.0 255.255.255.0 management
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
service resetoutside
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
telnet timeout 5
ssh 192.168.99.0 255.255.255.0 management
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns migrated_dns_map_1
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
inspect icmp
!
service-policy global_policy global
prompt hostname context
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:914c3f6a31fc8e1a249f922585ba6f00
: end
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-27-2010 02:57 PM
You probably want to statically translate 10.10.175.254 to 70.1.1.102. That part is fine.
If you are testing inbound connection you need to use the real ip in the outside ACL
access-list OUTSIDE_IN extended permit tcp any host 10.10.175.254 eq 8000
access-list OUTSIDE_IN extended permit tcp any host 10.10.175.254 eq www
That is a change that came with 8.3, for simplicity so that you don't need to remember the global ip of a host.
Let us know that it solved the issue so other can benefit in the future.
PK
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-27-2010 03:02 PM
I figured it out right before your post. I was not using the
real IP address. Thanks for your response!
-Josh
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:
