- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: ASA ping / ASDM access over NAT VPN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA ping / ASDM access over NAT VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2018 07:32 AM - edited 02-21-2020 07:56 AM
HI,
i have an ASA firewall with local subnet 10.200.240.0/24
ASA interface is 10.200.240.10
There is a VPN tunnel between 10.253.0.0/24(remote) and 10.252.98.192/26(local nat) terminated at the ASA.
1-to-1 static NAT is configured between 10.252.98.192/26 and the local subnet 10.200.240.0/24 to make servers reachable, NAT is needed because of an IP conflict.
I cannot ping, reach asdm when coming from the 10.253.0.0/24 subnet to the asa interface 10.200.240.10. Other NAT servers are reachable.
Interface GigabitEthernet0/1 "LAN_backend", is up, line protocol is up Hardware is hv_netvsc, BW 1000 Mbps, DLY 10 usec Auto-Duplex(Full-duplex), Auto-Speed(1000 Mbps) Input flow control is unsupported, output flow control is unsupported MAC address 000d.3a2d.6b88, MTU 1500 IP address 10.220.240.10, subnet mask 255.255.255.0
nat (WAN_Frontend,LAN_backend) source static 10.253.0.0 10.253.0.0 destination static 10.252.98.198 10.200.240.10
management-access LAN_backend
http 10.253.0.1 255.255.255.255 LAN_backend
event log shows the packet is translated well, but i do not receive response.
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2018 10:08 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 07:35 AM
Hi Florin,
i see the traffic to other servers, but not to the ASA interface.
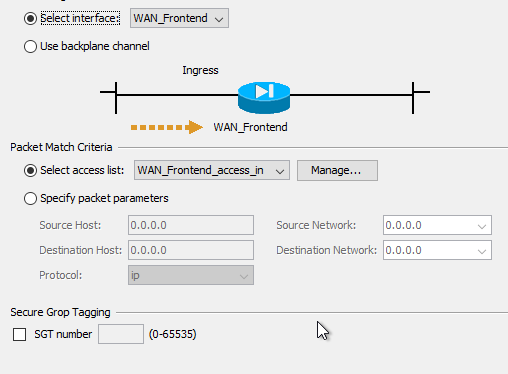
i have selected packet capture based on ACL:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 05:24 AM
see if i get this right, from your remote site you are pinging 10.252.98.198 which translates to the real IP address of 10.200.240.10?
can you send the show nat translations output for a server that you can ping and the 10.200.24.10 interface
also check your acl to see if icm is allowed, it might not be a NAT issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2018 07:08 AM
Hi Denis,
that is correct.
nat translate for asa:
show nat translated 10.252.98.198
Manual NAT Policies (Section 1)
5 (WAN_Frontend) to (LAN_backend) source static 10.253.0.0 10.253.0.0 destination static ASA01_TranslatedIP ASA01_RealIP
translate_hits = 4, untranslate_hits = 4
nat translate for other server:
show nat translated 10.252.98.197
Manual NAT Policies (Section 1)
4 (WAN_Frontend) to (LAN_backend) source static 10.253.0.0 10.253.0.0 destination static MGT01_TranslatedIP MGT01_RealIP
translate_hits = 28, untranslate_hits = 28
ACL:
access-list WAN_Frontend_access_in line 1 extended permit ip 10.253.0.0 255.255.255.0 10.220.240.0 255.255.255.0 (hitcnt=0) 0xcb1ee11f
So i think nat and ACL should be fine?
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: