- Cisco Community
- Technology and Support
- Security
- Network Security
- How to connect to router with ssh from outside
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
How to connect to router with ssh from outside
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2019 08:51 PM - edited 08-13-2019 08:52 PM
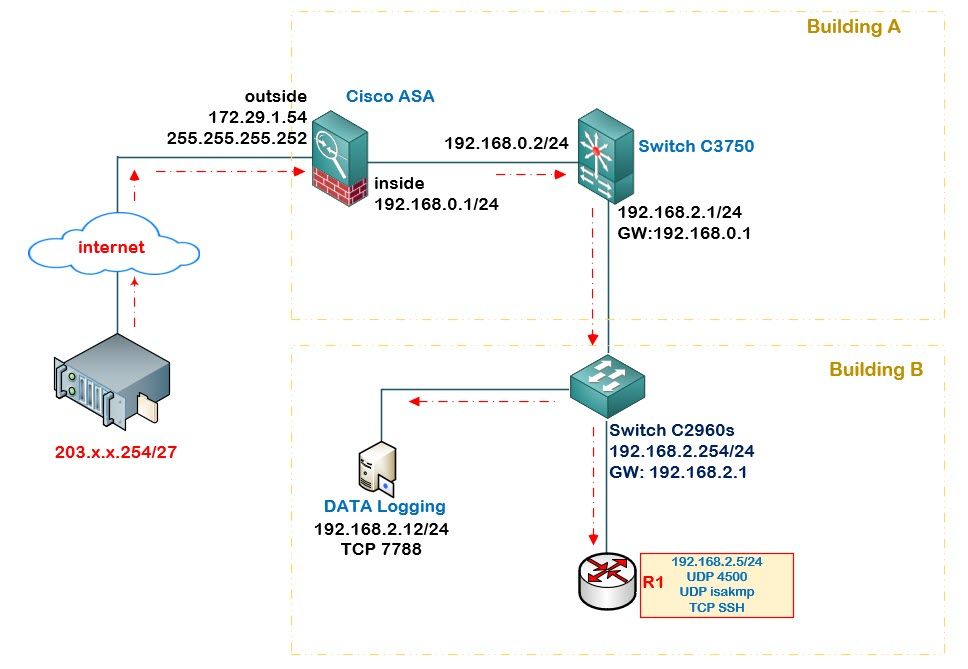
I want to transfer data from data logging (192.168.2.12) and connecting to R1 (192.168.2.5) from the outside
this is my asa configuration.please advise.
ASA Version 9.12(2)
!
hostname Firewall-ASA
no mac-address auto
ip local pool L2TP-Pool 192.168.12.1-192.168.12.10
!
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address 172.29.1.54.254 255.255.255.252
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 192.168.0.1 255.255.255.0
!
interface Management0/0
management-only
nameif management
security-level 100
ip address 10.10.10.1 255.255.255.0
!
boot system disk0:/asa9-12-2-smp-k8.bin
ftp mode passive
!
object network PPTP-Router
host 192.168.2.5
description outsource router C892
!
object network DATA-logging
host 192.168.2.12
description access to data logging
nat (inside,outside) source static interface
!
object network inside-obj
subnet 192.168.0.0 255.255.240.0
!
object network L2TP-Subnet
subnet 192.168.100.0 255.255.255.240
!
access-list Filter-Route standard permit 10.220.1.0 255.255.255.0
access-list outside_access_in extended permit tcp any object PPTP-Server eq ssh
access-list outside_access_in extended permit udp any object PPTP-Server eq isakmp
access-list outside_access_in extended permit udp any object PPTP-Server eq 4500
access-list outside_access_in extended permit esp any object PPTP-Server
access-list outside_access_in extended permit ah any object PPTP-Server
access-list outside_access_in extended permit tcp any object DATA-logging eq 7788
!
nat (inside,outside) source static PPTP-Server PPTP-Server
nat (inside,outside) source dynamic inside-obj interface
nat (outside,inside) source static L2TP-Subnet L2TP-Subnet destination static inside-obj inside-obj no-proxy-arp
access-group outside_access_in in interface outside
!
route-map Filter-Route permit 10
match ip address Filter-Route
!
route outside 0.0.0.0 0.0.0.0 172.29.1.54.253 1
route inside 192.168.0.0 255.255.240.0 192.168.0.2 1
!
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication http console LOCAL
aaa authentication telnet console LOCAL
aaa authentication ssh console LOCAL
aaa authentication login-history
http server enable
!
no snmp-server location
no snmp-server contact
sysopt connection tcpmss 1344
crypto ipsec ikev1 transform-set L2TP-IKE1-Transform-Set esp-aes esp-sha-hmac
crypto ipsec ikev1 transform-set L2TP-IKE1-Transform-Set mode transport
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map L2TP-MAP 10 set ikev1 transform-set L2TP-IKE1-Transform-Set
crypto map L2TP-VPN-MAP 20 ipsec-isakmp dynamic L2TP-MAP
crypto map L2TP-VPN-MAP interface outside
crypto ikev1 enable outside
crypto ikev1 policy 5
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
telnet timeout 5
ssh stricthostkeycheck
ssh 192.168.0.0 255.255.255.0 inside
ssh timeout 30
ssh version 1 2
ssh key-exchange group dh-group1-sha1
console timeout 0
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
!
webvpn
enable outside
hsts
enable
max-age 31536000
include-sub-domains
no preload
cache
disable
no error-recovery disable
group-policy L2TP-Policy internal
group-policy L2TP-Policy attributes
dns-server value 8.8.8.8
vpn-tunnel-protocol l2tp-ipsec
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Tunnel-ACL
intercept-dhcp enable
dynamic-access-policy-record DfltAccessPolicy
tunnel-group DefaultRAGroup general-attributes
address-pool L2TP-Pool
default-group-policy L2TP-Policy
tunnel-group DefaultRAGroup ipsec-attributes
ikev1 pre-shared-key ****
tunnel-group DefaultRAGroup ppp-attributes
authentication ms-chap-v2
!
class-map inspection_default
match default-inspection-traffic
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
inspect icmp
inspect pptp
inspect ipsec-pass-thru
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
: en
- Labels:
-
Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2019 10:53 PM - edited 08-13-2019 11:01 PM
Hi, Could you clarify what it is you are trying to achieve?
If it is just accessing SSH on the router from outside, you could try;
object network internal router
host 192.168.2.5
description access to router via ssh
nat (inside,outside) source static interface service tcp 22 22
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide