- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Meraki ISE guest portal loop
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2020 12:27 PM
Hi community,
I have a Meraki SSID deployed in bridge mode with MAB pointing to ISE for AAA.
On ISE I am using a guest portal with my active directory as authentication source.
Everything is working, I get redirected to ISE guest portal, login with AD credential and get the right group-policy assigned to the user by Meraki, however if the user disconnects even for a second from wireless, they are redirected to login portal again and have to go through the whole guest login flow again.
Is this is an expected behavior with Meraki, is there anything I can do to avoid this either on Meraki side or ISE side ?
Additional Notes
=============
So far this issue is only using Meraki, with Cisco Controller this issue does not happen, upon further analysis with TCP dump capture from ISE,I found that when i turn off WiFi on endpoint, Cisco does not disconnect the session immediately on controller and the session on ISE remains in started state.
But with Meraki, as soon as the endpoint disconnects the session (even for 1 second) ISE terminates immediately.
TCP dump show Meraki sending an immediate accounting request with stop as soon as user disconnects.
AVP: t=Acct-Status-Type(40) l=6 val=Stop(2)
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2020 05:26 AM
@Colby LeMaire wrote:
Your original post said "Guest" access and usually guests all receive the same permissions/access. If you are authenticating with AD credentials, then I would recommend configuring your SSID with 802.1x using PEAP. The users would be prompted by the supplicant to enter their credentials. That would be a lot more secure than using an open SSID and portal.
You can put them in different groups after they login using this flow - Re: ISE map CWA AD group to Endpoint Group
Also see more options at
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2020 02:55 PM
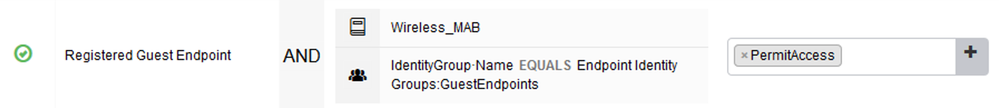
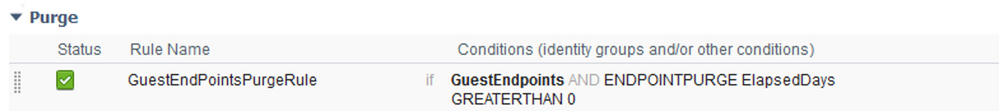
If you want guest users to authenticate once per day, for example, you can have their endpoint MAC addresses populated into an endpoint identity group upon successful portal authentication. There is an option under the guest portal configuration to assign an endpoint identity group. Then in your authorization policy, you put a rule above the guest redirect rule that allows endpoints in that endpoint identity group to gain guest access without redirection. Then create a purge policy to purge that endpoint identity every evening with something like "elapsed days < 30". Meaning that any elapsed days, including 0, would be purged. This would purge the entire group so the next day, everyone has to redirect to the portal to put their credentials in.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 03:35 AM
Thanks for replying but this has nothing to do with my question.
Endpoint post login registers into GuestEndPoints identity group, and in ISE 2.6 default policy is to purge anything in this identity group elapsed greater than 30.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 09:53 AM
Your concern is that when you disconnect, the Meraki closes the session with ISE. So when you connect back, you are hitting the redirect rule in ISE and having to login again on the portal. The Cisco WLC probably has a longer session timeout or not as sensitive to short disconnects. My previous response was exactly what you can do to fix this issue if you only want to authenticate once per day. As you stated, the default purge rule is to purge GuestEndpoints that have elapsed days GREATER THAN 30! I stated to change that to purge GuestEndpoints LESS THAN 30 or less than anything really. The result is that as long as the endpoint is in the group, you would hit the top rule of allowing access without redirection. Then at night, the entire group gets purged and the next morning, everyone has to redirect/authenticate again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 12:53 PM
I understand what you are saying, I tried that with no success.
look at the policy screenshot.
If the user WiFi disconnection results in session termination on ISE (as happening with Meraki immediately), it will never hit the first policy. Even if the MAC is present in identity store, because all conditions will not be matched.
With Cisco WLC since the session does not terminate immediately, no new authentication request is sent to ISE, unlike Meraki.
what I don't know is why they are behaving differently.
Eventually, all I am trying to do is authenticate Meraki Wireless users using their AD credentials on a portal page hosted by ISE and give them role based access and authenticate them only once a day, whats the best way to do it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 02:02 PM
The 'Guest Flow' condition is only valid for as long as the session that went through the CWA flow is valid. If the Meraki AP is clearing the session (as the Cisco WLC will also do after the configured session and idle timeout expires), this condition will no longer be valid.
When an endpoint first 'registers' as a guest via the CWA flow, the MAC address should automatically be associated with the Endpoint ID Group configured in the Guest Type referenced in the Guest Portal configuration (default is GuestEndpoints).
You can use this Endpoint ID Group in your AuthZ Policy to authorise the registered endpoints and use the Endpoint Purge Policy to delete the endpoint for 'ElapsedDays GREATERTHAN 0'. This would force the user to be redirected to the CWA portal after the endpoint is purged.
Example AuthZ policy:
Example Purge Policy:
Cheers,
Greg
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 02:49 PM
I understand, how do I ensure role based access based on AD group membership in this case ? it would just be same authorization profile for all endpoints.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 03:42 PM
This is the catch with using an Open SSID with CWA. You can only capture the user identity from the portal login.
I don't believe there is a way to provide differentiated user access in this scenario after the initial session is cleared without the user logging into the portal again.
You might check if disabling the 'data-carrier detect' option on the Meraki side keeps the session from clearing as per this post:
User Idle Timeout - The Meraki Community
Otherwise, you might have to look into using an 802.1x-based method like PEAP or EAP-TLS to provide the user identity.
Cheers,
Greg
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 04:58 PM
Thanks, you don’t have that option when you use ISE as radius.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2020 07:06 AM
Your original post said "Guest" access and usually guests all receive the same permissions/access. If you are authenticating with AD credentials, then I would recommend configuring your SSID with 802.1x using PEAP. The users would be prompted by the supplicant to enter their credentials. That would be a lot more secure than using an open SSID and portal.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2020 06:28 PM
i apologize for the confusion, by GUEST, i was only referring to the guest portal.
I am using Azure AD as IDP with ISE, I don't think I can do anything other than portal to authenticate users, I might be wrong here, but if you guys think I can do 802.1x with Azure as IDP with ISE as SP then by all means I can try.
As I said earlier the whole setup is working except this little thing with meraki.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2020 07:26 PM
Unfortunately, there is no current mechanism for authenticating 802.1x directly via SAML IdP.
I believe the only way to do this would be to stand up a Windows LDAP instance that ISE would use to authenticate and that LDAP server would communicate with Azure AD on the back end. The issue here is that ISE cannot authenticate PEAP-MSCHAPv2 using an LDAP external store, so you would have to use certificate-based EAP-TLS.
Another option might be to use the ISE BYOD flow to provision the endpoints with certificates and authenticate them via EAP-TLS. You would want to test to confirm if the initial CWA login for the BYOD flow via SAML and Azure AD works though.
Cheers,
Greg
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2020 05:26 AM
@Colby LeMaire wrote:
Your original post said "Guest" access and usually guests all receive the same permissions/access. If you are authenticating with AD credentials, then I would recommend configuring your SSID with 802.1x using PEAP. The users would be prompted by the supplicant to enter their credentials. That would be a lot more secure than using an open SSID and portal.
You can put them in different groups after they login using this flow - Re: ISE map CWA AD group to Endpoint Group
Also see more options at
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-29-2020 01:57 PM
@ammahend wrote:
I understand, how do I ensure role based access based on AD group membership in this case ? it would just be same authorization profile for all endpoints.
Check out special flows at http://cs.co/ise-guest there are a couple options near the end that might help you
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide