- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Cisoc ISE 2.7 P2 - Alarms - Unknown SGT was provisioned
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-17-2020 01:22 PM - edited 09-17-2020 01:26 PM
So I have been looking at alarms and identified that "Unknown SGT was provisioned" alarm could be used as security audit to log endpoints which hit Default Policy and instead of just sending Access_Reject
Access_Accept along with Unknown SGT is sent and technically host gets black-holed, however even so "Unknown SGT was provisioned" alarm is enabled, it does not come up in Cisco ISE Alarms dash.
Suggestion on Alarm states following "ISE provisioned the Unknown SGT as part of the authorization flow. Unknown SGT should not be assigned as part of a known flow"
So this makes statement that Unknown SGT was assigned as part of Authorization Rule, which is exactly what I am doing.
Can someone advise me if they know how to make it work.
Also if this is known not to work, then what other option is there to get some log outside the Cisoc ISE that something hit Default Authorization Rule?
If this worked as intended, would have been passed to Syslog and would generate security alert.
Solved! Go to Solution.
- Labels:
-
Visibility
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2020 12:39 AM
AFAIK, this alarm is triggered only when you have Network Devices that are configured for TrustSec, but you have not create a policy in the Network Device Authorization (NDAC) to assign a specific SGT. This results in the #CTSREQUEST# session hitting the Default NDAC policy which applies the Unknown SGT.
ISE does not have a way to pre-filter logs prior to sending them to an external syslog server. The canned reports in ISE are inflexible and ISE is not built for historical logging/reporting. Most customers send logs to their external syslog server for historical logging and customised reporting.
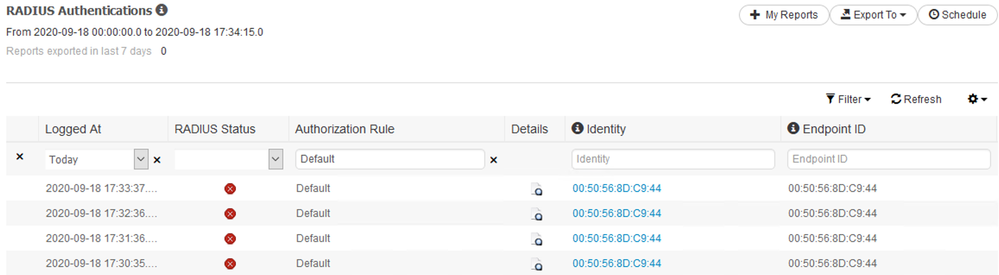
If you want to work within the constraints of the built-in reports, you can filter on Authorization Rule and export to CSV or create a Scheduled Report. You could also gather information via the REST API.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-17-2020 07:19 PM
This is correct. The Unknown SGT should not be used in an AuthZ Policy.
Common practice for external logging is to configure (at a minimum) the following Logging Categories to use the configured external syslog server (remote logging target):
- AAA Audit
- Failed Attempts
- Passed Authentications
- Accounting
- Administrative and Operational Audit
- Profiler
This would allow you to create filters, queries, and/or dashboards in your external logging system (i.e. Splunk) to identify sessions hitting the 'Default' AuthZ Policy (AuthorizationPolicyMatchedRule=Default) or an AuthZ Profile name used for the Default AuthZ Policy in a specific Policy Set (e.g. SelectedAuthorizationProfiles=MM-AuthZ-Default)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-17-2020 10:43 PM
Hi Greg,
I appreciate your reply, the reason I was looking at using Unknown SGT is that it technically provides our security requirements and if the Alarm was to work we would be able to pic this up in our monitoring system.
Adding Remote Logging Targets to the Logging Categories you are recommending is noisy, This would relay on remote party syslog server to filter through the noise and then cherry pick only logs of interest and at the same time we are wasting bandwidth to deliver all this noise with only few logs we are interested in.
Is there a way to filter particular messages at the Cisco ISE side and only send them once they match the AuthZ Default rule?
Also then at what conditions I am meant to expect alarm "Unknown SGT was provisioned" to be triggered, is this meant to be logged as soon AuthZ is matched to provision Unknown SGT or is it only picked up when Accounting from NAD reports on its attributes?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2020 12:39 AM
AFAIK, this alarm is triggered only when you have Network Devices that are configured for TrustSec, but you have not create a policy in the Network Device Authorization (NDAC) to assign a specific SGT. This results in the #CTSREQUEST# session hitting the Default NDAC policy which applies the Unknown SGT.
ISE does not have a way to pre-filter logs prior to sending them to an external syslog server. The canned reports in ISE are inflexible and ISE is not built for historical logging/reporting. Most customers send logs to their external syslog server for historical logging and customised reporting.
If you want to work within the constraints of the built-in reports, you can filter on Authorization Rule and export to CSV or create a Scheduled Report. You could also gather information via the REST API.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2020 02:45 AM
Thanks Greg for the explanation and potential workaround.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide