- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE posture check without redirect e.g. audit only
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2016 11:51 AM
Customer is evaluating ISE 2.0 with ASA/AC 4.2 for VPN and posture. Their requirement is for reporting of what remote VPN users have on their computers and not to restrict access.
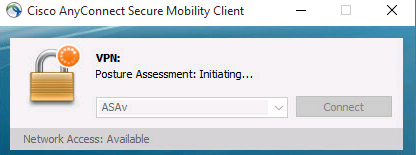
They were able to test ISE with posture check but only if they configure a redirect ACL for CWA, etc. This means that when the VPN is established, the connection does not allow user traffic until the posture check process is completed. And this means the AC ISE module pops up and shows status.
That is not acceptable for them. They need this all to happen without the user seeing the scan or having limited access until this is completed. It appears that without the redirect ACL, AC ISE is not find the ISE server and the scan never happens. Also it appears that if all the posture rules are set to monitor, the posture check does not happen either.
Is it possible to configure the ASA/AC/ISE so that posture is still done but it's transparent to the enduser -no popups, no limited connectivity, etc.
Thanks
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2016 08:10 PM
Such are not ISE posture features in current shipping ISE releases. However, some of up-coming enhancement in next ISE release might help. I will send some info offline.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2016 08:10 PM
Such are not ISE posture features in current shipping ISE releases. However, some of up-coming enhancement in next ISE release might help. I will send some info offline.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-20-2016 10:07 AM
The requested behavior sound similar to what you would get using AnyConnect and ASA with hostscan but not configuring any Dynamic Access Policies to match/act on the endpoint attributes but you would be able to see what is on the machine if you viewed a debug dap trace or syslog. They would see that posture assessment started but nothing else unless DAP was involved.
Snippet from dap trace OS hotfixes, Registry, File and Process check as well you can see the MS FW and AS status
DAP_TRACE: endpoint.os.hotfix["KB976933"] = "true"
DAP_TRACE: endpoint.os.hotfix["KB982018"] = "true"
DAP_TRACE: endpoint.registry["Cisco.Citrix.com"] = {}
DAP_TRACE: endpoint.registry["Cisco.Citrix.com"].exists = "true"
DAP_TRACE: endpoint.registry["Cisco.Citrix.com"].path = "HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Services\\Tcpip\\Parameters\\NV Domain"
DAP_TRACE: endpoint.registry["Cisco.Citrix.com"].type = "string"
DAP_TRACE: endpoint.registry["Cisco.Citrix.com"].value = "Cisco.Citrix.com"
DAP_TRACE: endpoint.file["corp-asset-file"] = {}
DAP_TRACE: endpoint.file["corp-asset-file"].exists = "true"
DAP_TRACE: endpoint.file["corp-asset-file"].path = "c:\\windows\\system32\\drivers\\etc\\corpasset.txt"
DAP_TRACE: endpoint.file["corp-asset-file"].name = "corpasset.txt"
DAP_TRACE: endpoint.file["corp-asset-file"].lastmodified = "22901032"
DAP_TRACE: endpoint.file["corp-asset-file"].timestamp = "1423231665"
DAP_TRACE: endpoint.file["corp-asset-file"].crc32 = "0x8E5DE40F"
DAP_TRACE: endpoint.process["Notepad"] = {}
DAP_TRACE: endpoint.process["Notepad"].exists = "true"
DAP_TRACE: endpoint.process["Notepad"].path = "notepad.exe"
DAP_TRACE: endpoint.process["Notepad"].name = "notepad.exe"
DAP_TRACE: endpoint.registry["ica-1"] = {}
DAP_TRACE: endpoint.registry["ica-1"].exists = "false"
DAP_TRACE: endpoint.registry["ica-1"].path = "HKEY_CLASSES_ROOT\\CSLID\\(238F683-B8B4-11CF-8771-00A024541EE3)"
DAP_TRACE: endpoint.registry["ica-2"] = {}
DAP_TRACE: endpoint.registry["ica-2"].exists = "false"
DAP_TRACE: endpoint.registry["ica-2"].path = "HKEY_CLASSES_ROOT\\Wow6432Node\\CLSID\\(238F6F83-B8B4-11CF-8771-00A024541EE3)"
DAP_TRACE: endpoint.device.protection_extension = "3.6.10120.2"
DAP_TRACE: endpoint.fw["MSWindowsFW"] = {}
DAP_TRACE: endpoint.fw["MSWindowsFW"].exists = "false"
DAP_TRACE: endpoint.fw["MSWindowsFW"].description = "Microsoft Windows Firewall"
DAP_TRACE: endpoint.fw["MSWindowsFW"].version = "7"
DAP_TRACE: endpoint.fw["MSWindowsFW"].enabled = "failed"
DAP_TRACE: endpoint.as["MicrosoftAS"] = {}
DAP_TRACE: endpoint.as["MicrosoftAS"].exists = "true"
DAP_TRACE: endpoint.as["MicrosoftAS"].description = "Windows Defender"
DAP_TRACE: endpoint.as["MicrosoftAS"].version = "6.1.7600.16385"
DAP_TRACE: endpoint.as["MicrosoftAS"].activescan = "ok"
DAP_TRACE: endpoint.as["MicrosoftAS"].lastupdate = "14486900"
DAP_TRACE: endpoint.as["MicrosoftAS"].timestamp = "1431645804"
DAP_TRACE: endpoint.anyconnect.clientversion = "4.2.00071"
DAP_TRACE: endpoint.anyconnect.platform = "win"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2017 04:54 AM
Has this been fixed in the current 2.2 release? Cause I see this also happening with Anyconnect 4.3 and ISE 2.2.
First I get a webbrowser pop-up, while the Anyconnect Posture with ISE is happening in the background. For the customer it's confusing for 'user experience'
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:

