- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Radius Called-Station-ID and Mobility Anchor
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 07:20 AM
Hi
Running ISE 2.,2, we have several mobility anchors with external companies, so we can work in their buildings and they can work in ours.
One of them seems to have on their WLC Radius Auth Called Station ID type as IP Address.
So this is causing issues.
It looks like I need to add their WLC in via IP for Called-Station -ID
What I'm not sure is this, my current Auth Policy is
DEVICE:Device Type EQUALS Device Type#All Device Typles#WLAN AND
Radius:Called-Station-ID ENDS WITH "myssid"
But if I add belowe
Radius:Called-Station-ID CONTAINS wlc_ip
so looks like
DEVICE:Device Type EQUALS Device Type#All Device Typles#WLAN AND
Redius:Called-Station-ID ENDS WITH "myssid" and
Radios:Called-Station-ID CONTAINS wlc_ip
Won't this stop all my current users and only allow any one trying to connect to "myssid" and from a certain wlc-IP?
Is there another format it should be in to allow all my existing and if comes from wlc-ip
many thanks
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 08:11 AM
First I would re-investigate the inconsistency in your Called Station ID setting. Often the network wireless team may set values with no understanding of impact on RADIUS. Allowing change there may resolve issue.
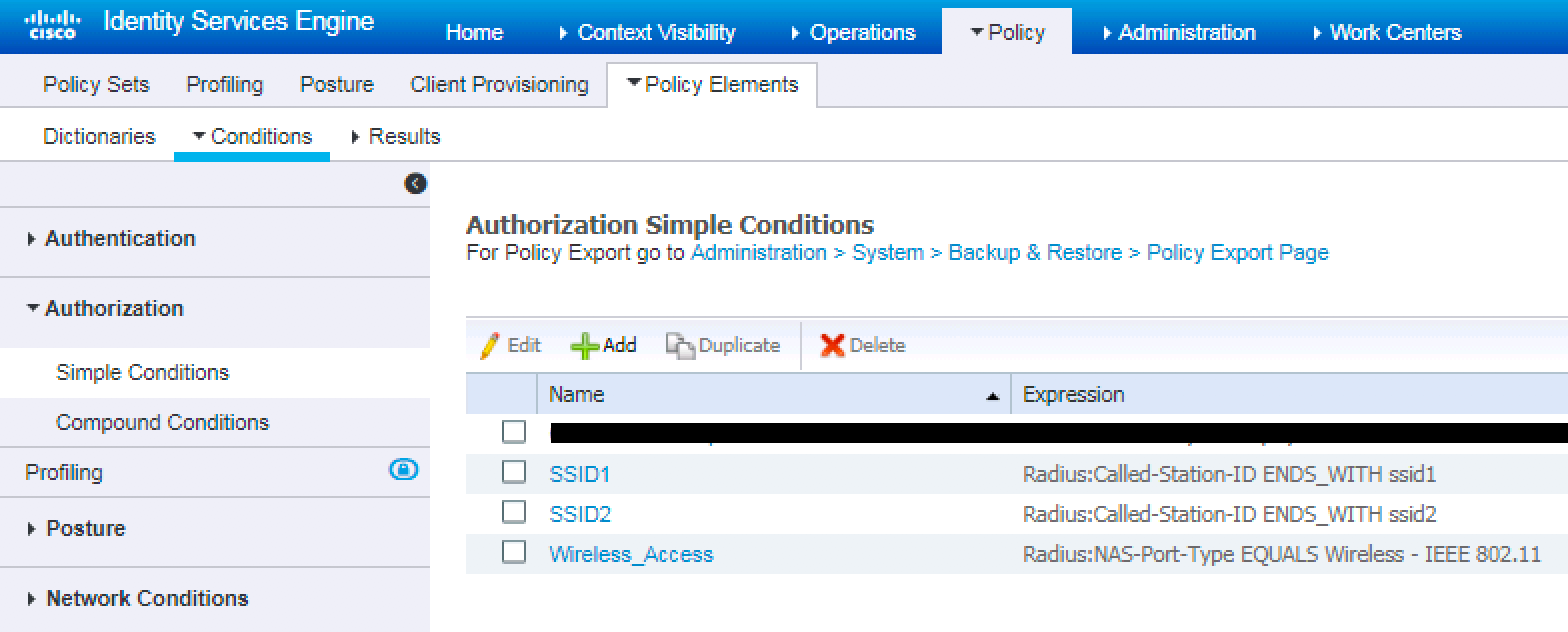
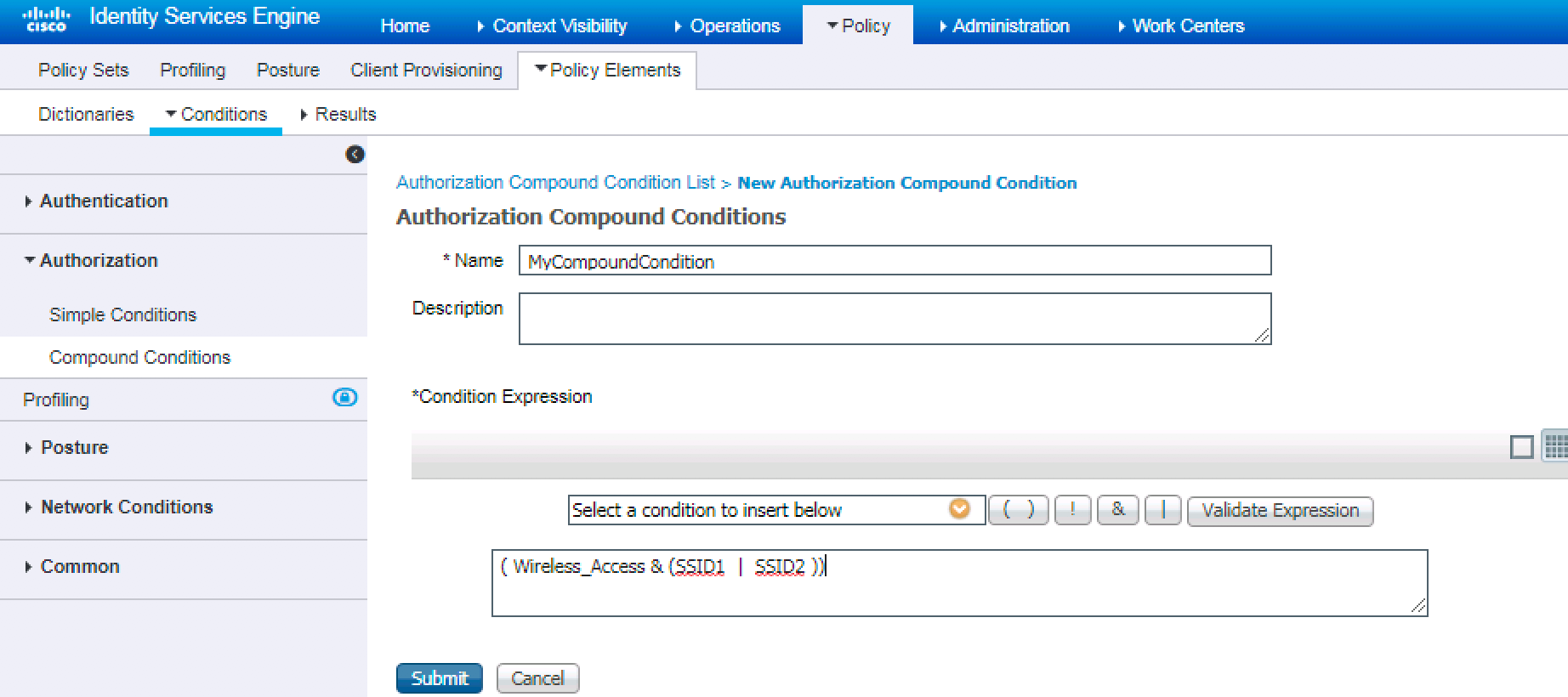
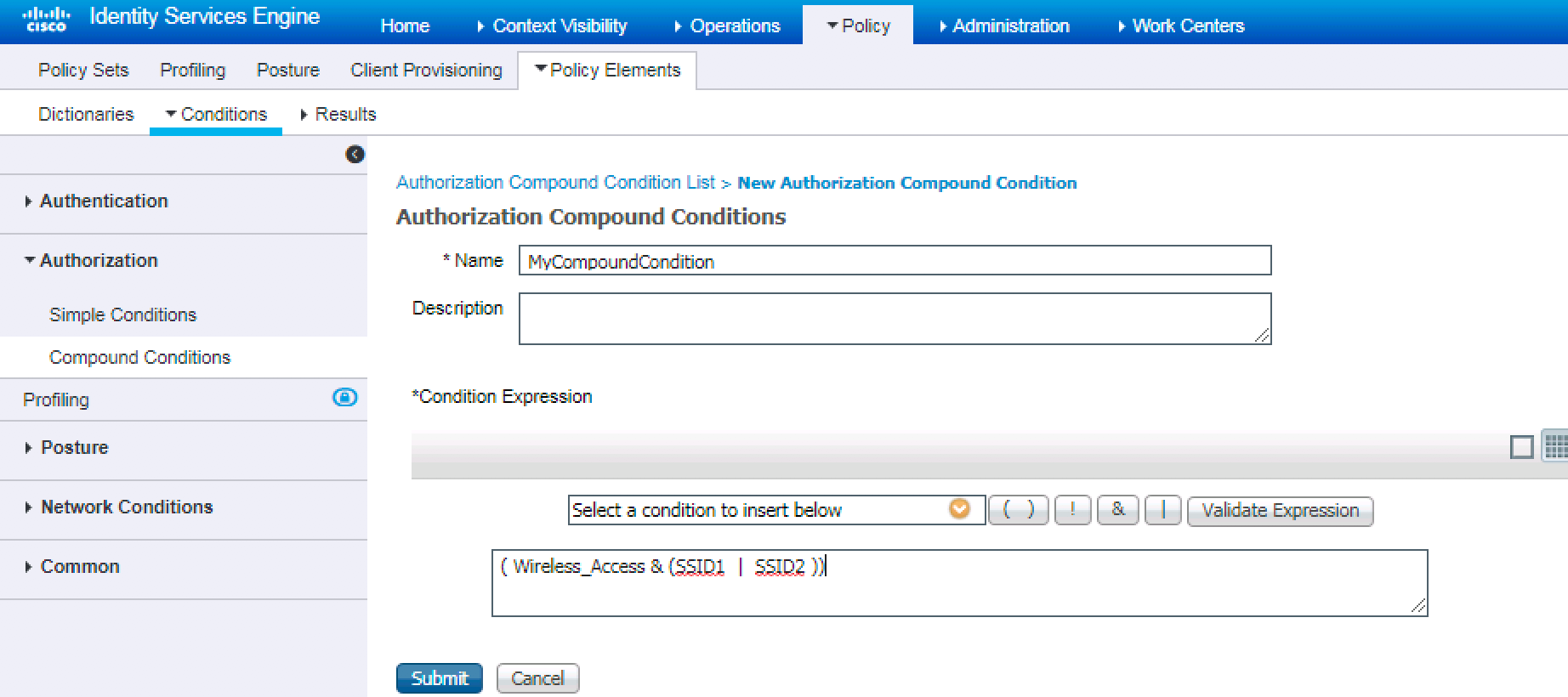
Secondly, I think you are looking to add a boolean logic to support "IF wlan AND (myssid OR wlcip)". If that is the case, this is possible but not intuitive in releases prior to 2.3. Create each of the authorization conditions above as a separate, simple authorization condition.
Then create a compound condition using the simple conditions. You will see a grid in right corner which allows boolean logic to be applied...
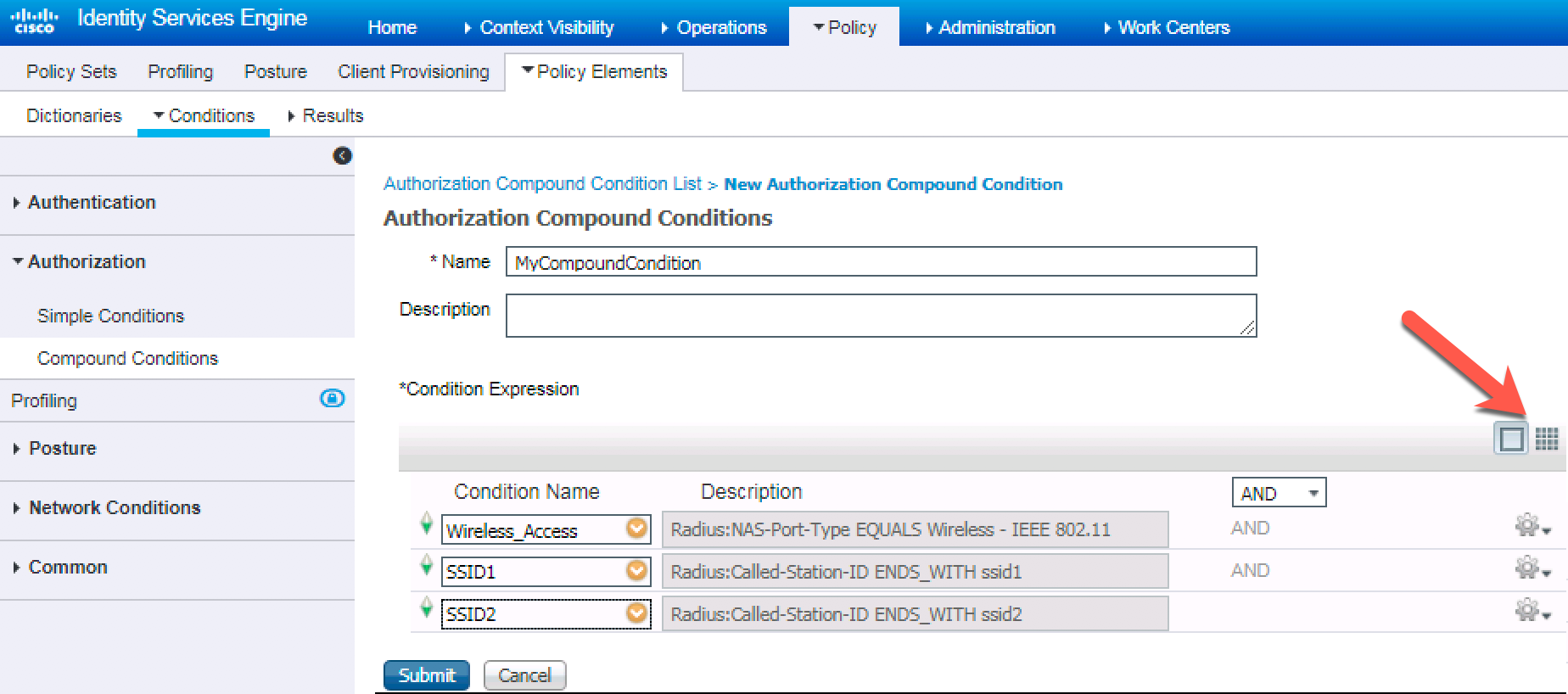
Change boolean to match requirements and then add this compound condition to AuthZ Policy Rule.
Craig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 08:11 AM
First I would re-investigate the inconsistency in your Called Station ID setting. Often the network wireless team may set values with no understanding of impact on RADIUS. Allowing change there may resolve issue.
Secondly, I think you are looking to add a boolean logic to support "IF wlan AND (myssid OR wlcip)". If that is the case, this is possible but not intuitive in releases prior to 2.3. Create each of the authorization conditions above as a separate, simple authorization condition.
Then create a compound condition using the simple conditions. You will see a grid in right corner which allows boolean logic to be applied...
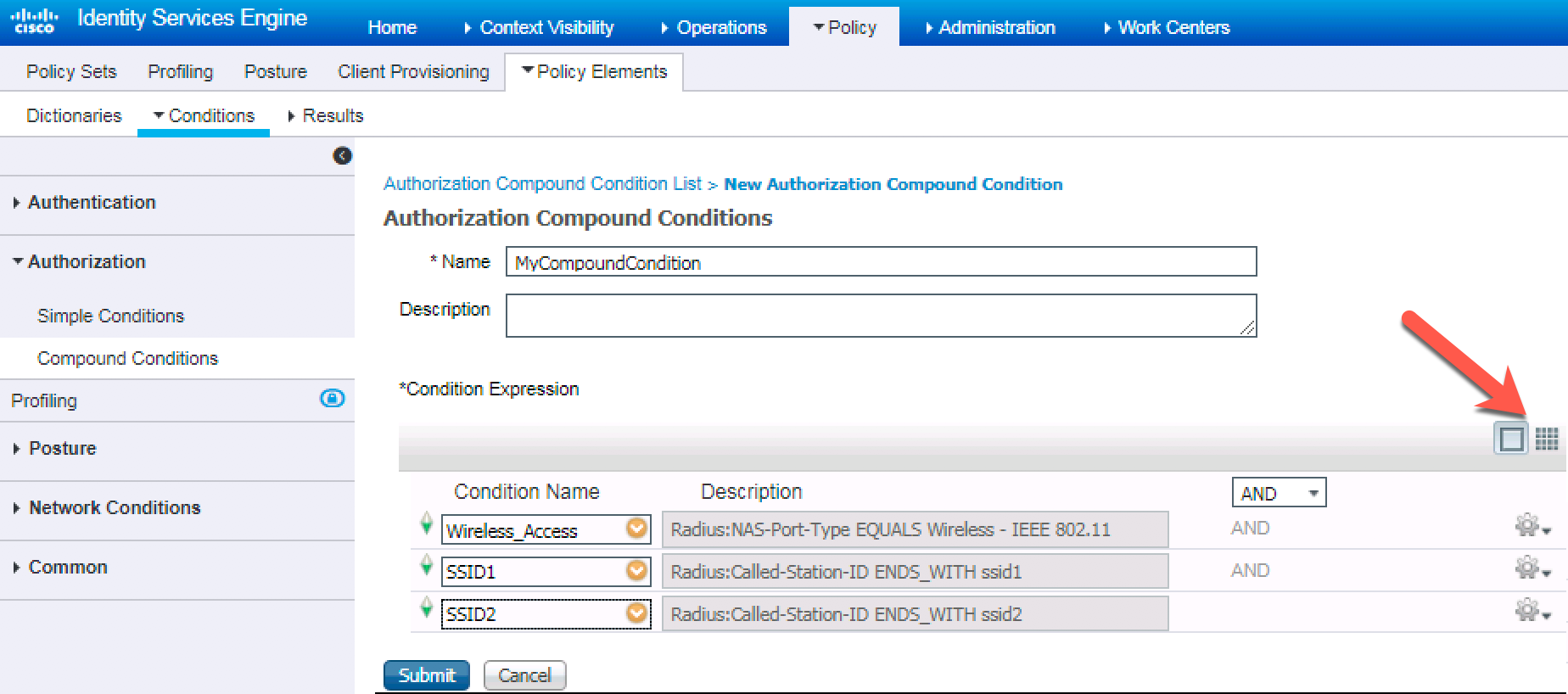
Change boolean to match requirements and then add this compound condition to AuthZ Policy Rule.
Craig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 11:20 AM
Logically, OR is your operator.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-01-2017 04:28 PM
I like the idea of the compound conditions. But how about a simple regex, using the MATCHES operator?
Not sure what you mean by wlc_ip ? Literally "wlc_ip" or an IP address?
Let's say you need to match on any of the following strings below "ssid1" or "ssid2" or "10.1.1.1" or "10.2.2.2" then this will be a legal regex syntax that ISE 2.2 is able to digest
DEVICE:Device Type EQUALS Device Type#All Device Types#WLAN AND
Radius:Called-Station-ID MATCHES (ssid1|ssid2|10\.1\.1\.1|10\.2\.2\.2)
The "." has to be escaped with a \ character because it has special significance in regular expressions. But apart from that I think it may be a viable solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 05:13 AM
+Thanks for reply's, I have to submit Change Request, and have no test bed to carry out on, so got the risk of disabling 4000+ devices. Best to create a copy and add the Radius:Called-Station-ID MATCHES (ssid1|ssid2|10\.1\.1\.1|10\.2\.2\.2) format.
The reason why posted is devices in the SE Onboarding connect, Mobil iron work, but non from the Corp AD Wireless Group on this one location., only difference is the Aut Radius on their WLC is set to IP Address
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 05:40 AM
In general, you should not config the WLC to send wlc ip as this may cause Calling Station ID to also be set for Client IP in open auth. This can cause issues with client matching rules based on Calling ID.
You can also set a rule to Monitor only to then see matching rules in actual live log details.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-02-2017 02:48 PM
One way to mitigate the risk is to build a lab VM and restore your prod config onto it. Should not take more than 2 hours to get that. Then spin up a Linux VM and install Free radius Utils and send packets to your lab. You can simulate your environment without any hardware. If you need 802.1x emulation then install eapol_test which is part of the wpa_supplicant package. I wrote a small blog series on this forum. I use this all the time to prototype my policies and it's really quick and efficient.
Rapid prototyping ISE Policies without any real networking hardware
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

