- Cisco Community
- Technology and Support
- Security
- Network Security
- how to create default route on multiple internet interfaces?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
how to create default route on multiple internet interfaces?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2013 10:58 AM - edited 03-11-2019 06:00 PM
Hi All,
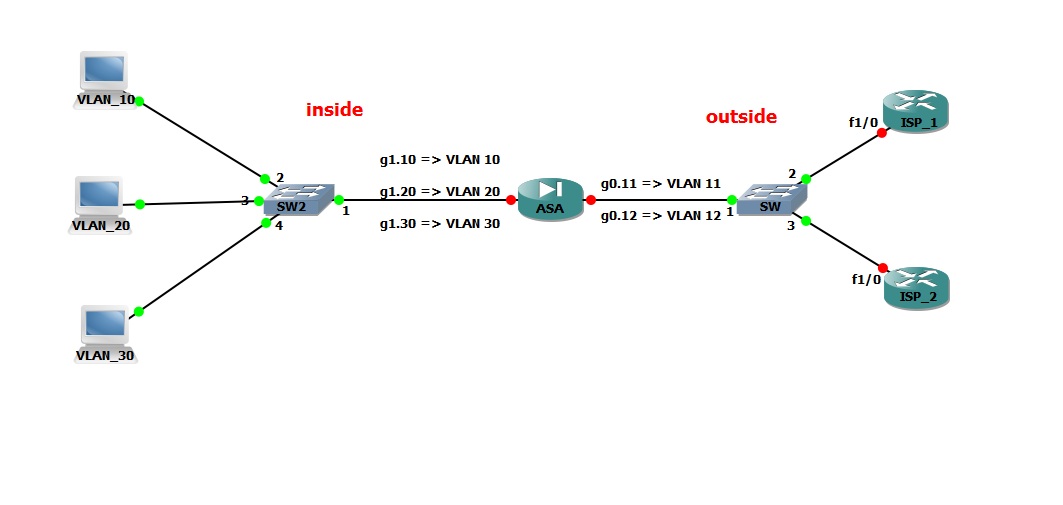
I have Case: .... please see the diagram in the image below
1- ASA Firewall version 8.2.
2- Access Switches, and no core switch(s).
3- 2 ISPs with different Real IPs Ranges.
what i want to do:
1- Make the ASA Firewall as a Core Switch "create vlans and route betwwen vlans".
2- NAT Groups of Vlans to an ISP and others to the Other ISP.
3- Make Default to the first ISP, and also Default route to the other ISP.
4- Track the first default route, if down go to the other route.....
How can i do this?
Thanks
Omar
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-14-2013 01:12 PM
Is this what you are looking for?
http://www.gomjabbar.com/2011/12/16/cisco-asa-sla-monitoring/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2013 08:33 PM
What you are talking about is known as Policy-based routing or PBR and it's not supported by the ASA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2013 10:29 PM
What he's talking about is just regular sla-monitoring (tracking static route) wich asa supports, not PBR as on ISR (with route-maps and etc.). So it easily can be done.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2013 10:20 PM
Hi Omar,
You can create two default route with different metric value say you have two internet gateways 1.1.1.1 (isp1) and 2.2.2.2 (isp2).
You can have a default route like the below in you ASA
route outisde 0.0.0.0 0.0.0.0 1.1.1.1
route outside 0.0.0.0 0.0.0.0 2.2.2.2 2
If 1.1.1.1(ISP1) fails and not reachable it will take the secondary def route to reach the internet.
Hope this helps.
By
Karthik
Please do rate if the given information helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2013 12:03 AM
It might be just me, but it sounds like PBR and SLA, still not supported.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
