- Cisco Community
- Technology and Support
- Security
- Network Security
- routing between vlan's on ASA 5505
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
routing between vlan's on ASA 5505
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2012 01:00 PM - edited 03-11-2019 05:34 PM
I have an ASA 5505 and I have the three regular vlans, outside, inside and dmz. The best would be only have outside and inside and skip dmz, but without explenation there is not possible to have more then two clients in whats now dmz because of a mac filter on third party device.
So as security is concerned dmz and inside is equal, one to one and there should be full access between them. I ran the wizard and said that the only way traffic not should be possible to flow is from dmz to outside.
In the NAT rules the onle rule is
global (outside) 1 interface nat (inside) 1 0.0.0.0 0.0.0.0
But traffic from one way or the other dmz to inside, og inside to dmz it says in log
| 3 | Dec 06 2012 | 15:38:39 | 305006 | 172.17.6.10 | 53 | portmap translation creation failed for udp src inside:192.168.6.102/49358 dst dmz:172.17.6.10/53 |
From documentation I have an image with network drawing from documentation.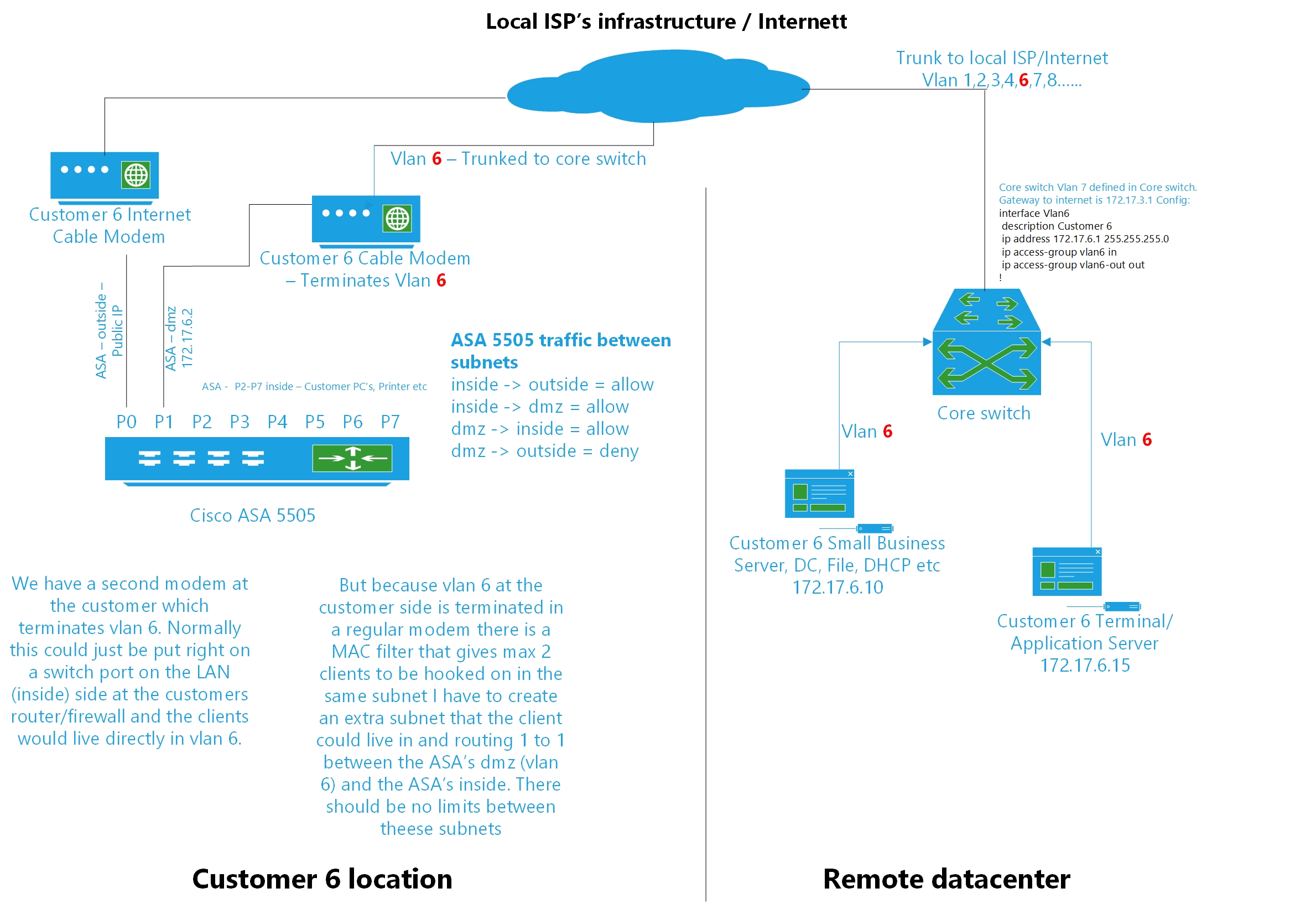
What do I have to do allow traffic btween inside and dmz, both ways.
Trond
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2012 01:18 PM
Hi,
So that log message refers to some DNS query not going through from "inside" to "dmz"
Have you considered configuring NAT0 / NAT Exemption between "inside" and "dmz" networks?
Could be done in following way for example
access-list INSIDE-NAT0 permit ip
nat (inside) 0 access-list INSIDE-NAT0
This would basically mean that NO translations would be made between the 2 networks you configure in the access-list. This works both ways naturally whoever is initiating the connection.
I'm not sure if this will correct the problem. I guess you have allowed the traffic between the 2 interfaces on the ASA?
- Jouni
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2012 01:46 PM
I'm not really grasping this nat consepts in the asa.
I first tried to do
static (dmz,inside) 172.17.6.0 192.168.6.0 netmask 255.255.255.0
static (inside,dmz) 192.168.6.0 172.17.6.0 netmask 255.255.255.0
but then when I was pinging for instance 192.168.6.20 from 172.17.6.15 the log says it couldnt find next hop and that destination was 172.17.6.20 and not 192.168.6.20
but then I removed it and tried it your way and that worked like a charm:)
Thanks
This is documented for later use!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2012 01:49 PM
Glad it worked out
One possible solution would have also been
static (inside,dmz) 192.168.6.0 192.168.6.0 netmask 255.255.255.0
Please rate if the information was helpfull
- Jouni
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:


