Cisco IOS-XE 16.10.1 – The “Catalyst” Update
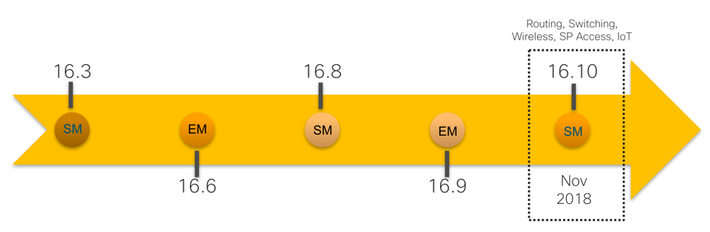
As a part of the Enterprise Networking (EN) team’s journey to Intent-based Networking, Cisco recently announced availability of the latest release on the IOS-XE train – IOS-XE Gibraltar 16.10.1. This is a standard maintenance release supporting Switching, Wireless, SP-Access, Routing (16.10.1a/b) as well as IOT platforms with a sustaining support lifetime of 12 months and two scheduled rebuilds. A unified software release for Enterprise Networking, it adds support for new software features on the existing platforms and also introduces support for new platforms across the various EN technology areas.
While 16.10 spans the breadth of the EN products, here we are going to focus specifically on all that the software release brings in for Catalyst.
IOS-XE 16.10.1 introduces support for two brand new members of the Cisco Catalyst 9000 family - The Catalyst 9200 Series Switches (modular uplink models) and the Catalyst 9800 Series Wireless Controllers.
Here’s a great read on the recent Catalyst 9000 Expansion.
Simplicity without Compromise
The new Cisco Catalyst 9200 Series Switches are enterprise-class access switches that extend the power of intent-based networking and Cisco Catalyst 9000 Series Switches hardware and software innovation to a broader scale of deployments. These switches focus on offering simplicity without compromise – they are secure, always on and provide IT simplicity features for the mid-market and simple branch deployments. IOS-XE 16.10.1 introduces support for 4 new SKUs in this family - C9200-24T, C9200-48T, C9200-24P and C9200-48P. These are 24 and 48 ports data-only and PoE variants that come with modular uplinks, modular fans (dual) and module power supplies (dual). There are two options for the modular uplinks - 4x1G and 4x10G. These switches support up to 8-member StackWise-160 and so provide Fast PoE+ capabilities for up to 384 ports per stack.
These modular uplink models are expected to FCS early next month. Also, note that the introductory software release for the fixed uplink models - 9200L – is IOS-XE 16.9.2 instead.
Always on, Secure, Deploy Anywhere
Catalyst is not just switching anymore!
The New Catalyst 9800 Series Wireless Controllers are powered by an open and programmable Cisco IOS XE and combine the best of RF excellence with IOS XE benefits. These are the industry’s most reliable and highly secure controllers, ready to deploy anywhere - including the cloud of your choice. You can: Install critical updates without affecting user access, manage rolling updates of Wi-Fi access points and deploy on-premises or run as software in select Catalyst 9000 switches or in private or public clouds. Visit here for all the details.
Catalyst Switching Platform Support
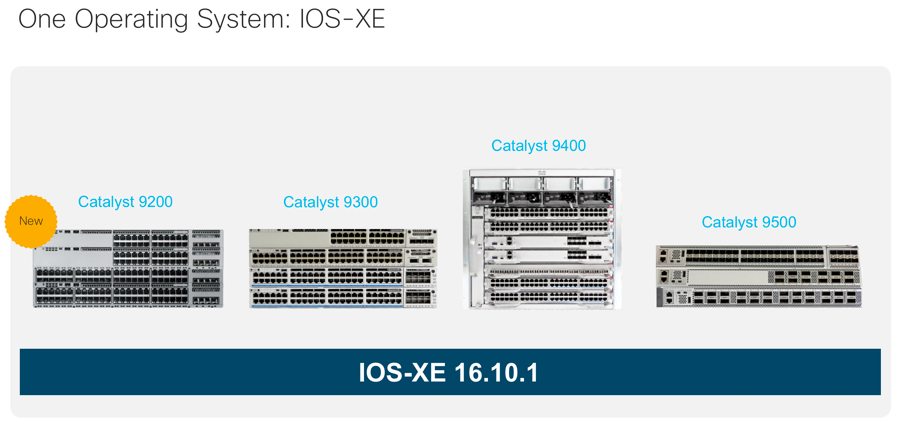
The complete switching platform support list for IOS-XE 16.10.1: C9200, C9300, C9400, C9500 and C9500 High Performance
Note: IOS-XE 16.10.1 does not support the Catalyst 3850/3650 platforms.
Catalyst Switching Software Support
Switching Software in IOS-XE 16.10.1 adds features across the Catalyst 9000 portfolio in areas of security, network segmentation, high availability and platform infrastructure. Following are the key switching features and their applicable platforms:
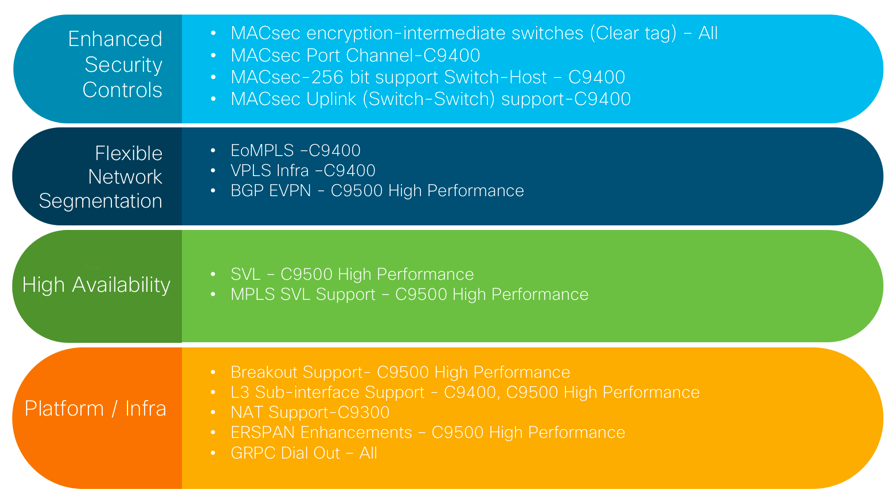
Starting with Security, enhancing the capability to provide a network-wide encryption is most sought after by governments and organizations. Compared with other 9K platforms, Catalyst 9400 has required catchup in its MACsec capabilities. 16.10.1 brings in the following enhancements in MACsec:
- Support for MACsec 256-bit MKA “Host to Switch” and 128-bit (SAP and MKA) and 256-bit MKA “Switch to Switch” on Catalyst 9400
- MACsec over Port Channel support on Catalyst 9400
- ClearTag MACsec feature support on all Catalyst 9000 switches – now Catalyst 9K switches acting as intermediary switches support MACsec connections between end devices in WAN MACsec deployments. The Clear Tag Feature enables the switch ASIC to forward encrypted packet without parsing the MACsec header. Prior to this release, encrypted packets were dropped if MACsec was not configured on the intermediate switches.
With the 16.10.1 release, Catalyst 9400 also enables support for Ethernet over MPLS (EoMPLS) and Virtual Private LAN services (VPLS). This is applicable to SUP-1/SUP1-XL in Standalone and SVL mode. EoMPLS/VPLS have been already supported on C9500 and C9500 High Performance Platforms prior to this release. BGP EVPN with VxLAN that enables scalable, multi-tenant and robust VxLAN overlay networks using BGP-EVPN and already supported on Catalyst 9300/9400/9500, is now also supported on the Catalyst 9500 High Performance Series with this release.
In High Availability, this release adds Cisco StackWise Virtual support on the Catalyst 9500 High Performance Series - C9500-32C, C9500-32QC, C9500-48Y4C & C9500-24Y4C models. In addition, the High-Performance models now also support MPLS in the StackWise Virtual mode. Cisco StackWise Virtual simplifies operational efficiency with a single control and management plane and provides best-in-class high-availability by pairing two switches into one virtual switch.
16.10.1 adds new features on the Platform Infrastructure side:
- Layer 2 sub-interfaces that create a logical division of a physical interface that operates are now supported on Catalyst 9400 and Catalyst 9500 High Performance platforms
- The Catalyst 9500 High Performance, specifically C9500-32C, now supports breakout option, whereby a 40G QSFP+ interface can be split into four 10G SFP+ interfaces and a single 100G QSFP28 interface can be split into four 25G SFP28 interfaces
- ERSPAN Source capabilities for the Catalyst 9500 High Performance models - Type II header: Truncation, DSCP and VRF & Type III header: Truncation, DSCP, VRF, SGT and Timestamp
- The Catalyst 9300 switches now also support Network Address Translation with support for 5K NAT TCAM entries
The release also introduces new capabilities in network programmability. All Catalyst 9000 switches now support gRPC Dial-Out functionality that expands existing Model Driven Telemetry capabilities with the addition of gRPC protocol support and Dial-Out (configured) telemetry subscriptions. gPRC’s Network Management Interface, or gNMI, that allows installation, editing and deletion of configurations of network devices using YANG data models, now also supports Wildcard and Namespaces. Updates relating to YANG data models in this release include new native and experimental models, as well as certain IETF and OpenConfig models. For the complete list of YANG models available with this release, navigate to https://github.com/YangModels/yang/tree/master/vendor/cisco/xe/16101.
16.10 adds an array of (30+) Serviceability Enhancements that are developed to help with troubleshooting the network and reduction in operational costs. These are either completely new or modified, debug, show or set commands that provide more comprehensive diagnostics and troubleshooting capabilities. Some examples are optimised event tracing, addition of new support packages (show-tech) for stack, platform, CoPP, QoS and port, pseudo packet tracer functionality and improvement in crash information. We suggest checking the platform specific release notes and command reference guides for details on the individual serviceability enhancements.
Finally, support for new optics and breakout cables has also been added and more specifics on this and all other features can be found in the platform specific IOS-XE 16.10 release notes, links to which are provided below:
Catalyst 9200 Series
Catalyst 9300 Series
Catalyst 9400 Series
Catalyst 9500 Series
What’s Next?
IOS-XE 16.11.1, the next standard maintenance release, is targeted for release in March 2019. Features that have been planned for this release include core features in the areas of MPLS and SVL, support for NBAR2 and Fabric enabled wireless on the Catalyst 9200, and Cisco eWLC enablement on Catalyst 9400 and 9500 High performance helping customers reduce cost and complexity. Stay tuned for more updates!
