- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Cisco Configuration Diff
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 04-08-2016 05:42 AM
Tool available at: https://cway.cisco.com/tools/confdiff/
Description
Have you ever struggled comparing two network configuration files?
Of course there exist numerous diff scripts and tools (Unix “diff” command, WinMerge…) but they are well suited for programming code or articles. When used on Cisco configuration files, they tend to flood relevant exception in a large amount of false positives, which might lead to mistakes and impact your productivity.
This tool addresses the problem with an approach that understands the hierarchical structure of Cisco configuration files and an output that facilitates comparison by reordering and aligning the files such that matching parts and corresponding sections are facing each other.
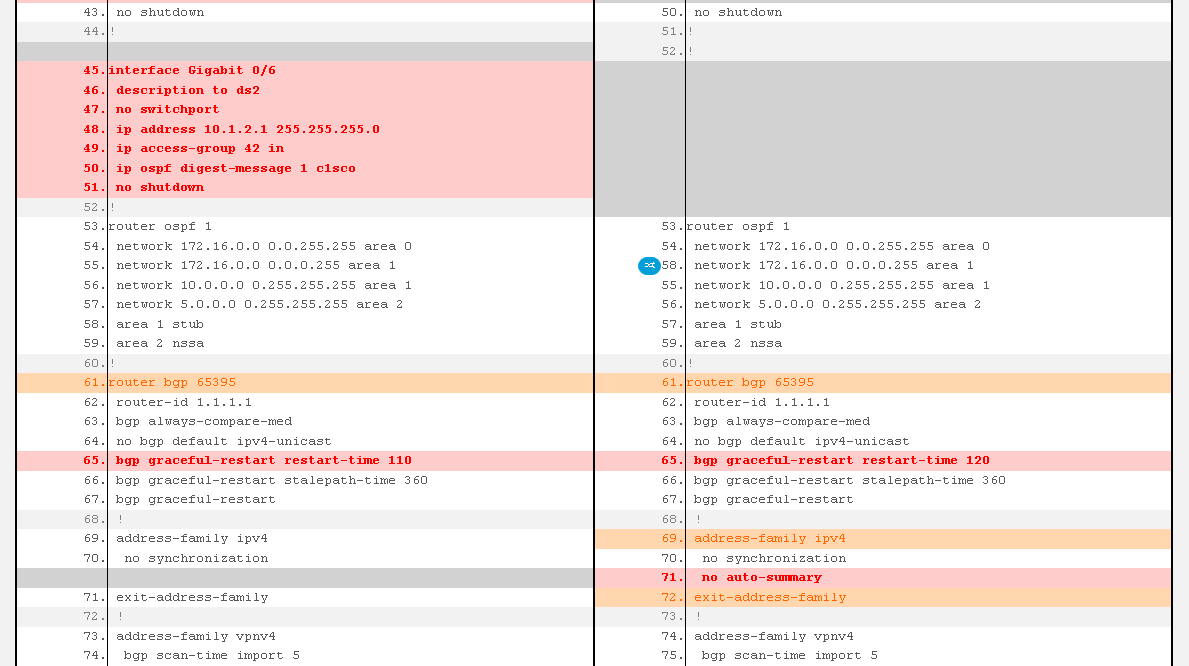
How to interpret the output:
- Red lines are different or missing in the other file
- Orange lines are headers or footers of sections containing red lines. They do have a matching line in the other configuration. Yet, they are highlighted because you have to type them to enter the right configuration context to configure or fix red lines (in other words, orange highlights the location of red lines in the configuration hierarchy)
- Blue icons are warnings about reordered lines: while the order of line in a given section is most of the time not meaningful, there are a few exceptions such as old IOS access-lists or IOS-XR route-policies, to which you must pay attention (hence the warning)
- At the top, two text zones give the raw unformatted diff (just red and orange lines) which you can easily copy/paste
NB: this tool infers the hierarchical structure of configurations from their indentation (spaces at the beginning of the line), so it is essential that indentation of input files follows the format of a show run.
Use Cases
- Comparing versions of the configuration for a given device and assess the evolution over time
- Verifying the changes performed in the network during a maintenance window
- Comparing configurations of devices with similar roles to work towards better standardisation
- Comparing the actual show run to the expected configuration (for example generated from the initial network design)
Technologies covered
Because it is based almost only on indentation, this tool is platform agnostic: it can be used for configuration files of IOS, IOS-XE, IOS-XR, NX-OS...
Tool developers
- Cedric Dessez – Network Consulting Engineer, Cisco Advanced Services – Amsterdam (NL)
- Guillaume Mulocher – Network Consulting Engineer, Cisco Advanced Services – Reading (UK)
Feedback
Your feedback is valuable to help us improve the tool. Do not hesitate to add a comment using the icon in the upper right corner of the page.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
great work, thx
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Nice tool. I bookmarked it for use later, but it displays as "Cisco Tool" by default, due to the title. You couldn't give it a nicer title for other people wanting to bookmark it could you?
<title>Cisco Tool</title>
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for the feedback, I will follow up on improving it :)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you very much Philip for the feedback. We will take that into account.
Kind regards
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great tool , is anyway to download a copy into the local PC. , we have at times no internet , the local copy would be great way to help .... ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you Sam for the feedback.
The tool is still in a Beta phase and I'm afraid it is not yet possible to download a standalone version, but you are not the first one to ask for it and we are reviewing our options to see whether (and how) we could do that.
Kind regards
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
Can you advise what happens to the configuration files that are "uploaded to Cisco"?
Does it get stored and used by Cisco in any way?
Thanks for your answer in advance!
Regards,
Florian
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Florian,
It is deleted, after running the tool and displayed the information, the customer files are deleted.
Thanks,
Antonio
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Have you considered (or will this work) with ASA firewall configurations?
-Scott
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Scott,
Thank you for your interest in the tool. As it is will work well with any pair of configuration files having a hierarchical structure including the ASA ones.
Regards,
Guillaume
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
hi
This is a great tool. I would also like a local copy of it.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great tool, this didn't work on ASA though
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great tool! is bookmarked now!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Any chance that the code for this will be released? In order to be able to include it in configuration review process?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Cedric,
I'm new to the community I must say Great tool! I just bookmarked!
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: