- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Evaluating Cisco SDWAN Cloud onRamp for SaaS using dCloud
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-18-2019 08:47 AM - edited 03-18-2019 09:46 AM
Note: This lab utilizes the dCloud SD-WAN platform. You must schedule this ahead of time before proceeding below!
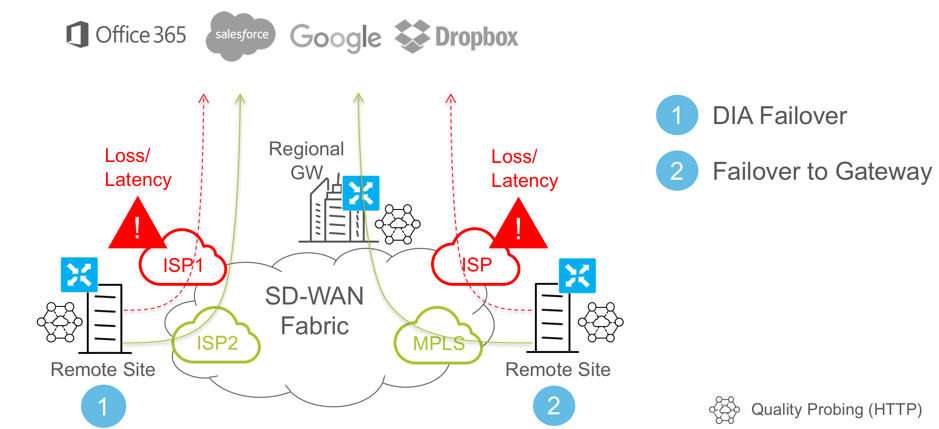
Cloud onRamp is one of the most popular features to enable within Cisco SDWAN. As many organizations start to make their shift to the cloud, many are looking for solutions to help facilitate the transition. As organizations increasingly take advantage of Software as a Service (SaaS), it becomes increasingly difficult to provide a positive user experience (i.e. we can’t control the Internet!). Cloud onRamp for SaaS is a feature that enables us to squeeze maximum efficiency out of our Internet links by selecting the best performing circuit to get a user’s traffic to the SaaS destination. Similar to how your Cisco SD-WAN solution monitors your transports via Bidirectional Forwarding Detection (BFD), Cloud onRamp utilizes HTTP ‘ping’ packets to monitor the loss, latency and response time for a SaaS application. These packets are sent every few seconds from each configured Internet transport. When a user accesses the configured SaaS application, the best transport is chosen based on the telemetry collected.
Step 0: Pre-requisites
Since this lab serves multiple use-cases, we must prep it with a bit of pre-configuration prior to starting with Cloud onRamp.
1. From the Configuration, Templates menu, click on the ellipsis to the right of the template named DC-vEdges and choose Edit.
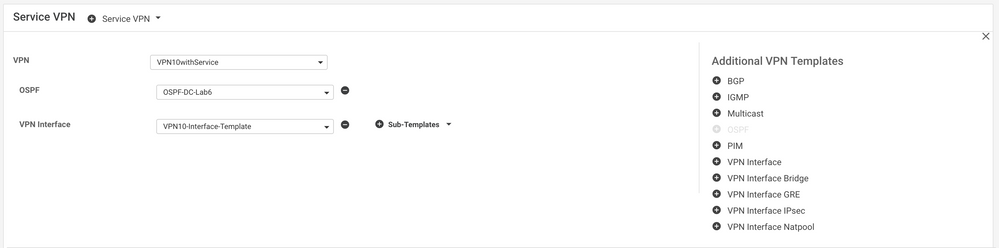
2. Scroll down to the Service VPN sub-section.
3. Click the OSPF button to the right of the Service VPN 10 instance (VPN10withService).
4. Click the down arrow for your new OSPF instance and select the Feature Template (OSPF-DC-Lab6):
5. Click the Update button at the bottom of the screen.
6. Click the Next button.
7. In the next window, you can review the configuration changes to the devices by clicking on them in the left-hand pane, or click the Configure Devices button to proceed.
8. In the Configure Devices window that appears, check the Confirm configuration changes for 4 devices box and click OK.
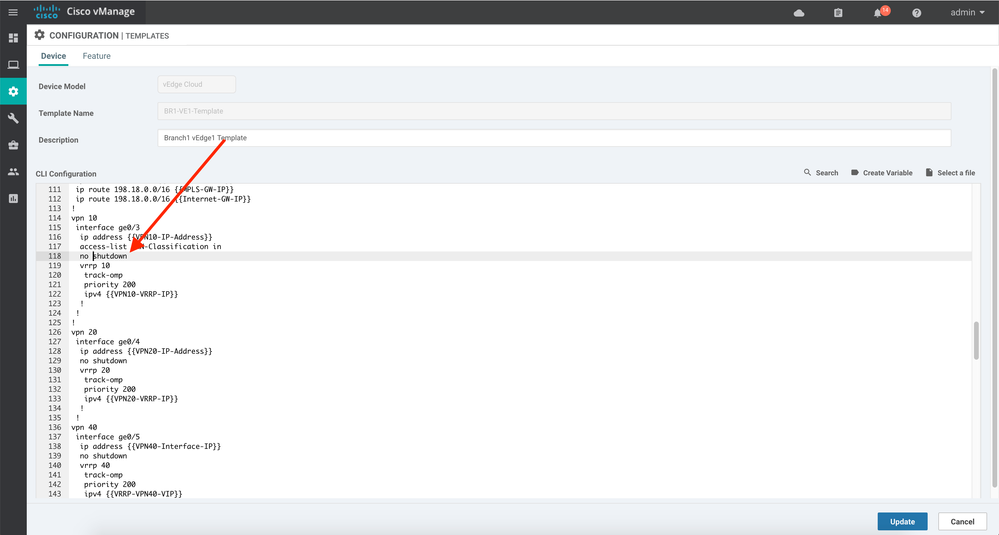
9. From the Configuration, Templates menu click on the ellipsis to the right of the template named BR1-VE1-Template and choose Edit.
10. Enable the LAN-facing interface by editing line 118 to read no shutdown:
Step 1: Enable Cloud onRamp for SaaS
You can enable the Cloud onRamp for SaaS service (f.k.a. CloudExpress) in sites with Direct Internet Access (DIA) and in DIA sites that access the Internet through a secure web gateway such as Cisco Umbrella. You can also enable the Cloud onRamp service in client sites that access the Internet through another site in the overlay network, called a gateway site. Gateway sites can include regional data centers or carrier-neutral facilities. When you enable the Cloud onRamp service on a client site that accesses the Internet through a gateway, you also enable the Cloud onRamp service on the gateway site.
All Cisco SD-WAN devices configured for the Cloud onRamp service must meet these requirements:
- The devices must run Viptela Software Release 16.3 or higher.
- The devices must run in vManage mode.
- You must configure a DNS server address in VPN 0.
- You must configure local exit interfaces in VPN 0:
- If the local interface list contains only physical interfaces, you must enable NAT on those interfaces. You can use normal default IP routes for next hops.
- If the local interface list contains only GRE interfaces, you do not need to enable NAT on those interfaces. You can add default routes to the IP address of the GRE tunnel to the destination.
- This feature is currently only supported on vEdges (cEdge will come in July, 2019).
- Additionally, the Cloud onRamp service runs on IPv4 only. It does not support IPv6 at this time.
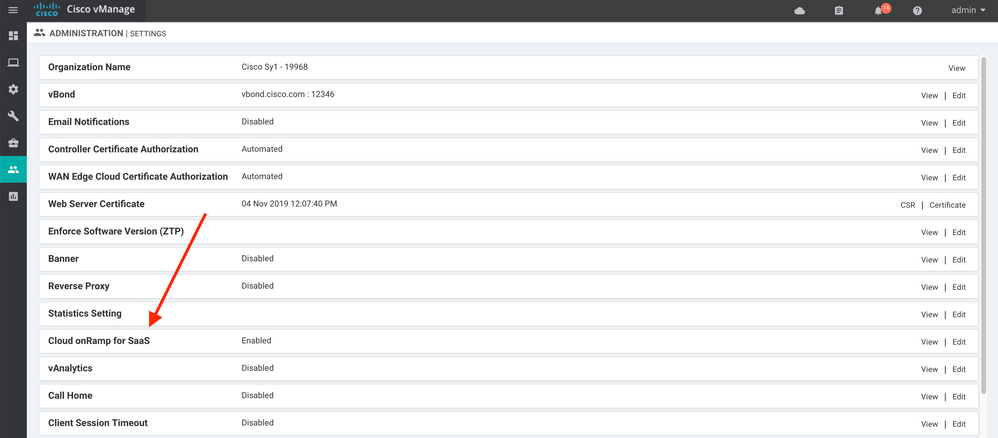
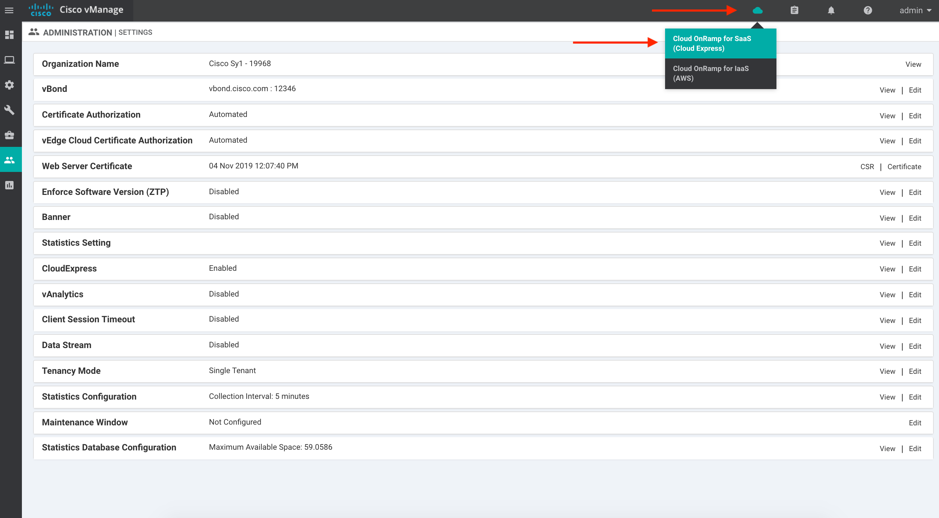
1. To begin our configuration, let’s make sure the feature is enabled globally. Navigate to Administration, Settings.
2. Find the Cloud onRamp for SaaS feature. It should be enabled for you, but if not, click on the Edit link and enable it:
3. Next, head to the Cloud onRamp menu at the top of the screen and click on Cloud OnRamp for SaaS:
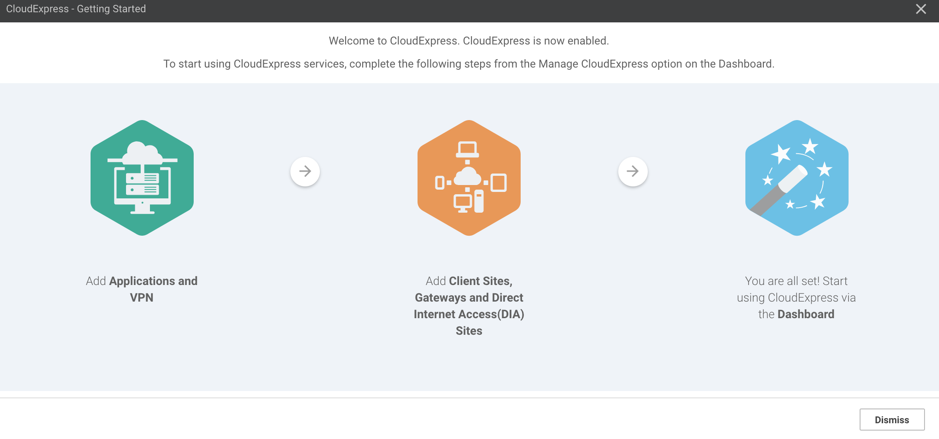
4. You will be presented with the following screen. Review the instructions and click Dismiss:
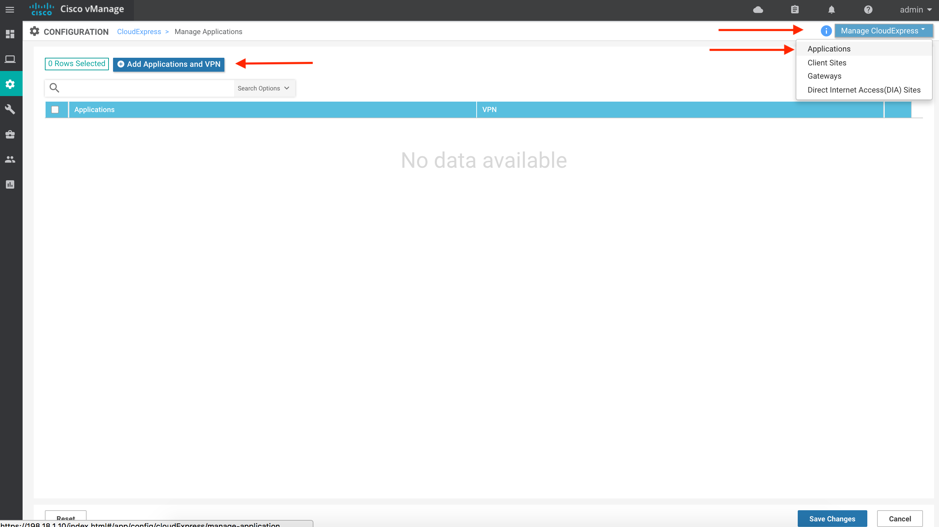
5. As mentioned in the instructions you just reviewed, the first step to configuring the service is to add the Applications and Service VPNs you wish to monitor. Click the Manage CloudExpress button in the upper right and choose Applications:
6. Click on the Add Applications and VPN button.
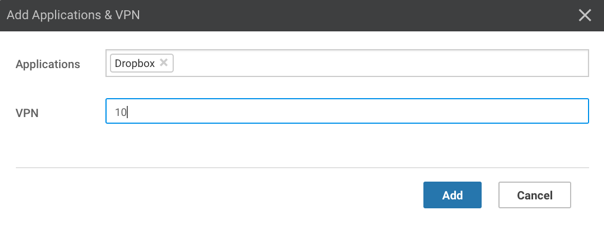
7. In the window that appears, choose the SaaS application you wish to monitor and enter VPN 10 in the VPN. We’ll choose DropBox in our example:
8. Click the Add button, followed by the Save Changes.
9. Next, we need to let the system know where our Client Sites are, or those who will be using this service. Click the Manage CloudExpress button and choose Client Sites.
10. Click the Attach Sites button.
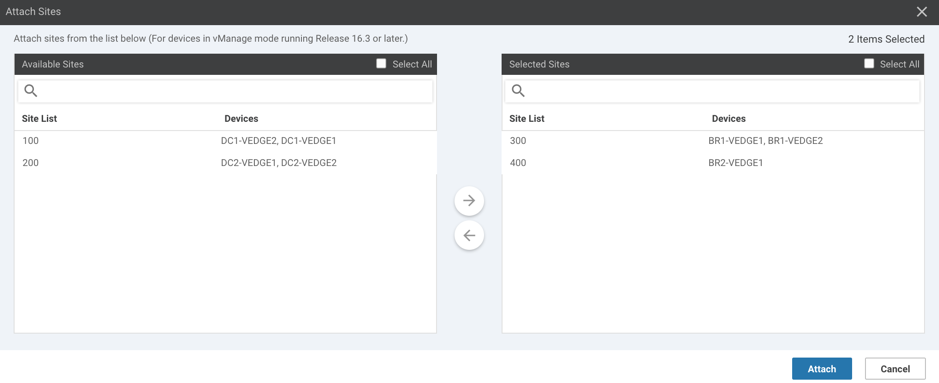
11. Choose your branch locations (denoted by a hostname beginning with "BR") in the window that appears and click the Attach button (note, Branch 3 has a cEdge allocated to it and, hence, may not be available in the output below):
12. The system will then provision the branch locations as necessary.
13. Now we need to tell the system where our Direct Internet Access sites are located. Click on the cloud in the upper right corner, followed by Cloud OnRamp for SaaS (Cloud Express).
14. Click the Manage CloudExpress button in the upper right and choose Direct Internet Access (DIA) Sites.
15. Click the Attach DIA Sites.
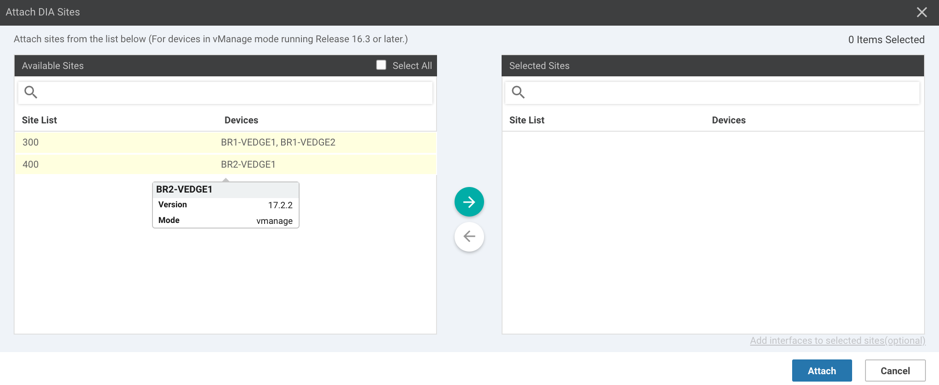
16. In the window that appears, choose your two branch locations (Site ID 300, and potentially 400) and click the Attach button:
17. The system will then push the necessary configuration to your DIA locations.
18. Lastly, we need to tell the system where our gateway sites are located. In the event of latency or loss at the branch locations, traffic can be backhauled to a gateway location for access. Click on the cloud in the upper right corner, followed by Cloud OnRamp for SaaS (Cloud Express).
19. Click on the Manage CloudExpress button and choose Gateways.
20. Click the Attach Gateways button.
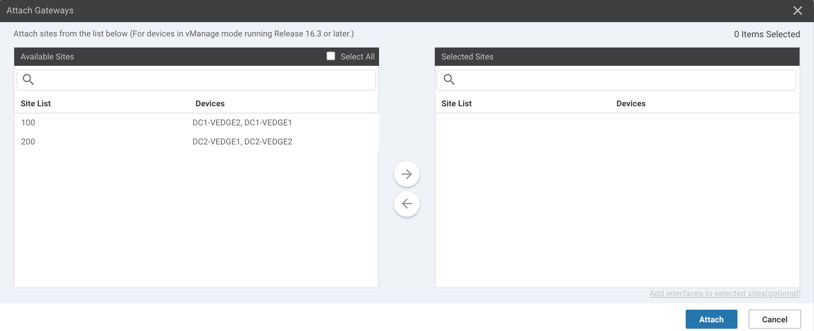
21. Select your two Data Center Site IDs and click the right arrow:
22. Click the Attach button.
23. The system will then begin provisioning the DC routers.
That’s it!
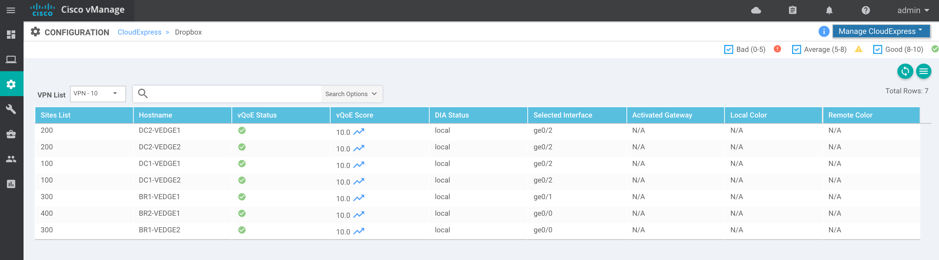
Now, let's monitor your new application. After giving the system a few minutes to begin polling the SaaS application, head back to the main Cloud onRamp for SaaS dashboard (click on the cloud in the upper right corner, followed by Cloud OnRamp for SaaS). Notice that your application now has a vQoE score (vQoE, or Quality of Experience, is a measurement between 1 and 10 that rates the performance of an application over the given transports):
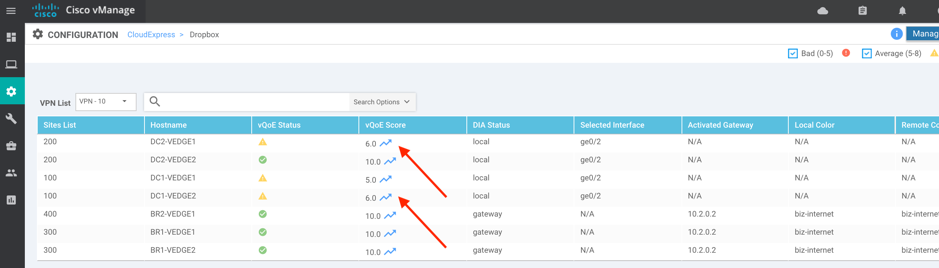
Clicking on the application will pull up additional information (choose VPN – 10 from the VPN List dropdown):
Clicking on the relative vQoE scores will show you how the application has performed historically. In our case, the DC routers aren’t performing quite as well as the Branch routers:
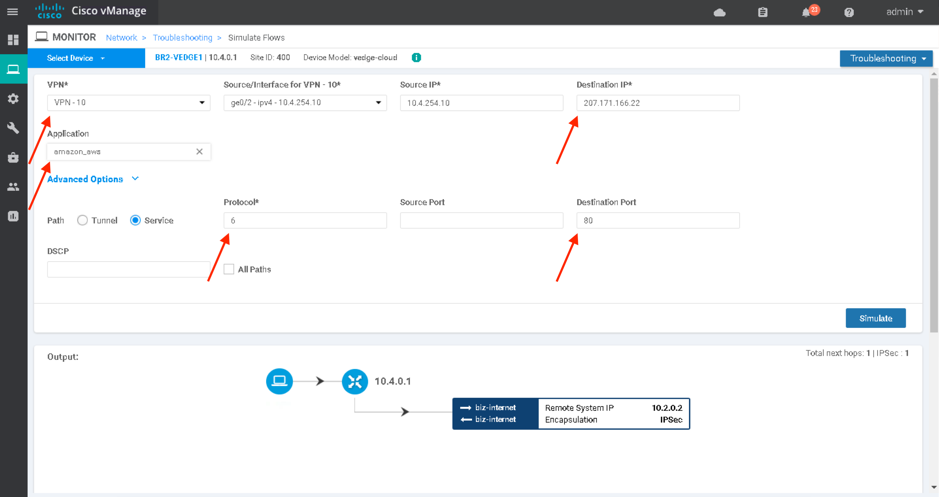
Lastly (optional), you can use the Simulate Flows tool (Device Dashboard, Troubleshooting, Simulate Flows) on each vEdge to see exactly where a router would forward this traffic at any given moment:
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
This is very useful explanation thank you for the details.
I have a question about the LAN routing for a potential DIA location:
In this location I have 2 x CE routers , each one has an MPLS link (primary and secondary)
There is a VSS CORE switch that has an eBGP relationship with both CEs
Now I want to introduce a vEdge with an enterprise internet link, and I want to use it for DIA and Cloud OnRamp (CloudExpress) for this and other locations.
I could form another BGP relationship with the vEdge, but is the vEdge capable of redistributing the CloudExpress SaaS routes? So when the users in the LAN resolves any SaaS FQDN (that belongs to O365 for example) they should be routed towards the vEdge, Is this possible?
Or what are the recommendations in this case?
Thank you!
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: