Introduction
ACL to match DVMRP is not supported in NCS5500. This document describes how to use UDF to match DVMRP packets in NCS5500.
Issue
ACL to match DVMRP packets is not supported in NCS5500. Hence there is no way to match DVMRP at interface and drop/permit DVMRP packets at interface level.
RP/0/RP1/CPU0:5508-1-721(config)#ipv4 access-list block-dvmrp
RP/0/RP1/CPU0:5508-1-721(config-ipv4-acl)#10 deny igmp any any dvmrp <<<< Commit of this config fails
RP/0/RP1/CPU0:5508-1-721(config-ipv4-acl)#20 permit ipv4 any any
RP/0/RP1/CPU0:5508-1-721(config-ipv4-acl)#int hu 0/0/0/0
RP/0/RP1/CPU0:5508-1-721(config-if)#ipv4 access-group block-dvmrp egress
RP/0/RP1/CPU0:5508-1-721(config-if)#commit
Thu Sep 3 10:04:10.737 PDT
% Failed to commit one or more configuration items during a pseudo-atomic operation. All changes made have been reverted. Please issue 'show configuration failed [inheritance]' from this session to view the errors
RP/0/RP1/CPU0:5508-1-721(config-if)#show config failed
Thu Sep 3 10:04:17.154 PDT
!! SEMANTIC ERRORS: This configuration was rejected by
!! the system due to semantic errors. The individual
!! errors with each failed configuration command can be
!! found below.
interface HundredGigE0/0/0/0
ipv4 access-group block-dvmrp egress
!!% 'dpa_feat_mgr' detected the 'warning' condition 'Match type of IGMP options not supported'
!
end
Solution
UDF can be used to match the DVMRP packets in NCS5500 to match and permit/drop it at the ingress interface.
Packet with DVMRP header:
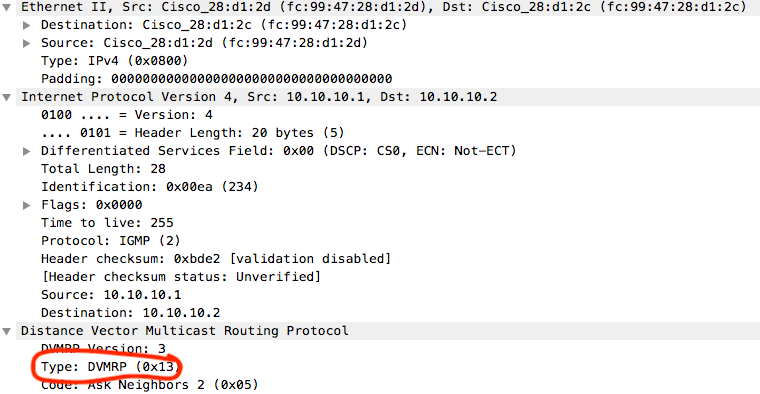
0000 fc 99 47 28 d1 2c fc 99 47 28 d1 2d 08 00 45 00
0010 00 1c 00 ea 00 00 ff 02 bd e2 0a 0a 0a 01 0a 0a
0020 0a 02 13 05 e8 e4 00 0a 04 0c 00 00 00 00 00 00 <<< Packet type DVMRP
0030 00 00 00 00 00 00 00 00 00 00 00 00
To match DVMRP packets we can match the type field in IGMP header(L4). The first byte of IGMP header here is 0x13. Hence we need to match L4, 0x13 to match DVMRP packet.
Configuration
udf udf_dvmrp header outer l4 offset 0 length 1 >>> Configure UDF, Match offset 0 or L4 header with length 1 B
hw-module profile tcam format access-list ipv4 src-addr dst-addr proto frag-bit udf1 udf_dvmrp >>> Configure UDK, Reload router/LC after this
ipv4 access-list UDF_DVMRP
10 deny igmp any any udf udf_dvmrp 0x13 0xff >>>> Match for 0x13 and protocol IGMP
20 permit ipv4 any any
!
interface Bundle-Ether31000
ipv4 address 1.1.1.2 255.255.255.0
ipv4 access-group UDF_DVMRP ingress >>>>> Apply ACL
!
RP/0/RP0/CPU0:xrg-307-NCS-5501-SE#show access-lists ipv4 UDF_DVMRP hardware ingress location 0/0/CPU0
Thu Sep 3 23:20:03.056 UTC
ipv4 access-list UDF_DVMRP
10 deny igmp any any (1799642834 matches) >>>>> DVMRP packets matching
20 permit ipv4 any any
RP/0/RP0/CPU0:xrg-307-NCS-5501-SE#show access-lists ipv4 UDF_DVMRP hardware ingress det location 0/0/CPU0
Thu Sep 3 23:20:17.486 UTC
UDF_DVMRP Details:
Sequence Number: 10
NPU ID: 0
Number of DPA Entries: 1
ACL ID: 1
ACE Action: DENY
ACE Logging: DISABLED
ABF Action: 0(ABF_NONE)
Hit Packet Count: 1819195451 >>>>> DVMRP packet hit
UDF Entries:
1: udf_dvmrp: 0x13 (mask: 0xff)
DPA Entry: 1
Entry Index: 0
DPA Handle: 0x8CD870A8
Sequence Number: 20
NPU ID: 0
Number of DPA Entries: 1
ACL ID: 1
ACE Action: PERMIT
ACE Logging: DISABLED
ABF Action: 0(ABF_NONE)
DPA Entry: 1
Entry Index: 0
DPA Handle: 0x8C4FBAC8
Sequence Number: IMPLICIT DENY
NPU ID: 0
Number of DPA Entries: 1
ACL ID: 1
ACE Action: DENY
ACE Logging: DISABLED
ABF Action: 0(ABF_NONE)
Hit Packet Count: 0
DPA Entry: 1
Entry Index: 0
DPA Handle: 0x8C4FC4E8
The stats for "permit any any" will not work with above configuration. Please configure "hw-module profile stats acl-permit" to enable the stats for permit.
Important Links
UDF: https://xrdocs.io/ncs5500/tutorials/user-defined-field-ncs55xx-and-ncs5xx/