The Cisco Document Team has posted an article. This document describes how to configure and verify Service Chaining to inspect traffic across different VRF. Know of something that needs documenting? Share a new document request...
Networking Knowledge Base
- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
-
Announcements
(40) -
AppDynamics
(15) -
Assurance and Policy
(29) -
Automation
(45) -
Buying Recommendation
(16) -
Catalyst 2000
(27) -
Catalyst 3000
(43) -
Catalyst 4000
(87) -
Catalyst 6000
(233) -
Catalyst 8000
(26) -
Catalyst 9000 Switches
(86) -
Catalyst Switch
(68) -
Cisco Annual Internet Report
(7) -
Cisco Catalyst Center
(3) -
Cisco Digital Network Architecture-DNA
(63) -
Cisco DNA
(96) -
Cisco DNA Assurance
(48) -
Cisco DNA Automation
(79) -
Cisco DNA Center
(119) -
Cisco DNA Center Upgrades
(8) -
Cisco DNA Cloud
(16) -
Cisco ENCS
(18) -
Cloud
(2) -
Cloud Networking
(28) -
Configuration
(70) -
CSC Highly Restricted Content for CAP
(3) -
EEM Scripting
(243) -
Getting Started with LANs
(1) -
IPv6
(25) -
IPv6 Configuration
(79) -
LAN
(62) -
LAN Switching
(180) -
Meraki Switch
(13) -
Network Management
(344) -
NFVIS
(23) -
Optical Networking
(33) -
Other Collaboration Topics
(1) -
Other IPv6
(28) -
Other Network Architecture
(79) -
Other Network Infrastructure Subjects
(2) -
Other Networking
(459) -
Other Networking Topics
(1) -
Other Routers
(118) -
Other Routing
(447) -
Other SD-WAN
(60) -
Other Service Providers
(1) -
Other Switches
(93) -
Other Switching
(785) -
Routing
(130) -
Routing Protocols
(298) -
Sales Resources
(1) -
SD-Access
(98) -
SD-Access Troubleshooting
(62) -
SD-WAN
(104) -
Service Providers
(13) -
Software Upgrades
(9) -
SP Mobility
(1) -
SP Video
(1) -
TAC Doc DNA
(11) -
TAC Doc LAN Switching
(44) -
TAC Doc NMS
(12) -
TAC Doc Notice
(5) -
TAC Doc Routing
(25) -
TAC Doc SDWAN
(64) -
ThousandEyes
(17) -
Tools
(1) -
Training
(1) -
vEdge Routers
(42) -
VNI and GCI
(15) -
WAN
(66) -
WAN Routing and Switching
(2) -
Wi-Fi 6
(17) -
Wireless and Mobility
(1)
- « Previous
- Next »
Knowledge Base Articles
The Cisco Document Team has posted an article. This document describes how to configure and monitor upstream and downstream bandwidth utilization on a transport interface on vEdge routers. Know of something that needs documenti...
The Cisco Document Team has posted an article. This document describes how to configure and verify Administrative Distance (AD) on default routes received via DHCP. Know of something that needs documenting? Share a new document...
The sheer number of bits in an IPv6 address can make IPv6 subnetting intimidating at best. With the addition of a new addressing scheme it's easy to get lost trying to break up your brand new /48 address across your enterprise.The New Boss, Same as t...
ResolutionYou can analyze network traffic passing through ports by using Switched Port Analyzer (SPAN). This sends a copy of the traffic to another port on the switch that has been connected to a SwitchProbe device, another Remote Monitoring (RMON) p...
Gigabit Ethernet is a widespread networking standard, but a question often arises: does it support the legacy half-duplex mode of communication? Let's break down the technical details.What is Half-Duplex and Full-Duplex?Half-Duplex: In a half-duplex ...
MPLS LAYER-3 VPN IntroductionVirtual Routing and Forwarding (VRF)MP-BGP (Multi-protocol BGP)RD (Route Distinguisher)RT (Route Target)Transport and VPN LabelMP...
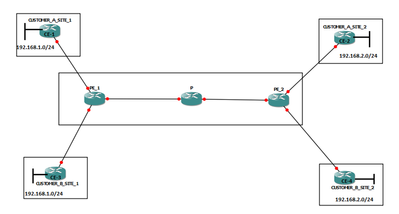
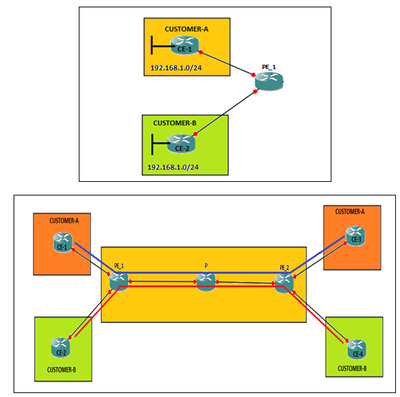

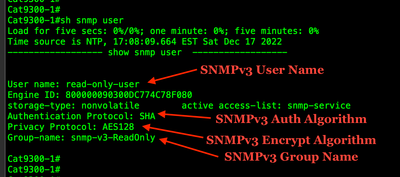
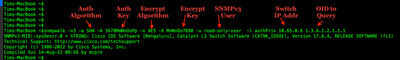
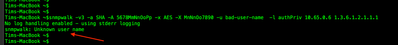
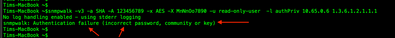
Table of Contents Table of ContentsAutomationSummaryTerminologySecurity LevelsSupportConfiguration StepsCreate an SNMP Poller Access ListCreate SNMP ViewsCreate SNMP GroupsCreate Read-Only SNMP UsersCreate Read-Write SNMP UsersFrequently Used OIDsVer...
This document is editable by everyone. If you know of an OID, please add it. If one is incorrect, please correct it and add notes.Monitoring CPU on Routers1.3.6.1.4.1.9.2.1.58.0Monitoring Memory on Routers1.3.6.1.4.1.9.9.48.1.1.1.6.1PIX/ASA/FWSMSyste...
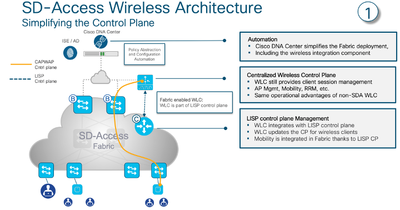
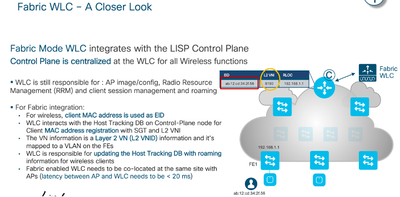
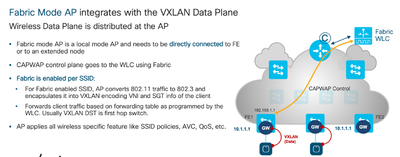
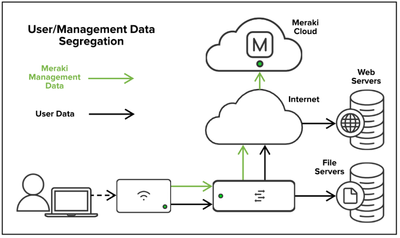
IntroductionValidated DesignTraffic Flow in Cisco Wireless SD-Access solutionMeraki Wireless Design FundamentalMeraki Device-to-Cloud CommunicationsLab SetupConfigurationValidation Introduction With the evolution of software defined networking (SD...
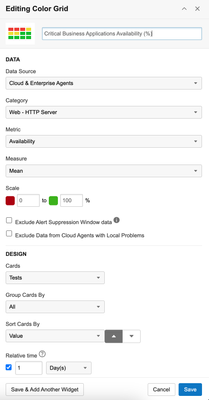
General Overview In today's fast-evolving business environment, executives heavily depend on data-driven insights to make prompt and well-informed decisions. Executive reporting plays a pivotal role, offering immediate access to crucial key perfor...



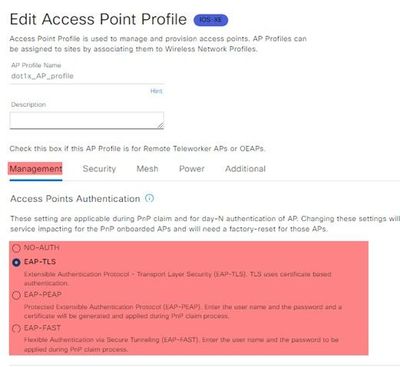
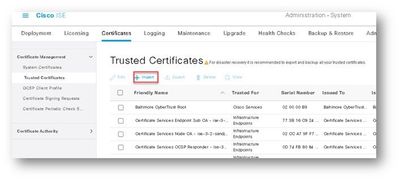
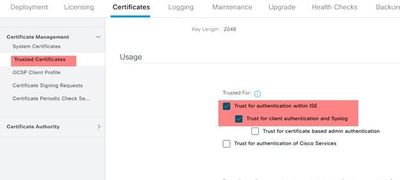
Introduction: Catalyst Center's release 2.2.3 marked the introduction of the Secure AP Onboarding feature, a significant advancement for network administrators seeking robust security measures. This feature facilitates the seamless integration of ac...

VRF LITEVRF Lite is a simplified version of VRF that uses only IP routing, while the full version of VRF can support multiple routing protocols like OSPF and BGP.VR...
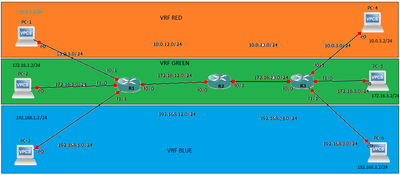
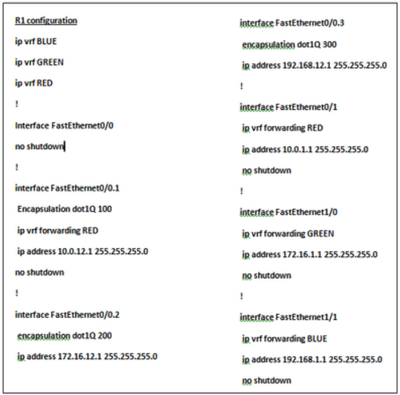

Virtual Routing and Forwarding (VRF)VRF is the abbreviation of Virtual Routing and Forwarding. Basically, VRF is a technology with which we can create separate virtual routers on...
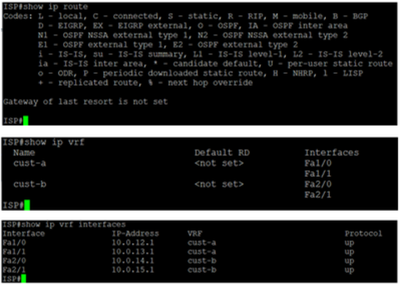
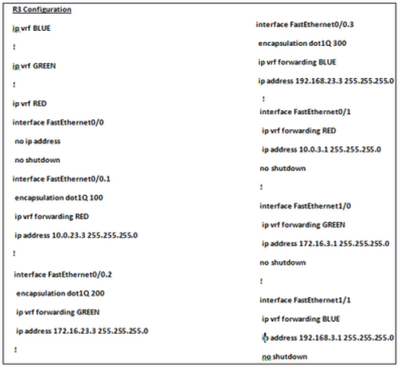
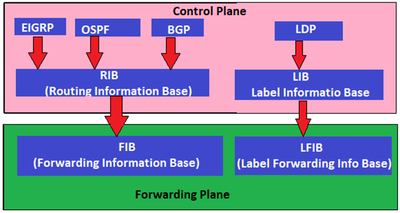
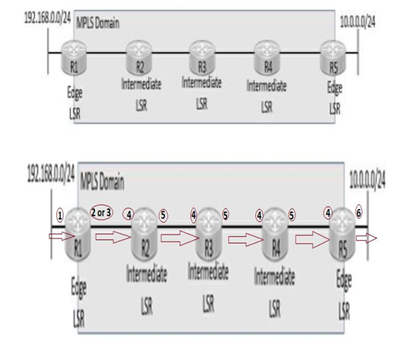
Multi-Protocol Label Switching (MPLS)First....Why we need MPLS ?In the above example, we have an example of an ISP with two customers “A” & “B”. The ISP only offers internet co...

Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:
-
TCC_2
 Level 10
Level 10 -
kadsteph
 Cisco Employee
Cisco Employee -
 Mohamed Alhenawy
Spotlight
Mohamed Alhenawy
Spotlight -
ashirkar
 Level 7
Level 7 -
tepatel
 Cisco Employee
Cisco Employee -
kramesh
 Cisco Employee
Cisco Employee -
SunilKhanna
 Level 1
Level 1 -
Sivagami Narayanan
 Level 1
Level 1 -
somgupta
 Level 1
Level 1 -
InayathUlla Sharieff
 Cisco Employee
Cisco Employee -
Adam Casella
 Level 1
Level 1 -
CscTsWebDocsCommunity Member
-
ciscomoderator
 Community Manager
Community Manager -
Pulkit Nagpal
 Cisco Employee
Cisco Employee -
 Marwan ALshawi
VIP Alumni
Marwan ALshawi
VIP Alumni -
Cisco Moderador
 Community Manager
Community Manager -
Tim Glen
 Cisco Employee
Cisco Employee -
chyan
 Cisco Employee
Cisco Employee -
ekhabaro
 Cisco Employee
Cisco Employee -
pbagga
 Cisco Employee
Cisco Employee -
vladimirsimic
 Level 1
Level 1 -
Andrew Gossett
 Cisco Employee
Cisco Employee -
Julie Burruss
 Level 4
Level 4 -
kthiruve
 Cisco Employee
Cisco Employee -
 CiscoNet Training Solutions
Spotlight
CiscoNet Training Solutions
Spotlight -
ITA TermsCommunity Member
-
Chieh Yu
 Cisco Employee
Cisco Employee -
Maher Abdelshkour
 Level 7
Level 7 -
Yogesh Ramdoss
 Cisco Employee
Cisco Employee -
teegeorg
 Cisco Employee
Cisco Employee -
 Leo Laohoo
Hall of Fame
Leo Laohoo
Hall of Fame -
dbellamk
 Cisco Employee
Cisco Employee -
Emmanuel Tychon
 Cisco Employee
Cisco Employee -
plumbis
 Level 7
Level 7 -
Joe Clarke
 Cisco Employee
Cisco Employee -
 Collin Clark
VIP Alumni
Collin Clark
VIP Alumni -
erazvi
 Cisco Employee
Cisco Employee -
jeaves@cisco.co
m  Cisco Employee
Cisco Employee -
Vignesh Rajendran Praveen
 Cisco Employee
Cisco Employee -
Svetlana Radzevich
 Cisco Employee
Cisco Employee -
Phillip Remaker
 Cisco Employee
Cisco Employee -
 Meddane
VIP
Meddane
VIP -
Hilda Arteaga
 Cisco Employee
Cisco Employee -
MANISH Yadav
 Level 1
Level 1 -
Amit Sharma
 Cisco Employee
Cisco Employee -
Timothy Glen
 Cisco Employee
Cisco Employee -
thomas
 Cisco Employee
Cisco Employee -
Mohamed Anees Mohammed Abdulla
 Level 1
Level 1 -
zxcdsf06647
 Level 1
Level 1 -
Travis WilliamsCommunity Member
-
Anna Komarovska
 Cisco Employee
Cisco Employee -
JasperJamal4283
5  Level 1
Level 1 -
asofrani
 Cisco Employee
Cisco Employee -
tokunath
 Cisco Employee
Cisco Employee -
mtimm
 Cisco Employee
Cisco Employee -
arohyans
 Cisco Employee
Cisco Employee -
Thamaraiselvam Santhanam
 Level 1
Level 1 -
bvemula
 Cisco Employee
Cisco Employee -
akeswani
 Cisco Employee
Cisco Employee -
ranraju
 Cisco Employee
Cisco Employee -
Kureli Sankar
 Cisco Employee
Cisco Employee -
vasco2009Community Member
-
svemulap@cisco.
com  Cisco Employee
Cisco Employee -
thulsdau
 Cisco Employee
Cisco Employee -
pevaneyn
 Cisco Employee
Cisco Employee -
sandjose
 Cisco Employee
Cisco Employee -
infoCommunity Member
-
Santosh Sharma
 Cisco Employee
Cisco Employee -
Aleksandar Vidakovic
 Cisco Employee
Cisco Employee -
pkhilola
 Cisco Employee
Cisco Employee -
Santosh Shetty
 Level 1
Level 1 -
hadhaliw
 Cisco Employee
Cisco Employee -
Rodney Dunn
 Cisco Employee
Cisco Employee -
 Gopinath_Pigili
Spotlight
Gopinath_Pigili
Spotlight -
Victor Acevedo
 Cisco Employee
Cisco Employee -
 siskum
Spotlight
siskum
Spotlight -
Shawn FordCommunity Member
-
Souvik Ghosh
 Cisco Employee
Cisco Employee -
 Masoud Pourshabanian
VIP Alumni
Masoud Pourshabanian
VIP Alumni -
faylee
 Cisco Employee
Cisco Employee -
Richard Primm
 Cisco Employee
Cisco Employee -
rsilviu
 Cisco Employee
Cisco Employee -
Fabrice Ducomble
 Cisco Employee
Cisco Employee -
Vinit Jain
 Cisco Employee
Cisco Employee -
derek-shnosh
 Level 1
Level 1 -
Eric MitchellCommunity Member
-
almuench
 Cisco Employee
Cisco Employee -
Colby Beam
 Cisco Employee
Cisco Employee -
ldanny
 Cisco Employee
Cisco Employee -
Karthik Kumar Thatikonda
 Cisco Employee
Cisco Employee -
Ashley PriceCommunity Member
-
jpl861
 Level 4
Level 4 -
rsaville@cisco.
com  Cisco Employee
Cisco Employee -
 Szombatfalvi Hunor
Spotlight
Szombatfalvi Hunor
Spotlight -
kaannadu
 Level 1
Level 1 -
Dennis McLaughlin
 Cisco Employee
Cisco Employee -
Brand4480
 Level 1
Level 1 -
sunikris
 Cisco Employee
Cisco Employee -
 Deepak Kumar
VIP Alumni
Deepak Kumar
VIP Alumni -
okumar
 Cisco Employee
Cisco Employee -
 M02@rt37
VIP
M02@rt37
VIP -
Vinod Arya
 Cisco Employee
Cisco Employee -
brharden
 Level 1
Level 1 -
James D Hensley
 Cisco Employee
Cisco Employee -
Randeep Singh
 Cisco Employee
Cisco Employee -
Jay Young
 Cisco Employee
Cisco Employee -
 Bilal Nawaz
VIP Alumni
Bilal Nawaz
VIP Alumni -
 Abdu
Spotlight
Abdu
Spotlight -
alanssie
 Cisco Employee
Cisco Employee -
jawestbrCommunity Member
-
MUHAMMAD TAYYAB MUNIR
 Level 1
Level 1 -
Mani Ganesan
 Level 4
Level 4 -
Janel Kratky
 Cisco Employee
Cisco Employee -
Huan NguyenCommunity Member
-
Salman Asadullah
 Cisco Employee
Cisco Employee -
jiksCommunity Member
-
Anim Saxena
 Level 1
Level 1 -
parkjaehyunCommunity Member
-
mtsb
 Level 1
Level 1 -
jedolphi
 Cisco Employee
Cisco Employee -
Monica Lluis
 Level 9
Level 9 -
sarahanand
 Level 1
Level 1 -
yicliu
 Cisco Employee
Cisco Employee -
pramod
 Level 1
Level 1 -
Roman Rodichev
 Level 7
Level 7 -
sakella
 Level 1
Level 1 -
cpartsenidis
 Level 1
Level 1 -
claudiu.tudorasCommunity Member
-
mmanusan
 Cisco Employee
Cisco Employee -
HashamM
 Cisco Employee
Cisco Employee -
Ivan Shirshin
 Cisco Employee
Cisco Employee -
EllaRichardsonCommunity Member
-
Brandon Lynch
 Cisco Employee
Cisco Employee -
routerscisco12
 Level 1
Level 1 -
Rajat Chauhan
 Cisco Employee
Cisco Employee -
asdvads vwe
 Level 1
Level 1 -
krunal_shah
 Level 1
Level 1 -
Luis Villanueva
 Cisco Employee
Cisco Employee -
kousaku345
 Level 1
Level 1 -
Eric Yu
 Level 1
Level 1 -
kg.pramodCommunity Member
-
fengwm1202
 Level 1
Level 1 -
roor
 Cisco Employee
Cisco Employee -
Andrew Yourtchenko
 Cisco Employee
Cisco Employee -
tshah
 Cisco Employee
Cisco Employee -
Chandhuru sekaran marimuthu
 Level 1
Level 1 -
Akshay Kaul
 Cisco Employee
Cisco Employee -
krun_shah
 Level 1
Level 1 -
cjaffree2Community Member
-
gabriel.ybarra
 Level 1
Level 1 -
krisgovi
 Cisco Employee
Cisco Employee -
James Murray Curtis
 Level 1
Level 1 -
ahmed.gadi
 Level 1
Level 1 -
Carlos Villagran
 Cisco Employee
Cisco Employee -
stanti
 Cisco Employee
Cisco Employee -
duyeager
 Cisco Employee
Cisco Employee -
hcaldwel
 Cisco Employee
Cisco Employee -
Luc De Ghein
 Cisco Employee
Cisco Employee -
asholomo
 Cisco Employee
Cisco Employee -
melaniemaillet
 Level 1
Level 1 -
Raphael Wouters
 Cisco Employee
Cisco Employee -
Viral Bhutta
 Cisco Employee
Cisco Employee -
alexiflo
 Cisco Employee
Cisco Employee -
Sonal Singh
 Cisco Employee
Cisco Employee -
adaguila
 Cisco Employee
Cisco Employee -
Sakun Sharma
 Level 1
Level 1 -
wzhang
 Cisco Employee
Cisco Employee -
Furose M
 Level 3
Level 3 -
glgersc
 Level 1
Level 1 -
sathvik k v
 Level 3
Level 3 -
Dilip Kumar Pandey
 Level 1
Level 1 -
 Dennis Mink
VIP Alumni
Dennis Mink
VIP Alumni -
Karthik B V
 Level 1
Level 1 -
Rachna Lal
 Level 1
Level 1 -
Omar Santos
 Cisco Employee
Cisco Employee -
benedict dcunha
 Level 1
Level 1 -
nivmanoh
 Cisco Employee
Cisco Employee -
Vivien Chia
 Community Manager
Community Manager -
inderdeepsingh1
 Level 1
Level 1 -
 Seb Rupik
VIP Alumni
Seb Rupik
VIP Alumni -
inderdeeps
 Level 4
Level 4 -
Rama Darbha
 Level 1
Level 1 -
expertadvisor20
151  Level 1
Level 1 -
Gerald C. Paciello
 Level 1
Level 1 -
dshornstein
 Level 1
Level 1 -
cisco_admin1
 Level 3
Level 3 -
abfentan
 Cisco Employee
Cisco Employee -
Jonathan Cuthbert
 Cisco Employee
Cisco Employee -
 tellis002
Spotlight
tellis002
Spotlight -
oharcour
 Cisco Employee
Cisco Employee -
Samer R. Saleem
 Level 4
Level 4 -
Kewal Agarwal
 Cisco Employee
Cisco Employee -
traimen
 Level 1
Level 1 -
aeguiart
 Cisco Employee
Cisco Employee -
Shelley Bhalla
 Level 3
Level 3 -
ramakkr2
 Cisco Employee
Cisco Employee -
migcerva
 Cisco Employee
Cisco Employee -
abhijit379
 Level 1
Level 1 -
 Ganesh Hariharan
VIP Alumni
Ganesh Hariharan
VIP Alumni -
vnazarov
 Cisco Employee
Cisco Employee -
rvkcisco1
 Level 1
Level 1 -
wang xianglun
 Level 1
Level 1 -
toholt
 Cisco Employee
Cisco Employee -
Vasilii Mikhailovskii
 Level 7
Level 7 -
Takashi Higashimura
 Cisco Employee
Cisco Employee -
jlafuent
 Cisco Employee
Cisco Employee -
Ashish Arora
 Level 1
Level 1 -
Xavier Hick
 Level 1
Level 1 -
Roberto CruzCommunity Member
-
hailin huang
 Level 1
Level 1 -
snottontour
 Level 1
Level 1 -
anaiyar
 Level 1
Level 1 -
yocfloreCommunity Member
-
Kamden Schewitz
 Cisco Employee
Cisco Employee -
Vladimir.Timkin
 Level 1
Level 1 -
Tomas de Leon
 Cisco Employee
Cisco Employee -
Jay Tiwari
 Cisco Employee
Cisco Employee -
abdeabdu@cisco.
com  Cisco Employee
Cisco Employee -
Tiago Santos da Silva
 Cisco Employee
Cisco Employee -
Kavin Patel
 Level 1
Level 1 -
Berenice Guerra
 Cisco Employee
Cisco Employee -
youness hafid
 Level 1
Level 1 -
efrahim
 Level 4
Level 4 -
Jurgens L
 Level 3
Level 3 -
 David Samuel Penaloza Seijas
Spotlight
David Samuel Penaloza Seijas
Spotlight -
Armando Yesua Garcia Calderon
 Cisco Employee
Cisco Employee -
Kris Thompson
 Level 1
Level 1 -
Bananaman
 Level 1
Level 1 -
burleyman
 Level 8
Level 8 -
grerose
 Level 6
Level 6 -
Kevin-RobertsCommunity Member
-
Rajan Parmar
 Cisco Employee
Cisco Employee -
mohammedrafiq
 Level 1
Level 1 -
eric.tabaldievCommunity Member
-
Patricia WestCommunity Member
-
Ehsan Momeni Bashusqeh
 Level 1
Level 1 -
stalCommunity Member
-
mavespig
 Level 3
Level 3 -
Lova RABAKO
 Level 1
Level 1 -
shooda
 Cisco Employee
Cisco Employee -
Setsuko Saito
 Cisco Employee
Cisco Employee -
Javier Portuguez
 Level 9
Level 9 -
Nitin MamgainCommunity Member
-
Christopher Stos-Gale
 Level 1
Level 1 -
Dan Frey
 Cisco Employee
Cisco Employee -
Sabina TaylorCommunity Member
-
kumarkrishnar
 Level 1
Level 1 -
chuckwilson
 Level 1
Level 1 -
abmehta
 Level 1
Level 1 -
leabell
 Cisco Employee
Cisco Employee -
Maria Palmero Amador
 Cisco Employee
Cisco Employee -
pfrascaCommunity Member
-
iliaklimov
 Level 1
Level 1 -
ankugarg
 Level 3
Level 3 -
Miguel Monterrubio
 Cisco Employee
Cisco Employee -
brunogeoffronCommunity Member
-
maheshsankpal
 Level 1
Level 1 -
nicolas.vanpope
ringhe  Level 1
Level 1 -
Pedro Garduno Dominguez
 Cisco Employee
Cisco Employee -
ataranen
 Level 1
Level 1 -
VLA_WeyBridge_2
 Level 1
Level 1 -
xevious.venegas
 Level 1
Level 1 -
matikow79
 Level 3
Level 3 -
lamav
 Level 8
Level 8 -
Matthew Blanshard
 Cisco Employee
Cisco Employee -
Patricia WendtCommunity Member
-
Paul VargheseCommunity Member
-
Neeraj Arora
 Level 3
Level 3 -
WoodsieLordShab
 Level 1
Level 1 -
Gautam Renjen
 Cisco Employee
Cisco Employee -
dipak jaiswal
 Level 1
Level 1 -
Anton Komarov
 Cisco Employee
Cisco Employee -
jaymatrona222
 Level 1
Level 1 -
Ashley Herring
 Community Manager
Community Manager -
Navanshu Sehgal
 Cisco Employee
Cisco Employee -
Andrew JudsonCommunity Member
-
Scott Bradley
 Cisco Employee
Cisco Employee -
Preston Chilcote
 Cisco Employee
Cisco Employee -
Natsuki Takeshi
 Cisco Employee
Cisco Employee -
satanovskyl
 Level 1
Level 1 -
developer001
 Level 1
Level 1 -
TestschampCommunity Member
-
15305886186Community Member
-
 Francesco Molino
VIP Alumni
Francesco Molino
VIP Alumni -
limehouse
 Level 1
Level 1 -
angumber
 Cisco Employee
Cisco Employee -
sdheer
 Cisco Employee
Cisco Employee -
ammyjhon
 Level 1
Level 1 -
prashant.pattek
ar Community Member -
Adrian Martinez
 Level 1
Level 1 -
Sarav
 Level 1
Level 1 -
baiclampCommunity Member
-
Michael Rizk
 Level 1
Level 1 -
TOM FRANCHINA
 Level 1
Level 1 -
Ichiro NaitoCommunity Member
-
networker99
 Level 1
Level 1 -
Pradeep Chaudhari
 Cisco Employee
Cisco Employee -
Francine Richards
 Level 4
Level 4 -
Michael Combs
 Cisco Employee
Cisco Employee -
szigeti
 Cisco Employee
Cisco Employee -
Jeahowan Kim
 Level 1
Level 1 -
butturwa
 Cisco Employee
Cisco Employee -
Vijaya Lakshmi
 Cisco Employee
Cisco Employee -
Didier DRIEUX
 Level 1
Level 1 -
Christopher Dreier
 Level 3
Level 3 -
Peter Paluch
 Cisco Employee
Cisco Employee -
SilmarSilveira
 Level 1
Level 1 -
Piyush PanditCommunity Member
-
INCSallen18Community Member
-
Syed Shahzad Ali
 Level 1
Level 1 -
Steven Luzynski
 Cisco Employee
Cisco Employee -
rsanchezre
 Level 1
Level 1 -
mustiman
 Level 1
Level 1 -
Himanshu Varma
 Community Manager
Community Manager -
roguep4cketCommunity Member
-
Christian Jouas
 Level 1
Level 1 -
vvasisth
 Level 1
Level 1 -
Edward Swenson
 Cisco Employee
Cisco Employee -
sughosh
 Cisco Employee
Cisco Employee -
Kevin Regan
 Cisco Employee
Cisco Employee -
renjithg
 Cisco Employee
Cisco Employee -
libxu
 Level 1
Level 1 -
Rajagopal Sivaramakrishna
n  Level 1
Level 1 -
Nadeem Ahmed
 Cisco Employee
Cisco Employee -
StephenJ DayCommunity Member
-
Manish Kumar
 Cisco Employee
Cisco Employee -
Jiess
 Level 1
Level 1 -
Matthias Falkner
 Cisco Employee
Cisco Employee -
Kelli Glass
 Community Manager
Community Manager -
siarena
 Cisco Employee
Cisco Employee -
michaelchung
 Level 1
Level 1 -
Manish Naik
 Level 1
Level 1 -
rashidsiddiqui
 Level 1
Level 1 -
msdx99011
 Level 1
Level 1 -
francisco_1
 Level 7
Level 7 -
Praveen ChigurupatiCommunity Member
-
CSCO10985840
 Level 1
Level 1 -
universal777
 Level 1
Level 1 -
Josesanchez1508
93  Level 1
Level 1 -
Kuljeet Singh Kohli
 Level 1
Level 1 -
jon.ellis
 Level 1
Level 1 -
dhhruv.arya
 Level 1
Level 1 -
dennispoulsenCommunity Member
-
Gabriela Godoi do Prado
 Community Manager
Community Manager -
HatemCisco2010
 Level 1
Level 1 -
 Mark Malone
VIP Alumni
Mark Malone
VIP Alumni -
Masato Koizumi
 Cisco Employee
Cisco Employee -
Ronit Bhattacharjee
 Level 1
Level 1 -
Narayan Subramanian
 Cisco Employee
Cisco Employee -
referinfo
 Level 1
Level 1 -
SUTHERLAND GLOBAL SERVICES SGS
 Level 1
Level 1 -
mustapha.chaab_
2  Level 1
Level 1 -
robhugh
 Cisco Employee
Cisco Employee -
dmitry911Community Member
-
Rajeev Sharma
 Cisco Employee
Cisco Employee -
mishao
 Level 1
Level 1 -
rsimoni
 Cisco Employee
Cisco Employee -
frangar2Community Member
-
pt_wang
 Level 1
Level 1 -
Adrian Jimenez
 Cisco Employee
Cisco Employee -
Mohit Chauhan
 Level 1
Level 1 -
firemtngems
 Level 1
Level 1 -
ashu_genius
 Level 1
Level 1 -
Luca Pecchiari
 Level 1
Level 1 -
vdadlaney
 Level 1
Level 1 -
Madhukrishnan Gopinathan Nair
 Level 7
Level 7 -
Sumant Mali
 Cisco Employee
Cisco Employee -
dzacks
 Cisco Employee
Cisco Employee -
cslefort
 Level 1
Level 1 -
Francisco Palomares
 Level 1
Level 1 -
vishal4444
 Level 1
Level 1 -
Jason Kunst
 Cisco Employee
Cisco Employee -
essa.anas
 Level 1
Level 1 -
gosekar
 Cisco Employee
Cisco Employee -
Jae Hak Kim
 Cisco Employee
Cisco Employee -
KushakeivCommunity Member
-
convmsCommunity Member
-
 josimaru85
Spotlight
josimaru85
Spotlight -
dimplejaral
 Level 1
Level 1 -
liuliang_dc
 Level 1
Level 1 -
Lucas Rojan
 Level 1
Level 1 -
Satish Chandran
 Cisco Employee
Cisco Employee -
e.shik_i-teco
 Level 1
Level 1 -
Richard Michael
 Cisco Employee
Cisco Employee -
manfernandez
 Level 1
Level 1 -
smcisco
 Level 1
Level 1 -
daniel.dib
 Level 7
Level 7 -
Ian Cowley
 Level 1
Level 1 -
Jay Johnston
 Cisco Employee
Cisco Employee -
yingshen
 Level 1
Level 1 -
michelle.m.mCommunity Member
-
Amin Shahabuddin
 Cisco Employee
Cisco Employee -
shantanu.muniCommunity Member
-
mnagired
 Cisco Employee
Cisco Employee -
nesimmonCommunity Member
-
zeroho0815Community Member
-
rjain5
 Cisco Employee
Cisco Employee -
josecesp
 Level 1
Level 1 -
leepeiwai
 Level 1
Level 1 -
lfriedma
 Cisco Employee
Cisco Employee -
Omer RajaCommunity Member
-
tahirshabbirCommunity Member
-
gnyeki001
 Level 1
Level 1 -
Jacopo Belcredi
 Level 1
Level 1 -
nbhayman1
 Level 1
Level 1 -
Ramprasath Sadasivam
 Level 1
Level 1 -
Jose Rosales
 Level 1
Level 1 -
hagbard84
 Level 1
Level 1 -
guruprasadr
 Level 7
Level 7 -
Hung Tsung Chen
 Level 1
Level 1 -
SeregaStr
 Level 1
Level 1 -
Guohua Zhang
 Level 1
Level 1 -
tmikelson
 Level 1
Level 1 -
Guided Resource Moderator
 Level 4
Level 4 -
Justin Reeve
 Level 1
Level 1 -
CSCO10993123
 Level 1
Level 1 -
mihailsolovey
 Level 1
Level 1 -
srstumpf
 Level 1
Level 1 -
babanov_nurbaCommunity Member
-
norman_hsiaoCommunity Member
-
sam_cds_cds
 Level 1
Level 1 -
Amilee San Juan
 Cisco Employee
Cisco Employee -
JBaker79530
 Level 1
Level 1 -
maheshgohilCommunity Member
-
RuuttulaCommunity Member
-
CATYO
 Level 1
Level 1 -
ATtheincredible
af  Level 1
Level 1 -
Mahmoud ShokouhiCommunity Member
-
tollom
 Cisco Employee
Cisco Employee -
Grant-Security/
Network Analyst  Level 1
Level 1 -
Soni ThakurCommunity Member
-
subhish_p
 Level 1
Level 1 -
yafli
 Cisco Employee
Cisco Employee -
DavidCloete1Community Member
-
arsalanh2000Community Member
-
rychaney
 Cisco Employee
Cisco Employee -
lindpan
 Cisco Employee
Cisco Employee -
SammyAko79750
 Level 1
Level 1 -
shrihangupta
 Level 1
Level 1 -
m.x
 Level 1
Level 1 -
polyviosmichael
ides Community Member -
sjulianscCommunity Member
-
gregoryworceste
r Community Member -
jurangel
 Cisco Employee
Cisco Employee -
aleck.sithole1
 Level 1
Level 1 -
arifdatau
 Level 1
Level 1 -
chris.smailes
 Level 1
Level 1 -
Geetanjli Sharma
 Cisco Employee
Cisco Employee -
Kundan Prasad
 Level 1
Level 1 -
csjnlcsjnl
 Level 1
Level 1 -
leandro11603Community Member
-
migrzela
 Level 3
Level 3 -
Eric Kenny
 Level 1
Level 1 -
ben.epskamp
 Level 1
Level 1 -
moonviewingjp
 Level 1
Level 1 -
mesehar
 Cisco Employee
Cisco Employee -
dwapstra
 Cisco Employee
Cisco Employee -
federico.ciuffa
rdi  Level 1
Level 1 -
LiWenbin2008
 Level 1
Level 1 -
gayviswa
 Cisco Employee
Cisco Employee -
toniinformatika
 Level 1
Level 1 -
imbashir
 Cisco Employee
Cisco Employee -
T0mTheCat
 Level 1
Level 1 -
ernelson
 Cisco Employee
Cisco Employee -
juaflor2
 Cisco Employee
Cisco Employee -
markuswirth85
 Level 1
Level 1 -
bberry
 Level 1
Level 1 -
surkv
 Cisco Employee
Cisco Employee -
DouglasJBellCommunity Member
-
kunihiko.fujii
 Level 1
Level 1 -
Oliver Gorwits
 Level 1
Level 1 -
millerdl
 Level 1
Level 1 -
vita_user
 Level 1
Level 1 -
xayavongp
 Level 1
Level 1 -
juancarlosmarti
nez  Level 1
Level 1 -
rmelumalCommunity Member
-
Ma Juner
 Level 1
Level 1 -
Larry Sullivan
 Level 3
Level 3 -
acui
 Cisco Employee
Cisco Employee -
Pavan Siripuram
 Cisco Employee
Cisco Employee -
Trevor Janssen
 Level 1
Level 1 -
Jamie Hancock
 Level 1
Level 1 -
slopes
 Level 1
Level 1 -
ZhengWeiWei8310
3  Level 1
Level 1 -
muthupriyanka
 Level 1
Level 1 -
Momodou lamin Manneh
 Level 1
Level 1 -
Ruchir Jain
 Cisco Employee
Cisco Employee -
CSCO11332572
 Level 1
Level 1 -
_wacolaco_
 Level 1
Level 1 -
Vinay Sharma
 Level 7
Level 7 -
uwantknow
 Level 1
Level 1 -
vishal_2007
 Level 1
Level 1 -
Juri Jestin
 Level 1
Level 1 -
Schoe HeCommunity Member
-
yogesh rajguru
 Level 1
Level 1 -
Pawan Gupta
 Cisco Employee
Cisco Employee -
Ty Gadberry
 Level 1
Level 1 -
Muhammad Khan
 Level 1
Level 1 -
anantbha
 Cisco Employee
Cisco Employee -
Niko1
 Level 1
Level 1 -
bolick
 Cisco Employee
Cisco Employee -
nibehlCommunity Member
-
orahman99
 Level 1
Level 1 -
whorowitz
 Level 1
Level 1 -
neleusCommunity Member
-
 moises.nisenbau
moises.nisenbaum Spotlight -
geert.nuyttens
 Level 1
Level 1 -
rob.hicks1
 Level 1
Level 1 -
vimoreno
 Cisco Employee
Cisco Employee -
Barry Landon
 Level 1
Level 1 -
styletoleeCommunity Member
-
ISE-EndpointAna
lytics-TME Community Member -
admin_faisal
 Level 1
Level 1 -
rgiorgi
 Cisco Employee
Cisco Employee -
enter_doorCommunity Member
-
koslyr000
 Level 1
Level 1 -
dabur10376004
 Level 1
Level 1 -
Kt43387
 Level 1
Level 1 -
Abdelhadi.mouss
aid Community Member -
paulanthonywill
iams  Level 1
Level 1 -
rachid1974
 Level 1
Level 1 -
manikantann
 Level 1
Level 1 -
traviwil
 Cisco Employee
Cisco Employee -
jcorbe
 Level 1
Level 1 -
hsfwm1202Community Member
-
Ludovic25120Community Member
-
mike_millerCommunity Member
-
kish05
 Level 1
Level 1 -
ksilanderCommunity Member
-
ssamiullah
 Level 1
Level 1 -
Patrick McHenry
 Level 3
Level 3 -
totardo.tobing1
1  Level 1
Level 1 -
Shameel Ummer
 Cisco Employee
Cisco Employee -
jeff slansky
 Level 1
Level 1 -
suitsdCommunity Member
-
Aleksey Engalichev
 Level 1
Level 1 -
ronaldsmithholy
cross Community Member -
jameslruderCommunity Member
-
trsandersonii
 Level 1
Level 1 -
asihkurniasari
 Level 1
Level 1 -
Kevin DeMott
 Level 1
Level 1 -
Sigeesh Sivadasan
 Level 1
Level 1 -
Anycast
 Level 1
Level 1 -
elhadjibdiallo
 Level 1
Level 1 -
ciscoroyzhang
 Level 1
Level 1 -
DW007
 Level 1
Level 1 -
zivx
 Level 1
Level 1 -
fruition3000
 Level 1
Level 1 -
Stefan Sutter
 Level 1
Level 1 -
Rouhollahkhb
 Level 1
Level 1 -
Srinivas N
 Level 1
Level 1 -
Mohammed NijamuddinCommunity Member
-
kbkim1025
 Level 1
Level 1 -
ctripoli
 Cisco Employee
Cisco Employee -
siddindia
 Level 1
Level 1 -
fhfgfdg
 Level 1
Level 1 -
Ranjan Singh
 Level 1
Level 1 -
tamu_1129
 Level 1
Level 1 -
pradeep Kumar
 Level 1
Level 1 -
David White
 Cisco Employee
Cisco Employee -
paratrooper
 Level 1
Level 1 -
Jennifer Yeung
 Cisco Employee
Cisco Employee -
donglee0728Community Member
-
kawaii00mak
 Level 1
Level 1 -
cschroeder12000Community Member
-
lidldk000
 Level 1
Level 1 -
dshiehCommunity Member
-
Prashant Sheshasayee
 Level 1
Level 1 -
jsalinasfCommunity Member
-
gemini1133
 Level 1
Level 1 -
worseoneahCommunity Member
-
Anukalp S
 Level 1
Level 1 -
Jonas_zhang
 Level 1
Level 1 -
avtsuk
 Level 1
Level 1 -
Palmen000
 Level 1
Level 1 -
Vladimir Saliy
 Level 1
Level 1 -
p.maillot
 Level 1
Level 1 -
mgoodlingCommunity Member
-
Steiner_roman_2Community Member
-
dellpe741
 Level 1
Level 1 -
990@Cisco
 Level 1
Level 1 -
suntongmengmoCommunity Member
-
Saurabh Shrivastava
 Cisco Employee
Cisco Employee -
BonYeol Gu
 Level 1
Level 1 -
 Oleg Volkov
Spotlight
Oleg Volkov
Spotlight -
speakerperez
 Level 1
Level 1 -
dmifly.chuang
 Level 1
Level 1 -
10MillionCommunity Member
-
sdavids5670
 Level 2
Level 2 -
bkoryus
 Level 1
Level 1 -
netcprojectCommunity Member
-
rclaus001Community Member
-
InSpaceDude
 Level 1
Level 1 -
kyeonghoKIM3388
0  Level 1
Level 1 -
rhub
 Level 1
Level 1 -
joseph
 Level 1
Level 1 -
preetpeethambar
an  Level 1
Level 1 -
bird74702002Community Member
-
LJ Gabrillo
 Level 5
Level 5 -
Sam Den
 Level 1
Level 1 -
kommunikationsn
etze  Level 1
Level 1 -
metrovalparaisoCommunity Member
-
Ryan Tian
 Level 1
Level 1 -
Thedude
 Level 7
Level 7 -
BMC TECH DATA BMC TECH DATA
 Level 1
Level 1 -
nkarpysh
 Cisco Employee
Cisco Employee -
feeder392
 Level 1
Level 1 -
miimta
 Level 1
Level 1 -
Putut Wijaya
 Level 1
Level 1 -
Parthiv Shah
 Cisco Employee
Cisco Employee -
shihabcheeranth
odika Community Member -
benny6812
 Level 1
Level 1 -
sathyanarayana.
b  Level 1
Level 1 -
smickleCommunity Member
-
Shao Kuo ChengCommunity Member
-
daymo2584
 Level 1
Level 1 -
vinodk_gupta
 Level 1
Level 1 -
jsakamotCommunity Member
-
laxman_enjapura
m10  Level 1
Level 1 -
Sergio Garrido
 Level 1
Level 1 -
natpan
 Cisco Employee
Cisco Employee -
ambtaylo
 Cisco Employee
Cisco Employee -
qin gen
 Level 1
Level 1 -
adalessandro
 Level 1
Level 1 -
kevin.hu
 Level 3
Level 3 -
mi204978
 Level 1
Level 1 -
kishorecisco
 Level 1
Level 1 -
FAbong_gersCommunity Member
-
npsangvt1Community Member
-
sanjayprajapati
sr45381  Level 1
Level 1 -
pmhlovely
 Level 1
Level 1 -
daksh_acharCommunity Member
-
anjum_ciscoCommunity Member
-
schnoor2aCommunity Member
-
juan.astudillo
 Level 1
Level 1 -
emansusiloCommunity Member
-
Mohamed Sayed
 Level 1
Level 1 -
subash3521
 Level 1
Level 1 -
ABorg815
 Level 1
Level 1 -
michaelpietzschCommunity Member
-
d_steffen
 Level 1
Level 1 -
MrMaregaTech
 Level 1
Level 1 -
stev1efaill
 Level 1
Level 1 -
marcusrayCommunity Member
-
exfat65
 Level 1
Level 1 -
voss.michael
 Level 1
Level 1 -
haijason
 Level 1
Level 1 -
cmyers1@usgs.go
v  Level 1
Level 1 -
tagee
 Level 1
Level 1 -
Maksim_Machkari
n Community Member -
subash cobi
 Level 1
Level 1 -
Hector Gustavo Serrano Gutierrez
 Cisco Employee
Cisco Employee -
emilioj.romero
 Level 1
Level 1 -
Satwinder81
 Level 1
Level 1 -
VIKASKAWADE
 Level 1
Level 1 -
tinajunjun
 Level 1
Level 1 -
Jonathancert_2
 Level 1
Level 1 -
yyokotan
 Cisco Employee
Cisco Employee -
Byungkuk.Kim
 Level 1
Level 1 -
chipshot1971Community Member
-
li-he
 Level 1
Level 1 -
gregorypierce1
 Level 1
Level 1 -
chhjain
 Cisco Employee
Cisco Employee -
wdzaxiaowei
 Level 1
Level 1 -
kechengpc
 Level 1
Level 1 -
laykomDmitry
 Level 1
Level 1 -
Vinoo
 Cisco Employee
Cisco Employee -
manojs87910
 Level 1
Level 1 -
Jananoor1Community Member
-
zhaojunling
 Level 1
Level 1 -
ncfb-awarsame
 Level 1
Level 1 -
angelidata
 Level 1
Level 1 -
carol1981Community Member
-
cuijian.vip
 Level 1
Level 1 -
netbeginner
 Level 2
Level 2 -
nmyamani
 Level 1
Level 1 -
Qumak-SekomCommunity Member
-
kathykooda
 Level 1
Level 1 -
benemaleeCommunity Member
-
JamieWilliamMee
chan Community Member -
cisco-reseller
 Level 1
Level 1 -
kian_hong2000
 Level 1
Level 1 -
bozodog69Community Member
-
pascal.vizeliCommunity Member
-
Nikita Singh
 Cisco Employee
Cisco Employee -
muimam
 Cisco Employee
Cisco Employee -
dg99
 Cisco Employee
Cisco Employee -
UWE SCHREIBERCommunity Member
-
Wayne Cromwell
 Level 1
Level 1 -
nabil_mdn1
 Level 1
Level 1 -
dmaluski-n1etyCommunity Member
-
saaj5571723Community Member
-
manoj_kspCommunity Member
-
avmega
 Level 1
Level 1 -
Akula Jyoti Lakshmi
 Level 1
Level 1 -
j.leroux
 Level 1
Level 1 -
amisuissa
 Level 1
Level 1 -
fdupontbossards
as Community Member -
nikhilshetti
 Level 1
Level 1 -
philip daly
 Level 1
Level 1 -
Nibrad.A.Mahdi
 Level 1
Level 1 -
romenawerCommunity Member
-
Bikas Pandey
 Level 1
Level 1 -
spt177
 Level 1
Level 1 -
Praveen Sharma
 Cisco Employee
Cisco Employee -
tahuja
 Cisco Employee
Cisco Employee -
Vivek V
 Cisco Employee
Cisco Employee -
Uzziel Sevilla Castillo
 Level 1
Level 1 -
mahmoodkhd
 Level 1
Level 1 -
davidcheung
 Level 1
Level 1 -
Udayashankar Subramanian S
 Cisco Employee
Cisco Employee -
smallbusiness
 Community Manager
Community Manager -
henk.sterkenCommunity Member
-
chandrakant.zil
e  Level 1
Level 1 -
anake
 Level 1
Level 1 -
pwc_mexico
 Level 1
Level 1 -
Vladimir Kachesov
 Level 1
Level 1 -
Sami Ali Saleh Ahmed
 Level 1
Level 1 -
ejrgensen
 Level 1
Level 1 -
f.b.becker
 Level 1
Level 1 -
dengguoliCommunity Member
-
vinunes
 Cisco Employee
Cisco Employee -
joealone1
 Level 1
Level 1 -
Chinh Duong
 Level 1
Level 1 -
Rajesh cisco
 Level 1
Level 1 -
Rahul Kukreja
 Level 1
Level 1 -
zhangwei7070
 Level 1
Level 1 -
mrabbiCommunity Member
-
kanmai
 Level 1
Level 1 -
divine007
 Level 1
Level 1 -
FBURRESIECCommunity Member
-
benolyndav
 Level 4
Level 4 -
Pat Gainer
 Level 1
Level 1 -
smartboy2255
 Level 1
Level 1 -
 Harish Balakrishnan
Spotlight
Harish Balakrishnan
Spotlight -
Sergio Alvares
 Level 1
Level 1 -
befekadu worku
 Level 1
Level 1 -
bhornilesh
 Level 1
Level 1 -
Javier Mor SaenzCommunity Member
-
Steev112
 Level 1
Level 1 -
brittanydrossCommunity Member
-
lcelisve
 Cisco Employee
Cisco Employee -
indrapalccna
 Level 1
Level 1 -
Waqas Karim (CCIE)
 Level 1
Level 1 -
ariesjackCommunity Member
-
tfortunato
 Level 1
Level 1 -
laurent.sulejCommunity Member
-
usmc4lifeCommunity Member
-
kyukim
 Cisco Employee
Cisco Employee -
ayacopinoCommunity Member
-
snowflys_yeh
 Level 1
Level 1 -
pankaj.upadhyay
 Level 1
Level 1 -
dcruiser14
 Level 1
Level 1 -
jkaras
 Level 1
Level 1 -
aakhter
 Cisco Employee
Cisco Employee -
fsebera
 Level 4
Level 4 -
bdrincic
 Level 1
Level 1 -
Nagendra Kumar Nainar
 Cisco Employee
Cisco Employee -
mohdayaz1981
 Level 1
Level 1 -
Ahmed Sheibani
 Level 1
Level 1 -
Rohit saurav
 Level 1
Level 1 -
Soliman Fathy
 Level 1
Level 1 -
anikjitmitraCommunity Member
-
jackson.ku
 Level 3
Level 3 -
Dusan Sladojevic
 Level 1
Level 1 -
Shivu b
 Level 1
Level 1 -
lalitmbhattCommunity Member
-
shivlu jain
 Level 5
Level 5 -
Willem de Groot
 Level 1
Level 1 -
enniog123
 Level 1
Level 1 -
robertziegerCommunity Member
-
shailesh.kshirs
agar Community Member -
thomaskhho
 Level 1
Level 1 -
marco.cordeiroCommunity Member
-
cadodd
 Cisco Employee
Cisco Employee -
fly
 Level 2
Level 2 -
zalonso1975
 Level 1
Level 1 -
Linda Waterhouse
 Level 1
Level 1 -
pgrosset
 Cisco Employee
Cisco Employee -
point.blankCommunity Member
-
miracle_david@y
ahoo.com  Level 1
Level 1 -
Daniel Vieceli
 Level 1
Level 1 -
FLKRISTIANCommunity Member
-
Lokesh Kumar Lal
 Cisco Employee
Cisco Employee -
DataCenterRatCommunity Member
-
ezhilcharu
 Level 1
Level 1 -
apanduraCommunity Member
-
Geevarghese Cheria
 Cisco Employee
Cisco Employee -
jaysidhu
 Cisco Employee
Cisco Employee -
Monica Arroyo
 Level 1
Level 1 -
vishalpatil86
 Level 1
Level 1 -
lavshanm
 Cisco Employee
Cisco Employee -
Vijayakumar Govindan
 Level 1
Level 1 -
Sudeb Das
 Level 1
Level 1 -
deepspeedCommunity Member
-
 Jon Marshall
Hall of Fame
Jon Marshall
Hall of Fame -
sksharma14426
 Level 1
Level 1 -
md_boingCommunity Member
-
ryeevani
 Cisco Employee
Cisco Employee -
vmovvaCommunity Member
-
pradeeppai36Community Member
-
janleslie
 Level 1
Level 1 -
fredluneau
 Level 1
Level 1 -
kangupta
 Cisco Employee
Cisco Employee -
cacafom
 Level 1
Level 1 -
vasu.winitCommunity Member
-
KAROLY KOHEGYI
 Level 2
Level 2 -
Chez
 Level 1
Level 1 -
Jeffrey Keown
 Cisco Employee
Cisco Employee -
sivathot
 Cisco Employee
Cisco Employee -
networkcheff
 Cisco Employee
Cisco Employee -
arslanrana
 Level 1
Level 1 -
mwillyar
 Cisco Employee
Cisco Employee -
Cesar Pinheiro Macena de Souza
 Level 1
Level 1 -
RickG2112
 Level 1
Level 1 -
andre.batisaCommunity Member
-
Mohammad Anowar Hossain Mazumder
 Level 1
Level 1 -
cisco-admin
 Level 1
Level 1 -
tjunusov
 Level 1
Level 1 -
rspllalitha123
 Level 1
Level 1 -
Lisa Latour
 Level 6
Level 6 -
Dejan Puhar
 Cisco Employee
Cisco Employee -
sumnguye
 Cisco Employee
Cisco Employee -
lespejel
 Level 3
Level 3 -
Akshay Raghoji
 Community Manager
Community Manager -
Tyler Langston
 Cisco Employee
Cisco Employee -
mperezve
 Cisco Employee
Cisco Employee -
xthuijs
 Cisco Employee
Cisco Employee -
Jose Correa
 Cisco Employee
Cisco Employee -
kkarmark
 Cisco Employee
Cisco Employee -
paul.strazza
 Level 1
Level 1 -
paulnguy
 Cisco Employee
Cisco Employee -
Peter Marchand
 Cisco Employee
Cisco Employee -
jcedrone
 Cisco Employee
Cisco Employee -
kebaldwi
 Cisco Employee
Cisco Employee -
Philip Petty
 Cisco Employee
Cisco Employee -
Ambarish Kumar
 Cisco Employee
Cisco Employee -
Utkarsh Asthana
 Cisco Employee
Cisco Employee -
pkuchina
 Cisco Employee
Cisco Employee -
nsyal
 Cisco Employee
Cisco Employee -
maksrini
 Cisco Employee
Cisco Employee -
navphili
 Cisco Employee
Cisco Employee -
padidier
 Cisco Employee
Cisco Employee -
vaganesa
 Cisco Employee
Cisco Employee -
mskouenb
 Cisco Employee
Cisco Employee -
arsasiku
 Cisco Employee
Cisco Employee -
pvijay
 Cisco Employee
Cisco Employee -
sahuja2Community Member
-
aitalia
 Cisco Employee
Cisco Employee -
droten
 Cisco Employee
Cisco Employee -
vsidhart
 Cisco Employee
Cisco Employee -
chcha
 Cisco Employee
Cisco Employee -
jim.ivers
 Level 1
Level 1 -
sharsaha
 Cisco Employee
Cisco Employee -
hshah2
 Level 1
Level 1 -
abhinav2Community Member
-
hpanigra
 Level 1
Level 1 -
rigoel
 Cisco Employee
Cisco Employee -
David Williams
 Level 1
Level 1 -
Atahar Khan
 Cisco Employee
Cisco Employee -
asalcant
 Cisco Employee
Cisco Employee -
Lucinda Witt
 Level 1
Level 1 -
csavgroup
 Level 1
Level 1 -
luoxiaolongCommunity Member
-
vivichan
 Level 1
Level 1 -
jmp780718
 Level 1
Level 1 -
savijaycs1Community Member
-
Somasundaram Jayaraman
 Cisco Employee
Cisco Employee -
pabloarturo
 Level 1
Level 1 -
contact
 Level 1
Level 1 -
Raj Pathak
 Level 1
Level 1 -
vik
 Cisco Employee
Cisco Employee -
ssiripur
 Cisco Employee
Cisco Employee -
tggugginoCommunity Member
-
svani
 Cisco Employee
Cisco Employee -
kthned
 Level 3
Level 3 -
v-pramodkgCommunity Member
- « Previous
- Next »
Learn about the new products, features, and integrations coming to the Cisco WAN + Routing portfolio this fall.