- Cisco Community
- Technology and Support
- Networking
- Other Network Architecture Subjects
- Re: IPSEC Lan to Lan to Internet
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2018 05:37 AM - edited 03-03-2019 08:55 AM
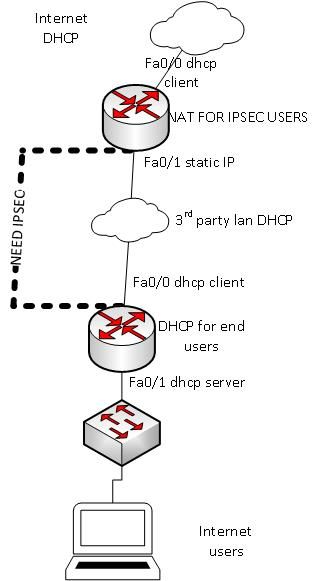
Hi I have a requirement to implement an IP-Sec service like the attached pic. Due to a 3rd party LAN that carries traffic I would like a IPSec tunnel between two routers. The end users will need internet ( NAT to say a 192.168.1.x).
Does anyone have a suitable config to suit or could point me in the right direction. The end internet users will need DHCP too.
Solved! Go to Solution.
- Labels:
-
Other Networking
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2018 07:26 AM
My final solution after days on this was to use Dynamic Multipoint IPsec VPN as described in :
https://www.cisco.com/c/en/us/support/docs/security-vpn/ipsec-negotiation-ike-protocols/41940-dmvpn.html..
I did note that there is a LOT of OLD doco out there that will not run properly on IOS 12.3 or higher for this type of stuff.
I used a mikrotik router(static) to simulate the 3rd part wan, as well as giving me an option to see the traffic live(using routeros torch!).. Thats why there are some static IP's on the interfaces(Also note the ip route statements I added to suit the testing environment )
HUB/Internet / Internal WAN Config... ( Runs on IOS v12.4 on c1841)
------------------
hostname hub
crypto isakmp policy 1
authentication pre-share
crypto isakmp key MYPASSWORD address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set trans2 esp-des esp-md5-hmac
mode transport
!
crypto ipsec profile vpnprof
set transform-set trans2
!
interface Loopback0
ip address 192.168.0.1 255.255.255.0
ip virtual-reassembly
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.1 255.255.255.0
no ip redirects
ip mtu 1400
ip nat inside
ip nhrp authentication test
ip nhrp map multicast dynamic
ip nhrp network-id 100000
ip nhrp holdtime 600
ip virtual-reassembly
no ip split-horizon eigrp 1
delay 1000
tunnel source FastEthernet0/1
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile vpnprof
!
interface FastEthernet0/0
description WAN - To Internet Connection
ip address dhcp
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
no cdp enable
!
interface FastEthernet0/1
description To 3rd party WAN
ip address 10.130.100.37 255.255.255.0
duplex auto
speed auto
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 192.168.0.0
no auto-summary
!
ip route 10.100.100.2 255.255.255.255 10.130.100.1
!
!
ip nat inside source list NAT interface FastEthernet0/0 overload
!
ip access-list extended NAT
permit ip 192.168.0.0 0.0.255.255 any
!
!
**************** SPOKE SITE(router) connected to the 3rd party WAN / TO END USERS ****************
hostname Spoke
crypto isakmp policy 1
authentication pre-share
crypto isakmp key MYPASSWORD address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set trans2 esp-des esp-md5-hmac
mode transport
!
crypto ipsec profile vpnprof
set transform-set trans2
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.2 255.255.255.0
ip mtu 1400
ip nhrp authentication test
ip nhrp map 10.0.0.1 10.130.100.37
ip nhrp network-id 100000
ip nhrp holdtime 300
ip nhrp nhs 10.0.0.1
delay 1000
tunnel source FastEthernet0/0
tunnel destination 10.130.100.37
tunnel key 100000
tunnel protection ipsec profile vpnprof
!
interface FastEthernet0/0
description WAN-Network
ip address 10.100.100.2 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
description LAN-Network to
ip address 192.168.1.1 255.255.255.0
duplex auto
speed auto
!
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 192.168.1.0
!
no ip forward-protocol nd
no ip http server
no ip http secure-server
!
!
ip route 0.0.0.0 0.0.0.0 192.168.0.1
ip route 10.130.100.37 255.255.255.255 10.100.100.1
!
ip dhcp pool EndUsers
network 192.168.1.0 255.255.255.0
default-router 192.168.1.1
dns-server 4.4.4.4
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2018 06:13 AM
Hi there,
If you are trying to secure all the clear traffic from the 'lower' site on you diagram from transiting the 3rd party LAN, then this is perfect use case for a tunnel/ "frontdoor" VRF. I wrote a blog post about it here:
https://configif.wordpress.com/2017/12/21/tunnel-vrf/
cheers,
Seb.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2018 01:49 PM
I will further investigate the tunnel/ipsec option today. That said, as its for a production environment I need to get this exact. I haven't had to do something like this before, so its a bit of a learning curve for me !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2018 05:22 AM
On the basis that the external facing interface of the lower router does not have a fixed IP address (guessing due to the use of DHCP) I would tend to head for an encrypted GRE tunnel. I have done quite a few of these in the past with Internet-based hub-&-spoke solutions, where the spokes have either fixed or variable IP addresses. I guess there could be plenty of alternative methods.
Hope this helps,
Dave
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2018 07:26 AM
My final solution after days on this was to use Dynamic Multipoint IPsec VPN as described in :
https://www.cisco.com/c/en/us/support/docs/security-vpn/ipsec-negotiation-ike-protocols/41940-dmvpn.html..
I did note that there is a LOT of OLD doco out there that will not run properly on IOS 12.3 or higher for this type of stuff.
I used a mikrotik router(static) to simulate the 3rd part wan, as well as giving me an option to see the traffic live(using routeros torch!).. Thats why there are some static IP's on the interfaces(Also note the ip route statements I added to suit the testing environment )
HUB/Internet / Internal WAN Config... ( Runs on IOS v12.4 on c1841)
------------------
hostname hub
crypto isakmp policy 1
authentication pre-share
crypto isakmp key MYPASSWORD address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set trans2 esp-des esp-md5-hmac
mode transport
!
crypto ipsec profile vpnprof
set transform-set trans2
!
interface Loopback0
ip address 192.168.0.1 255.255.255.0
ip virtual-reassembly
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.1 255.255.255.0
no ip redirects
ip mtu 1400
ip nat inside
ip nhrp authentication test
ip nhrp map multicast dynamic
ip nhrp network-id 100000
ip nhrp holdtime 600
ip virtual-reassembly
no ip split-horizon eigrp 1
delay 1000
tunnel source FastEthernet0/1
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile vpnprof
!
interface FastEthernet0/0
description WAN - To Internet Connection
ip address dhcp
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
no cdp enable
!
interface FastEthernet0/1
description To 3rd party WAN
ip address 10.130.100.37 255.255.255.0
duplex auto
speed auto
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 192.168.0.0
no auto-summary
!
ip route 10.100.100.2 255.255.255.255 10.130.100.1
!
!
ip nat inside source list NAT interface FastEthernet0/0 overload
!
ip access-list extended NAT
permit ip 192.168.0.0 0.0.255.255 any
!
!
**************** SPOKE SITE(router) connected to the 3rd party WAN / TO END USERS ****************
hostname Spoke
crypto isakmp policy 1
authentication pre-share
crypto isakmp key MYPASSWORD address 0.0.0.0 0.0.0.0
!
crypto ipsec transform-set trans2 esp-des esp-md5-hmac
mode transport
!
crypto ipsec profile vpnprof
set transform-set trans2
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.2 255.255.255.0
ip mtu 1400
ip nhrp authentication test
ip nhrp map 10.0.0.1 10.130.100.37
ip nhrp network-id 100000
ip nhrp holdtime 300
ip nhrp nhs 10.0.0.1
delay 1000
tunnel source FastEthernet0/0
tunnel destination 10.130.100.37
tunnel key 100000
tunnel protection ipsec profile vpnprof
!
interface FastEthernet0/0
description WAN-Network
ip address 10.100.100.2 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
description LAN-Network to
ip address 192.168.1.1 255.255.255.0
duplex auto
speed auto
!
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 192.168.1.0
!
no ip forward-protocol nd
no ip http server
no ip http secure-server
!
!
ip route 0.0.0.0 0.0.0.0 192.168.0.1
ip route 10.130.100.37 255.255.255.255 10.100.100.1
!
ip dhcp pool EndUsers
network 192.168.1.0 255.255.255.0
default-router 192.168.1.1
dns-server 4.4.4.4
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide