- Cisco Community
- Technology and Support
- Security
- Other Security Subjects
- Re: Static NAT command
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2019 08:19 PM
Hi,
I have been trying to understand and figure it out my self before posting here, but im unable to find a proper answer,
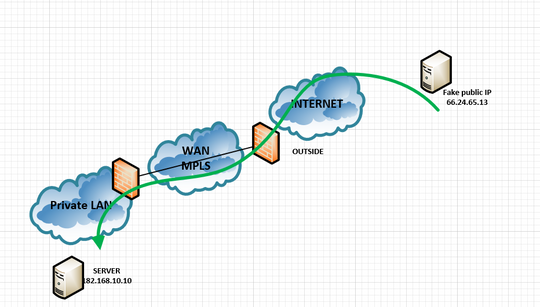
I have been reading some good docs but got more confused with Static Policy NAT and all I want is to allow a server from the outside to communicate with our internal server as the image below:
the external public server subnets (2 subnets) should communicate with the internal server over port 80
I have this config:
object-group network Public_Subnets
network-object 66.249.65.0 255.255.255.0
network-object 66.249.64.0 255.255.255.0
object network obj_priv_ip
host 192.168.10.10
object network obj_public_ip
host X.X.X.X <-------> this is my reserved public IP different from the outside interface but its available
access-list inside-in line 1 extended permit tcp host 192.168.10.10 object-group Public_Subnets eq 80
access-list outside-in line 1 extended permit tcp object-group Public_Subnets host 192.168.10.10 eq 80
nat (inside,outside) source static obj_priv_ip obj_public_ip destination object-group Public_Subnets object-group Public_Subnets no-proxy-arp route-lookup
but I get an error saying that the object does not match or does not exist when I enter the NAT statement
Im running ASA5585-SSP-20, Version 9.6(4)5
questions:
1- if its Static NAT: do I need the access list to be in place to allow it? on outside ? is itnt enough just the inside ACL?
I have seen some videos where they put simple NAT and the communication is already allowed from outside to inside, possibly Im wrong, but with static nat, do I need a firewall policy rule access list?
2- can you help me with the proper NAT command please?
is there any other way to make it much easier than the way Im trying to do it?
note: in the diagram, I put a single public fake IP from Internet, but in reality, the requirement is 2 public subnets
Solved! Go to Solution.
- Labels:
-
Other Security Topics
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-19-2019 02:05 AM
First the information you have in the description and the picture you posted not co-related at all, IP address outside and inside also.
As per my understanding you want to specific IP range to have only access to your internal IP address Web Server.
Then you need to do order below :
1. You need to map your one of your Public IP with Static NAT and ACL for your web server
2. Like example x.x.x.x - > 192.x.x.x.x ( x.x.x.x is your public IP address - not the the pool to allow)
3. Once that is working, then you need create an ACL on address range you would like to allow inside.
Example for Static NAT ( as per your picture)
access-list inbound permit tcp any host 192.168.10.10 access-group inbound in interface outside object network obj-192.168.10.10 host 192.168.10.10 nat (inside,outside) static x.x.x.x <-- replace with public IP of your network.
test and advise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-19-2019 02:05 AM
First the information you have in the description and the picture you posted not co-related at all, IP address outside and inside also.
As per my understanding you want to specific IP range to have only access to your internal IP address Web Server.
Then you need to do order below :
1. You need to map your one of your Public IP with Static NAT and ACL for your web server
2. Like example x.x.x.x - > 192.x.x.x.x ( x.x.x.x is your public IP address - not the the pool to allow)
3. Once that is working, then you need create an ACL on address range you would like to allow inside.
Example for Static NAT ( as per your picture)
access-list inbound permit tcp any host 192.168.10.10 access-group inbound in interface outside object network obj-192.168.10.10 host 192.168.10.10 nat (inside,outside) static x.x.x.x <-- replace with public IP of your network.
test and advise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2019 07:45 AM
Surely, the pic was not with the right info,
I guess I got myself very complicated cause I was trying to policy the rules access via the nat statement, but I think I can do that in the access list
the object nat did the trick, it worked for sure, but I just got a wonder why policy nat even exists if you can control that from the access list too, like if you want to permit or block a port
thanks for your help, I left it as it is with your example for now xD
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide