- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: Cisco ISE 2.1 Certificate for EAP Authenticaion
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco ISE 2.1 Certificate for EAP Authenticaion
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2018 11:43 AM - edited 02-21-2020 10:55 AM
- Labels:
-
Other NAC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2018 12:33 PM
Hi agapitca19
If I understand you post correctly then you want a non-Windows client to authenticate against Cisco ISE via Wireless Connection using some EAP protocol that us TLS (EAP-TLS, PEAP(EAP-TLS), EAP-FAST(EAP-TLS) or EAP-TTLS(EAP-TLS)).
Assuming you want to do just server side TLS authentication (and not client side TLS authentication), Now for this to work, whether it is Linux or MACOSX the Operating system need to trust the Root Certificate authority (CA) that signed the EAP Authentication certificate that exist in Cisco ISE.
Exporting the EAP Authentication certificate alone from Cisco ISE is not sufficient in fact you don't even need to export that certificate but what you need instead is to export the Root CA that signed this EAP Authentication certificate and import it under the Trusted Root Certificates under the Operating system of choice.
Procedures to import certificates under different operating systems are different and you can google it to find exact steps.
Warning: Don't ever export the Cisco ISE certificates with private key and put them in client certificate this is very insecure and technically this is called identify theft.
you should only export with private keys in case of backups and should be safely secured.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-07-2018 05:43 AM
Mohamed,
Thank you for the reply. I forgot to mention that this is for medical devices that store medical supplies. I don't know what OS they use but definitely not Windows, MACOSX, nor Linux. We want to try these medical devices to authenticate with a trusted certificate.
Exporting Root CA, is that the actual certificate that was given to us by the third party vendor when we submitted a Certificate Signing Request(CSR)?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-07-2018 11:11 PM - edited 05-07-2018 11:16 PM
Hi agapitca19
Even if the OS is not one of these operating system (Windows, MACOSX, Linux) the concept still the same even if they are running android or some variation of Unix.
The client has to trust the Root CA that have signed the EAP Authentication certificate used by ISE.
Well if this CSR was for EAP Authentication purposes (or multi-use including EAP) then it is not this certificate itself but the signer root CA of that certificate.
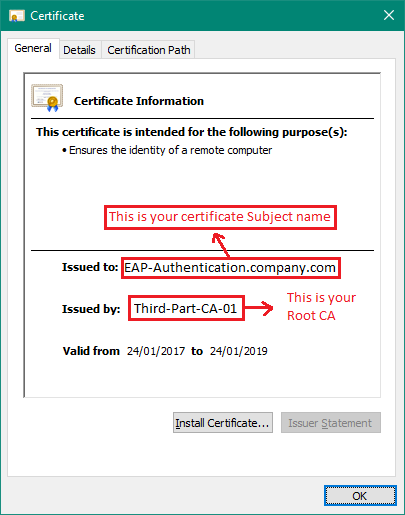
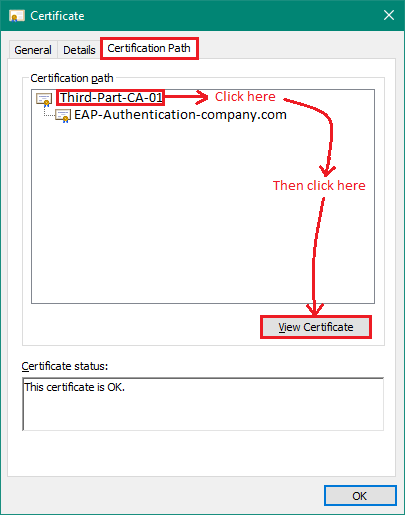
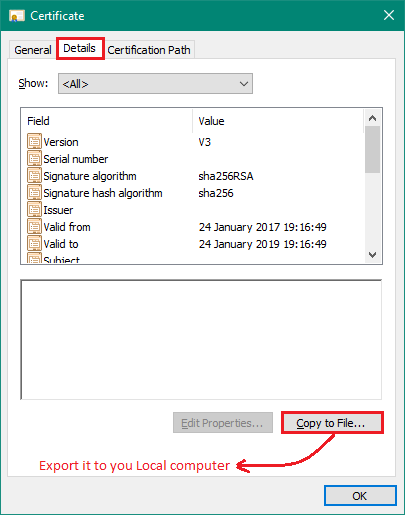
To check that if the certificate is in .cer extension (DER or Base-64 encoded) see screen shots below:
if you certificate is in .pem format then you can use OpenSSL for windows to get information (available for download from GitHub)
Mostly when they send you this certificate it would include the Root CA and any Sub-Root CA (if exists) (mostly in .p7b format) or you can simply ask the third party for the Root CA.
If your third party is a public Root CA (ex. GoDaddy or Digicert) there is a chance that your custom OS is supporting that Root CA by default (as the OS comes with a pre-installed list of public Root CAs - unless the OS is too old) and in this case the OS will automatically trust the ISE certificate with no issue.
If not then you have to manually import this root CA into these medical devices OS Root CA list or script it somehow.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: