- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Dual Internet Link load-balancing,traffic from Outside Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Dual Internet Link load-balancing,traffic from Outside Issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-26-2012 05:57 AM - edited 03-04-2019 03:01 PM
Hi All,
We deploy Cisco Router 2921 at company edge, it has two internet link connect.
Gig0/0 was Fix Public IP:219.134.186.X
Gig0/1 was connect ADSL moden, dialer0 IP was dynamic.
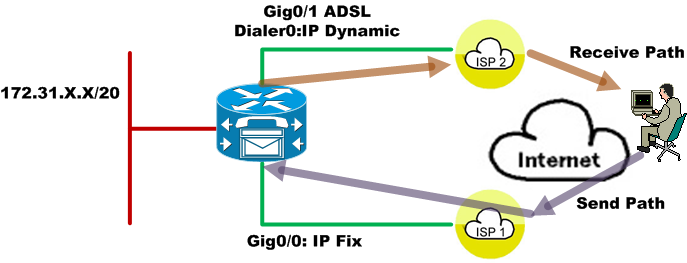
Like the topology, we configure inside traffic load balance to internet, it is work well.
But it has some issue from internet traffic to Router own interface address, If packet visit Gig0/0 Fix IP like "ping" or "ssh"
The router probable return packet from dialer0 IP.
Router seemingly can't identify the fraffic which interface ingress and egress at the same interface. situation like this the router
can't provide some service on it own address. And idear?
Some config file in attach.
----------
Rock.
- Labels:
-
Other Routing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 12:50 PM
Hi,
This evening I can't but tomorrow evening it's possible at 9 PM brussels time, just let me know or tell me which time tomorrow will suit you.
Regards.
Alain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-05-2012 05:50 AM
Hi,
If we change topo like this maybe can resolve my problem:

But i don't have test yet, theoretically i think can be done.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-30-2012 09:48 AM
Have you test it yet?
I have the same question on my network
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 04:57 AM
Mohamed,
If I configure both the interface PBR and also the ip local PBR which one would take priority?
HTH
Kishore
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 05:29 AM
Hi Kishore,
There is no Priority in this Context.
The Difference is that (Local Policy/PBR) as the name implies is local to the Router, Traffic originated by the router itself is policy based routed, While the (PBR) is a Policy that matches all datagrams hiting an interface (Incoming) Traffic that hits an interface is subject to the PBR.
Regards,
Mohamed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 05:37 AM
Hi Mohamed,
Thnks for the reply. I understand that. What I was asking was if I had both of them configured which of them will be used.
So, lets take this thread for eg: traffic is destined to the router so will the router use the policy on the interface or will it use the local policy PBR to reply back
Regards
Kishore
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 06:03 AM
Hi Kishore,
it will use the local PBR policy not the other one in this case.
Regards.
Alain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 06:36 AM
Thanks Alain. Any doco or link to point out what you mentioned. Not that I dont trust you but If I am asked by someone else then I can send them the same link
BTW, please check your PM
Regards
Kishore
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2012 12:51 PM
Hi kishore,
I'll answer you tomorrow.
Regards.
Alain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-23-2012 12:21 PM
I did Lab it up... So to speak, or needed this same function on my router, so I tested both ways:
Code : C2900-UNIVERSALK9-M), Version 15.1(4)M3
Scenario : I have a default gateway on my 2900 router through an ASA firewall. I need to be able to SSH to the router, on an external interface, but it uses the ASA for default traffic, so I can either VPN in, and then SSH or implement this work around.
Work Arround Implemented :
ip access-list extended External_Manager_Traffic
permit tcp host 30.20.10.1 eq 22 any
permit icmp host 30.20.10.1 any echo-reply
!
route-map External_Management permit 10
match ip address External_Manager_Traffic
set ip next-hop 30.20.10.2 ! ISP Gateway
!
ip route 0.0.0.0 0.0.0.0 10.31.120.254
!
interface GigabitEthernet0/1
description Sip and VPN interface
ip address 30.20.10.1 255.255.255.0
!
ip local policy route-map External_Management
I tried putting the policy-map on the gig 0/1 interface, but it didn't work. The router hasn't yet decided the traffic needs to go anywhere when it hits the interface. It then is sent to CPU and CPU uses routing table to lookup and send to default route. By Adding the Local Policy route-map we tell the CPU to apply this route map to traffic exiting the CPU. In this case we bypass the routing table and set the next hop, which triggers routing table lookup for the next hop rather than for the ultimate destination.
CCIE 6145
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-30-2012 10:03 AM
Could you paste a diagram with the IPs?
I think the outbound SSH traffic (to Internet) response don´t use the 22 port, so this traffic doesn´t match the ACL and won´t be routed through the IP 30.20.10.2 necessarily.
To develop this solution is neccessary identify the outbound traffic to create an appropiate ACL/route, o set a rule to guarantee outbound traffic (ssh response) will be forwarded through que same interface/ISP it was received (ssh request).
I´ve the same problem with a pptp VPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-30-2012 11:25 AM
ip access-list extended External_Manager_Traffic
permit tcp host 30.20.10.1 eq 22 any
permit icmp host 30.20.10.1 any echo-reply
My ACL here clearly states to permit return traffic for SSH sessions towards 30.20.10.1. It doesn't state traffic destined to 30.20.10.1 on port 22, it says RETURN Traffic
Correct version as I have it:
permit tcp host 30.20.10.1 eq 22 any
Incorrect verion as you describe wouldn't work :
permit tcp host 30.20.10.1 any eq 22
The port 22 I'm matching on is for the Source Host TCP port, not the destination host TCP port.
Its working in production using this config. I really don't have time to do a drawing. The IP addresses I've changed from production for obvious reasons.
CCIE 6145
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-30-2012 09:49 PM
I gather based on your answer using the configuration and schema attached, the return traffic (vpn response) should always go back through the router
2. Is that so?

LoadBalancer#
ip access-list extended External_VPN_access
permit tcp host 192.168.1.150 eq 1723 any
permit icmp host 192.168.1.150 any echo-reply
!
route-map External_VPN permit 10
match ip address External_VPN_access
set ip next-hop 192.168.1.101
!
ip local policy route-map External_VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-30-2012 10:20 PM
1. in your scheme, the traffic destination is not the router. so a local policy map, will never match traffic sourced from another device, even if it passes through the routrer. you would need a normal policy map on the interface. to match that traffic. remember that ip local policy map only affects traffic from the cpu of the router itself, which is why it works from SSH, to the router, but not pptp through the router.
there are many gotcha's in your design, and it is very different than the topic here. you should describe what you want to do, and what challenges you are facing with it. i dont really see that the router has much of a roll there
CCIE 6145
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-01-2012 12:18 AM
The scheme is the network that I have installed in my workplace, and currently is working perfectly except for the issue of outside access through the VPN, which I think can be solved with a normal policy map as you say. My problem is very similar to the topic.
The role of the Cisco router in the network is to balance the load between the 2routers "fools" of ISPs, and providing failover. It does only static routing with CEF and without Nat, and a single interface connected to the network, which makes both input and output. Behind the balancer is a server that is the gateway and dhcp server (among other things) on my local network. I need the balancer is in-same ethernet segment as the other routers and configure the server to alternate routes on the server directly to the ISP's routers
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
