- Cisco Community
- Technology and Support
- Networking
- Routing
- Inside source static NAT translates destination instead...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Inside source static NAT translates destination instead...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-25-2013 09:07 AM - edited 03-04-2019 09:56 PM
Hello all,
You probably know the feeling when something works, but you don't know why it works, because it shouldn't
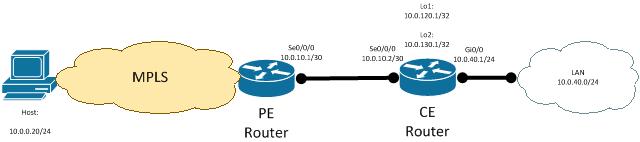
Here's the example of the topology I am working with:
The case is the following:
Two loopback addresses lo1 and lo2 on the CE router are being used for management purposes, including SNMP monitoring source addresses for various different monitoring servers each accepting the traffic only from one of the loopback addresses.
10.0.0.20 host is used for management purposes but it also acts as SNMP monitoring server and only accepts traffic originated by lo2, however lo1 is set as snmp-server trap-source, so the following global statement exist in the configuration:
ip nat inside source static 10.0.120.1 10.0.130.1 route-map SNMPLOGGING
Obviously, lo2 is configured with:
ip nat inside
SNMPLOGGING route-map includes the routes to those SNMP servers accepting the traffic only from lo2:
route-map SNMPLOGGING, permit, sequence 10
Match clauses:
ip address (access-lists): 199
Set clauses:
Policy routing matches: 0 packets, 0 bytes
---
Extended IP access list 199
10 permit ip host 10.0.130.1 host 10.0.0.20
20 permit ip host 10.0.130.1 host 10.0.0.24
30 permit ip host 10.0.130.1 host 10.0.0.21
40 permit ip host 10.0.130.1 host 10.0.0.22
50 permit ip host 10.0.130.1 host 10.1.0.20
Routes to LAN subnet and lo2 are being advertised from CE router to PE router via BGP.
The problem is the following:
SSH to CE router lo2 (10.0.130.1) doesn't work from 10.0.0.20. It seems like it's attempting to connect infinitely (via bash). I managed to fix it by adding ip nat outside statement to Se0/0/0 of the CE router, but I just can't understand why it fixes the problem. I added it because I saw that in the debug output of the CE router while attempting establishing SSH session from 10.0.0.20:
008157: Dec 11 13:04:40: IP: s=10.0.0.20 (Serial0/0/0), d=10.0.120.1, len 52, input feature <-- note that destination is 10.0.120.1, whilst I was connecting to 10.0.130.1
008158: Dec 11 13:04:40: TCP src=42315, dst=22, seq=2610185189, ack=0, win=49640 SYN, CCE Input Classification(5), rtype
0, forus FALSE, sendself FALSE, mtu 0, fwdchk FALSE
The only reason for that I could think of is PE router doing the destionation NAT from 10.0.120.1 to 10.0.130.1 but it doesn't! There's no NAT happening on the PE router at all.
So if someone could just explain me why adding ip nat outside statement to Se0/0/0 of the CE router helps to get the SSH traffic going it will definitely save me from the headache , I just don't see why NAT is happening here if traffic is originated from 10.0.0.20 as global NAT statement only specifies 10.0.120.1 as the source address for translation...
- Labels:
-
Other Routing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-26-2013 03:45 AM
Mikhail
I am slightly confused as you seem to be saying before you enabled "ip nat outside" on the s0/0/0 interface everything worked except for ssh but i would have expected you to have to have configured that for anything to work ?
In answer to your specific question -
I just don't see why NAT is happening here if traffic is originated from 10.0.0.20 as global NAT statement only specifies 10.0.120.1 as the source address for translation...
The source and destination are relative to the interface they are coming in on. So when you configure a static NAT statement like this -
ip nat inside source static 192.168.5.1 195.10.10.1
this creates a permanent entry in the NAT table. What it means is -
1) any traffic from the inside where the source IP is 192.168.5.1 will have the source IP translated to 195.10.10.1
and
2) any traffic from the outside where the destination IP is 195.10.10.1 will have the destination IP changed to 192.168.5.1
note that inside and outside in the above are defined by the "ip nat ..." statements on your router. It has to work like this because you need to NAT the IP both ways.
Both dynamic and static NAT need to translate the addresses in both directions. The difference with a static NAT is that because it creates a permanent entry in the translation table the traffic can be initiated from either the inside or the outside. In your case it is being initiated from the outside.
A very common use of static NAT is for internet services eg. you have a web server on private addressing and you want it to be accessible from the internet. So using the example above your web server has a real IP of 192.168.5.1 but this is not routable on the internet so you allocate the public IP of 195.10.10.1 to it. So if a user on the internet connects to the web server it would look like -
src IP 177.5.5.10 -> dst IP 195.10.10.1 (translated to 192.168.5.1)
src IP 192.168.5.1 (translated to 195.10.10.1) -> dst IP 177.5.5.10
notice that this is exactly the behaviour you are seeing when you connect from the outside to your loopback interface.
Hope that makes sense.
Jon
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:
