- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Outside Ports to Inside Ports
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Outside Ports to Inside Ports
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-03-2021 03:47 PM
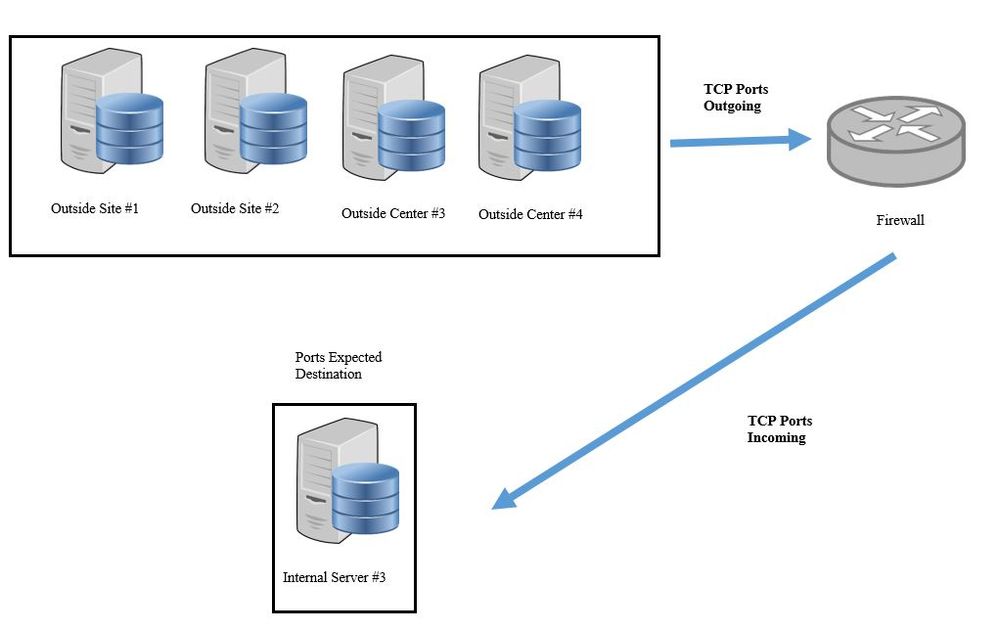
I am new to Cisco Firepower FDM Firewalls and not very familiar with port forwarding from outside networks. I am trying to allow specific Outside IP's to be able to be routed to a specific inside server. I have tried to setup port forwarding and the outside IP's do get to our network but only to our internal web server and not the intended server. If you have any suggestions, please let me know! I have attached a basic topology of what I am trying to accomplish.
- Labels:
-
Other Routing
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-03-2021 03:59 PM
Never used FDM, but it should be the same as FMC
try below document :
https://www.petenetlive.com/KB/Article/0001680
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-03-2021 04:06 PM
Thank you for the suggestion, I will have to try this. So even though I want and outside network to come inside, the policy should be setup as inside / outside with the internal server as the originating packet source and the external network as the destination packet source?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2021 12:43 AM
If the request coming from always outside to inside you need to setup outside only. ( depends on what FW you have)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2021 10:43 AM
I have a Firepower 1120 Firewall. I set up the NAT policy as suggested in the link the you sent but I don't think that it is working and is getting passed. They are able to get connected to our network but they are getting to our web server and not the intended server. I did setup an Access Rule as well that should direct the outside ports from the outside network to the specific inside IP and it is also getting no hits. I moved the NAT policy up to the top of the list and it still is the same result.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2021 11:01 AM
They are able to get connected to our network but they are getting to our web server and not the intended server.
explain more here, what is that web server ? we need more information here in terms of IP address (outside and inside) and what ports ?
what web server IP from outside able to reach?
what is the intended server IP address and port?
is the intended server port is working internally and open ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2021 11:13 AM - edited 06-08-2021 07:23 PM
When I said web server I meant Exchange, dns, dhcp server is what it is going to. One of the ports is port https 443 and the ports are open on the intended inside server. The exchange IP is *************** and the intended IP is *************.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2021 12:10 PM
Still, we have limited information here: to clarify?
The exchange IP is 192.168.0.6 - this is working ( YES/ NO) - is this suppose to work as part of this setup?
intended IP is 192.168.0.234 - check the difference between the above IP address and this address?
Do you have NAT inside to outside ?
Are you able to see the Logs of the request coming to FW ? (since you know the outside source IP )
Do you have a dedicated Static IP which you doing NAT outside to inside ? or you using the same IP address of Outside interface IP Address?
Also, check the Logs it gives you more information why it was not working?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2021 01:54 PM
Yes, the Exchange 192.168.0.6 is working and it is not a part of this setup.
The NAT is setup as inside / outside. Cisco tech had suggested to setup as outside / inside but when I did, it showed the 192.168.0.234 server as a duplicate IP on the network.
The logs I did last showed that it was using the any / any NAT policy that was setup by the tech that did the firewall which is at the bottom of the NAT list. The only other NAT policy is the policy of inside / outside Exchange IP to any interface.
When doing the NAT for the setup to the 192.168.0.234 from the outside IP I put in the specific outside IP address and port.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide