- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
VLSM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2020 04:11 AM
Hi all,
I need some direction into right path
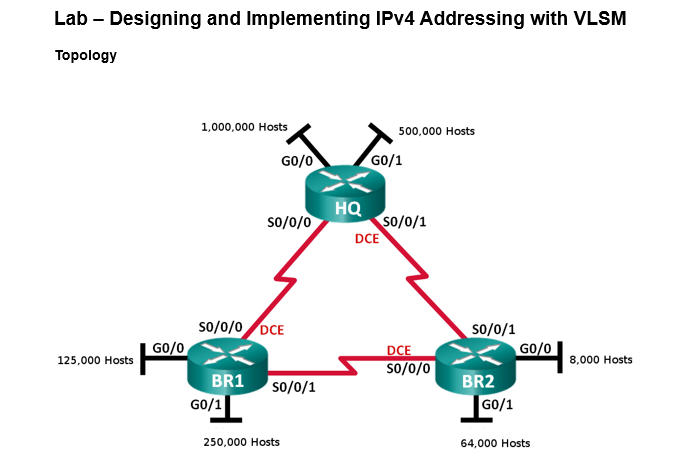
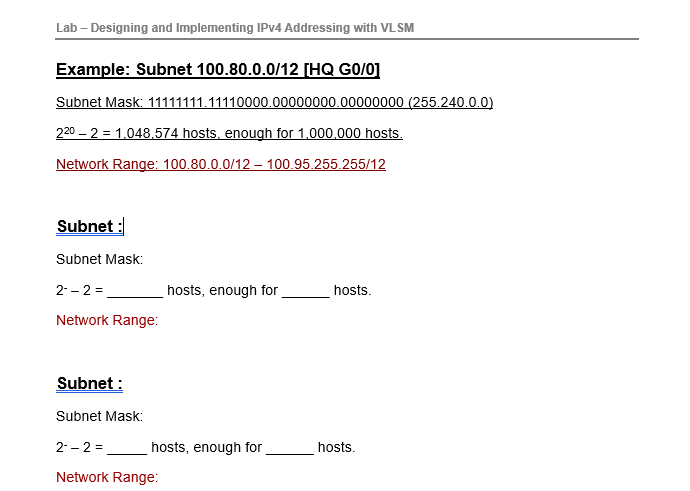
They have given a topology and an example but i am confused with the ip address that how the ip address in the example came and what ip address and subnet mask do i use for this worksheet ahead like this one in the images.
- Labels:
-
Other Routing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2020 04:36 AM
there is a good view explain in dertailed :
https://www.youtube.com/watch?v=B90kYpnbKhY
=====Preenayamo Vasudevam=====
***** Rate All Helpful Responses *****
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2020 05:09 AM
@balaji.bandiThank you for the video.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2020 05:25 AM
VLSM is very confusing.
What you need to do firstly is organize your subnets by size largest first
1,000,000
500,000
250,000 and etc
Then you need to work out how what power of 2 is just greater than 1,000,000
In the example above you can see it is 2^20 .
The 20 is significant because this is the number of Hosts bit you need for this subnet.
Your given base network is 100.80 /12 which looks like in binary
11111111.0101
Subnet 0
2^20 -2 gives 1,048,574 hosts which is enough for 1,000,000 hosts
valid host addresses 11111111.01010000.00000000.00000001 to 11111111.01011111.11111111.11111110
Your next subnet add binary 1
11111111.0110
how many hosts?
need to find 2 power of just bigger than 500,000 which in this case is 2^19 =524,288 -2 = 524,286 which is enough for 500,000 hosts
Hope this helps you get on with it.
Peter
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-03-2020 03:22 AM
Good explanation
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide