- Cisco Community
- Technology and Support
- Networking
- SD-WAN and Cloud Networking
- Re: Dual ISP failover on vEdge
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 07:35 AM
Hi all
I'm building an SDWAN lab and one of my scenarios I want to test is dual ISP failover at a branch location
I am confused about how you set up the default routes. I want the default route to switch to the second ISP connection if the primary ISP is broken (in the past I did this using IP SLA)
The tunnel part actually works correctly without any extra config but the internet breakout doesn't work
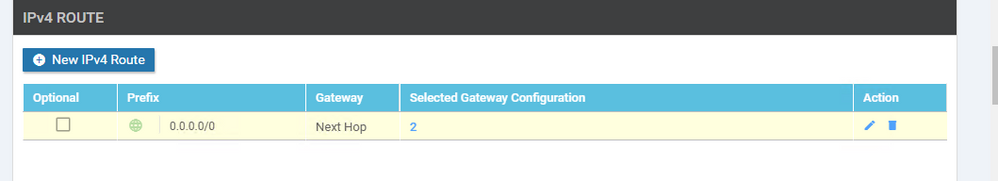
I created a tracker object as per Systems and Interfaces Configuration Guide, Cisco SD-WAN Release 20.x - Track Static Routes for Service VPNs [Cisco SD-WAN] - Cisco but when I try to apply this to VPN0 as per my screenshot below I get the error "Static route tracker cannot be configured for VPN 0":
Is there any recommended way to do this?
Thanks in advance
Solved! Go to Solution.
- Labels:
-
SD-WAN Infrastructure
-
SD-WAN vManage
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 02:56 PM
Hi,
configure 2 different trackers and apply them to different interfaces (per tracker per interface). This is "must" option per "DIA Deployment Guide".
Page 24-26 describes router with 2 internet (+NAT) channels
https://www.cisco.com/c/dam/en/us/td/docs/solutions/CVD/SDWAN/sdwan-dia-deploy-2020aug.pdf
HTH,
Please rate and mark as an accepted solution if you have found any of the information provided useful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 09:03 AM
Hi,
you may use interface tracker. It is created in system template, but applied to interface in interface template - advanced options.
HTH,
Please rate and mark as an accepted solution if you have found any of the information provided useful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 09:37 AM
Thanks,
I got the route tracking working but the NAT doesn't work once failed over
Here's my config:
S4-VE1# show run system host-name S4-VE1 system-ip 9.9.9.9 site-id 4 admin-tech-on-failure no route-consistency-check no vrrp-advt-with-phymac sp-organization-name BT_SDWAN_LAB organization-name BT_SDWAN_LAB tracker tracker1 endpoint-dns-name www.bbc.co.uk threshold 100 interval 10 ! clock timezone Europe/London vbond 203.0.113.13 aaa auth-order local radius tacacs usergroup basic task system read write task interface read write ! usergroup netadmin ! usergroup operator task system read task interface read task policy read task routing read task security read ! user admin password xxx ! user ciscotacro description CiscoTACReadOnly group operator status enabled ! user ciscotacrw description CiscoTACReadWrite group netadmin status enabled ! ! logging disk enable ! ! ntp parent no enable stratum 5 exit ! ! omp no shutdown graceful-restart advertise connected advertise static ! security ipsec authentication-type sha1-hmac ah-sha1-hmac ! ! banner login "Test Banner" motd "Test MOTD" ! vpn 0 dns 8.8.4.4 secondary dns 8.8.8.8 primary interface ge0/0 ip address 100.64.4.2/29 nat ! tracker tracker1 tunnel-interface encapsulation ipsec color public-internet allow-service all no allow-service bgp allow-service dhcp allow-service dns allow-service icmp allow-service sshd allow-service netconf no allow-service ntp no allow-service ospf no allow-service stun allow-service https ! no shutdown ! interface ge0/1 ip address 100.64.4.10/29 nat ! tracker tracker1 tunnel-interface encapsulation ipsec color biz-internet allow-service all no allow-service bgp allow-service dhcp allow-service dns allow-service icmp allow-service sshd allow-service netconf no allow-service ntp no allow-service ospf no allow-service stun allow-service https ! no shutdown ! ip route 0.0.0.0/0 100.64.4.1 ip route 0.0.0.0/0 100.64.4.9 ! vpn 1 interface ge0/2 ip address 10.4.1.1/24 no shutdown ! ip route 0.0.0.0/0 vpn 0 ! vpn 512 name OOB_MGMT interface eth0 description OOB_MGMT ip address 172.17.12.9/16 no shutdown ! ip route 0.0.0.0/0 172.17.0.1 ! S4-VE1#
When both connections are up:
S4-VE1# show int ge0/0
interface vpn 0 interface ge0/0 af-type ipv4
ip-address 100.64.4.2/29
if-admin-status Up
if-oper-status Up
if-tracker-status Up
encap-type null
port-type transport
mtu 1500
hwaddr 00:50:56:83:74:0b
speed-mbps 1000
duplex full
tcp-mss-adjust 1416
uptime 0:01:25:40
rx-packets 67441
tx-packets 81015
S4-VE1# show ip route nat
Codes Proto-sub-type:
IA -> ospf-intra-area, IE -> ospf-inter-area,
E1 -> ospf-external1, E2 -> ospf-external2,
N1 -> ospf-nssa-external1, N2 -> ospf-nssa-external2,
e -> bgp-external, i -> bgp-internal
Codes Status flags:
F -> fib, S -> selected, I -> inactive,
B -> blackhole, R -> recursive, L -> import
PROTOCOL NEXTHOP NEXTHOP NEXTHOP
VPN PREFIX PROTOCOL SUB TYPE IF NAME ADDR VPN TLOC IP COLOR ENCAP STATUS
---------------------------------------------------------------------------------------------------------------------------------------------
1 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
65528 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
512 172.17.0.0/16 connected - eth0 - - - - - F,S
65528 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
65528 192.168.0.0/24 connected - loopback65528- - - - - F,S
Once primary internet connection is down .. no NAT any more even though its enabled on the interface...
S4-VE1# show int ge0/0
interface vpn 0 interface ge0/0 af-type ipv4
ip-address 100.64.4.2/29
if-admin-status Up
if-oper-status Up
if-tracker-status Down
encap-type null
port-type transport
mtu 1500
hwaddr 00:50:56:83:74:0b
speed-mbps 1000
duplex full
tcp-mss-adjust 1416
uptime 0:01:27:49
rx-packets 68576
tx-packets 83064
S4-VE1# show ip route nat
S4-VE1#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 02:56 PM
Hi,
configure 2 different trackers and apply them to different interfaces (per tracker per interface). This is "must" option per "DIA Deployment Guide".
Page 24-26 describes router with 2 internet (+NAT) channels
https://www.cisco.com/c/dam/en/us/td/docs/solutions/CVD/SDWAN/sdwan-dia-deploy-2020aug.pdf
HTH,
Please rate and mark as an accepted solution if you have found any of the information provided useful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2021 01:10 AM - edited 06-18-2021 01:13 AM
Thanks for that - I missed that part in the guide!
Weirdly enough, before your reply, I upgraded the vEdge to 20.5.1 and my setup using the same tracker actually started working without any changes... but I will use 2 different trackers in future if I have further problems as it's best to meet the recommendations from Cisco.
NAT routes now look like what i'd expect:
S4-VE1# show ip route nat
Codes Proto-sub-type:
IA -> ospf-intra-area, IE -> ospf-inter-area,
E1 -> ospf-external1, E2 -> ospf-external2,
N1 -> ospf-nssa-external1, N2 -> ospf-nssa-external2,
e -> bgp-external, i -> bgp-internal
Codes Status flags:
F -> fib, S -> selected, I -> inactive,
B -> blackhole, R -> recursive, L -> import
PROTOCOL NEXTHOP NEXTHOP NEXTHOP
VPN PREFIX PROTOCOL SUB TYPE IF NAME ADDR VPN TLOC IP COLOR ENCAP STATUS
---------------------------------------------------------------------------------------------------------------------------------------------
1 0.0.0.0/0 nat - ge0/1 - 0 - - - F,S
1 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
65528 0.0.0.0/0 nat - ge0/1 - 0 - - - F,S
65528 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
65530 0.0.0.0/0 nat - ge0/1 - 0 - - - F,S
65530 0.0.0.0/0 nat - ge0/0 - 0 - - - F,S
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide