- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Failover Site-to-Site IPSec VTI Tunnels Between two ASA 9.7(1) using CLI
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-25-2017 01:56 AM - edited 05-01-2018 11:59 PM
Introduction
This document describes how to configure a site-to-site (LAN-to-LAN) IPSec IKE Version 1 (IKEv1) tunnels using Virtual Tunnel Interface (VTI) between two Cisco ASA. ASA VPN module was enhanced with this logical interface in version 9.7(1) and is used to create a VPN tunnel to a peer, supports route based VPN using profiles attached to VTI interfaces. More details can be found on Release Notes for ASA software 9.7(1).
Objective
Traffic between HQ and DR should pass across primary IPSec tunnel and in the case that primary link fail should failover to the backup tunnel.
Components Used
- Cisco ASA version 9.7(1);
- Cisco 1941 Series Integrated Services Router (ISR) that runs Cisco IOS Version 15.4(3)M2, used to simulate ISP A and B.
Configuration
Network Diagram
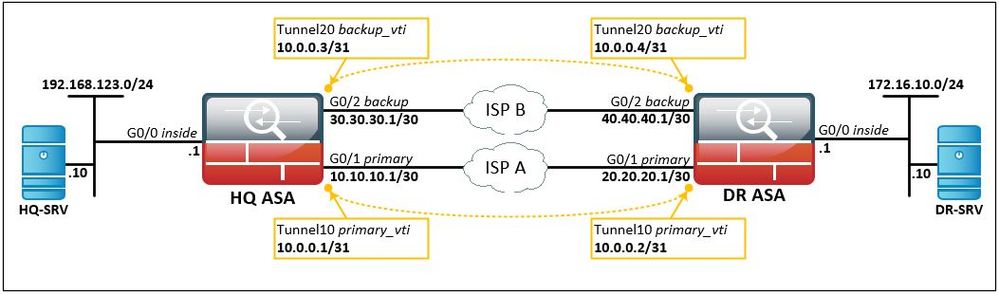
The information in this document uses network setup as bellow:
Configuration Steps
HQ ASA Configuration
First, we are adding IPSec Phase 1 and 2 configuration:
crypto ikev1 enable primary
crypto ikev1 enable backup
!
crypto ikev1 policy 10
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
!
crypto ipsec ikev1 transform-set SET1 esp-aes esp-sha-hmac
!
crypto ipsec profile PROFILE1
set ikev1 transform-set SET1
set pfs group2
!
tunnel-group 20.20.20.1 type ipsec-l2l
tunnel-group 20.20.20.1 ipsec-attributes
ikev1 pre-shared-key cisco123
!
tunnel-group 40.40.40.1 type ipsec-l2l
tunnel-group 40.40.40.1 ipsec-attributes
ikev1 pre-shared-key cisco123
for VTI interfaces configuration we are using a new feature introduced in version 9.7(1), 31-bit Subnet Mask (“For routed interfaces, you can configure an IP address on a 31-bit subnet for point-to-point connections.”, more information on Release Notes):
interface Tunnel10
description PRIMARY_VTI
nameif primary_vti
ip address 10.0.0.1 255.255.255.254
tunnel source interface primary
tunnel destination 20.20.20.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile PROFILE1
!
interface Tunnel20
description BACKUP_VTI
nameif backup_vti
ip address 10.0.0.3 255.255.255.254
tunnel source interface backup
tunnel destination 40.40.40.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile PROFILE1
to check connectivity to primary interface of our peer we use IP SLA and a track object:
sla monitor 1
type echo protocol ipIcmpEcho 20.20.20.1 interface primary
sla monitor schedule 1 life forever start-time now
!
track 1 rtr 1 reachability
then, add routes to destination networks/addresses:
route primary_vti 172.16.10.0 255.255.255.0 10.0.0.2 1 track 1
route backup_vti 172.16.10.0 255.255.255.0 10.0.0.4 5
route primary 20.20.20.1 255.255.255.255 10.10.10.2 1
route backup 40.40.40.1 255.255.255.255 30.30.30.2 1
DR ASA Configuration
For DR ASA configuration is similar to HQ ASA, only ip addresses are changed:
crypto ikev1 enable primary
crypto ikev1 enable backup
!
crypto ikev1 policy 10
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
!
crypto ipsec ikev1 transform-set SET1 esp-aes esp-sha-hmac
!
crypto ipsec profile PROFILE1
set ikev1 transform-set SET1
set pfs group2
!
tunnel-group 10.10.10.1 type ipsec-l2l
tunnel-group 10.10.10.1 ipsec-attributes
ikev1 pre-shared-key cisco123
isakmp keepalive threshold 10 retry 10
!
tunnel-group 30.30.30.1 type ipsec-l2l
tunnel-group 30.30.30.1 ipsec-attributes
ikev1 pre-shared-key cisco123
isakmp keepalive threshold 10 retry 10
!
interface Tunnel10
description PRIMARY_VTI
nameif primary_vti
ip address 10.0.0.2 255.255.255.254
tunnel source interface primary
tunnel destination 10.10.10.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile PROFILE1
!
interface Tunnel20
description BACKUP_VTI
nameif backup_vti
ip address 10.0.0.4 255.255.255.254
tunnel source interface backup
tunnel destination 30.30.30.1
tunnel mode ipsec ipv4
tunnel protection ipsec profile PROFILE1
!
sla monitor 1
type echo protocol ipIcmpEcho 10.10.10.1 interface primary
sla monitor schedule 1 life forever start-time now
!
track 1 rtr 1 reachability
!
route primary_vti 192.168.123.0 255.255.255.0 10.0.0.1 1 track 1
route backup_vti 192.168.123.0 255.255.255.0 10.0.0.3 5
route primary 10.10.10.1 255.255.255.255 20.20.20.2 1
route backup 30.30.30.1 255.255.255.255 40.40.40.2 1
Verifying the results
State of IKEv1 Phase 1 and Phase 2 can be checked with following commands:
HQ-ASA# show crypto ikev1 sa
IKEv1 SAs:
Active SA: 2
Rekey SA: 0 (A tunnel will report 1 Active and 1 Rekey SA during rekey)
Total IKE SA: 2
1 IKE Peer: 40.40.40.1
Type : L2L Role : responder
Rekey : no State : MM_ACTIVE
2 IKE Peer: 20.20.20.1
Type : L2L Role : responder
Rekey : no State : MM_ACTIV
HQ-ASA# show crypto ipsec sa
interface: primary_vti
Crypto map tag: __vti-crypto-map-5-0-10, seq num: 65280, local addr: 10.10.10.1
access-list __vti-def-acl-0 extended permit ip any any
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 20.20.20.1
#pkts encaps: 246, #pkts encrypt: 246, #pkts digest: 246
#pkts decaps: 246, #pkts decrypt: 247, #pkts verify: 247
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 246, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 10.10.10.1/0, remote crypto endpt.: 20.20.20.1/0
path mtu 1500, ipsec overhead 74(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabled
current outbound spi: E93C8DB9
current inbound spi : 00AC6E39
inbound esp sas:
spi: 0x00AC6E39 (11300409)
transform: esp-aes esp-sha-hmac no compression
in use settings ={L2L, Tunnel, PFS Group 2, IKEv1, VTI, }
slot: 0, conn_id: 86016, crypto-map: __vti-crypto-map-5-0-10
sa timing: remaining key lifetime (kB/sec): (3914979/28492)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0xFFFFFFFF 0xFFFFFFFF
outbound esp sas:
spi: 0xE93C8DB9 (3913059769)
transform: esp-aes esp-sha-hmac no compression
in use settings ={L2L, Tunnel, PFS Group 2, IKEv1, VTI, }
slot: 0, conn_id: 86016, crypto-map: __vti-crypto-map-5-0-10
sa timing: remaining key lifetime (kB/sec): (3914979/28491)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
interface: backup_vti
Crypto map tag: __vti-crypto-map-6-0-20, seq num: 65280, local addr: 30.30.30.1
access-list __vti-def-acl-0 extended permit ip any any
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 40.40.40.1
#pkts encaps: 0, #pkts encrypt: 0, #pkts digest: 0
#pkts decaps: 0, #pkts decrypt: 0, #pkts verify: 0
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 30.30.30.1/0, remote crypto endpt.: 40.40.40.1/0
path mtu 1500, ipsec overhead 74(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabled
current outbound spi: 446005A9
current inbound spi : 8BB0984A
inbound esp sas:
spi: 0x8BB0984A (2343606346)
transform: esp-aes esp-sha-hmac no compression
in use settings ={L2L, Tunnel, PFS Group 2, IKEv1, VTI, }
slot: 0, conn_id: 77824, crypto-map: __vti-crypto-map-6-0-20
sa timing: remaining key lifetime (kB/sec): (3915000/27623)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
outbound esp sas:
spi: 0x446005A9 (1147143593)
transform: esp-aes esp-sha-hmac no compression
in use settings ={L2L, Tunnel, PFS Group 2, IKEv1, VTI, }
slot: 0, conn_id: 77824, crypto-map: __vti-crypto-map-6-0-20
sa timing: remaining key lifetime (kB/sec): (3915000/27623)
IV size: 16 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
HQ-ASA# show crypto ipsec stats
IPsec Global Statistics
-----------------------
Active tunnels: 2
Previous tunnels: 8
Inbound
Bytes: 410004
Decompressed bytes: 410004
Packets: 4881
Dropped packets: 0
Replay failures: 0
Authentications: 4881
Authentication failures: 0
Decryptions: 4881
Decryption failures: 0
TFC Packets: 0
Decapsulated fragments needing reassembly: 0
Valid ICMP Errors rcvd: 0
Invalid ICMP Errors rcvd: 0
Outbound
Bytes: 411012
Uncompressed bytes: 411012
Packets: 4893
Dropped packets: 0
Authentications: 4893
Authentication failures: 0
Encryptions: 4894
Encryption failures: 0
TFC Packets: 0
Fragmentation successes: 0
Pre-fragmentation successses: 0
Post-fragmentation successes: 0
Fragmentation failures: 0
Pre-fragmentation failures: 0
Post-fragmentation failures: 0
Fragments created: 0
PMTUs sent: 0
PMTUs rcvd: 0
Protocol failures: 0
Missing SA failures: 0
System capacity failures: 0
Inbound SA delete requests: 17
Outbound SA delete requests: 0
Inbound SA destroy calls: 17
Outbound SA destroy calls: 6
and interfaces status:
HQ-ASA# show interface Tunnel 10
Interface Tunnel10 "primary_vti", is up, line protocol is up
Hardware is Virtual Tunnel Description: PRIMARY_VTI
MAC address N/A, MTU 1500
IP address 10.0.0.1, subnet mask 255.255.255.254
Traffic Statistics for "primary_vti":
0 packets input, 0 bytes
1 packets output, 28 bytes
0 packets dropped
1 minute input rate 0 pkts/sec, 0 bytes/sec
1 minute output rate 0 pkts/sec, 0 bytes/sec
1 minute drop rate, 0 pkts/sec
5 minute input rate 0 pkts/sec, 0 bytes/sec
5 minute output rate 0 pkts/sec, 0 bytes/sec
5 minute drop rate, 0 pkts/sec
Tunnel Interface Information:
Source interface: primary IP address: 10.10.10.1
Destination IP address: 20.20.20.1
Mode: ipsec ipv4 IPsec profile: PROFILE1
HQ-ASA# show interface ip brief
Interface IP-Address OK? Method Status Protocol
GigabitEthernet0/0 192.168.123.1 YES CONFIG up up
GigabitEthernet0/1 10.10.10.1 YES CONFIG up up
GigabitEthernet0/2 30.30.30.1 YES CONFIG up up
GigabitEthernet0/3 unassigned YES unset administratively down up
GigabitEthernet0/4 unassigned YES unset administratively down up
GigabitEthernet0/5 unassigned YES unset administratively down up
GigabitEthernet0/6 unassigned YES unset administratively down up
Management0/0 unassigned YES unset administratively down up
Tunnel10 10.0.0.1 YES CONFIG up up
Tunnel20 10.0.0.3 YES CONFIG up up
You might also see:
CLI Book 3: Cisco ASA Series VPN CLI Configuration Guide, 9.7
I hope to be helpful.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Fantastic work, how about a config with redundancy but using OSPF/EIGRP/ISIS?
Also, how would you most easily implement ACLs to these VTIs? I tried to use the no sysopt connection permit-vpn command and use the outside interface ACLs but the ASA did not like it and gave me a bunch of green errors like this:
"Inbound TCP connection denied from x.x.x.x/port to x.x.x.x/port flags SYN on interface Tunnel4"
"Inbound TCP connection denied from x.x.x.x/port to x.x.x.x/port flags RST on interface Tunnel4"
"Deny inbound UDP from x.x.x.x/port to x.x.x.x/53 due to DNS Query"
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Unfortunately OSPF/EIGRP is not supported at this time but you can use BGP which is supported.
I recommend you to look on this document: http://www.cisco.com/c/en/us/td/docs/security/asa/roadmap/asa_new_features.html regarding new features introduced, from time to time.
To use ACL on VTI's you have to apply an vpn-filter on the group-policy related to that tunnel. For our example above, applied to DR-ASA, this will look like this:
tunnel-group 10.10.10.1 general-attributes
default-group-policy GP_HQ_VTI_Tunnels
tunnel-group 30.30.30.1 general-attributes
default-group-policy GP_HQ_VTI_Tunnels
group-policy GP_HQ_VTI_Tunnels internal
group-policy GP_HQ_VTI_Tunnels attributes
vpn-filter value ACL_VTI_FROM_HQ
vpn-tunnel-protocol ikev1
ACL_VTI_FROM_HQ it's an extended access-list applied to tunnel. This access-list is working in one direction only (it is somewhere specified, i don't have now the link for the document now), you can restrict only incoming traffic (HQ->DR in this example), outgoing traffic is fully allowed.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Very good document!
Does it support multiple VTI tunnels from one source interface to many destinations?
I am trying to figure out if it can be used for a solution below.
The solution must meet the following requirements:
- A single home Internet connection on ASA5506
- ASA5506 automatically connects to the ASA at Site A as a primary VPN tunnel
- If the Site A ASA is down, ASA5506 automatically fails over to the ASA at Site B as a secondary VPN tunnel, and automatically switch back to Site A when appropriate (not during active use)
- The switch over must be seamless
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: