Objective:
Configuring IPSec VPN between IOS Router and any Remote VPN Peer
Symptom:
Phase 1 Completes but Phase 2 is failing with the below error
: ISAKMP:(1002): IPSec policy invalidated proposal with error 32
: ISAKMP:(1002): phase 2 SA policy not acceptable! (local X.X.1.3 remote X.X.1.100)
: ISAKMP: set new node -1593419981 to QM_IDLE
: ISAKMP:(1002):Sending NOTIFY PROPOSAL_NOT_CHOSEN protocol 3
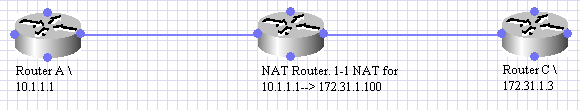
Topology:
Current Crypto Configuration:
Some parts of Relevant Crypto Config on Router C
Router C:
crypto isakmp profile RouterA
keyring All
match identity address 172.31.1.100 255.255.255.255
!
crypto map outside-map 1 ipsec-isakmp
set peer 172.31.1.100
set transform-set 3des-sha
match address 102
set isakmp-profile RouterA
Failed Debugs:
Below is snipped output from "debug crypto isakmp" and "debug crypto ipsec" from "Router C".
<SNIP>
*Dec 9 19:30:13.403: ISAKMP (1002): ID payload
next-payload : 8
type : 1
address : 10.1.1.1
protocol : 17
port : 0
length : 12
*Dec 9 19:30:13.403: ISAKMP:(0):: peer matches *none* of the profiles
*Dec 9 19:30:13.403: ISAKMP:(1002): processing HASH payload. message ID
<SNIP>
*Dec 9 19:30:13.475: map_db_check_isakmp_profile profile did not match
*Dec 9 19:30:13.475: map_db_find_best did not find matching map
*Dec 9 19:30:13.475: IPSEC(ipsec_process_proposal): proxy identities not supported
*Dec 9 19:30:13.475: ISAKMP:(1002): IPSec policy invalidated proposal with error 32
*Dec 9 19:30:13.475: ISAKMP:(1002): phase 2 SA policy not acceptable! (local 172.31.1.3 remote 172.31.1.100)
*Dec 9 19:30:13.475: ISAKMP: set new node -1593419981 to QM_IDLE
*Dec 9 19:30:13.475: ISAKMP:(1002):Sending NOTIFY PROPOSAL_NOT_CHOSEN protocol 3
.....
Solution:
The problem here is that the Crypto Map is referencing the ISAKMP Profile "RouterA", which means that during Phase1 the Remote Router should match the ISAKMP Profile.
A common mistake is that while defining the "match" statement in the ISAKMP Profile the POST-NAT address of the Remote Peer is used and the ISAKMP profile never gets matched as seen above. This results in Phase2 failure with error 32.
This can be fixed in two ways
Option 1:
Remove the ISAKMP profile reference from the Crypto Map, however this is probably not the best approach. The ISAKMP profiles provide great flexibility therefore Option 2 as below is a better option.
Option 2:
A. Modify the "match.." statement in the ISAKMP profile to match the address as being sent by the Remote peer. As seen from the above debugs , this address is 10.1.1.1. So the below config will fix the problem
crypto isakmp profile RouterA
no match identity address 172.31.1.100 255.255.255.255
match identity address 10.1.1.1 255.255.255.255
B. However the above solution can represent a problem, when the Remote Peer has a DHCP assigned address. In this case a better approach can be to configure the Remote Router to send its hostname as the ISAKMP Identity instead of "IP Address".
On Cisco devices this can be configured as
crypto isakmp identity hostname
Modify "Router C" config as below
crypto isakmp profile RouterA
no match identity address 172.31.1.100 255.255.255.255
match identity host RouterA
The above will fix the problem and the solution will keep working even if RouterA's WAN IP changes.
Working Debugs:
Below is snipped output from "debug crypto isakmp" and "debug crypto ipsec" from "Router C". You can see that now correct ISAKMP Profile being matched and Phase 1 \ Phase 2 succeeds.
<SNIP>
*Dec 12 21:47:53.063: ISAKMP:(1002): processing ID payload. message ID = 0
*Dec 12 21:47:53.063: ISAKMP (1002): ID payload
next-payload : 8
type : 2
FQDN name : RouterA
protocol : 17
port : 0
length : 15
*Dec 12 21:47:53.063: ISAKMP:(0):: peer matches RouterA profile
<SNIP>
*Dec 12 21:47:53.087: ISAKMP:(1002):deleting node -585098955 error FALSE reason "QM done (await)"
*Dec 12 21:47:53.087: ISAKMP:(1002):Node -585098955, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH
*Dec 12 21:47:53.087: ISAKMP:(1002):Old State = IKE_QM_R_QM2 New State = IKE_QM_PHASE2_COMPLETE
*Dec 12 21:47:53.087: IPSEC(key_engine): got a queue event with 1 KMI message(s)
*Dec 12 21:47:53.087: IPSEC(key_engine_enable_outbound): rec'd enable notify from ISAKMP
Side Note:
This problem is Not limited to any NAT scenario as in the above example. This could be a problem in any setup, where the "Correct ISAKMP Profile" does not get matched due to mis-configured "match" statement in the Profile.
References-------
http://www.cisco.com/en/US/products/ps6120/products_tech_note09186a00807e0aca.shtml