Introduction:
This document explains how to configure LDAP on ASA so that user has "monitor only" access to ASDM.
Prerequisites:
Ensure that you meet below mentioned requirements before implementation.
- Define ASA as a AAA client on LDAP server.
- Define the IP address and an identical shared secret key on the LDAP and ASA.
Devices Used:
The information is based on below mentioned software and hardware versions:
All of the devices used in this document started with factory default configuration.
Configuration on ASA:
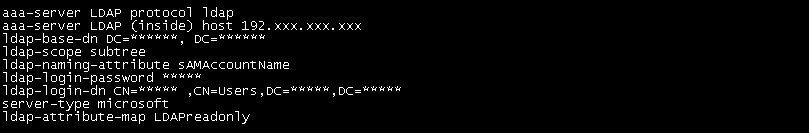
1.) AAA server configuration
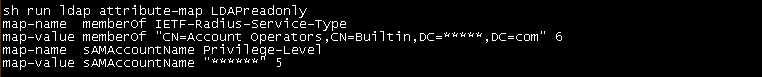
2. LDAP attribute map configuration:
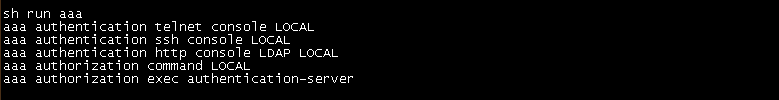
3. AAA configuration on ASA
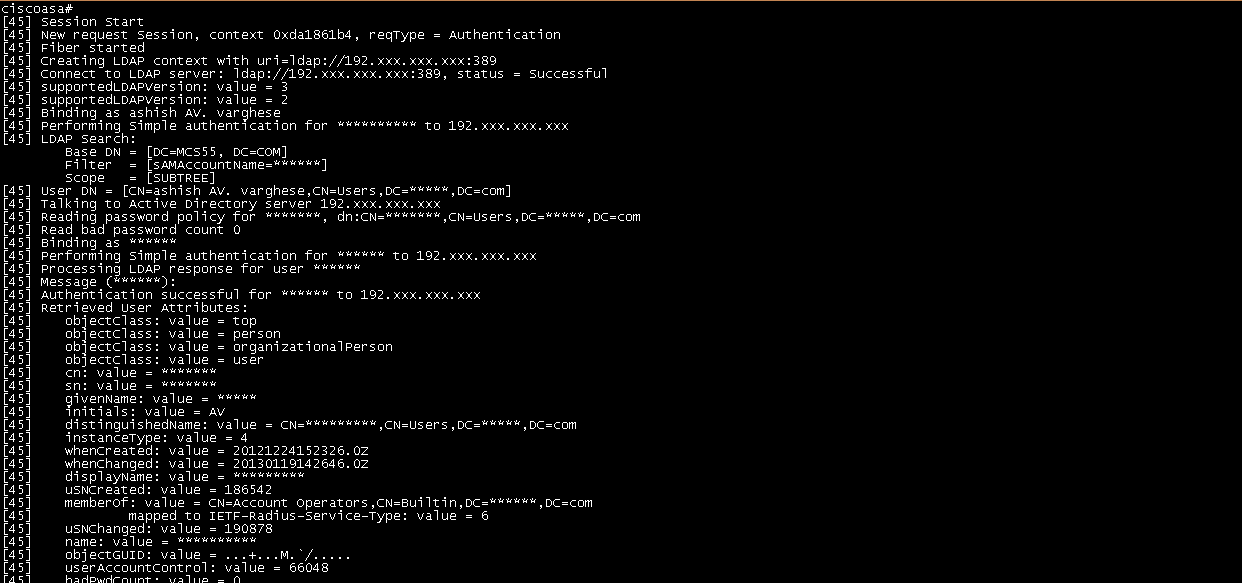
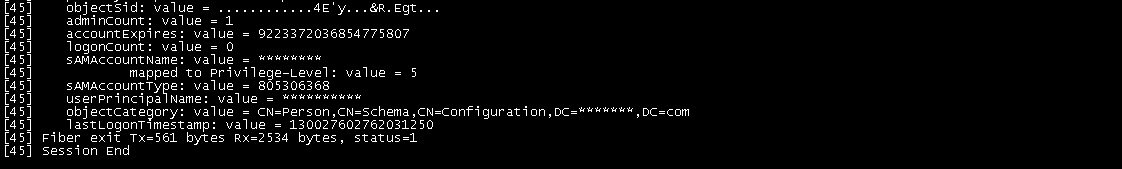
Verification:
Scenario 2:
Problem:
User have configured the ASA CX and configured the Web filtering policies.
In the policies, he has created the user objects for each of his user with their IP address for the Source. But he need to integrate it with Active Directory which will be easy for him to add user in the object group by
their domain username. what will be the steps for it.
And also that can be easily identified in the event tab with that username, as for now its just showing me the IP of the user doing illegal surfing.
Solution:
You will need to setup/install CDA instead. CDA provides several benefits over the older AD Agent such as, GUI interface for management, runs on its own VM - doesn't need to be installed on a DC, and
Windows 2012 support. Below is additional information regarding CDA for you to review:
Once you install CDA on your network Please follow the installation guide for Active Directory Integration. Once you done, you can see the user name on access policy.
CDA Installation Guide:
http://www.cisco.com/c/en/us/td/docs/security/ibf/cda_10/Install_Config_guide/cda10/whats_new.html
CDA Download:
https://software.cisco.com/download/release.html?mdfid=284143092&flowid=31542&softwareid=284724387&release=CDA&relind=AVAILABLE&rellifecycle=&reltype=latest