- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Configuring ACS 5.x to send customized Alarms to ACS admin
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
05-02-2013 09:30 AM - edited 02-21-2020 09:59 PM
Introduction
Configuring ACS 5.x to send customized Alarms to ACS admin
Configuration
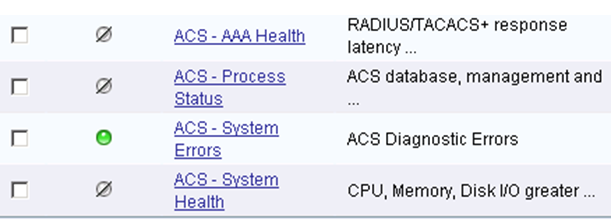
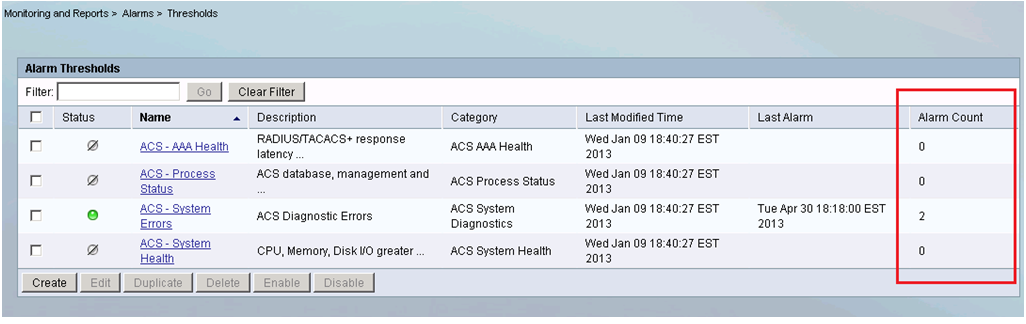
We can use ACS 5.x for sending alarms, if it meets a certain threshold for certain condition, by default there are 4 alarms:
If we want ACS to notify us via e-mail about few other aspects explained below, that can be done.
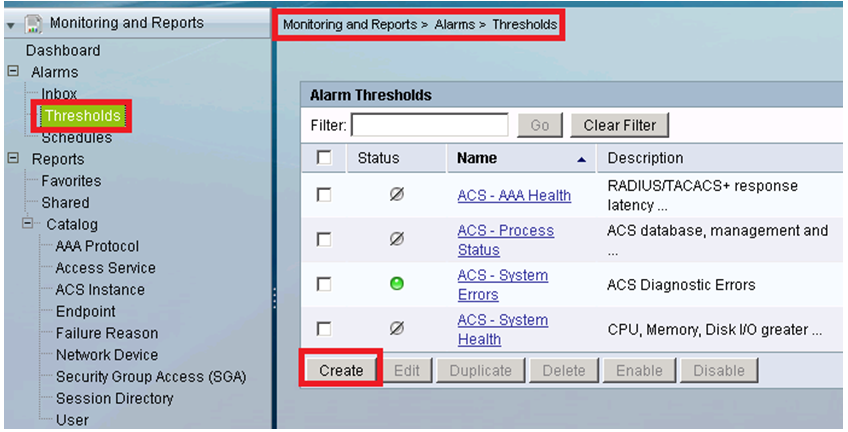
Step 1. Access ACS gui --> monitoring and reports --> Alarms --> Thresholds and click on create.
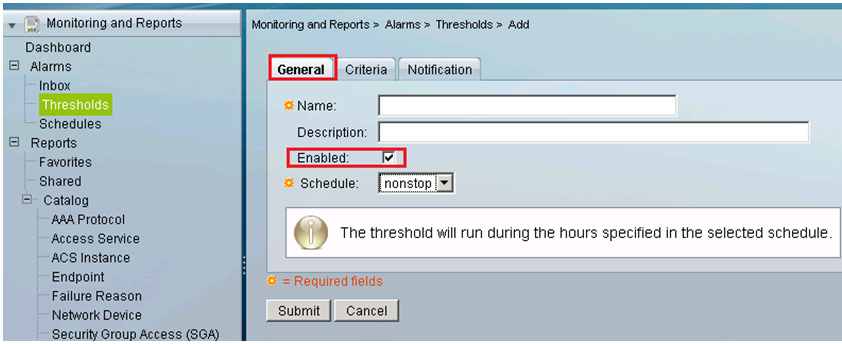
STEP 2. Under General tab you can mention a name that help you relate to the alarm you want to configure and enable the alarm.
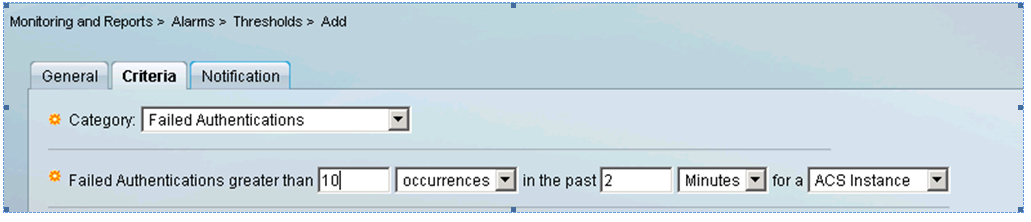
STEP 3. Under criteria we need to specify the parameter that ACS is supposed to monitor and send an alert when the threshold is crossed.
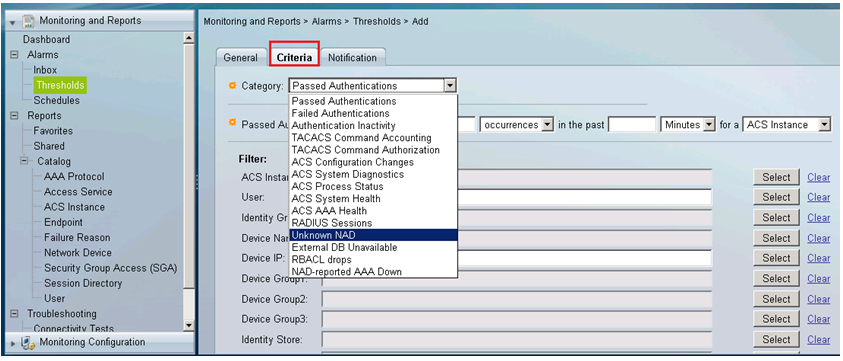
The categories available are:
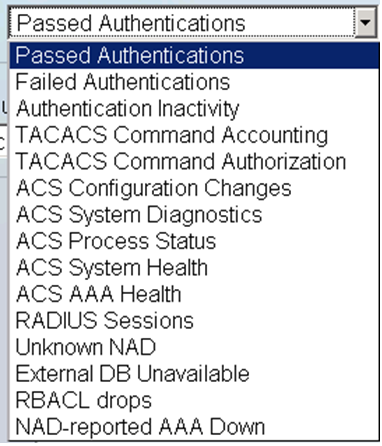
ACS, if configured will monitor the above mentioned categories.
STEP 4. Next steps would be to configure the threshold :
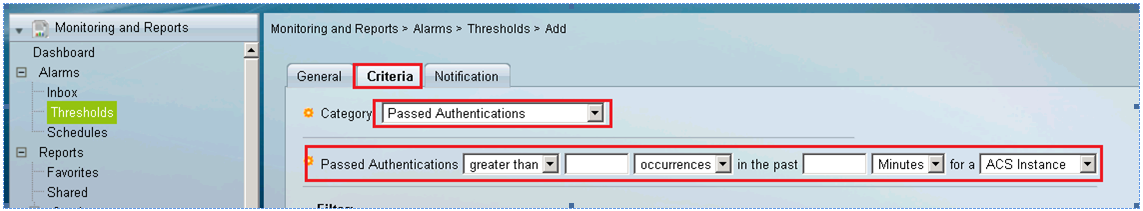
In the above screen shot I have chosen category as “passed authentication”, I can optionally choose between the options mentioned in STEP 3. In the threshold we can mention what is the limit for the passed authentication in the given time frame and for a given ACS instances, if this threshold is crossed, ACS is supposed to generate an alarm and send an e-mail to the administered.
STEP 5. In addition to this ACS provides us the option for defining filters, so that the alarm can be specifically generated for following parameter:
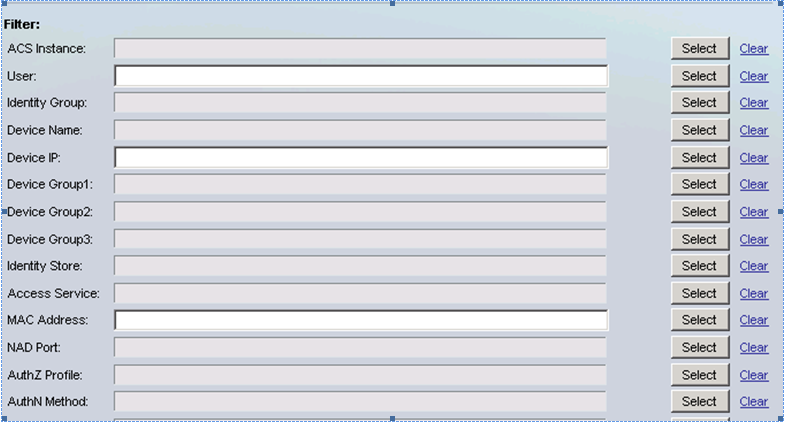
That means ACS will calculate the threshold for those devices, which matches the filter.
STEP 6. Now, under “notifications” section, you can choose the severity for which ACS is supposed to send the alarm.
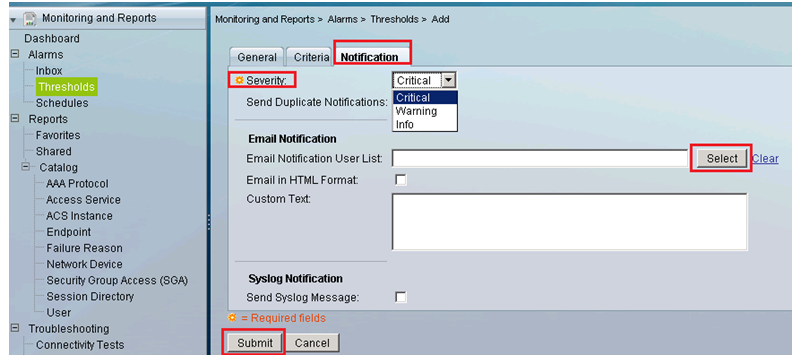
STEP 7. For the user list ACS will pull up (when we click select), those user e-mail ID’s which have been defined under ACS gui > System Administration > Administrators > Accounts
STEP 8. Click submit
Example
Let’s say if we want ACS to generate alarm if the user fails authentication more than 10 times in past 2 minutes, following will be my threshold configuration.
Additionally, ACS dashboard, will show the “alarm count”, which is supposed to increase when particular request hits the threshold.
Please feel free to comment in case of any query.
User wondering, if she using LDAP for external authentication, can she use the internal identity attribute?
for example :
i create an user X , his password type is LDAP, but the identity group is "Group 1"
can i define rules
Idenitty Group in "Group 1" permit access ? or i need to do group mapping first?
Solution:
It is possible to define an internal user whose password is taken from an external store.
In internal user definition select "Password Type" to be the LDAP database and then define the rest of the user definition, including identity groups, as desired
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Is there any way to pass along into the emal message any details from the event?: offending IP, host that access was attempted on, login ID associated with the failed attempt . . . etc.
I have been looking for variables that can be put into the Custom Text section
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi ,
We can use following option, With category failed or passed attempts.
| Monitoring and Reports > | Alarms > | Thresholds > | Add |
Regards
~JG
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
thank you Jagdeep. I did get that far. The emails or syslogs generated do not contain the detail I was looking for. Do you know if there are variables that can be put into the generated message that will give this information:
offending IP, host that access was attempted on, login ID associated with the failed attempt
. . . etc. ,
thanks for your response.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Kdlittletree,
I have the same need to see some more details in the email alerts sent by ACS.
Please were you able to find a way around it?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
no. i continue logging into the acs server to check the details of the event(s)
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: