- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: Encrytion between two Cisco 1841 Routers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 06:49 AM
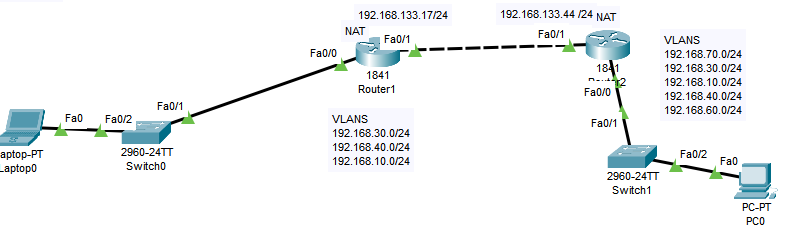
Hi @all, I have the following topology. I wish to encrypt the traffic between both router in such a way that all data that goes from one side to another through the link stays encrypted @royalblues
Solved! Go to Solution.
- Labels:
-
Branch Router
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 06:52 AM
Hi,
You can use IPSEC if your IOS support security features. See link:
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 07:34 AM
On the router, you are not configuring the vlan access list. You just configure each IP segment that is associated with each vlan.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 06:52 AM
Hi,
You can use IPSEC if your IOS support security features. See link:
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 07:05 AM
Thank you very much! But how can I configure the access lists for every VLAN ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 07:34 AM
On the router, you are not configuring the vlan access list. You just configure each IP segment that is associated with each vlan.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2020 08:03 AM
Hello,
as an alternative, you could also configure VTIs. Does the local traffic just have to go to the other side, or do you also need Internet access for your local Vlans ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2020 12:01 AM
Hi! The local traffic goes to the other side and the local VLAN's already have internet through NAT und ISP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2020 12:59 AM
Hello,
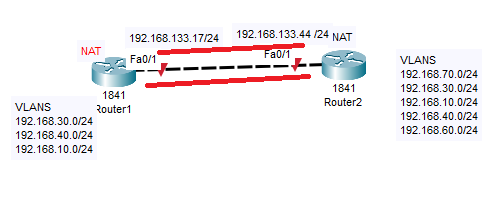
what did you configure to resolve the problem of overlapping networks at each side ? Did you use policy NAT, or twice NAT ? Post the running configurations of both your 1841 routers...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2020 03:28 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2020 08:12 AM
Just for reference, can you post your final, working configs ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-31-2020 12:14 AM
Router1
hostname test
!
!
!
!
!
ip dhcp pool vlan30
network 192.168.30.0 255.255.255.0
default-router 192.168.30.254
dns-server 192.168.134.8
!
!
!
ip cef
no ipv6 cef
!
!
!
!
crypto isakmp policy 10
hash md5
!
crypto isakmp key 01.020r address 192.168.133.44
!
!
!
crypto ipsec transform-set 01.020r esp-des esp-md5-hmac
!
crypto map 01.020r 10 ipsec-isakmp
set peer 192.168.133.44
set transform-set 01.020r
match address 100
!
!
!
!
ip ssh time-out 60
ip domain-name test.com
!
!
spanning-tree mode pvst
!
!
!
!
!
!
interface FastEthernet0/0
no ip address
duplex auto
speed auto
!
interface FastEthernet0/0.30
encapsulation dot1Q 30
ip address 192.168.30.254 255.255.255.0
ip nat inside
!
interface FastEthernet0/1
ip address 192.168.133.17 255.255.255.0
ip nat outside
duplex auto
speed auto
crypto map 01.020r
!
interface Vlan1
no ip address
shutdown
!
ip nat pool 01.020r 192.168.133.17 192.168.133.17 netmask 255.255.255.0
ip nat inside source list 10 pool 01.020r overload
ip classless
!
ip flow-export version 9
!
!
access-list 10 permit 192.168.30.0 0.0.0.255
access-list 100 permit ip 192.168.30.0 0.0.0.255 192.168.30.0 0.0.0.255
!
banner motd ^C
ex
^C
!
!
@Georg Pauwen wrote:Just for reference, can you post your final, working configs ?
!
!
!
line con 0
!
line aux 0
!
line vty 0 4
login
!
!
!
end
Router2
Current configuration : 1338 bytes
!
version 12.4
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname Router
!
!
!
!
!
ip dhcp pool vlan30
network 192.168.30.0 255.255.255.0
default-router 192.168.30.254
dns-server 192.168.134.8
!
!
!
ip cef
no ipv6 cef
!
!
!
!
crypto isakmp policy 10
hash md5
authentication pre-share
!
crypto isakmp key 06.010r address 192.168.133.17
!
!
!
crypto ipsec transform-set 06.010r esp-des esp-md5-hmac
!
crypto map 06.010r 10 ipsec-isakmp
set peer 192.168.133.17
set transform-set 06.010r
match address 100
!
!
!
!
!
!
spanning-tree mode pvst
!
!
!
!
!
!
interface FastEthernet0/0
no ip address
duplex auto
speed auto
!
interface FastEthernet0/0.30
encapsulation dot1Q 30
ip address 192.168.30.254 255.255.255.0
ip nat inside
!
interface FastEthernet0/1
ip address 192.168.133.44 255.255.255.0
ip nat outside
duplex auto
speed auto
crypto map 06.010r
!
interface Vlan1
no ip address
shutdown
!
ip nat pool 06.010r 192.168.133.44 192.168.133.44 netmask 255.255.255.0
ip nat inside source list 10 pool 06.010r overload
ip classless
!
ip flow-export version 9
!
!
access-list 10 permit 192.168.30.0 0.0.0.255
access-list 100 permit ip 192.168.30.0 0.0.0.255 192.168.30.0 0.0.0.255
!
!
!
!
!
!
line con 0
!
line aux 0
!
line vty 0 4
login
!
!
!
end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2020 06:24 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide