- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: Nexus_DHCP_device can not gain IP address
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Nexus_DHCP_device can not gain IP address
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-17-2019 05:27 AM - edited 09-17-2019 05:30 AM
hello, friends
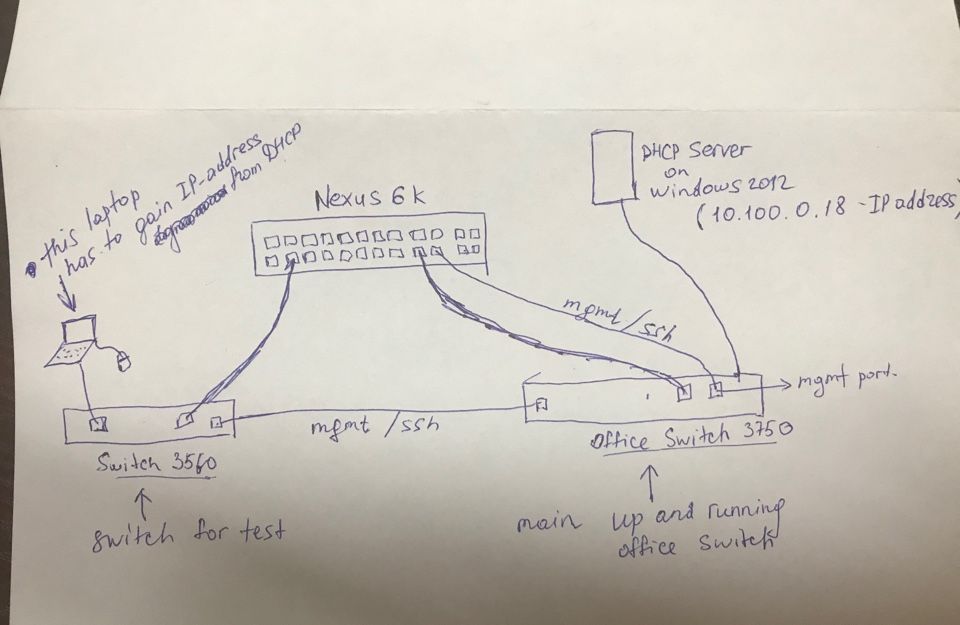
I need a help. For more info open an attached image, please.
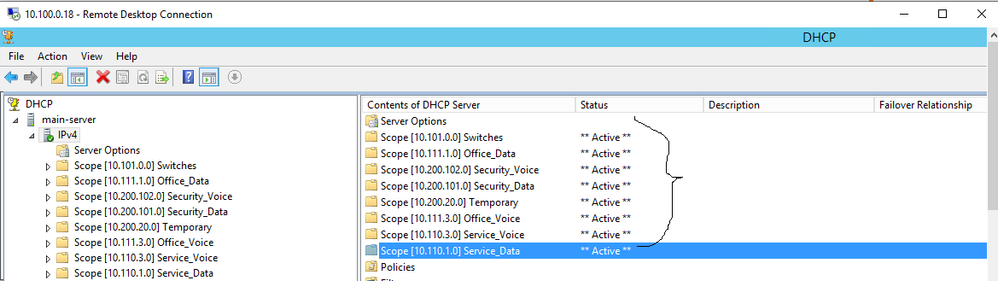
1. I installed DHCP Server on Windows server 2012. Created 8 dhcp scopes for 8 subnets.
2. I configured DHCP relay on Nexus 6000. (configuration file is attached)
3. I configured C3560 switch to connect user devices, as you know on Nexus all ports are SFP, that's why I use this switch to connect user devices to the nexus. (configuration file of C3560 is attached)
4. The interface fastethernet0/2 on C3560 I configured as switchport mode access and the port belongs to vlan 402. Then I
connected my laptop to this port, but I couldn't get any IP-address from this scope (dhcp-address-range 10.111.3.6 - 10.111.3.254)
That is my problem. Any advice would be helpful
- Labels:
-
LAN Switching
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 03:11 AM
but what for this command "ip default-gateway 192.168.210.1"??? I dont understand. Could you explain me?
Can I don't use it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 06:33 AM
If this the device only doing L2, theris L3 routing required in the Swithch
below command only rquired to reach managment. (rather we use to use ip route command)
ip default-gateway 192.168.210.1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 08:52 AM
Hello
This switch can be a host switch - no up routing so basically it’s just like a pc
ip address
subnet mask
default gateway
The D/G is required for remote access to the switch otherwise without it you would not be able reach it off it own subnet
Please rate and mark as an accepted solution if you have found any of the information provided useful.
This then could assist others on these forums to find a valuable answer and broadens the community’s global network.
Kind Regards
Paul
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 09:10 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 10:25 PM
Hello,
how did you resolve this ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2019 02:26 AM
everything configured like you all mentioned here. The problem was that interface vlans was on down state. I just used command "no shutdown" and everything had worked fine
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2019 05:44 AM
Well sorry but these is just like I am keeping my point of View As u said that Nexus all ports are SFP so you have given one Cisco switch with it and then on that switch you have connected server and on that server you have created various DHCP Pool.
But what mine thinking say is Its good what you have did atleast I got to know such scenerio also but what if
1->You have Created a DHCP IP Pool on your Nexus device only
2-> and after that you would have created multiple VLANs as you have already Created and also VLAN SVI on Nexus Only.
3-> what these could have done is your Nexus would have worked as an DHCP Server as it has the capacity to do that I believe that so because I have personally not worked on Nexus
4-> The setup would have been much easier sorry but I just felt that from my end to explain things according to my scenerio
I hope with Server you have not only created DHCP server pool but also AD & Other Domain settings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-18-2019 10:37 AM
Hello,
on a side note, and I don't know if this has already been mentioned, your access port needs the 'spanning-tree portfast' command, try and add that:
interface FastEthernet0/2
switchport access vlan 402
switchport mode access
spanning-tree portfast
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2019 02:28 AM - edited 09-27-2019 05:06 AM
zachrhart@gmail.com Hello, guys!
one more question about DHCP Option 82. Do I need to configure it on nexus?
In general for what we use this option?
And what about the trusted interface? Should I configure a trusted interface? (Ensure that the DHCP server is connected to the device using a trusted interface. https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus9000/sw/6-x/security/configuration/guide/b_Cisco_Nexus_9000_Series_NX-OS_Security_Configuration_Guide/b_Cisco_Nexus_9000_Series_NX-OS_Security_Configuration_Guide_chapter_01101.html)
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide