- Cisco Community
- Technology and Support
- Networking
- Switching
- Since it's only 4 routers,
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
OSPF, where to area.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-09-2015 06:47 AM - edited 03-08-2019 03:02 AM
Hi,
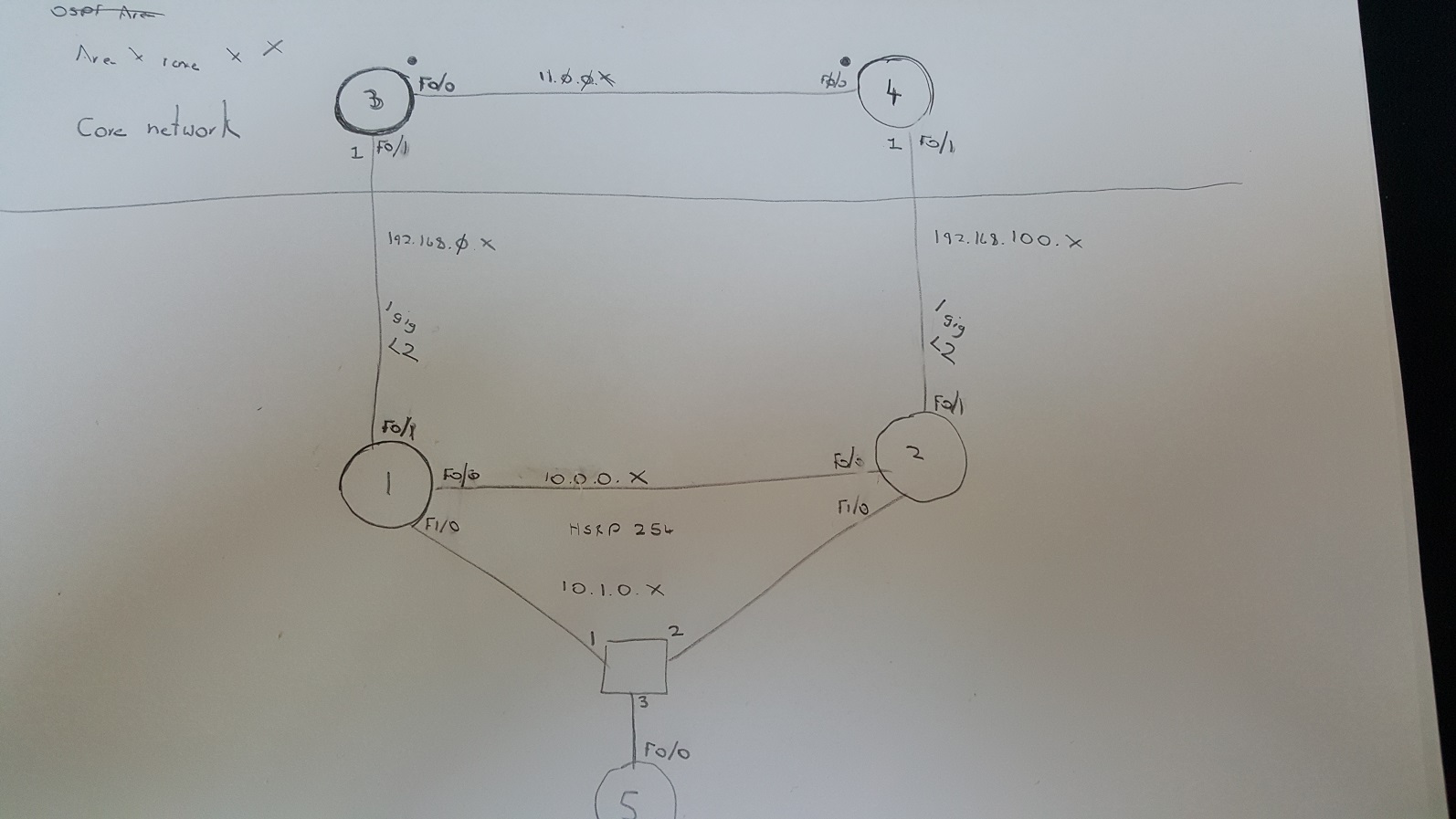
Food for though this one for me. We have a core network (Routers 3 / 4) which are running EIGRP and I need to hook in a new site using 2x1 l2 circuits and use OSPF. So router 3 is connected to router 1 and Router 4 to router 2. I want to run ospf from 3/4 to 1/2 for site resilience and favour link 3 to 1. I want sites 1/2 only to receive a default route to get the traffic back to the core, and also want site 3/4 to receive a simple /16 route. My current design has area 0 between 3/4, then area 1 between 3/1, 4/2, and 1/2. Link 4/2 has a cost of 1000 on both interfaces. However in this setup there is some interesting behavour. Router 4 still routes via router 2 as these routes are Intra area even though they are a distance of over 1000 because the other routes learned via R3 are Inter Area routes but at a lower cost. So I have choices, do I extend area 0 to router 1/2 outside interfaces, OR at the moment as this is the only OSPF pocket, also have the link between 3/4 as area 1. However, that does not align to my hopes of having area 1 as a totally stubby area and only receiving a default route and advertising a summary /16 out of that area. Any thoughts on how better to do this?
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-09-2015 10:00 AM
Since it's only 4 routers, probably the easiest thing to do would be to put them all in Area 0. Usually I only start adding areas when the number of routers gets too high (so your topology tables don't get too crazy) or to separate different geographic areas.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-09-2015 12:19 PM
Hi,
It would probably be the easiest, but it doesnt give me the nice summarisation out of the site 1/2 as its not on an ABR or a default route into a stub kind of site, also bearing in mind the future with our core network hopefully going VPLS, so that would be our area 0 for OSPF.
So without having to change much in the future, I could make this all area 10 for example(im sure I dont need area 0 unless connecting different areas) and just default originate and accept the non summarised routes(not to many initially). I guess my brain is thinking ahead and want to structure this preemptively.
Lee
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


