- Cisco Community
- Technology and Support
- Collaboration
- TelePresence and Video Infrastructure
- Interworked - No permission - Insufficient privilege
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Interworked - No permission - Insufficient privilege
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2017 02:38 PM - edited 03-18-2019 01:40 PM
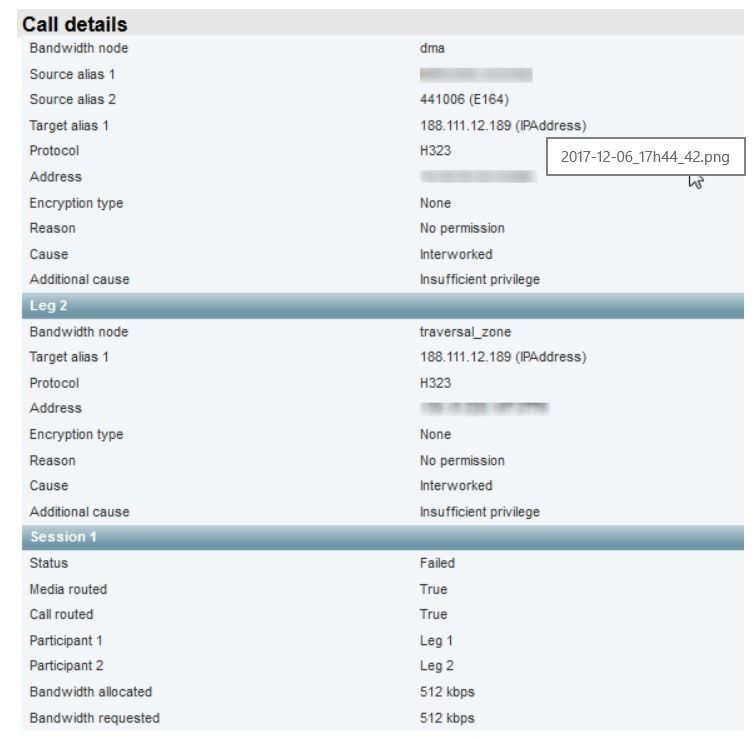
I'm having a DMA where i have registered my GS using H.323 and VCS C has been added as a External Gatekeeper. Now when i tried to place a call to an public IP address from the GS device using H.323 am getting an error like present in the screenshot.
Also the same error replicating in the VCS E as well. I've tested the call by registering the GS device in SIP only mode to DMA and VCS C has been added as a External SIP peer, now dials the same public IP address and it works fine without any issues.
Inter-working has been configured as "ON" in VCS E and VCS C was set to off. I've two environments in production am running my vcs on 8.6 and in test (Virtual environment) am running my VCS on version 8.10.
Could you please help me analyze and resolve this issue.
Thanks
Aravind S

- Labels:
-
Other Collaboration Endpoints
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-06-2018 08:33 PM
As per this thread cisco vcs Interworking No permission, you will get the Insufficient privilege error when the VCS is set to only perform interworking for registered endpoints. Change the Interworking to "on" instead of "registered only" and see id that helps solve your issue.
Please remember to mark helpful responses and to set your question as answered if appropriate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-06-2018 11:53 PM
Hi Wayne
Thanks for your reply.
The inter working is set to On, in VCS expressway. But it doesn't improve my situation.
Please find the call flow
Endpoint --> DMA --> VCS C --> VCS E (interworking off and the call ends here)--> VCSC --> VCSE (interworking is on)
I know the call flow is not normal, but this setup was recommended by cisco due to our acquisition of a company. In order to harmonize their video infrastructure cisco has recommended this setup.
Please let me know if you need further information.
Thanks
Aravind S
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2018 05:12 PM
Why are you going from a C > E > C > E? Can you explain the deployment more in details, is this all on the same network, are you traversing different networks, multiple organizations?
Try and set interworking to On for all VCS' in the call path.
On the VCS-C that the DMA is neighbored to, what is the authentication mode set to? Try setting it to "Trust as authenticated".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2018 01:18 PM
Hi Patrick,
This design was recommended by CISCO only.
Let me explain this with A and B organization.
A is my organization, which is already having A VCS C and A VCS E. Now we bought the B organization where we had deployed B VCS C in their network (Since no transparent network available between A and B organization) and B VCS E in my (A) corporate network to harmonize both organization video infrastructure. Since traversal is not possible between A VCS C and B VCS C, we had deployed B VCS E in A corporate network.
Endpoint -->DMA -Neighbor-> B VCS C -Traversal-> B VCS E -Neighbor-> A VCS C -Traversal-> A VCS E --> Public Endpoint
I don't remember the authentication mode, but i'll look for this option tomorrow, please let me know, once it has been configured as "Trust as authenticated" do we need to set on or off as an authentication policy.
Hope I haven't confused you with my explanations. Please let me know if you need any clarifications.
Thanks
Aravind S
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2018 01:48 PM
Treat as authenticated means all calls coming from that particular zone will appear as authenticated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2018 01:32 PM
Dear All
Thanks and sorry for the delayed reply.
Finally found a solution for my daisy chain of VCS in my environment. Now everything seems to be working as expected.
Thanks to @Patrick Sparkman for giving me one of the hint about "treat as authenticated". But what i did apart from this is, i've enabled custom zone profile.
Endpoint (H323) -->DMA -Neighbor-> B VCS C (Custom zone profile for the Neighbour DMA) -Traversal-> B VCS E (Custom zone profile for the neighbour A VCS C) (interworking H323 to SIP) -Neighbor-> A VCS C (Custom zone profile for the neighbour B VCS E) -Traversal-> A VCS E (goes out as SIP) --> Public Endpoint.
Attaching a example screenshot of this custom profile. Only thing we need to be careful is while enabling H323 parameter in the custom profile. This will have some impact if you are environment is completely in SIP.
But still i've one issue, When i'm dialing an external <confid>@DNS from my endpoint the call is getting disconnected after 22 minutes. When i dial an external <confid>@IP Address the call is running properly without an interruption even after an hour.
Any suggestions most welcome.
Thanks
Aravind S
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

