- Cisco Community
- Technology and Support
- Data Center and Cloud
- Unified Computing System (UCS)
- Unified Computing System Discussions
- Re: Role of the Native VLAN for UCS vNIC
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-25-2020 07:41 AM
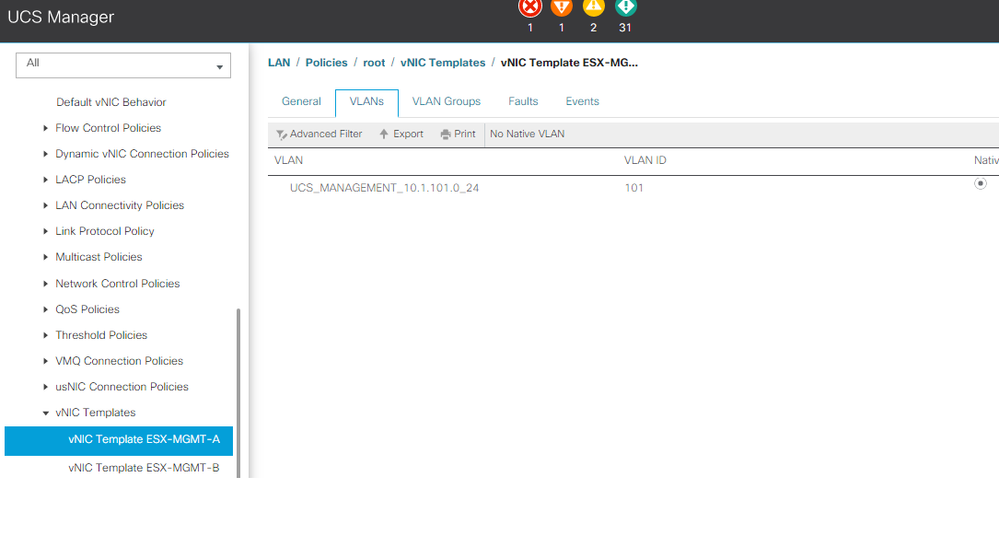
Preparing to migrate a UCS from one location to another - I noticed that the ESX/blade management VLAN 101 is checked as being "Native". However if I look at the switch side of the uplink ports there is no VLAN 101 assigned to be native for those trunks. VLAN 101 is simply a part of the trunk. Was this just an oversight by whoever set this up? The mac addresses for the blades/esx's are visible on the port channels serving the FI uplinks. But I'm kind of surprised this works if UCS is expecting native vlan - ie UNTAGGED frames for this VLAN. Any insight would be appreciated.
SAC-CORE01# sho interface trunk
--------------------------------------------------------------------------------
Port Native Status Port
Vlan Channel
--------------------------------------------------------------------------------
Eth1/3 1 trnk-bndl Po2
Eth1/4 1 trnk-bndl Po2
Eth1/5 1 trnk-bndl Po3
Eth1/6 1 trnk-bndl Po3
STP Forwarding:
Po2 1,9-11,20,30,32,34,36,38,40,42,44,46,48,50,52,54,56,58,91-93,99,101-102,120,192,254,1000,1250
Po3 1,9-11,20,30,32,34,36,38,40,42,44,46,48,50,52,54,56,58,91-93,99,101-102,120,192,254,1000,1250
Solved! Go to Solution.
- Labels:
-
UCS Networking and Storage
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-25-2020 05:12 PM
Hi @CiscoMedMed ,
Your configuration is perfectly fine, and as expected. Let me trace a couple of packet flows for you to see if it helps you understand.
Any host using the vNIC Template ESX-MGMT-A will send untagged frames.
The untagged frame will arrive at the Fabric Interconnect, where it is handled by the virtual interface that maps to the relevant server and be classified as belonging to VLAN 101 (because it is untagged and yout vNIC tempate specifies that the untagged VLAN is VLAN 101)
The frame will be transmitted up your trunked uplink carrying a VLAN tag of 101, which is just what you want.
In the reverse direction, traffic coming in from your upllinks to the Fabric Interconnect with a VLAN tag of 101 will (based on destination MAC address) find that it's exit interface is the virtual interface that's mapped to the vNIC, and since VLAN 101 is configured as Native for this virtual interface, will be transmitted untagged.
I think the concept you may be missing is how the vNIC thing works in UCS Manger. But in very simple terms, when you create a vNIC for a server, a virtual interface gets created in the FIs that map to the vNIC. I've configured a server as closely as possible to your scenario and here is the resultant configuration that appears in UCSM
HX-FI-A# connect nxos Cisco Nexus Operating System (NX-OS) Software <snip> HX-FI-A(nx-os)# show run interface vEthernet 1119 !Command: show running-config interface Vethernet1119 !Time: Sat Dec 26 01:10:42 2020 version 7.0(3)N2(4.12b) interface Vethernet1119 description server 1, VNIC ESX-MGMT-A untagged cos 2 no pinning server sticky pinning server pinning-failure link-down switchport mode trunk switchport trunk native vlan 119 switchport trunk allowed vlan 119 no hardware vethernet mac filtering per-vlan bind interface port-channel1280 channel 1119 service-policy type qos input ep-qos-silver no shutdown
Except my native VLAN is VLAN 119
Forum Tips: 1. Paste images inline - don't attach. 2. Always mark helpful and correct answers, it helps others find what they need.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-25-2020 05:12 PM
Hi @CiscoMedMed ,
Your configuration is perfectly fine, and as expected. Let me trace a couple of packet flows for you to see if it helps you understand.
Any host using the vNIC Template ESX-MGMT-A will send untagged frames.
The untagged frame will arrive at the Fabric Interconnect, where it is handled by the virtual interface that maps to the relevant server and be classified as belonging to VLAN 101 (because it is untagged and yout vNIC tempate specifies that the untagged VLAN is VLAN 101)
The frame will be transmitted up your trunked uplink carrying a VLAN tag of 101, which is just what you want.
In the reverse direction, traffic coming in from your upllinks to the Fabric Interconnect with a VLAN tag of 101 will (based on destination MAC address) find that it's exit interface is the virtual interface that's mapped to the vNIC, and since VLAN 101 is configured as Native for this virtual interface, will be transmitted untagged.
I think the concept you may be missing is how the vNIC thing works in UCS Manger. But in very simple terms, when you create a vNIC for a server, a virtual interface gets created in the FIs that map to the vNIC. I've configured a server as closely as possible to your scenario and here is the resultant configuration that appears in UCSM
HX-FI-A# connect nxos Cisco Nexus Operating System (NX-OS) Software <snip> HX-FI-A(nx-os)# show run interface vEthernet 1119 !Command: show running-config interface Vethernet1119 !Time: Sat Dec 26 01:10:42 2020 version 7.0(3)N2(4.12b) interface Vethernet1119 description server 1, VNIC ESX-MGMT-A untagged cos 2 no pinning server sticky pinning server pinning-failure link-down switchport mode trunk switchport trunk native vlan 119 switchport trunk allowed vlan 119 no hardware vethernet mac filtering per-vlan bind interface port-channel1280 channel 1119 service-policy type qos input ep-qos-silver no shutdown
Except my native VLAN is VLAN 119
Forum Tips: 1. Paste images inline - don't attach. 2. Always mark helpful and correct answers, it helps others find what they need.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-26-2020 10:17 PM
Very helpful indeed. Thank you!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide