- Cisco Community
- Technology and Support
- Security
- VPN
- How to disable ISAKMP default policy on Cisco 2800 router
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2013 12:47 AM
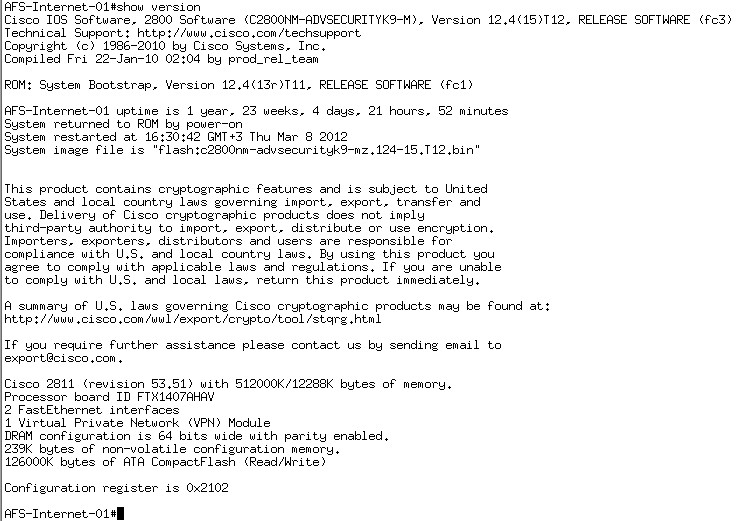
I am having an audit point asking me to disable or remove the default ISAKMP policy on my router. I tried to do that, but I received an error that the command is not supported as below:

If this is not possible on my router which has an IOS version:
So, is it possible to upgrade my router's IOS to the latest version to resolve this issue, which is:
"c2800nm-advsecurityk9-mz.151-4.M6"
If this also will not solve my problem, could I have a formal document from CISCO that on my router it's not supported "disabling the ISAKMP default policy.
I would really appreciate your reply guys.
Thanks in advance,
Solved! Go to Solution.
- Labels:
-
VPN
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2013 02:10 AM
Hi Ebrahim,
The version 15.1(4)M6 do support the command "no crypto isakmp default policy".
Before executing "no crypto isakmp default policy".
:
router#sh cry isakmp default policy
Default IKE policy
Default protection suite of priority 65507
encryption algorithm: AES - Advanced Encryption Standard (128 bit keys).
hash algorithm: Secure Hash Standard
authentication method: Rivest-Shamir-Adleman Signature
Diffie-Hellman group: #5 (1536 bit)
lifetime: 86400 seconds, no volume limit
Default protection suite of priority 65508
encryption algorithm: AES - Advanced Encryption Standard (128 bit keys).
hash algorithm: Secure Hash Standard
authentication method: Pre-Shared Key
Diffie-Hellman group: #5 (1536 bit)
lifetime: 86400 seconds, no volume limit
.
.
.skipped output
After:
router(config)#no cry isakmp default policy
router #sh cry isakmp default policy
router#sh cry isa policy
Global IKE policy
*****
If you upgrade , you should be ale to remove default isakmp policy.
Thanks
Santhosh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2013 01:36 AM
Hi Ebrahim,
The command "no crypto isakmp default policy" was intriduced in 12.4(20)T. Look for "crypto isakmp default policy" section int he following doc.
http://www.cisco.com/en/US/docs/ios/security/command/reference/sec_c4.html#wp1051491.
151-4.M6 does have this command:
route(config)r #sh ver
Cisco IOS Software, Linux Software (I86BI_LINUX-ADVENTERPRISEK9-M), Version 15.1(4)M6, DEVELOPMENT TEST SOFTWARE
router(config)#no crypto isakmp default policy ?
Thanks,
Santhosh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2013 02:02 AM
Thanks Santhosha Shetty for your reply, so could I upgrade my router to this IOS "c2800nm-advsecurityk9-mz.151-4.M6"? and if so, would that will remove/disable the default protection suite, i.e. when I issue the command "show srypto isakmp policy", I won't see the default in below image (which has a 56-bit encryption):

Please advice.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2013 02:10 AM
Hi Ebrahim,
The version 15.1(4)M6 do support the command "no crypto isakmp default policy".
Before executing "no crypto isakmp default policy".
:
router#sh cry isakmp default policy
Default IKE policy
Default protection suite of priority 65507
encryption algorithm: AES - Advanced Encryption Standard (128 bit keys).
hash algorithm: Secure Hash Standard
authentication method: Rivest-Shamir-Adleman Signature
Diffie-Hellman group: #5 (1536 bit)
lifetime: 86400 seconds, no volume limit
Default protection suite of priority 65508
encryption algorithm: AES - Advanced Encryption Standard (128 bit keys).
hash algorithm: Secure Hash Standard
authentication method: Pre-Shared Key
Diffie-Hellman group: #5 (1536 bit)
lifetime: 86400 seconds, no volume limit
.
.
.skipped output
After:
router(config)#no cry isakmp default policy
router #sh cry isakmp default policy
router#sh cry isa policy
Global IKE policy
*****
If you upgrade , you should be ale to remove default isakmp policy.
Thanks
Santhosh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-09-2019 11:48 AM
Another solution would be by creating a costume policy. Once created it will automatically remove the default ones.
Hopes the above helps!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide