- Cisco Community
- Technology and Support
- Security
- VPN
- IPSec over GRE between Cisco UC540 Series and Linux
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
IPSec over GRE between Cisco UC540 Series and Linux
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-03-2012 06:45 PM - edited 02-21-2020 06:02 PM
Hi all,
I've a problem with an IPSec ove GRE Tunnel between a Cisco Router and a Linux Server with Racoon
My goal is that all the traffic that transit from the subnet behind our server that need to reach our Lan should be encrypted (and viceversa, from our LAN to the Server's LAN).
I've tried to configure an IPSec Tunnel but I've some problems and I'm not be able to identify the causes.
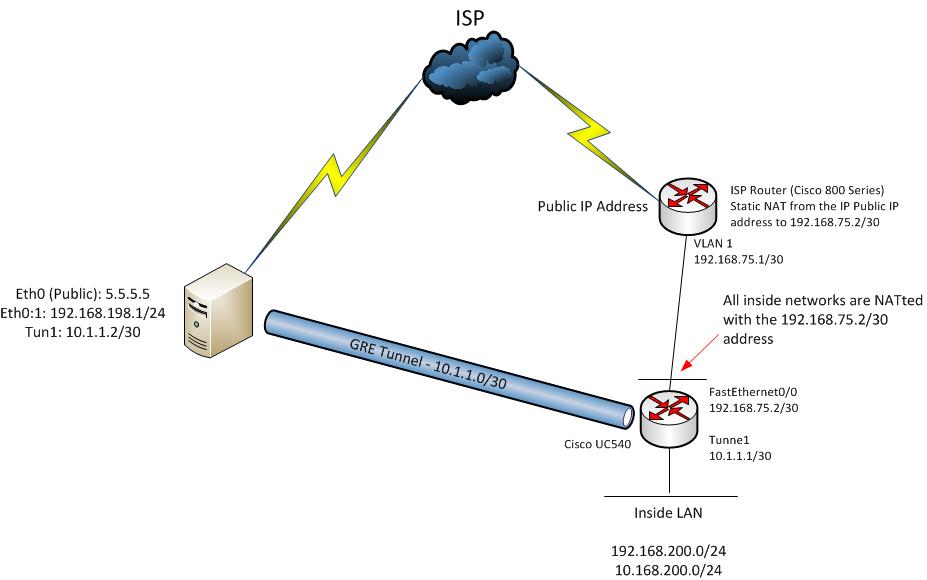
I've this logical situation:
The UC540 configuration is:
crypto keyring SRV
description Keys for Server
pre-shared-key address 10.1.1.2 key <key>
!
crypto isakmp policy 2
encr 3des
authentication pre-share
group 2
crypto isakmp profile Server
keyring SRV
match identity address 10.1.1.2 255.255.255.255
crypto ipsec transform-set srvtransform esp-3des esp-sha-hmac
crypto map srv-cryptomap 1 ipsec-isakmp
set peer 10.1.1.2
set transform-set srvtransform
set pfs group2
set isakmp-profile Server
match address SERVER_VPN
interface Tunnel1
description Connection to Server
ip address 10.1.1.1 255.255.255.252
tunnel source FastEthernet0/0
tunnel destination <Public_IP_SERVER>
crypto map srv-cryptomap
ip access-list extended SERVER_VPN
permit gre host 192.168.75.2 host <Public_IP_SERVER>
permit ip host 10.1.1.1 host 10.1.1.2
permit ip host 10.1.1.1 192.168.198.0 0.0.0.255
permit ip 192.168.200.0 0.0.0.255 host 10.1.1.2
permit ip 10.168.200.0 0.0.0.255 host 10.1.1.2
permit ip 192.168.75.0 0.0.0.255 host 10.1.1.2
permit ip 192.168.200.0 0.0.0.255 192.168.198.0 0.0.0.255
permit ip 10.168.200.0 0.0.0.255 192.168.198.0 0.0.0.255
permit ip 192.168.75.0 0.0.0.255 192.168.198.0 0.0.0.255
deny ip any any
ip access-list extended NONAT-IPSEC
deny ip 10.168.200.0 0.0.0.255 host 10.1.1.2
deny ip 192.168.75.0 0.0.0.255 host 10.1.1.2
deny ip 192.168.200.0 0.0.0.255 host 10.1.1.2
deny ip host 10.1.1.1 host 10.1.1.2
permit ip 192.168.200.0 0.0.0.255 any
permit ip 10.168.200.0 0.0.0.255 any
permit ip 192.168.75.0 0.0.0.255 any
deny ip any any
ip nat inside source route-map NO_NAT interface FastEthernet0/0 overload
route-map NO_NAT permit 10
match ip address NONAT-IPSEC
For completeness I also show you the Racoon configuration that is relative simple. It is composed by two files:
/etc/racoon/racoon.conf : the configuration file used to configure various aspects of the IPsec connection, including authentication methods and encryption algorithms used in the connection
/etc/ipsec-tools.conf : SetKey daemon configuration file that manipulates the key management and security attributes of IPsec in the kernel. This executable is controlled by the racoon key management daemon
/etc/racoon/racoon.conf
path pre_shared_key "/etc/racoon/psk.txt";
path certificate "/etc/racoon/certs";
listen
{
isakmp 10.1.1.2[500];
adminsock disabled;
}
timer
{
natt_keepalive 10 sec;
}
remote 10.1.1.1 {
#Exchange mode for IKE
exchange_mode main;
#When a new key should be generated
lifetime time 86400 sec;
proposal {
encryption_algorithm 3des;
hash_algorithm sha1;
authentication_method pre_shared_key;
dh_group 2;
}
}
#Everybody can initialize the tunnel
sainfo anonymous {
### Diffie-HellMan Group 2 - Key Exchange Protocol
pfs_group 2;
### Encryption algorithms
encryption_algorithm 3des;
#### Authentication algorithms
authentication_algorithm hmac_sha1;
#### Compression for faster trasmission
compression_algorithm deflate;
###When a new key should be generated
lifetime time 86400 sec;
}
/etc/ipsec-tools.conf
#!/usr/sbin/setkey -f
flush;
spdflush;
spdadd 10.1.1.2/32[any] 10.1.1.1/32[any] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
spdadd 10.1.1.1/32[any] 10.1.1.2/32[any] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 10.1.1.1/32[0] 192.168.198.0/24[0] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 192.168.198.0/24[0] 10.1.1.1/32[0] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
spdadd 192.168.75.0/30[0] 10.1.1.2/32[0] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 10.1.1.2/32[0] 192.168.75.0/30[0] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
spdadd 192.168.200.0/24[0] 10.1.1.2/32[0] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 10.1.1.2/30[0] 192.168.200.0/24[0] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
spdadd 192.168.200.0/24[0] 192.168.198.0/24[0] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 192.168.198.0/24[0] 192.168.200.0/24[0] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
spdadd 10.168.200.0/24[0] 192.168.198.0/24[0] any -P in ipsec
esp/tunnel/10.1.1.1-10.1.1.2/require;
spdadd 192.168.198.0/24[0] 10.168.200.0/24[0] any -P out ipsec
esp/tunnel/10.1.1.2-10.1.1.1/require;
These are some tests that I've done:
(No active connection - First time that the two endpoint establish the tunnel)
Ping from 10.1.1.2 to 10.1.1.1 (All works fine also IPSec encapsulation)
Ping from 192.168.198.1 to 10.1.1.1 (All works fine also IPSec encapsulation)
Ping from 192.168.200.0/24 to 10.1.1.2 (All works fine also IPSec encapsulation)
Ping from 10.168.200.0/24 to 10.1.1.2 (All works fine also IPSec encapsulation)
Ping from 192.168.198.1 to 192.168.200.0/24 and 10.1.1.2 to 192.168.200.0/24 - (FAILED with this error on the Cisco UC: 007236: May 4 01:20:50.898: %CRYPTO-4-RECVD_PKT_NOT_IPSEC: Rec'd packet not an IPSEC packet. (ip) vrf/dest_addr= /10.168.200.63, src_addr= 10.1.1.2, prot= 1 )
Ping from 192.168.198.1 to 10.168.200.0/24 and 10.1.1.2 to 10.168.200.0/24 - (FAILED with this error on the Cisco UC: 007236: May 4 01:20:50.898: %CRYPTO-4-RECVD_PKT_NOT_IPSEC: Rec'd packet not an IPSEC packet. (ip) vrf/dest_addr= /10.168.200.63, src_addr= 10.1.1.2, prot= 1 )
This is the "debug crypto isakmp" during the FAILED pings:
007371: ISAKMP (0): received packet from 10.1.1.2 dport 500 sport 500 Global (N) NEW SA
007372: ISAKMP: Found a peer struct for 10.1.1.2, peer port 500
007373: ISAKMP: Locking peer struct 0x8D0EDF90, refcount 1 for crypto_isakmp_process_block
007374: ISAKMP: local port 500, remote port 500
007375: ISAKMP:(0):insert sa successfully sa = 8C921E54
007376: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH
007377: ISAKMP:(0):Old State = IKE_READY New State = IKE_R_MM1
007378: ISAKMP:(0): processing SA payload. message ID = 0
007379: ISAKMP:(0): processing vendor id payload
007380: ISAKMP:(0): vendor ID is DPD
007381: ISAKMP:(0):found peer pre-shared key matching 10.1.1.2
007382: ISAKMP:(0): local preshared key found
007383: ISAKMP : Scanning profiles for xauth ... sdm-ike-profile-1
007384: ISAKMP:(0): Authentication by xauth preshared
007385: ISAKMP:(0):Checking ISAKMP transform 1 against priority 1 policy
007386: ISAKMP: life type in seconds
007387: ISAKMP: life duration (VPI) of 0x0 0x1 0x51 0x80
007388: ISAKMP: encryption 3DES-CBC
007389: ISAKMP: auth pre-share
007390: ISAKMP: hash SHA
007391: ISAKMP: default group 2
007392: ISAKMP:(0):atts are acceptable. Next payload is 0
007393: ISAKMP:(0):Acceptable atts:actual life: 0
007394: ISAKMP:(0):Acceptable atts:life: 0
007395: ISAKMP:(0):Fill atts in sa vpi_length:4
007396: ISAKMP:(0):Fill atts in sa life_in_seconds:86400
007397: ISAKMP:(0):Returning Actual lifetime: 86400
007398: ISAKMP:(0)::Started lifetime timer: 86400.
007399: ISAKMP:(0): processing vendor id payload
007400: ISAKMP:(0): vendor ID is DPD
007401: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
007402: ISAKMP:(0):Old State = IKE_R_MM1 New State = IKE_R_MM1
007403: ISAKMP:(0): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) MM_SA_SETUP
007404: ISAKMP:(0):Sending an IKE IPv4 Packet.
007405: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
007406: ISAKMP:(0):Old State = IKE_R_MM1 New State = IKE_R_MM2
007407: ISAKMP (0): received packet from 10.1.1.2 dport 500 sport 500 Global (R) MM_SA_SETUP
007408: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH
007409: ISAKMP:(0):Old State = IKE_R_MM2 New State = IKE_R_MM3
007410: ISAKMP:(0): processing KE payload. message ID = 0
007411: ISAKMP:(0): processing NONCE payload. message ID = 0
007412: ISAKMP:(0):found peer pre-shared key matching 10.1.1.2
007413: ISAKMP:(2035):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
007414: ISAKMP:(2035):Old State = IKE_R_MM3 New State = IKE_R_MM3
007415: ISAKMP:(2035): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) MM_KEY_EXCH
007416: ISAKMP:(2035):Sending an IKE IPv4 Packet.
007417: ISAKMP:(2035):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
007418: ISAKMP:(2035):Old State = IKE_R_MM3 New State = IKE_R_MM4
007419: ISAKMP (2035): received packet from 10.1.1.2 dport 500 sport 500 Global (R) MM_KEY_EXCH
007420: ISAKMP:(2035):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH
007421: ISAKMP:(2035):Old State = IKE_R_MM4 New State = IKE_R_MM5
007422: ISAKMP:(2035): processing ID payload. message ID = 0
007423: ISAKMP (2035): ID payload
next-payload : 8
type : 1
address : 10.1.1.2
protocol : 17
port : 500
length : 12
007424: ISAKMP:(0):: peer matches ServerNorimberga profile
007425: ISAKMP:(2035):Found ADDRESS key in keyring SRV
007426: ISAKMP:(2035): processing HASH payload. message ID = 0
007427: ISAKMP:(2035):SA authentication status:
authenticated
007428: ISAKMP:(2035):SA has been authenticated with 10.1.1.2
007429: ISAKMP:(2035):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE
007430: ISAKMP:(2035):Old State = IKE_R_MM5 New State = IKE_R_MM5
007431: ISAKMP:(2035):SA is doing pre-shared key authentication using id type ID_IPV4_ADDR
007432: ISAKMP (2035): ID payload
next-payload : 8
type : 1
address : 10.1.1.1
protocol : 17
port : 500
length : 12
007433: ISAKMP:(2035):Total payload length: 12
007434: ISAKMP:(2035): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) MM_KEY_EXCH
007435: ISAKMP:(2035):Sending an IKE IPv4 Packet.
007436: ISAKMP:(2035):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE
007437: ISAKMP:(2035):Old State = IKE_R_MM5 New State = IKE_P1_COMPLETE
007438: ISAKMP:(2035):Input = IKE_MESG_INTERNAL, IKE_PHASE1_COMPLETE
007439: ISAKMP:(2035):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
007440: ISAKMP (2035): received packet from 10.1.1.2 dport 500 sport 500 Global (R) QM_IDLE
007441: ISAKMP: set new node -1096258148 to QM_IDLE
007442: ISAKMP:(2035): processing HASH payload. message ID = -1096258148
007443: ISAKMP:(2035): processing NOTIFY INITIAL_CONTACT protocol 1
spi 0, message ID = -1096258148, sa = 0x8C921E54
007444: ISAKMP:(2035):SA authentication status:
authenticated
007445: ISAKMP:(2035): Process initial contact,
bring down existing phase 1 and 2 SA's with local 10.1.1.1 remote 10.1.1.2 remote port 500
007446: ISAKMP:(2035):deleting node -1096258148 error FALSE reason "Informational (in) state 1"
007447: ISAKMP:(2035):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY
007448: ISAKMP:(2035):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
007449: IPSEC(key_engine): got a queue event with 1 KMI message(s)
007450: Delete IPsec SA by IC, local 10.1.1.1 remote 10.1.1.2 peer port 500
007451: IPSEC(delete_sa): deleting SA,
(sa) sa_dest= 10.1.1.1, sa_proto= 50,
sa_spi= 0x5992AE0C(1502785036),
sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 26
sa_lifetime(k/sec)= (4453102/3600),
(identity) local= 10.1.1.1:0, remote= 10.1.1.2:0,
local_proxy= 10.1.1.1/255.255.255.255/0/0 (type=1),
remote_proxy= 10.1.1.2/255.255.255.255/0/0 (type=1)
007452: IPSEC(update_current_outbound_sa): updated peer 10.1.1.2 current outbound sa to SPI 0
007453: IPSEC(delete_sa): deleting SA,
(sa) sa_dest= 10.1.1.2, sa_proto= 50,
sa_spi= 0x90FFDCD(152042957),
sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 27
sa_lifetime(k/sec)= (4453102/3600),
(identity) local= 10.1.1.1:0, remote= 10.1.1.2:0,
local_proxy= 10.1.1.1/255.255.255.255/0/0 (type=1),
remote_proxy= 10.1.1.2/255.255.255.255/0/0 (type=1)
007454: Delete IPsec SA by IC, local 10.1.1.1 remote 10.1.1.2 peer port 500
007455: IPSEC(delete_sa): deleting SA,
(sa) sa_dest= 10.1.1.1, sa_proto= 50,
sa_spi= 0xA754262B(2807309867),
sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 28
sa_lifetime(k/sec)= (4465713/3600),
(identity) local= 10.1.1.1:0, remote= 10.1.1.2:0,
local_proxy= 192.168.200.0/255.255.255.0/0/0 (type=4),
remote_proxy= 10.1.1.2/255.255.255.255/0/0 (type=1)
007456: IPSEC(update_current_outbound_sa): updated peer 10.1.1.2 current outbound sa to SPI 0
007457: IPSEC(delete_sa): deleting SA,
(sa) sa_dest= 10.1.1.2, sa_proto= 50,
sa_spi= 0x970C112(158384402),
sa_trans= esp-3des esp-sha-hmac , sa_conn_id= 29
sa_lifetime(k/sec)= (4465713/3600),
(identity) local= 10.1.1.1:0, remote= 10.1.1.2:0,
local_proxy= 192.168.200.0/255.255.255.0/0/0 (type=4),
remote_proxy= 10.1.1.2/255.255.255.255/0/0 (type=1)
007458: ISAKMP: set new node -1109512957 to QM_IDLE
007459: ISAKMP:(2035): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) QM_IDLE
007460: ISAKMP:(2035):Sending an IKE IPv4 Packet.
007461: ISAKMP:(2035):purging node -1109512957
007462: ISAKMP:(2035):Input = IKE_MESG_FROM_IPSEC, IKE_PHASE2_DEL
007463: ISAKMP:(2035):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
007464: ISAKMP: set new node -47588763 to QM_IDLE
007465: ISAKMP:(2035): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) QM_IDLE
007466: ISAKMP:(2035):Sending an IKE IPv4 Packet.
007467: ISAKMP:(2035):purging node -47588763
007468: ISAKMP:(2035):Input = IKE_MESG_FROM_IPSEC, IKE_PHASE2_DEL
007469: ISAKMP:(2035):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE
007470: ISAKMP (2035): received packet from 10.1.1.2 dport 500 sport 500 Global (R) QM_IDLE
007471: ISAKMP: set new node -1954382596 to QM_IDLE
007472: ISAKMP:(2035): processing HASH payload. message ID = -1954382596
007473: ISAKMP:(2035): processing SA payload. message ID = -1954382596
007474: ISAKMP:(2035):Checking IPSec proposal 1
007475: ISAKMP: transform 1, ESP_3DES
007476: ISAKMP: attributes in transform:
007477: ISAKMP: SA life type in seconds
007478: ISAKMP: SA life duration (VPI) of 0x0 0x1 0x51 0x80
007479: ISAKMP: encaps is 1 (Tunnel)
007480: ISAKMP: authenticator is HMAC-SHA
007481: ISAKMP: group is 2
007482: ISAKMP:(2035):atts are acceptable.
007483: IPSEC(validate_proposal_request): proposal part #1
007484: IPSEC(initialize_sas): invalid IPv4 proxy IDs
007485: ISAKMP:(2035): IPSec policy invalidated proposal with error 32
007486: ISAKMP:(2035): phase 2 SA policy not acceptable! (local 10.1.1.1 remote 10.1.1.2)
007487: ISAKMP: set new node 2106783083 to QM_IDLE
007488: ISAKMP:(2035):Sending NOTIFY PROPOSAL_NOT_CHOSEN protocol 3
spi 2272909024, message ID = 2106783083
007489: ISAKMP:(2035): sending packet to 10.1.1.2 my_port 500 peer_port 500 (R) QM_IDLE
007490: ISAKMP:(2035):Sending an IKE IPv4 Packet.
007491: ISAKMP:(2035):purging node 2106783083
007492: ISAKMP:(2035):deleting node -1954382596 error TRUE reason "QM rejected"
007493: ISAKMP:(2035):Node -1954382596, Input = IKE_MESG_FROM_PEER, IKE_QM_EXCH
007494: ISAKMP:(2035):Old State = IKE_QM_READY New State = IKE_QM_READY
007495: ISAKMP (2035): received packet from 10.1.1.2 dport 500 sport 500 Global (R) QM_IDLE
007496: ISAKMP:(2035): phase 2 packet is a duplicate of a previous packet.
007497: ISAKMP:(2035): retransmitting due to retransmit phase 2
007498: ISAKMP:(2035): ignoring retransmission,because phase2 node marked dead -1954382596
007499: ISAKMP:(2033):purging node -920717814
007500: ISAKMP (2035): received packet from 10.1.1.2 dport 500 sport 500 Global (R) QM_IDLE
007501: ISAKMP:(2035): phase 2 packet is a duplicate of a previous packet.
007502: ISAKMP:(2035): retransmitting due to retransmit phase 2
007503: ISAKMP:(2035): ignoring retransmission,because phase2 node marked dead -1954382596
If I make some show commands I have:
UC540#sh crypto isakmp peers
Peer: 10.1.1.2 Port: 500 Local: 10.1.1.1
Phase1 id: 10.1.1.2
UC540#show crypto isakmp sa
IPv4 Crypto ISAKMP SA
dst src state conn-id status
10.1.1.1 10.1.1.2 QM_IDLE 2035 ACTIVE Server
Sorry for the long post!
Hope that someone can help me with this issue or indicate me some possibile solutions or tests.
If you need other info do not hesitate to ask me.
Thank you in advance.
- Labels:
-
IPSEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-05-2012 03:08 AM
hello
does the UC540 have a route to to the linux server network 192.168.198.0/24 via its tunnel interface?
if not, you can add a static route:
ip route 192.168.198.0 255.255.255.0 Tunnel1
check also that the linux server has a route to the UC540 network 192.168.200.0/24 via its tunnel interface.
hth
andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-05-2012 07:19 AM
Hi andy,
thanks for your reply but unfortunately the UC540 and the Linux Server has all the routes.
UC540#sh ip route
[...cut..]
S 192.168.198.0/24 is directly connected, Tunnel1
[...cut...]
SRV~# ip r s
10.1.1.0/30 dev tun1 proto kernel scope link src 10.1.1.2
10.168.200.0/24 via 10.1.1.1 dev tun1
192.168.198.0/24 dev eth0 proto kernel scope link src 192.168.198.1
192.168.200.0/24 via 10.1.1.1 dev tun1
It's a very strange issue.... I think that the "key" to resolve this issue is in the log message:
007236: May 4 01:20:50.898: %CRYPTO-4-RECVD_PKT_NOT_IPSEC: Rec'd packet not an IPSEC packet. (ip) vrf/dest_addr= /10.168.200.63, src_addr= 10.1.1.2, prot= 1
It seems that the packet arrives but not encrypted....The question is....why if the configuration are the same, the packets sometimes are encrypted and sometimes not? mmmmm...
I appreciate the attempt to help me.
Thanks again.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

