- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Split Tunnel can not reach any LAN.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2018 12:17 PM - edited 11-16-2018 12:20 PM
ASA Version 9.1(2)
!
hostname Admin-Anyconnect-ASA
xlate per-session deny tcp any4 any4
xlate per-session deny tcp any4 any6
xlate per-session deny tcp any6 any4
xlate per-session deny tcp any6 any6
xlate per-session deny udp any4 any4 eq domain
xlate per-session deny udp any4 any6 eq domain
xlate per-session deny udp any6 any4 eq domain
xlate per-session deny udp any6 any6 eq domain
names
ip local pool vpnpool 172.16.199.10-172.16.199.240 mask 255.255.255.0
ip local pool WaterAcess 172.16.198.10-172.16.198.254 mask 255.255.255.0
!
interface GigabitEthernet0/0
speed 100
duplex full
nameif outside
security-level 0
ip address XXXXXXX
!
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 172.16.199.254 255.255.255.0
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/5
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
management-only
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
clock timezone MST -7
clock summer-time MDT recurring
same-security-traffic permit inter-interface
same-security-traffic permit intra-interface
object network obj-AnyconnectPool
subnet 172.16.199.0 255.255.255.0
object network inside
subnet 172.16.199.0 255.255.255.0
object network NETWORK_OBJ_172.16.199.0_24
subnet 172.16.199.0 255.255.255.0
object network WaterAccess
subnet 192.168.70.0 255.255.255.0
object network NETWORK_OBJ_172.16.198.0_24
subnet 172.16.198.0 255.255.255.0
object network test
subnet 172.16.99.0 255.255.255.0
object-group network GRP-INSIDE-NETWORK
network-object 192.168.0.0 255.255.0.0
network-object 172.16.199.0 255.255.255.0
network-object 172.16.99.0 255.255.255.0
access-list xyz standard permit 192.168.0.0 255.255.0.0
access-list XYZ standard permit 172.16.0.0 255.255.0.0
access-list XYZ standard permit 172.16.199.0 255.255.255.0
access-list AnyConnect_Client_Local_Print extended deny ip any4 any4
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq lpd
access-list AnyConnect_Client_Local_Print remark IPP: Internet Printing Protocol
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 631
access-list AnyConnect_Client_Local_Print remark Windows' printing port
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 9100
access-list AnyConnect_Client_Local_Print remark mDNS: multicast DNS protocol
access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.251 eq 5353
access-list AnyConnect_Client_Local_Print remark LLMNR: Link Local Multicast Name Resolution protocol
access-list AnyConnect_Client_Local_Print extended permit udp any4 host 224.0.0.252 eq 5355
access-list AnyConnect_Client_Local_Print remark TCP/NetBIOS protocol
access-list AnyConnect_Client_Local_Print extended permit tcp any4 any4 eq 137
access-list AnyConnect_Client_Local_Print extended permit udp any4 any4 eq netbios-ns
access-list Split-Water standard permit 192.168.70.0 255.255.255.0
pager lines 24
logging enable
logging buffered debugging
logging asdm warnings
mtu outside 1500
mtu inside 1500
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-713.bin
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
nat (inside,outside) source static any any destination static NETWORK_OBJ_172.16.199.0_24 NETWORK_OBJ_172.16.199.0_24 no-proxy-arp route-lookup
nat (inside,outside) source static WaterAccess WaterAccess destination static NETWORK_OBJ_172.16.198.0_24 NETWORK_OBJ_172.16.198.0_24 no-proxy-arp route-lookup
!
object network inside
nat (inside,outside) dynamic interface
route outside 0.0.0.0 0.0.0.0 xxxxx
route inside 172.16.1.0 255.255.255.0 172.16.199.253 1
route inside 172.16.4.0 255.255.255.0 172.16.199.253 1
route inside 172.16.99.0 255.255.255.0 172.16.199.253 1
route inside 192.168.0.0 255.255.0.0 172.16.199.253 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
aaa-server Radius protocol radius
aaa-server Radius (inside) host 192.168.0.7
timeout 5
key *****
aaa-server RADIUSSERVERS protocol radius
max-failed-attempts 5
aaa-server RADIUSSERVERS (inside) host 192.168.0.7
timeout 60
key *****
user-identity default-domain LOCAL
aaa authentication ssh console LOCAL
aaa authentication telnet console LOCAL
aaa authentication http console LOCAL
http server enable
http 0.0.0.0 0.0.0.0 inside
http 172.16.99.0 255.255.255.0 inside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
crypto ipsec ikev2 ipsec-proposal DES
protocol esp encryption des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal 3DES
protocol esp encryption 3des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES
protocol esp encryption aes
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES192
protocol esp encryption aes-192
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES256
protocol esp encryption aes-256
protocol esp integrity sha-1 md5
crypto ipsec security-association pmtu-aging infinite
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev2 ipsec-proposal AES256 AES192 AES 3DES DES
crypto map outside_map 65535 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map outside_map interface outside
crypto ca trustpoint ASDM_TrustPoint0
enrollment terminal
subject-name CN=XYZ
keypair XYZ
crl configure
crypto ca trustpoint ASDM_TrustPoint1
enrollment terminal
crl configure
crypto ca trustpoint ASDM_TrustPoint2
enrollment terminal
crl configure
crypto ca trustpoint ASDM_TrustPoint3
enrollment terminal
crl configure
crypto ca trustpoint ASDM_TrustPoint4
keypair ASDM_TrustPoint4
crl configure
crypto ca trustpool policy
quit
crypto ikev2 policy 1
encryption aes-256
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 10
encryption aes-192
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 20
encryption aes
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 30
encryption 3des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 40
encryption des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 enable outside client-services port 443
crypto ikev2 remote-access trustpoint ASDM_TrustPoint0
telnet 172.16.99.0 255.255.255.0 inside
telnet 172.16.199.253 255.255.255.255 inside
telnet timeout 5
ssh 172.16.99.0 255.255.255.0 inside
ssh 192.168.168.0 255.255.255.0 inside
ssh 172.16.199.253 255.255.255.255 inside
ssh timeout 5
ssh version 2
ssh key-exchange group dh-group1-sha1
console timeout 0
management-access inside
threat-detection basic-threat
threat-detection statistics host
threat-detection statistics port
threat-detection statistics protocol
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
ntp server 91.189.94.4 source outside prefer
ssl encryption 3des-sha1 des-sha1 aes128-sha1 aes256-sha1
ssl trust-point ASDM_TrustPoint4 inside
ssl trust-point ASDM_TrustPoint4 outside
ssl trust-point ASDM_TrustPoint4 outside vpnlb-ip
webvpn
enable outside
anyconnect image disk0:/anyconnect-win-3.1.14018-k9.pkg 3
anyconnect image disk0:/anyconnect-linux64-4.6.01103-webdeploy-k9.pkg 5
anyconnect image disk0:/anyconnect-macos-4.6.01103-webdeploy-k9.pkg 6
anyconnect profiles xxx disk0:/
anyconnect enable
tunnel-group-list enable
group-policy "XXXX" internal
group-policy "XXXX" attributes
wins-server none
dns-server value 192.168.0.3 192.168.0.39
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value XXXX
default-domain value XXXX
webvpn
anyconnect mtu 1280
anyconnect profiles value XXX type user
group-policy GroupPolicy_WaterAccess internal
group-policy GroupPolicy_WaterAccess attributes
wins-server none
dns-server value 192.168.0.3
vpn-tunnel-protocol ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Water
default-domain none
address-pool vpnpool
authentication-server-group RADIUSSERVERS
default-group-policy "]"
tunnel-group "]" webvpn-attributes
group-alias "]" enable
tunnel-group WaterAccess type remote-access
tunnel-group WaterAccess general-attributes
address-pool WaterAcess
default-group-policy GroupPolicy_WaterAccess
tunnel-group WaterAccess webvpn-attributes
group-alias WaterAccess enable
!
class-map inspection_default
match default-inspection-traffic
class-map cx_acl
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
inspect pptp
inspect icmp
class cx_acl
cxsc fail-open
!
service-policy global_policy global
prompt hostname context
no compression anyconnect-ssl http-comp
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly 15
subscribe-to-alert-group configuration periodic monthly 15
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:c3ac8273a07437993db8fab0abb9dc5c
: end
Admin-Anyconnect-ASA#
here is the config, I am trying to use Split-tunnel for water access, and I am not able to reach any LAN when I connected as an anyconnect client, I can see 192.168.70.0/24(watersomthing) in my local route table. In LAN, 192.168.70.0 could be reached by the ASA. Does anyone know the reason?
Solved! Go to Solution.
- Labels:
-
AnyConnect
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 03:32 PM
If you put the static route in what is the output of a traceroute to the 172.16.198.x network?
Does it get routed to the RAS ASA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2018 05:05 PM
You may need a nat exemption from your anyconnect vpn pool to the network you're trying to connect to on the inside interface. It looks like you attempted this, but you're one network off:
Your anyconnect addresses are:
ip local pool vpnpool 172.16.199.10-172.16.199.240 mask 255.255.255.0
but the nat is:
nat (inside,outside) source static WaterAccess WaterAccess destination static NETWORK_OBJ_172.16.198.0_24 NETWORK_OBJ_172.16.198.0_24 no-proxy-arp route-lookup
Try to add this:
nat (inside,outside) source static WaterAccess WaterAccess destination static NETWORK_OBJ_172.16.199.0_24 NETWORK_OBJ_172.16.199.0_24 no-proxy-arp route-lookup
Give this a try
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2018 11:06 PM
thank you for helping, the 199.x subnet is a different group, wateraccesssubnet is 198.x. subnet 199.x is full tunnel now, I want to make a new group for different client .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-17-2018 02:36 PM
yeharold94@gmail.com wrote:
thank you for helping, the 199.x subnet is a different group, wateraccesssubnet is 198.x. subnet 199.x is full tunnel now, I want to make a new group for different client .
I suspect that this may not be the case, though I'm not able to test it now, take a look at the config snippet I posted below. Since you have two different address pools configured, one in the tunnel-group a.k.a connection profile (address pool indicated in red), and then a different one in the group policy itself ( group policy in green, address pool indicated in blue). I suspect that the group policy is going to override it and be assigned to the user. This group policy address pool is the .199. I would however like you to test this theory by connecting yourself, and seeing what address you are assigned.
group-policy GroupPolicy_WaterAccess attributes wins-server none dns-server value 192.168.0.3 vpn-tunnel-protocol ssl-client split-tunnel-policy tunnelspecified split-tunnel-network-list value Split-Water default-domain none address-pool vpnpool tunnel-group WaterAccess type remote-access tunnel-group WaterAccess general-attributes address-pool WaterAcess default-group-policy GroupPolicy_WaterAccess tunnel-group WaterAccess webvpn-attributes group-alias WaterAccess enable ip local pool vpnpool 172.16.199.10-172.16.199.240 mask 255.255.255.0 ip local pool WaterAcess 172.16.198.10-172.16.198.254 mask 255.255.255.0
On another note, can you also post the output of "show run all | include sysopt"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-18-2018 03:15 PM
group-policy "GroupPolicy_full VPN" attributes
wins-server none
dns-server value 192.168.0.3 192.168.0.39
vpn-tunnel-protocol ikev2 ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value full
default-domain value ad.tsuutina.com
webvpn
anyconnect mtu 1280
anyconnect profiles value full type user
group-policy GroupPolicy_WaterAccess internal
group-policy GroupPolicy_WaterAccess attributes
wins-server none
dns-server value 192.168.0.3
vpn-tunnel-protocol ssl-client
split-tunnel-policy tunnelspecified
split-tunnel-network-list value Split-Water
default-domain none
ip local pool vpnpool 172.16.199.10-172.16.199.240 mask 255.255.255.0
ip local pool WaterAcess 172.16.198.10-172.16.198.254 mask 255.255.255.0
Admin-Anyconnect-ASA# show run all | include sysopt
no sysopt connection timewait
sysopt connection tcpmss 1380
sysopt connection tcpmss minimum 0
sysopt connection permit-vpn
sysopt connection reclassify-vpn
no sysopt connection preserve-vpn-flows
no sysopt radius ignore-secret
no sysopt noproxyarp outside
no sysopt noproxyarp insideAdmin-Anyconnect-ASA# show run all | include sysopt
no sysopt connection timewait
sysopt connection tcpmss 1380
sysopt connection tcpmss minimum 0
sysopt connection permit-vpn
sysopt connection reclassify-vpn
no sysopt connection preserve-vpn-flows
no sysopt radius ignore-secret
no sysopt noproxyarp outside
no sysopt noproxyarp inside
tunnel-group "full VPN" type remote-access
tunnel-group "full VPN" general-attributes
address-pool vpnpool
authentication-server-group RADIUSSERVERS
default-group-policy "full"
tunnel-group "full VPN" webvpn-attributes
group-alias "full VPN" enable
tunnel-group WaterAccess type remote-access
tunnel-group WaterAccess general-attributes
address-pool WaterAcess
default-group-policy GroupPolicy_WaterAccess
tunnel-group WaterAccess webvpn-attributes
group-alias WaterAccess enable
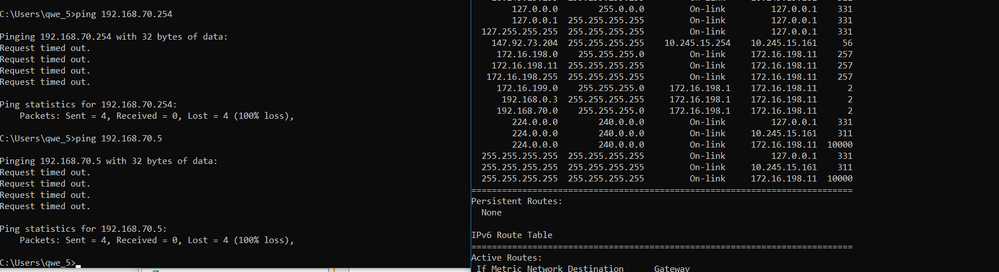
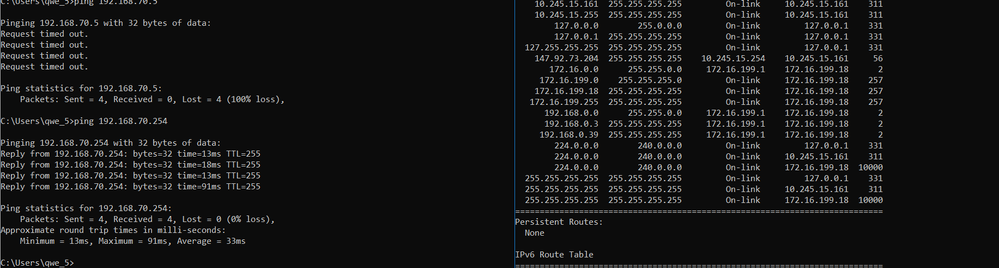
the picture is my PC route print from different groups, by the way, when I connected to WaterAccess, I will reconnect in few mins. Do you have any idea why
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-19-2018 10:22 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 07:52 AM
Ethernet adapter Ethernet 2:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 172.16.198.10
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
IPv4 Route Table
===========================================================================
Active Routes:
Network Destination Netmask Gateway Interface Metric
0.0.0.0 0.0.0.0 172.16.99.254 172.16.99.90 40
127.0.0.0 255.0.0.0 On-link 127.0.0.1 331
127.0.0.1 255.255.255.255 On-link 127.0.0.1 331
127.255.255.255 255.255.255.255 On-link 127.0.0.1 331
outside address 255.255.255.255 172.16.99.254 172.16.99.90 41
172.16.99.0 255.255.255.0 On-link 172.16.99.90 296
172.16.99.90 255.255.255.255 On-link 172.16.99.90 296
172.16.99.255 255.255.255.255 On-link 172.16.99.90 296
172.16.198.0 255.255.255.0 On-link 172.16.198.10 257
172.16.198.10 255.255.255.255 On-link 172.16.198.10 257
172.16.198.255 255.255.255.255 On-link 172.16.198.10 257
172.16.199.0 255.255.255.0 172.16.198.1 172.16.198.10 2
192.168.0.3 255.255.255.255 172.16.198.1 172.16.198.10 2
192.168.0.7 255.255.255.255 172.16.99.254 172.16.99.90 41
192.168.0.39 255.255.255.255 172.16.99.254 172.16.99.90 41
192.168.70.0 255.255.255.0 172.16.198.1 172.16.198.10 2
224.0.0.0 240.0.0.0 On-link 127.0.0.1 331
224.0.0.0 240.0.0.0 On-link 172.16.99.90 296
224.0.0.0 240.0.0.0 On-link 172.16.198.10 10000
255.255.255.255 255.255.255.255 On-link 127.0.0.1 331
255.255.255.255 255.255.255.255 On-link 172.16.99.90 296
255.255.255.255 255.255.255.255 On-link 172.16.198.10 10000
that information is from my PC when I connected to anyconnect.
I have 192.168.70.0 in my route table, but when I try to reach (ping) this subnet, I get information below
C:\WINDOWS\system32>ping 192.168.70.254
Pinging 192.168.70.254 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 192.168.70.254:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
from my ASA I can reach 192.168.70.0 subnet, I was wondering why I can not reach 192.168.70.0 by my PC.
My configuration of remote VPN attached above
Thank you for your helping
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 09:06 AM
Is the ASA the default gateway for the 192.168.70.0/24 network? If not, does that network have a route to the VPN IP Pool network (172.16.198.0/24)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 11:11 AM
it is not the gateway, it goes to one of my local Vlan which is subnet 192.168.70.0/24, I have the route on vpn 172.16.198.0 to 192.168.70.0, and I can see that route on my PC.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 11:21 AM
What device is the default gateway for 192.168.70.0 network? The ASA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 12:00 PM - edited 11-20-2018 12:02 PM
Admin-Anyconnect-ASA# sh route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is 147.92.73.201 to network 0.0.0.0
S 172.16.199.18 255.255.255.255 [1/0] via outside address, outside
S 172.16.198.10 255.255.255.255 [1/0] via outside address, outside
C 172.16.199.0 255.255.255.0 is directly connected, inside
S 172.16.4.0 255.255.255.0 [1/0] via 172.16.199.253, inside
S 172.16.1.0 255.255.255.0 [1/0] via 172.16.199.253, inside
S 172.16.99.0 255.255.255.0 [1/0] via 172.16.199.253, inside
C outside address 255.255.255.248 is directly connected, outside
S 192.168.70.0 255.255.255.0 [1/0] via 172.16.199.253, inside
S* 0.0.0.0 0.0.0.0 [1/0] via outsdie address , outside
S 192.168.0.0 255.255.0.0 [1/0] via 172.16.199.253, inside
Admin-Anyconnect-ASA#
the is my route table on my ASA
S* 0.0.0.0/0 [1/0] via 192.168.254.254
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.10.10.0/24 is directly connected, Vlan30
L 10.10.10.253/32 is directly connected, Vlan30
172.16.0.0/16 is variably subnetted, 14 subnets, 3 masks
C 172.16.1.0/24 is directly connected, Vlan110
L 172.16.1.254/32 is directly connected, Vlan110
C 172.16.4.0/24 is directly connected, Vlan95
L 172.16.4.254/32 is directly connected, Vlan95
C 172.16.99.0/24 is directly connected, Vlan99
L 172.16.99.254/32 is directly connected, Vlan99
C 172.16.199.0/24 is directly connected, Vlan199
L 172.16.199.253/32 is directly connected, Vlan199
C 172.16.250.0/30 is directly connected, Vlan80
L 172.16.250.1/32 is directly connected, Vlan80
C 172.16.251.0/30 is directly connected, Vlan82
L 172.16.251.1/32 is directly connected, Vlan82
C 172.16.251.8/30 is directly connected, Vlan84
L 172.16.251.9/32 is directly connected, Vlan84
172.20.0.0/16 is variably subnetted, 4 subnets, 2 masks
C 172.20.0.0/24 is directly connected, Vlan100
L 172.20.0.41/32 is directly connected, Vlan100
C 172.20.1.0/24 is directly connected, Vlan201
L 172.20.1.209/32 is directly connected, Vlan201
192.168.0.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.0.0/24 is directly connected, Vlan5
L 192.168.0.20/32 is directly connected, Vlan5
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Vlan6
L 192.168.1.254/32 is directly connected, Vlan6
S 192.168.3.0/24 [1/0] via 192.168.20.253
192.168.7.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.7.0/24 is directly connected, Vlan7
L 192.168.7.254/32 is directly connected, Vlan7
192.168.20.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.20.0/24 is directly connected, Vlan20
L 192.168.20.254/32 is directly connected, Vlan20
192.168.30.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.30.0/24 is directly connected, Vlan10
L 192.168.30.254/32 is directly connected, Vlan10
C 192.168.40.0/23 is directly connected, Vlan40
192.168.40.0/32 is subnetted, 1 subnets
L 192.168.40.254 is directly connected, Vlan40
C 192.168.60.0/23 is directly connected, Vlan60
192.168.61.0/32 is subnetted, 1 subnets
L 192.168.61.254 is directly connected, Vlan60
192.168.65.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.65.0/24 is directly connected, Vlan65
L 192.168.65.254/32 is directly connected, Vlan65
192.168.70.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.70.0/24 is directly connected, Vlan70
L 192.168.70.254/32 is directly connected, Vlan70
192.168.90.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.90.0/24 is directly connected, Vlan90
L 192.168.90.254/32 is directly connected, Vlan90
S 192.168.162.0/23 [1/0] via 172.16.99.237
192.168.254.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.254.0/24 is directly connected, Vlan250
L 192.168.254.253/32 is directly connected, Vlan250
TTN-ADM-CRSW-04#
that is my route on my switch
thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 12:08 PM
Define a static route on the switch to route the 172.16.198.0/24 network to the inside interface of the ASA.
ip route 172.16.198.0 255.255.255.0 172.16.199.254
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 03:17 PM
no it is not working,
Now, I use another ASA and go to another gate to get to the internet.
Thank you for helping.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-20-2018 03:32 PM
If you put the static route in what is the output of a traceroute to the 172.16.198.x network?
Does it get routed to the RAS ASA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-21-2018 08:55 AM
Gateway of last resort is 192.168.254.254 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 192.168.254.254
10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
C 10.10.10.0/24 is directly connected, Vlan30
L 10.10.10.253/32 is directly connected, Vlan30
172.16.0.0/16 is variably subnetted, 15 subnets, 3 masks
C 172.16.1.0/24 is directly connected, Vlan110
L 172.16.1.254/32 is directly connected, Vlan110
C 172.16.4.0/24 is directly connected, Vlan95
L 172.16.4.254/32 is directly connected, Vlan95
C 172.16.99.0/24 is directly connected, Vlan99
L 172.16.99.254/32 is directly connected, Vlan99
S 172.16.198.0/24 [1/0] via 172.16.199.254
C 172.16.199.0/24 is directly connected, Vlan199
L 172.16.199.253/32 is directly connected, Vlan199
C 172.16.250.0/30 is directly connected, Vlan80
L 172.16.250.1/32 is directly connected, Vlan80
C 172.16.251.0/30 is directly connected, Vlan82
L 172.16.251.1/32 is directly connected, Vlan82
C 172.16.251.8/30 is directly connected, Vlan84
L 172.16.251.9/32 is directly connected, Vlan84
172.20.0.0/16 is variably subnetted, 4 subnets, 2 masks
C 172.20.0.0/24 is directly connected, Vlan100
L 172.20.0.41/32 is directly connected, Vlan100
C 172.20.1.0/24 is directly connected, Vlan201
L 172.20.1.209/32 is directly connected, Vlan201
192.168.0.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.0.0/24 is directly connected, Vlan5
L 192.168.0.20/32 is directly connected, Vlan5
192.168.1.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.1.0/24 is directly connected, Vlan6
L 192.168.1.254/32 is directly connected, Vlan6
S 192.168.3.0/24 [1/0] via 192.168.20.253
192.168.7.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.7.0/24 is directly connected, Vlan7
L 192.168.7.254/32 is directly connected, Vlan7
192.168.20.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.20.0/24 is directly connected, Vlan20
L 192.168.20.254/32 is directly connected, Vlan20
192.168.30.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.30.0/24 is directly connected, Vlan10
L 192.168.30.254/32 is directly connected, Vlan10
C 192.168.40.0/23 is directly connected, Vlan40
192.168.40.0/32 is subnetted, 1 subnets
L 192.168.40.254 is directly connected, Vlan40
C 192.168.60.0/23 is directly connected, Vlan60
192.168.61.0/32 is subnetted, 1 subnets
L 192.168.61.254 is directly connected, Vlan60
192.168.65.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.65.0/24 is directly connected, Vlan65
L 192.168.65.254/32 is directly connected, Vlan65
192.168.77.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.77.0/24 is directly connected, Vlan77
L 192.168.77.254/32 is directly connected, Vlan77
192.168.90.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.90.0/24 is directly connected, Vlan90
L 192.168.90.254/32 is directly connected, Vlan90
S 192.168.162.0/23 [1/0] via 172.16.99.237
192.168.254.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.254.0/24 is directly connected, Vlan250
L 192.168.254.253/32 is directly connected, Vlan250
I created another ip for testing, this time I would like to use 192.168.77.0/24 as Loacl address.
S 172.16.198.10 255.255.255.255 [1/0] via , outside C 172.16.199.0 255.255.255.0 is directly connected, inside S 172.16.4.0 255.255.255.0 [1/0] via 172.16.199.253, inside S 172.16.1.0 255.255.255.0 [1/0] via 172.16.199.253, inside S 172.16.99.0 255.255.255.0 [1/0] via 172.16.199.253, inside C 147.92.73.200 255.255.255.248 is directly connected, outside S* 0.0.0.0 0.0.0.0 [1/0] via , outside S 192.168.0.0 255.255.0.0 [1/0] via 172.16.199.253, inside
and It works!!! thank you so much
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide