Hello,I have an IKEv2 Site-to-Site IPSec tunnel (VTI with static routing) between ASA firewall and 2 stateless HA routers configured with HSRP (IPSec end point is HSRP VIP hosted on the HSRP active router).Despite the fact it is not stateful (not sup...
VPN
- Mark all as New
- Mark all as Read
- Float this item to the top
- Subscribe
- Bookmark
- Subscribe to RSS Feed
- Threaded format
- Linear Format
- Sort by Topic Start Date
The content you are looking for has been archived. View related content below.
-
AAA
(3) -
Access Control Server (ACS)
(1) -
AnyConnect
(6,512) -
Appliances
(1) -
ASA
(1) -
ASR 1000 Series
(1) -
ATAs and Gateways and Accessories
(1) -
Buying Recommendation
(34) -
Catalyst Switch
(1) -
Cisco Adaptive Security Appliance (ASA)
(28) -
Cisco Bugs
(1) -
Cisco Cafe
(14) -
Cisco Cloud Services Router
(2) -
Cisco DNA
(2) -
Cisco DNA Automation
(1) -
Cisco Firepower Device Manager (FDM)
(2) -
Cisco Firepower Management Center (FMC)
(4) -
Cisco Firepower Threat Defense (FTD)
(6) -
Cisco Software
(6) -
Cisco Start India
(1) -
Clientless SSL
(266) -
Cloud Security
(1) -
Community Feedback Forum
(15) -
Community Ideas
(9) -
Compliance and Posture
(2) -
Conferencing
(1) -
Connectivity Issues and VPN
(1) -
Device Admin
(1) -
DMVPN
(733) -
Duo
(63) -
Emergency Responder
(1) -
Enterprise Agreement
(1) -
Firewalls
(1) -
FlexVPN
(169) -
General
(1) -
GetVPN
(135) -
Identity Services Engine (ISE)
(5) -
IPSEC
(4,294) -
ISR 1000 Series
(2) -
ISR 4000 Series
(4) -
LAN Switching
(2) -
License
(1) -
Network Management
(21) -
New Document Idea
(1) -
NGFW Firewalls
(3) -
Optical Networking
(1) -
Other Cisco DNA
(1) -
Other Collaboration Topics
(3) -
Other Community Feedback
(1) -
Other IP Telephony
(1) -
Other NAC
(1) -
Other Network
(13) -
Other Network Security Topics
(8) -
Other Networking
(6) -
Other Routers
(8) -
Other Routing
(13) -
Other Security Topics
(2) -
Other Switches
(2) -
Other Switching
(1) -
Other VPN Topics
(13,559) -
Other Wireless and Mobility Subjects
(1) -
Other Wireless Topics
(2) -
Physical Security
(3) -
Remote Access
(5,842) -
Routers
(1) -
Routing
(2) -
Routing Protocols
(12) -
RV340
(1) -
Security Certifications
(1) -
Security Management
(3) -
Small Business Routers
(2) -
Small Business Switches
(1) -
Storage Networking
(1) -
Umbrella
(26) -
VPN
(22,039) -
VPN and AnyConnect
(1) -
VPN y AnyConnect
(4) -
WAN
(2) -
Web Security
(2) -
Wired
(1) -
Wireless Network Management
(3) -
Wireless Security
(5) -
Wireless Security and Network Management
(1)
- « Previous
- Next »
Forum Posts
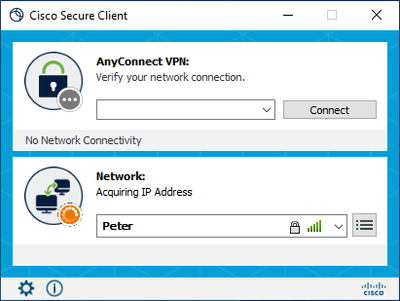
We have tried upgrading from Cisco AnyConnect 4.10.07073 to Secure Client 5.1.1.42 with NAM connecting to wired and wireless networks.After the upgrade NAM fails to acquire the IP address from the phone.Connecting to enterprise EAP SSIDs and other us...
Hello,FTD's 2110 at 7.3.1.1.I have two datacenters running that code on 2110s. They have the same configuration for the most part and the same size fiber internet 500 Mbps circuit. Coming in on VPN1, running a speed test from my home connection is ab...
I have a weird situation I need to connect to two sepaate VPN (not at the same time).One of these requires Cisco Secure Client 5.x the second works with Any Connect 4.x.I have Cisco Secure Client 5.x installed, if i try connecting to the VPN that use...
After starting anyconnect I find network connectivity stops working under WSL2 (Windows Substem for Linux)the fix seems to be: Get-NetAdapter | Where-Object {$_.InterfaceDescription -Match "Cisco AnyConnect"} | Set-NetIPInterface -InterfaceMetric 400...
Hello, as part of my preparation for CCNA Security I've been making up my own topologies and configuring them, however, I need a little help with this one. In the topology (included .pka), I configured VLANs, Port Security, OSPF, OSPF Authentication ...
Hi, I have one issue with IPSec tunnel Lan-to-Lan between ASA 5525x (v9.8) and ASA FPR 2110 (v9.16). My Tunnel is up but ping between each client was not successful. Both peer status sh cry isakmp sa in "MM_ACTIVE".I ran packet-tracer icmp between pe...
Hi EveryoneI'm using a trial version of ASAv and i believe it has full functionality but is limited in 100kbps. I'm trying to set up remote access anyconnect vpn which authenticates to our NPS radius server. As you can see in the radius debug, it see...
I can't seem to overcome the following error when configuring AnyConnect with SAML according to https://community.cisco.com/t5/security-knowledge-base/configure-anyconnect-with-saml-authentication-on-ftd-managed-via/ta-p/4467779:Deployment Failed: Us...
Hi,I have a newly reinstalled OS Windows 11 PC. There is Cisco AnyConnect Secure Mobility Client on my PC to connect to my work access. Randomly my pc crashes, basically freezes. After manually power off and power on When I check event viewer the las...
When a client connect to the HQ via AnyConnect vpn, they can access the HQ local subnet, but can´t access the subnet at the remote office, that has an site-to-site connection to the HQ.Can this be configuret via the Cisco Firepower gui?Cisco Firepowe...
Hello , Cisco FPR version 7.2.5 is possible make group lock for local user that connect to local network over AnyConnect. I want to make Anyconnect access in our network where we have more group policy, we can not find that we can lock local user fo...
Hi All,We are experiencing some issues with different users, hope someone here can help solve it.First our setup, we have clients connecting with Client VPN using Cisco AnyConnect version 4.9.06037 and connecting to a Cisco ASA5585-SSP-20 running So...
Resolved! Tracking VPN Brute Force
Hello everyone,Can you provide me with the eventid of the VPN failed logon on Cisco's devices?I couldn't find any examples and i wan't to create a brute force rule for it in my SIEM solutions.
Following upgrading to upgrading to 5.1.2.42 to fix the vulnerability CVE-2024-20337Within Microsoft Defender this is still flagged as vulnerability for the CVEIt appears to refer to a component of the install:C:\Program Files (x86)\Cisco\Cisco Secur...
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:
| Subject | Author | Posted |
|---|---|---|
| 04-18-2024 03:23 PM | ||
| 04-18-2024 01:50 PM | ||
| 04-18-2024 11:35 AM | ||
| 04-18-2024 10:47 AM | ||
| 04-17-2024 06:49 AM |
| User | Count |
|---|---|
| 8 | |
| 4 | |
| 1 | |
| 1 | |
| 1 |





