- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Virtual Tunnel Interface (VTI) on FTD
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Tunnel VTY on FTD
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2018 07:10 AM - edited 03-12-2019 05:18 AM
We have a big project involving the deployment of hundred of firewall in different locations: HQ and shops. Each shop was connected to the regional HQ via VPN, either EasyVPN or static L2L (the latter case, when the shop has two Internet lines).
Currently, all location use ASA devices, which are going to be migrated/replaced with FTDs, centrally managed by FMC.
The implementation already started but we found several limitations in the current implementation of the VPN, compared to what was possible with the ASA:
- on the HQ hub, concetrating the VPNs from the shops, it's not possible to impose an order among the crypto-maps;
- it's not possible to configure a backup peer IP address in hub&spoke VPNs (unless you resort to contorted configurations);
- VTI tunnels - which would be absolutely welcome - are not supported: you can configure almost every aspect using FlexConfig, but not "nameif" and "ip address" command under the Tunnel if;
- it's not possible to associate a filter ACL to a VPN.
We would like to know if these four issues are included in the roadmap for the next upgrade; in particular, the VTI vpn is of particular interest for us: we see that there're a couple "enhancement request bugs" (CSCvf75938, CSCvj24040), acting as placeholders for the fact that VTI should be supported, but without any clue about when that will happen.
Thanks in advance.
- Labels:
-
Other VPN Topics
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-22-2018 02:23 AM
I also have no timeline. But I'm pretty sure that Cisco is very aware of the fact that many customers (including me) are eagerly waiting for these features (and many more) in FTD. I'm hoping to see some more in the next bigger releases.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-22-2018 04:24 AM
I would suggest you make sure your Cisco account manager is aware of your need for these enhancements. It will carry more weight via that path than via your posting here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-30-2019 07:04 PM
anybody knows if this vti feature is coming to ftd anytime soon?
i also have a large deployment with vti and dynamic routing that the feature is holding back migration to higher model firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2019 11:20 PM
It's not in the just-released Firepower 6.5 so don't hold your breath waiting for it. I doubt we will see it before 2020.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-26-2019 02:54 PM
Waiting for VTIs on FTD too.
In case this miracle happen, can you just put a note here too ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-27-2019 07:52 PM - edited 10-27-2019 07:52 PM
If you have a Cisco account manager you can request they submit an enhancement request on your behalf. Internally it's known as a "Firestarter" request. The more customers that request a given feature, the higher priority it gets within the development team.
Unfortunately they don't consider postings here as a customer request.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2020 07:40 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2020 08:54 AM - edited 02-18-2020 09:33 AM
You Cisco account manager should be familiar with it. If they aren't, they can contact their cybersecurity SE covering the account.
Meanwhile I have heard (at Cisco Live Barcelona) that VTIs are coming this fall with Firepower 6.7
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2020 10:52 AM - edited 02-19-2020 11:37 AM
@Marvin Rhoads we are deploying FTD and already using ASA VTI. i have escalated this to my cisco account manger as Firestarter" request. thank you for the tip/way to escalate this to cisco firewall team.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-22-2020 03:51 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2020 09:32 PM
waited so long i can live by waiting till fall.
i also escalated to account manager
Did anybody hear any feedback back?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2020 12:05 AM
My account manager at Cisco direct me to speak with a system engineer. This nice guy assured me it is escalated internally he the issue will be fixed in coming next release.
So I don’t no when it will be out. It is frustrating no FTD vti and no tunnels to AWS as we heavily based on site to site VPN’s
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2020 03:18 PM - edited 03-12-2020 03:20 PM
Funny you mention AWS as this was the same reason I was looking into VTI on FTD. That said, you can absolutely do a policy-based VPN to AWS. In fact AWS even has instructions on the VPN setup section on how to do this, the trick is you (obviously) cannot do BGP routing, so the config example only shows up if you configure the VPN on AWS with static routing. The only limitation with a policy based VPN to AWS is you can only have a single SA and I don't think you can have the SA do 0.0.0.0/0 so if you wanted to have a vpn from 192.168.0.1/24 and 10.1.0.0/24 there is no way to make it work. If all of your networks are inside of 10.0.0.0/16 then no problem, just use the /16 and you will be good.
Now, with all of that said, I think the main reason that FTD doesn't have VTI yet is that quite frankly you shouldn't be doing these types of VPNs on FTD. The modern day replacement for a "VPN Concentrator" is the ISR 4K or ASR routers. IOS XE has EXCELLENT ipsec support, and that is my device of choice for this type of application. I'm even considering the CSR 1000v for this too. I just wish the pricing for CSR was a bit better, especially for the higher throughput versions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2020 03:19 AM
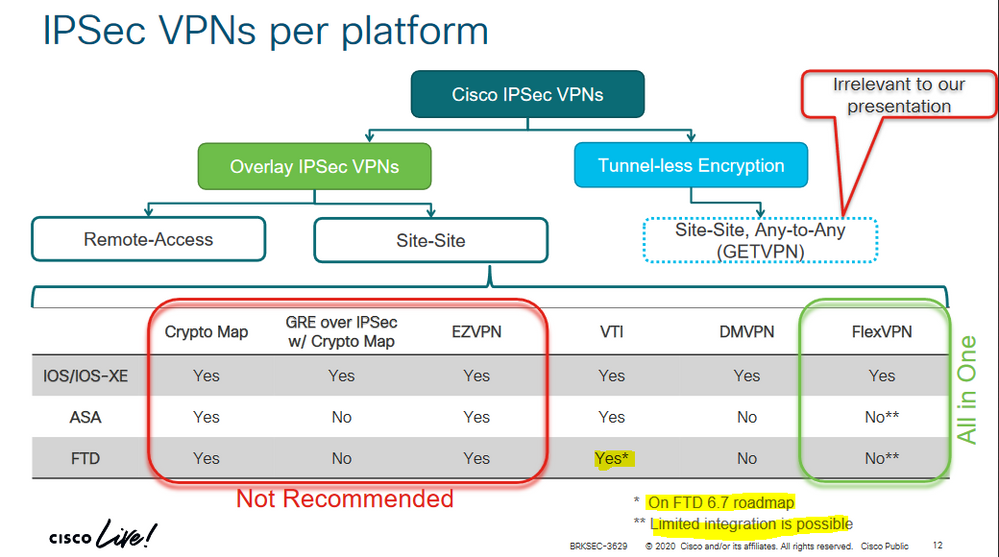
VTI for FTD coming in version 6.7. here is the link cisco live 2020 spain. link here
BRKSEC-3629
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: