- Cisco Community
- Technology and Support
- Security
- VPN
- VPNs Only Work For Certain Subnets
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
VPNs Only Work For Certain Subnets
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-04-2016 03:29 PM
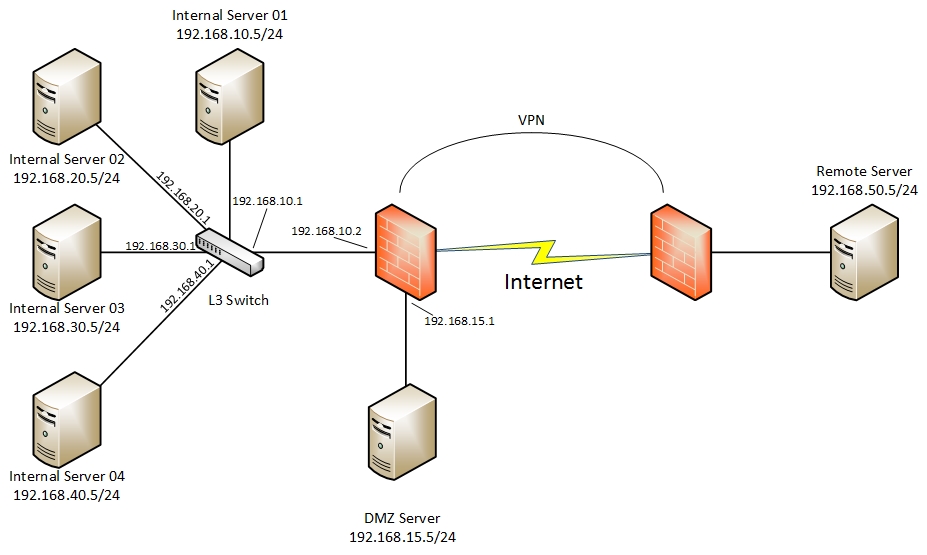
I have a couple of VPNs but am having issues with certain subnets accessing the remote sites. I've created the below diagram to help explain. If a server that is on a subnet to which the ASA firewall, (ASA 5510), has an interface that it is part of, those servers can ping the remote server. However, if a server is on any other subnet it cannot ping the remote site. In the below example Server 01 is part of the 192.168.10.0/24 subnet, and because the ASA firewall has an interface on this same subnet that server can ping the remote site. The same goes for the DMZ server which is connected directly to the firewall on the 192.168.15.0/24 subnet.
All other subnets, such as 192.168.20.0/24, .30.0/24, & .40.0/24 cannot reach the remote site on the other end of the VPN tunnels.
How can I get subnets such as .20, .30, and .40 to be able to reach the remote sites across the VPN?
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-04-2016 08:31 PM
aalbrecht27,
Thanks for your post, I've reviewed your environment as best I can without configuration files being provided. Just to make referencing things easier, lets call the left firewall "FW-A" and the right firewall "FW-B".
Now, from my understanding, you can access the subnet(s) directly connected to FW-A (192.168.10.0 for example) from the other end of the tunnel but not subnets that have their layer 3 residing on the switch? If this is the case, it is more than likely going to be a routing issue.
Please make sure that FW-A and FW-B both have routes to the subnets hanging off of the layer 3 switch. Also, your access control lists and interesting traffic access control lists for the tunnel will need to match this in order for it to work. If you have any issues knowing the correct commands to use, please attach the full sanitised configuration from each firewall and I'll write some commands tailored to your environment. In this case, please don't forget to let me know the version of ASA you are running.Let me know how you get along, I look forward to hearing back.
Kind regards,
Luke
Please rate helpful posts and mark correct answers.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide