Hello Experts,
Do we have the means to determine the radio slot the AP uses to send the deauth frames while containing the rogue APs / rogue clients?
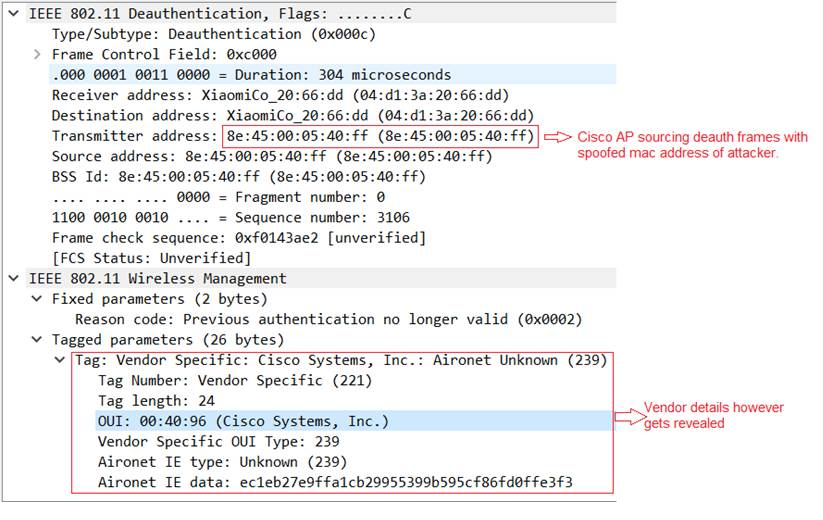
Since for containment, the AP will be using the spoofed mac address of the attacker, the wireless PCAPs for obvious reasons will not help in determining the same. The OUI exposed in PCAPs will however help identity that the deauth frames (broadcast/unicast) is launched by an Cisco AP (using spoofed mac address of attacker)
There could however be the debugs/ show cli’s from AP which may help us determine radio used in containment. Could someone please share the way to evaluate the radio used in containment?