- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- EAP-FAST Security level
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 04:22 PM - edited 07-03-2021 11:45 PM
Hi all,
I use EAP-FAST in my network and I have some questions about it.
1) is there any vulnerability detected with EAP-FAST?
2) Can I restrict the establishment two or more simultaneous sessions using the same account and same PAC? how
3) Can I use EAP-FAST with MAC address filtering through ACS?
4) What is the level of security provided by EAP-FAST? is there technology more security than EAP-FAST?
Thanks for your reply.
Thanks.
Solved! Go to Solution.
- Labels:
-
Wireless Security
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:03 AM
check this one, may be i am still pretending:
rate me please on this if you liked it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 04:44 PM
1) Vulnerabilty if anonymous PAC provisioning is enabled machines connecting with valid user credentials will be automatically assigned a PAC and can gain access if you need to use automatic PAC provsioning to get a machine on to the network switch it on to get the machine on but switch it back off again when you are done.
2) i have never tried this so I can't help you on that question sorry.
3) If you are using ACS 5 then I am sure you could but mac filtering is not really all that secure anyway as macs can still be easily spoofed..
4) One of the most secure methods that you can use is EAP-TLS this is a two way certficate exchange where the ACS verfied the client certificate and the client verfies that the ACS is genuine by verifiying the server certifcate, You need a CA server in place to do this and you need to have the CA added as a trusted root on the ACS. If a client machine is lost or stolen you can revoke the certificate and stop someone from gaining access. A little less secure is EAP-PEAP the client can use their AD credentials to gain access the credentials are passed within a tunnel to protect them. The client can also bet set to validate the server certifcate in this method. To prevent users logging on with machines by using their AD credentials you can also set up a policy to check the machine exists in AD before authorising the user onto to the network.
Good Post about setting this up here
https://supportforums.cisco.com/docs/DOC-21825
If you want to be really granualar about securtiy you could start looking at ISE
Regards
Martin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 10:51 PM
Hi Mostafa:
- I am not really deep in what vulnerabilities availalbe. Just try to avoid anonymous provisioning like Martin mentioned. I've read somewhere before that EAP-FAST phase 0 (anonymous provisioning) is somehow vulnerable (or let us say phase 0 is easier to be compromised).
- From the radius server you can restrict the number of user sessoins. In ACS 5.x for example that is configured under:
Access Policies -> Max User Session Policy.
You can configure the max session per user or per group.
- There was an early discussion here in cisco support forums if user and mac auth both can be used at the same time with ACS 5.x and we found it is possible but it needs some overhead in configuration. If you ask about EAP-FAST with only mac filtering (i.e. the mac address is considered the username that is going to be sent to the radius) then the mac address of the client must be added to the radius as both a username and a password.
- EAP-FAST provides good level of security. However, EAP-TLS provides more security but it is however requires more overhead for CA implementation and provisioning the certificates to every single client device.
Here is a configuration doc: https://supportforums.cisco.com/docs/DOC-15587
Don't forget that EAP-FAST needs usually third-party supplicants to work. e.x. Windows by default does not support EAP-FAST. You need a third party utility for EAP-FAST to work or the utility that comes with your wireless adapter (if available).
Hope this is useful to you.
Regards,
Amjad
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 01:35 AM
Hi Amjad,
3) no I ask about user and mac auth with EAP-FAST,is it possible?if yes can you give me the configuration.
Regards.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 01:50 AM
this is sample config on ACS for leap with mac auth:
The following link how to configure mac authentication alone:
Athenciation types config in gerenal examples:
EAP FAST config:
Based on the above you can easily do it all together.
--------------------------------------------------------------------------------------------------
Please make sure to rate correct answers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 01:50 AM
well, you can check this discussion:
https://supportforums.cisco.com/message/3886301#3886301
Maldehne pretended it will work the way he posted (he posted a screenshot about configuration).
Now, from my understanding to how ACS works and the radius attribute he used I would say it will work in OR scenario (user OR mac auth) but not both at the same time.
As maldehne is an expert TAC engineer I would suggest that you give his config a try if it works or not.
If it did not work I posted a suggeted config that will usually work at the same discussion but below maldehne post.
Let us know which worked with you.
Regards,
Amjad
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:00 AM
Nice words my friend. keep going.
Check my answer on the thread u have referred to since you have doubts about it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 08:30 AM
Hi Amjad,
1) with EAP-FAST we provide user + PAC to authenticate there isn't any other way to add ours mac address or it add automatically?
2) Can I configure ACS to check first username then check mac address. but if one of two failed "the authentication fail".
3) Can I do a local MAC filtring in the WLC if authentication user+mac is not possible.
Thanks with rate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-18-2013 11:09 PM
1)
Everything should be fine with EAP-FAST but you should take into consideration some issues when your clients are being provisioned their PACs through inband PAC provisioning.
What will happen? see
The in-band provisioning mode operates inside a TLS tunnel raised by Anonymous DH or Authenticated DH or RSA algorithm for key agreement.
To minimize the risk of exposing the user's credentials, a clear text password should not be used outside of the protected tunnel. Therefore, EAP-MSCHAPv2 or EAP-GTC are used to authenticate the user's credentials within the protected tunnel. The information contained in the PAC is also available for further authentication sessions after the inner EAP method has completed.
Automatic In-Band PAC Provisioning, which is the same as EAP-FAST phase zero, sends a new PAC to an end-user client over a secured network connection. Automatic In-Band PAC Provisioning requires no intervention of the network user or an ACS administrator, provided that you configure ACS and the end-user client to support Automatic In-Band PAC Provisioning.
In general, phase zero of EAP-FAST does not authorize network access. In this general case, after the client has successfully performed phase zero PAC provisioning, the client must send a new EAP-FAST request in order to begin a new round of phase one tunnel establishment, followed by phase two authentication.
However, if you choose the Accept Client on Authenticated Provisioning option, ACS sends a RADIUS Access-Accept (that contains an EAP Success) at the end of a successful phase zero PAC provisioning, and the client is not forced to reauthenticate again. This option can be enabled only when the Allow Authenticated In-Band PAC Provisioning option is also enabled.
Because transmission of PACs in phase zero is secured by MSCHAPv2 authentication, when MSCHAPv2 is vulnerable to dictionary attacks, we recommend that you limit use of Automatic In-Band PAC Provisioning to initial deployment of EAP-FAST.
After a large EAP-FAST deployment, PAC provisioning should be done manually to ensure the highest security for PACs.
EAP-FAST has been enhanced to support an authenticated tunnel (by using the server certificate) inside which PAC provisioning occurs. The new cipher suites that are enhancements to EAP-FAST, and specifically the server certificate, are used.
2) Max user sessions
3)Yes
4)PEAP ( EAP TLS )
Side note:
EAP FAST is now supported on Micrsofot supplicants , so yeah it should work with third party supplicants
----------------------------------------------------------------------------------------------------------
Please make sure to rate correct answers and rate the thread as answered
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 01:57 AM
Side note:
EAP FAST is now supported on Micrsofot supplicants , so yeah it should work with third party supplicants
Mohammad: what do you mean by EAP-FAST supported on microsoft supplicant?
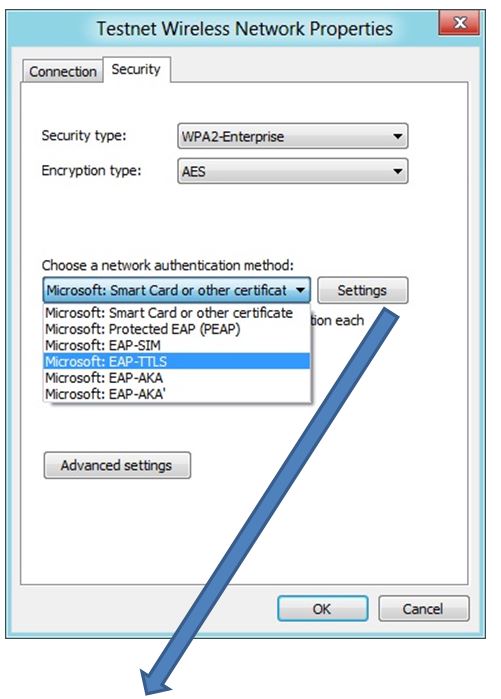
It is not supported by default on windows xp or windows 7. not even newer windows 8 (see below screenshot).
If you have a supported driver (intel PROset for example) your config will probably appear in the list of EAP methods in the supplicant. But that is an addition done by the driver, not by microsoft with its supplicant.
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:01 AM
It is supported , there is a piece of software to download it from microsoft and it should work 7abibi.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:05 AM
There is a piece of software but it is not from microsoft.
If you have intel driver you can add eap-fast to your windows supplicant like in this link:
http://www.intel.com/support/wireless/wlan/sb/CS-032728.htm
but it works only with intel adapters.
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:03 AM
check this one, may be i am still pretending:
rate me please on this if you liked it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 02:36 AM
Your link is workign amazingly wiht my Broadcom adapter!!
Now I can say Bye Bye to the anyconnect NAM.
I can only give 5 starts. But I strongly encourage others to give you 5s as well. ;-)
Thanks my teacher,
Amjad
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-19-2013 05:16 AM
hi all
Is there outils to check/simulate attack or intrusion with EAP-FAST?
to ensure that all is ok.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


