- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: Very High level explanation of this WLC/ISE security setup?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Very High level explanation of this WLC/ISE security setup?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2020 06:54 AM - edited 07-05-2021 12:39 PM
I'm not sure how to even ask the right question here but if anyone has some pointers on how I can understand the configuration below or any simple concepts or explanations I would really appreciate it, many thanks.
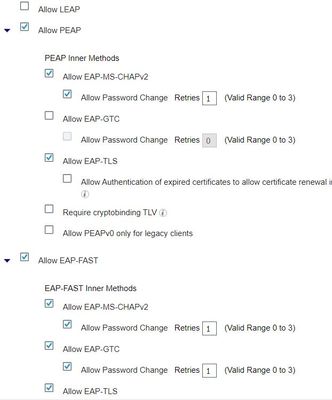
As a novice, the settings below just say to me our system uses WPA2 security, 802.1x, PEAP MSCHAPV2 security, EAP-FAST, but how do all the various methods fit together? I doubt there is an simple explanation but anything would help.
WLC:
ISE:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2020 08:13 AM
One the radius server, you are basically saying what types of 802.1x variations you want to accept. One the ISE rules, you can specify exact EAP method to allow.
On the client device is really how you define what type of 802.1x method to use.
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2020 08:17 AM
Many thanks for getting back to me. What is WPA2 there for if 802.1x is being used? This is probably a really stupid question but I am brand new to all this so apologies.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2020 06:05 AM
https://en.wikipedia.org/wiki/Wi-Fi_Protected_Access#WPA_terminology
WPA2 with pre-shared key known as WPA-Personal and WPA2 with 802.1x known as WPA-Enterprise.
The encryption layer is WPA2. The encryption keys are derived from PSK or 802.1x protocol.
Please click Helpful if this post helped you and Select as Solution (drop down menu at top right of this reply) if this answered your query.
------------------------------
TAC recommended codes for AireOS WLC's and TAC recommended codes for 9800 WLC's
Best Practices for AireOS WLC's, Best Practices for 9800 WLC's and Cisco Wireless compatibility matrix
Check your 9800 WLC config with Wireless Config Analyzer using "show tech wireless" output or "config paging disable" then "show run-config" output on AireOS and use Wireless Debug Analyzer to analyze your WLC client debugs
Field Notice: FN63942 APs and WLCs Fail to Create CAPWAP Connections Due to Certificate Expiration
Field Notice: FN72424 Later Versions of WiFi 6 APs Fail to Join WLC - Software Upgrade Required
Field Notice: FN72524 IOS APs stuck in downloading state after 4 Dec 2022 due to Certificate Expired
- Fixed in 8.10.190.0, latest 9800 releases, 8.5.182.11 (8.5 mainline) and 8.5.182.108 (8.5 IRCM)
Field Notice: FN70479 AP Fails to Join or Joins with 1 Radio due to Country Mismatch, RMA needed
How to avoid boot loop due to corrupted image on Wave 2 and Catalyst 11ax Access Points (CSCvx32806)
Field Notice: FN74035 - Wave2 APs DFS May Not Detect Radar After Channel Availability Check Time
Leo's list of bugs affecting 2800/3800/4800/1560 APs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2020 06:41 AM
Thanks for that. I have a lot of reading up to do!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2020 08:31 AM
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2020 09:11 AM
WPA2 is a standard that can be used for PSK or dot1x, this is why we select it on the WLC. If your environment uses EAP-TLS as an example, on ISE side you don't need to enable any allowed protocols but EAP-TLS. However, if you use EAP-PEAP, then you only need EAP-PEAP to be enabled, and depending on what inner protocol you will be using with EAP-PEAP, whether MSCHAPv2 or EAP-TLS, you enable that accordingly. In other words, it all depends on your deployment, if you want to be very specific, which is good practice, then you just enable what you need along the whole authentication patch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2020 05:59 AM - edited 10-23-2020 06:00 AM
As Aref mentioned, keep in mind that inner protocol because that defines how your deployment would be since that EAP-TLS is certificate based and MSCHAPV2 uses Active Directory Credentials. The EAP-TLS Certificate can be signed by a public certificate authority or using your own PKI Infrastructure.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide