- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: WLC5520 public wifi can't reach DHCP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2021 08:45 AM - edited 07-05-2021 01:20 PM
Hello,
We have a WLC5520 which works fine for our private WiFi, but the public WiFi cannot reach the DHCP server.
The interface is set to "vlan900", which has an IP address of 172.16.48.2 /22.
On the router, 172.16.48.1 works and can be reach with this address. However, I cannot ping 172.16.48.2 from anywhere.
The interface is up, I see the SSID from WiFi clients but when I try to connect, it says "cannot obtain IP address".
The private WiFi can reach the DHCP server just fine.
show interface summary Number of Interfaces.......................... 6 Interface Name Port Vlan Id IP Address Type Ap Mgr Guest -------------------------------- ---- -------- --------------- ------- ------ ----- management 1 12 192.168.12.5 Static Yes No redundancy-management 1 12 0.0.0.0 Static No No redundancy-port - untagged 0.0.0.0 Static No No service-port N/A N/A 10.110.2.5 Static No No virtual N/A N/A 1.1.1.2 Static No No vlan900 1 900 172.16.48.2 Dynamic No No
EDIT: Additional info....
From the WLC I cannot ping the gateway on 172.16.48.1 but I can ping it on 192.168.12.1. This is probably why the public WiFi can't reach the DHCP server (which is on the 192.168.10.x network). But the private WiFi can. I'm looking at the trunk from the WLC to the gateway and it looks ok ? What am I missing?
Solved! Go to Solution.
- Labels:
-
Catalyst Wireless Controllers
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 12:45 PM
Ok so after removing the ACL 2008, I can now ping 172.16.48.2 from anywhere and the WLC can ping the gateway on 172.16.48.1. It can even ping the DHCP server 192.168.10.9!
But Public WiFi clients still cannot get an IP address.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2021 05:46 AM - edited 03-10-2021 05:53 AM
Please note that after putting "DHCP Proxy Mode" to "DISABLED", now clients can reach the DHCP.
However, they are able to access our entire network, which is of course NOT something we want.
I have found this ACL :
#sh access-lists 2600
Extended IP access list 2600
10 permit icmp 172.16.48.0 0.0.3.255 any echo-reply
20 permit tcp 172.16.48.0 0.0.3.255 any established
30 deny ip 172.16.48.0 0.0.3.255 192.168.10.0 0.0.0.255 (1760 matches)
40 deny ip 172.16.48.0 0.0.3.255 192.168.11.0 0.0.0.255
50 deny ip 172.16.48.0 0.0.3.255 192.168.12.0 0.0.0.255
60 deny ip 172.16.48.0 0.0.3.255 192.168.20.0 0.0.0.255
70 deny ip 172.16.48.0 0.0.3.255 192.168.25.0 0.0.0.255
80 deny ip 172.16.48.0 0.0.3.255 192.168.30.0 0.0.0.255
90 deny ip 172.16.48.0 0.0.3.255 192.168.222.0 0.0.0.255
100 deny ip 172.16.48.0 0.0.3.255 192.168.240.0 0.0.0.255
110 deny ip 172.16.48.0 0.0.3.255 192.168.255.0 0.0.0.255
120 deny ip 172.16.48.0 0.0.3.255 10.4.8.0 0.0.0.3
130 deny ip 172.16.48.0 0.0.3.255 192.168.1.0 0.0.0.7
140 permit ip 172.16.48.0 0.0.3.255 any (44 matches)I'm not sure how to include this to the Public WiFi ? Will this ACL not block connection between the clients (172.16.48.x /22) to the DHCP (192.168.10.9) ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2021 12:28 PM
Makesure bootp & DNS traffic is permitted in your ACL , something like below
remark Permit DHCP IP assignment
permit udp any any eq bootps
permit udp any eq bootpc any
remark Permit DNS
permit udp any any eq domain
HTH
Rasika
*** Pls rate all useful responses ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2021 12:09 PM
Did you make sure vlan 900 is allowed in the trunk link between WLC & Switch. You should be able to ping vlan 900 IP from your network.
HTH
Rasika
*** Pls rate all useful responses ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2021 12:33 PM
The WLC is linked to the gateway, on port 6:
#sh int trunk Port Vlans allowed on trunk Gi1/0/1 1-4094 Gi1/0/2 1-4094 Gi1/0/3 1-4094 Gi1/0/4 1-4094 Gi1/0/5 1-4094 Gi1/0/6 10,12,900 Gi1/0/8 1-4094
Is there anywhere else I should check?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2021 01:10 PM
Pls "show interface detailed vlan900" from WLC and "show run int vlan 900" & "show arp vlan 900" from the SW to verify your configs, there may be some misconfiguration
HTH
Rasika
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 05:05 AM
show run int vlan900 Building configuration... Current configuration : 120 bytes ! interface Vlan900 ip address 172.16.48.1 255.255.252.0 ip access-group 2008 in ip helper-address 192.168.10.9 end
#show arp vlan 900 Protocol Address Age (min) Hardware Addr Type Interface Internet 172.16.48.1 - 00eb.d588.ce45 ARPA Vlan900 Internet 172.16.48.2 67 d478.9bc1.a65c ARPA Vlan900
(Cisco Controller) >show interface detailed vlan900 Interface Name................................... vlan900 MAC Address...................................... d4:78:9b:c1:a6:5c IP Address....................................... 172.16.48.2 IP Netmask....................................... 255.255.252.0 IP Gateway....................................... 172.16.48.1 External NAT IP State............................ Disabled External NAT IP Address.......................... 0.0.0.0 Link Local IPv6 Address.......................... fe80::d678:9bff:fec1:a65b/64 STATE ........................................... NONE IPv6 Address..................................... ::/128 STATE ........................................... NONE IPv6 Gateway..................................... :: IPv6 Gateway Mac Address......................... 00:00:00:00:00:00 STATE ........................................... NONE VLAN............................................. 900 Quarantine-vlan.................................. 0 NAS-Identifier................................... none Active Physical Port............................. 1 Primary Physical Port............................ 1 Backup Physical Port............................. Unconfigured DHCP Proxy Mode.................................. Global Primary DHCP Server.............................. 192.168.10.9 Secondary DHCP Server............................ Unconfigured DHCP Option 82................................... Disabled DHCP Option 82 bridge mode insertion............. Disabled IPv4 ACL......................................... Unconfigured URL ACL.......................................... Unconfigured URL ACL.......................................... Unconfigured mDNS Profile Name................................ Unconfigured AP Manager....................................... No Guest Interface.................................. No 3G VLAN.......................................... Disabled L2 Multicast..................................... Enabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 11:21 AM
What is that Access-list 2008, that may blocking that interface from reaching DHCP. Pls share that ACL entry to check, for testing, you can remove that line and verify. Again you may have to apply it again with modifications if that ACL block communication with DHCP server
HTH
Rasika
*** Pls rate all useful responses ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 11:26 AM
This was run on the gateway:
#sh access-lists 2008
Extended IP access list 2008
10 deny icmp any any (501 matches)
20 permit ip any any (9104 matches)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 12:17 PM
That is the reason why you cannot ping as that ACL block all ICMP traffic. Is that the issue you having ?
HTH
Rasika
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 12:19 PM - edited 03-09-2021 12:20 PM
That is one of the issues. The main issue is that the WLC cannot reach the DHCP server on interface vlan900 but can reach it on main interface. I don't believe access-list 2008 prevents anything else than ping, right?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 12:27 PM
Yes, ACL block ICMP traffic on vlan 900, that will make really hard to verify. I would suggest until you figure it out, remove that ACL and that can allow you to verify WLC can reach DHCP server on vlan 900 as the source.
HTH
Rasika
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 12:45 PM
Ok so after removing the ACL 2008, I can now ping 172.16.48.2 from anywhere and the WLC can ping the gateway on 172.16.48.1. It can even ping the DHCP server 192.168.10.9!
But Public WiFi clients still cannot get an IP address.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-09-2021 02:41 PM
That's a good sign
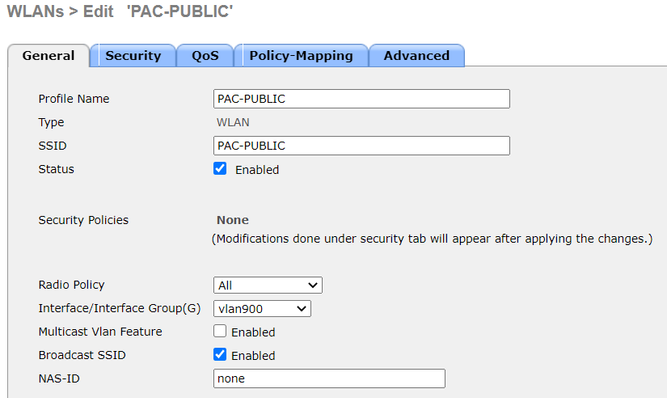
Did you check DHCP scope with the correct subnet defined on DHCP server for vlan 900? Also check that Public WiFi is mapped to vlan900 interface on WLC
HTH
Rasika
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2021 05:05 AM
Both look ok?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2021 05:46 AM - edited 03-10-2021 05:53 AM
Please note that after putting "DHCP Proxy Mode" to "DISABLED", now clients can reach the DHCP.
However, they are able to access our entire network, which is of course NOT something we want.
I have found this ACL :
#sh access-lists 2600
Extended IP access list 2600
10 permit icmp 172.16.48.0 0.0.3.255 any echo-reply
20 permit tcp 172.16.48.0 0.0.3.255 any established
30 deny ip 172.16.48.0 0.0.3.255 192.168.10.0 0.0.0.255 (1760 matches)
40 deny ip 172.16.48.0 0.0.3.255 192.168.11.0 0.0.0.255
50 deny ip 172.16.48.0 0.0.3.255 192.168.12.0 0.0.0.255
60 deny ip 172.16.48.0 0.0.3.255 192.168.20.0 0.0.0.255
70 deny ip 172.16.48.0 0.0.3.255 192.168.25.0 0.0.0.255
80 deny ip 172.16.48.0 0.0.3.255 192.168.30.0 0.0.0.255
90 deny ip 172.16.48.0 0.0.3.255 192.168.222.0 0.0.0.255
100 deny ip 172.16.48.0 0.0.3.255 192.168.240.0 0.0.0.255
110 deny ip 172.16.48.0 0.0.3.255 192.168.255.0 0.0.0.255
120 deny ip 172.16.48.0 0.0.3.255 10.4.8.0 0.0.0.3
130 deny ip 172.16.48.0 0.0.3.255 192.168.1.0 0.0.0.7
140 permit ip 172.16.48.0 0.0.3.255 any (44 matches)I'm not sure how to include this to the Public WiFi ? Will this ACL not block connection between the clients (172.16.48.x /22) to the DHCP (192.168.10.9) ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-10-2021 11:38 AM
You just simply need to apply that ACL onto vlan900 on the switch, that control to be done at switch SVI level and not at WLC end.
HTH
Rasika
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide