32607
查看次数
5
有帮助
27
回复
AP反复加入控制器,然后反复断开.求助。
本帖最后由 AlexChan21895 于 2020-4-8 14:33 编辑
console口输出显示在下方,vWLC虚拟控制器版本为: 8.5.161,AP为AIR-OEAP1810-CRD,在控制器内识别为AIR-OEAP1810-B-K9,恢复出厂后,它会自动升级适合控制器的固件版本,自动加入等等一切正常,但是加入后很快它又会闪红黄绿三色灯,表示又在重新连接控制器,而这时候它在控制器的状态是加入中,而等上一会,它就会成功地加入到控制器,并且在控制器的已加入AP列表中出现,那时候会闪绿灯,但很快又会回到闪红黄绿三色灯的状态去。这样反反复复。
其他连在这控制器的几个3602正常工作没有问题。尝试过capwap ap erase all 命令恢复出厂,它也能自动加入到控制器,但加入控制器后就开始断开,然后反复加入。看console口输出显示看不到有什么问题。
以下是console口输出显示,后面那些相同的部分就是一直在反复加入和断开。附图为控制器上的出错信息。
Welcome to Cisco.
Usage of this device is governed by Cisco's End User License Agreement,
available at:
http://www.cisco.com/c/en/us/td/docs/general/warranty/English/EU1KEN_.html.
Restricted Rights Legend
Use, duplication, or disclosure by the Government is subject to
restrictions as set forth in subparagraph (c) of the Commercial
Computer Software - Restricted Rights clause at FAR sec. 52.227-19 and
subparagraph (c) (1) (ii) of the Rights in Technical Data and Computer
Software clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
This product contains cryptographic features and is subject to United
States and local country laws governing import, export, transfer and
use. Delivery of Cisco cryptographic products does not imply
third-party authority to import, export, distribute or use encryption.
Importers, exporters, distributors and users are responsible for
compliance with U.S. and local country laws. By using this product you
agree to comply with applicable laws and regulations. If you are unable
to comply with U.S. and local laws, return this product immediately.
A summary of U.S. laws governing Cisco cryptographic products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by sending email to
export@cisco.com.
This product contains some software licensed under the
"GNU General Public License, version 2" provided with
ABSOLUTELY NO WARRANTY under the terms of
"GNU General Public License, version 2", available here:
http://www.gnu.org/licenses/old-licenses/gpl-2.0.html
This product contains some software licensed under the
"GNU Library General Public License, version 2" provided
with ABSOLUTELY NO WARRANTY under the terms of "GNU Library
General Public License, version 2", available here:
http://www.gnu.org/licenses/old-licenses/lgpl-2.0.html
This product contains some software licensed under the
"GNU Lesser General Public License, version 2.1" provided
with ABSOLUTELY NO WARRANTY under the terms of "GNU Lesser
General Public License, version 2.1", available here:
http://www.gnu.org/licenses/old-licenses/lgpl-2.1.html
This product contains some software licensed under the
"GNU General Public License, version 3" provided with
ABSOLUTELY NO WARRANTY under the terms of
"GNU General Public License, Version 3", available here:
http://www.gnu.org/licenses/gpl.html.
This product contains some software licensed under the
"GNU Affero General Public License, version 3" provided
with ABSOLUTELY NO WARRANTY under the terms of
"GNU Affero General Public License, version 3", available here:
http://www.gnu.org/licenses/agpl-3.0.html.
init started: BusyBox v1.23.2 (2020-02-17 12:14:41 PST)
[*01/01/1970 00:00:28.2913] GCM-128 POST passed
[*01/01/1970 00:00:28.2913] GCM-256 POST passed
[*01/01/1970 00:00:28.4113] === 5G radio domain is 41, COPY 5G BDF files from non_ETSI_BDF folder ===
[*01/01/1970 00:00:28.4612] 0
[*01/01/1970 00:00:28.6712] Active version: 8.5.161.0
[*01/01/1970 00:00:28.6712] Backup version: 8.5.151.0
Jan 1 00:00:28 FIPS[1659]: *** shell: FIPS Mode = disabled ***
[*01/01/1970 00:00:28.8611]
[*01/01/1970 00:00:28.8611] led pattern module start
User Access Verification
Username: [*01/01/1970 00:00:28.9211] AP1810
[*01/01/1970 00:00:29.0111] nss_driver - Turbo Support 1
[*01/01/1970 00:00:29.0111] Supported Frequencies - 110Mhz 550Mhz 733Mhz
[*01/01/1970 00:00:29.0411] NSS firmware booted
[*01/01/1970 00:00:29.0611] NSS firmware booted
[*01/01/1970 00:00:35.1891] ssdk_plat_init start
[*01/01/1970 00:00:35.1891] Register QCA PHY driver
[*01/01/1970 00:00:35.1991] PHY ID is 0x4dd036
[*01/01/1970 00:00:35.3691] qca probe f1 phy driver succeeded!
[*01/01/1970 00:00:35.3691] qca-ssdk module init succeeded!
[*01/01/1970 00:00:35.3791] Chip version 0x1302
[*01/01/1970 00:00:35.9789]
[*01/01/1970 00:00:35.9789] Swtich config done.
[*01/01/1970 00:00:37.9183] Current value of FACTORY_RESET=0
[*11/08/2016 23:59:59.0099] Last reload time: Apr 8 03:50:37 2020
[*04/08/2020 03:50:37.0000] Setting system time Wed Apr 8 03:50:37 UTC 2020
[*04/08/2020 03:50:37.0599] device wired0 entered promiscuous mode
[*04/08/2020 03:50:37.0899] device eth1 entered promiscuous mode
[*04/08/2020 03:50:38.6595] stile module dp init successfully
[*04/08/2020 03:50:38.6595] NBAR Label:BLD_V155_3_S_XE316_THROTTLE_LATEST_20180404_162221 NBAR VERSION:module build date: Feb 17 2020 at 12:28:56
[*04/08/2020 03:50:39.2993] miibus get dd50fc00!
[*04/08/2020 03:50:39.3293]
[*04/08/2020 03:50:39.3393] boot 26 build T-eaf8c9a5819ff90fa88df9b4045e20adf0d0a259-geaf8c9a5-vipendya board corsica mac 00:B0:E1:88:0C:C0
[*04/08/2020 03:50:39.3393] Module: mbedtls .text=0xbf000000 data=0xbf007e18 bss=0xbf008070
[*04/08/2020 03:50:39.3393] Module: aptrace .text=0xbf00c000 data=0xbf018834 bss=0xbf018cc0
[*04/08/2020 03:50:39.3393] Module: led_module .text=0xbf020000 data=0xbf0204e0 bss=0xbf020b48
[*04/08/2020 03:50:39.3393] Module: qca_nss_gmac .text=0xbf024000 data=0xbf02abd4 bss=0xbf02b098
[*04/08/2020 03:50:39.3393] Module: qca_nss_drv .text=0xbf034000 data=0xbf04f9e8 bss=0xbf050798
[*04/08/2020 03:50:39.3393] Module: qca_nss_capwapmgr .text=0xbf071000 data=0xbf075ad4 bss=0xbf075c28
[*04/08/2020 03:50:39.3393] Module: nssmgrctl .text=0xbf07c000 data=0xbf07d728 bss=0xbf07da4c
[*04/08/2020 03:50:39.3393] Module: qca_nss_portifmgr .text=0xbf083000 data= bss=0xbf083dcc
[*04/08/2020 03:50:39.3393] Module: qca_ssdk .text=0xbf088000 data=0xbf11e544 bss=0xbf123ecc
[*04/08/2020 03:50:39.3393] Module: proclikefs .text=0xbf172000 data= bss=0xbf172b40
[*04/08/2020 03:50:39.3393] Module: stile_lm_ft .text= data= bss=
[*04/08/2020 03:50:39.3393] Module: stile_lm_dp .text= data= bss=
[*04/08/2020 03:50:39.3393] Module: ipv6 .text=0xbfb01000 data=0xbfb31fc0 bss=0xbfb3386c
[*04/08/2020 03:50:39.3393] Module: bonding .text=0xbfb4d000 data=0xbfb5e640 bss=0xbfb5ea6c
[*04/08/2020 03:50:39.3393] Module: lowmemorykiller .text=0xbfb6b000 data=0xbfb6b2c0 bss=0xbfb6b44c
[*04/08/2020 03:50:39.3393] Module: qca_nss_profile:41.3886] ol_transfer_bin_file: flash data file defined
[*04/08/2020 03:50:41.3886] Cal location [0]: 00000000
[*04/08/2020 03:50:41.3886]
[*04/08/2020 03:50:41.3886] Wifi0 NAND FLASH Select OFFSET 0x1000
[*04/08/2020 03:50:41.4086] qc98xx_verify_checksum: flash checksum passed: 0xd618
[*04/08/2020 03:50:41.4086] ol_transfer_bin_file 3979: Download Flash data len 12064
[*04/08/2020 03:50:41.4286]
[*04/08/2020 03:50:41.4286] Board data initialized
[*04/08/2020 03:50:41.4786] ol_ath_download_firmware :First OTP download and Execute is good address:0xd800 return param 4660
[*04/08/2020 03:50:41.4786] ol_ath_download_firmware:##Board Id 22 , CHIP Id 1
[*04/08/2020 03:50:41.4786] ol_transfer_bin_file: Board Data File download to address=0xc0000 file name=AR900B/hw.2/boardData_AR900B_CUS260_negative_pwr_offset_2G_2X2_022.bin
[*04/08/2020 03:50:41.5586]
[*04/08/2020 03:50:41.5586] [Flash] : Ignore Module param
[*04/08/2020 03:50:41.5586] ol_ath_download_firmware : Second OTP download and Execute is good, param=0x0
[*04/08/2020 03:50:41.5786] ol_transfer_bin_file: Downloading firmware file: AR900B/hw.2/athwlan.bin
[*04/08/2020 03:50:42.7482] HTC Rx: insufficient length, got:4 expected =8
[*04/08/2020 03:50:42.7482] Startup Mode-0 set
[*04/08/2020 03:50:42.7482] HTC Service:0x0300 ep:1 TX flow control disabled
[*04/08/2020 03:50:42.7482] HTC Service:0x0100 ep:2 TX flow control disabled
[*04/08/2020 03:50:42.7482] Firmware_Build_Number:70
[*04/08/2020 03:50:42.7482] num_rf_chain:0x00000002 ht_cap_info:0x0000185b vht_cap_info:0x339979b2 vht_supp_mcs:0x0000fffa
[*04/08/2020 03:50:42.7482]
[*04/08/2020 03:50:42.7482] RES CFG Support wmi_service_bitmap 9778
[*04/08/2020 03:50:42.7482]
[*04/08/2020 03:50:42.7482] Sending Ext resource cfg: HOST PLATFORM as 0 and fw_feature_bitmap as 50 to TGT
[*04/08/2020 03:50:42.7482] ol_ath_service_ready_event: sw_cal_support_check_flag: 1
[*04/08/2020 03:50:42.8282] wmi_ready_event_rx: WMI UNIFIED READY event
[*04/08/2020 03:50:42.8282] htt_h2t_frag_desc_bank_cfg_msg - HTT_H2T_MSG_TYPE_FRAG_DESC_BANK_CFG sent to FW for radio ID = 0
[*04/08/2020 03:50:42.8282] ACS not enabled
[*04/08/2020 03:50:42.8282] ol_ath_thermal_mitigation_attach: --
[*04/08/2020 03:50:42.8282]
[*04/08/2020 03:50:42.8282] __ol_ath_attach() Allocated scn d7a40480
[*04/08/2020 03:50:42.8382] ol_ath_attach interface_id 1
[*04/08/2020 03:50:42.8482] Chip id: 0x9, chip version: 0x1000000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] Target Version is 1000000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] Flash Download Address c0000
[*04/08/2020 03:50:42.8482] ol_transfer_bin_file: flash data file defined
[*04/08/2020 03:50:42.8482] Cal location [1]: 00004000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] wifi1 NAND FLASH Select OFFSET 0x5000
[*04/08/2020 03:50:42.8682] qc98xx_verify_checksum: flash checksum passed: 0xae3f
[*04/08/2020 03:50:42.8682] ol_transfer_bin_file 3979: Download Flash data len 12064
[*04/08/2020 03:50:42.8882]
[*04/08/2020 03:50:42.8882] Board data initialized
[*04/08/2020 03:50:42.9381] ol_ath_download_firmware :First OTP download and Execute is good address:0xd400 return param 4660
[*04/08/2020 03:50:42.9381] ol_ath_download_firmware:##Board Id 21 , CHIP Id 1
[*04/08/2020 03:50:42.9381] ol_transfer_bin_file: Board Data File download to address=0xc0000 file name=AR900B/hw.2/boardData_AR900B_CUS239_negative_pwr_offset_5G_2X2_021.bin
[*04/08/2020 03:50:43.0081]
[*04/08/2020 03:50:43.0081] [Flash] : Ignore Module param
[*04/08/2020 03:50:43.0081] ol_ath_download_firmware : Second OTP download and Execute is good, param=0x0
[*04/08/2020 03:50:43.0281] ol_transfer_bin_file: Downloading firmware file: AR900B/hw.2/athwlan.bin
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x3, 0xdeb001, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x12, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x45, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x67, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:44.1977] HTC Rx: insufficient length, got:4 expected =8
[*04/08/2020 03:50:44.1977] Startup Mode-0 set
[*04/08/2020 03:50:44.1977] HTC Service:0x0300 ep:1 TX flow control disabled
[*04/08/2020 03:[*04/08/2020 03:51:01.0625] Loading sha2...
[*04/08/2020 03:51:01.0625] Dumpping sha1...
[*04/08/2020 03:51:02.5421] Loading MIC cert and key
[*04/08/2020 03:51:02.5421] Dumpping sha2...
[*04/08/2020 03:51:04.0216] Loading MIC cert and key
[*04/08/2020 03:51:04.4315] Generating key, this may take a while...
[*04/08/2020 03:51:08.7301] Public key portion is:
[*04/08/2020 03:51:08.7301] ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC26TxfEJHrGWUvetqKwWdOtKvFydoMRSV565vNfaCsIQonXzYM/JroWmHml2X7BhlcCRiT29xCRXhoYXEgqIz53t2VyAzU1zjAg/NSqUB/3N753WMkD35fCXN0oW8KsIZmCI48wOZc/kU8JpkzujaMPiow3A/kQ+/a8g6bAiFiAr2whntoyvmc57VuB8IKeWU1wBpKp5uOqns8ZXconFo2cyjBwubEg60h+5OKq8t6VXlYt7tBZbzVoF9XKiAA/zpVF73m04wem5Aq+GNHnEmiJjMW9Tk7a/Fm5/b9k8Vsxt1ddm3bUkTu5f4I4UVY1Hl1Ykfeg7shYxIGVa3mBC4V root@m00B0E1880CC0
[*04/08/2020 03:51:08.7301] Fingerprint: sha1!! b4:84:be:2f:dc:01:71:16:e8:fd:9f:7b:57:c0:1e:8d:13:1f:35:7a
[*04/08/2020 03:51:08.7701] pid 3997's current affinity mask: 3
[*04/08/2020 03:51:08.7701] pid 3997's new affinity mask: 1
[*04/08/2020 03:51:09.2800] Password for user changed
[*04/08/2020 03:51:09.4299] gzip -dc /etc/wcp.usermodule.template.gz | sed -e 's/__TX_POWER_2G_FILE__/\/radio_fw\/H2.csv/g' -e 's/__TX_POWER_5G_FILE__/\/radio_fw\/H5.csv/g' -e 's/__EVM_POWER_2G_FILE__/\/radio_fw\/EVM_2.csv/g' -e 's/__EVM_POWER_5G_FILE__/\/radio_fw\/EVM_5.csv/g' -e 's/__DOMAIN_2G__/0/g' -e 's/__DOMAIN_5G__/41/g' -e 's/__PWR_TABLE_49G__/0/g' -e 's/__PRODUCT_ID__/AIR-OEAP1810-B-K9/g' -e 's/__AP_TYPE__/63/g' -e 's/__WIRELESS_MAC__/00:B0:E1:88:99:80/g' -e 's/__WIRED_MAC__/00:B0:E1:88:0C:C0/g' -e 's/__WIRED1_MAC__/00:B0:E1:88:0C:C0/g' | DMALLOC_OPTIONS=debug=0x400003,inter=1000,log=/tmp/wcp.dmalloc.log,limit=40000000 wcpd &
[*04/08/2020 03:51:11.0094] DOT11_DRV[1]: Init Radio1
[*04/08/2020 03:51:11.0294] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:11.0394] DOT11_DRV[1]: set_channel Channel set to 36
[*04/08/2020 03:51:11.0494] DOT11_DRV[0]: Init Radio0
[*04/08/2020 03:51:11.0794] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.0794] DOT11_DRV[0]: set_channel Channel set to 6
[*04/08/2020 03:51:11.5293] DOT11_CFG[0] Radio Mode is changed from Local to FlexConnect
[*04/08/2020 03:51:11.5393] DOT11_DRV[0]: Start Radio0
[*04/08/2020 03:51:11.5393] DOT11_CFG[1] Radio Mode is changed from Local to FlexConnect
[*04/08/2020 03:51:11.5393] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:11.5592] ADDRCONF(NETDEV_CHANGE): wired3: link becomes ready
[*04/08/2020 03:51:11.5692] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.7592] DOT11_DRV[0]: set_channel Channel set to 1
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Start Radio0
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.9891] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:51:11.9991] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.0091] DOT11_DRV[1]: set_channel Channel set to 36
[*04/08/2020 03:51:12.0091] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:12.0191] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.2090] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:51:12.2290] /usr/sbin/capwapd: opening /click/cli_h/apr_bypass/active failed!: No such file or directory
[*04/08/2020 03:51:12.2290]
[*04/08/2020 03:51:12.2290] !!!!! {/usr/sbin/capwapd} failed writing /click/cli_h/apr_bypass/active len 1 data: "1"
[*04/08/2020 03:51:16.9875] Waiting for uplink IPv4 configuration
[*04/08/2020 03:51:21.9860] Waiting for uplink IPv4 configuration
[*04/08/2020 03:51:22.7657] ethernet_port wired0, ip 192.168.1.247, netmask 255.255.255.0, gw 192.168.1.1, mtu 1500, bcast 192.168.1.255, dns1 192.168.1.1, domain lan, vid 0, static_ip_failover false, dhcp_vlan_failover false
[*04/08/2020 03:51:28.1141] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:51:28.1141] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:51:28.1641] AP IPv4 Address updated from 0.0.0.0 to 192.168.1.247
[*04/08/2020 03:51:28.1840] dtls_init: Use MIC certificate
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] CAPWAP State: Init
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] PNP is not required,
[*04/08/2020 03:51:28.1840] Starting CAPWAP discovery
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] CAPWAP State: Discovery
[*04/08/2020 03:51:28.1940] Discovery Request sent to 192.168.1.3, discovery type STATIC_CONFIG(1)
[*04/08/2020 03:51:28.1940] IP DNS query for CISCO-CAPWAP-CONTROLLER.lan
[*04/08/2020 03:51:28.6639] Discovery Request sent to 192.168.1.3, discovery type STATIC_CONFIG(1)
[*04/08/2020 03:51:28.6739] Discovery Request sent to 255.255.255.255, discovery type UNKNOWN(0)
[*04/08/2020 03:51:28.6739]
[*04/08/2020 03:51:28.6739] CAPWAP State: Discovery
[*04/08/2020 03:51:28.6739] Discovery Response from 192.168.1.3
[*04/08/2020 03:51:28.7039] Discovery Response from 192.168.1.3
[*04/08/2020 03:51:28.7239] Discovery Response from 192.168.1.3
[*04/08/2020 03:53:49.0000]
[*04/08/2020 03:53:49.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:53:49.0199] First connect to vWLC, accept vWLC by default
[*04/08/2020 03:53:49.0199]
[*04/08/2020 03:53:49.0399]
[*04/08/2020 03:53:49.0399] CAPWAP State: Join
[*04/08/2020 03:53:49.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:53:49.0599] Join Response from 192.168.1.3
[*04/08/2020 03:53:49.1499] nss_capwapmgr_enable_tunnel[1661]:ddf0e000: tunnel 0 is already enabled
[*04/08/2020 03:53:49.1699]
[*04/08/2020 03:53:49.1699] CAPWAP State: Image Data
[*04/08/2020 03:53:49.2099] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:53:49.2199]
[*04/08/2020 03:53:49.2199] CAPWAP State: Configure
[*04/08/2020 03:53:49.2199] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:53:49.2199] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:53:52.0390] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:52.0390]
[*04/08/2020 03:53:54.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:54.8882]
[*04/08/2020 03:53:57.7473] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:57.7473]
[*04/08/2020 03:54:00.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:00.5964]
[*04/08/2020 03:54:03.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:03.4455]
[*04/08/2020 03:54:06.3046] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:06.3046]
[*04/08/2020 03:54:06.3046] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:54:06.3146] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:54:06.3146] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:54:06.3246] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:54:06.3246] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:54:06.4345] Flexconnect Switching to Standalone Mode!
[*04/08/2020 03:54:06.7145]
[*04/08/2020 03:54:06.7145] CAPWAP State: DTLS Teardown
[*04/08/2020 03:54:11.5729] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:11.5929] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:11.6129] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:22.0000]
[*04/08/2020 03:54:22.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:54:22.0399]
[*04/08/2020 03:54:22.0399] CAPWAP State: Join
[*04/08/2020 03:54:22.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:54:22.0499] Join Response from 192.168.1.3
[*04/08/2020 03:54:22.1499]
[*04/08/2020 03:54:22.1499] CAPWAP State: Image Data
[*04/08/2020 03:54:22.1999] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:54:22.1999]
[*04/08/2020 03:54:22.1999] CAPWAP State: Configure
[*04/08/2020 03:54:22.1999] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:22.1999] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:25.0291] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:25.0291]
[*04/08/2020 03:54:27.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:27.8882]
[*04/08/2020 03:54:30.7473] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:30.7473]
[*04/08/2020 03:54:33.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:33.5964]
[*04/08/2020 03:54:36.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:36.4455]
[*04/08/2020 03:54:39.3046] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:39.3046]
[*04/08/2020 03:54:39.3046] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:54:39.3046]
[*04/08/2020 03:54:39.3046] CAPWAP State: DTLS Teardown
[*04/08/2020 03:54:44.1931] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:44.2231] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:44.2330] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:53.0000]
[*04/08/2020 03:54:53.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:54:53.0399]
[*04/08/2020 03:54:53.0399] CAPWAP State: Join
[*04/08/2020 03:54:53.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:54:53.0399] Join Response from 192.168.1.3
[*04/08/2020 03:54:53.1599]
[*04/08/2020 03:54:53.1599] CAPWAP State: Image Data
[*04/08/2020 03:54:53.2099] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:54:53.2099]
[*04/08/2020 03:54:53.2099] CAPWAP State: Configure
[*04/08/2020 03:54:53.2099] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:53.2099] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:56.0390] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:56.0390]
[*04/08/2020 03:54:58.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:58.8882]
[*04/08/2020 03:55:01.7373] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:01.7373]
[*04/08/2020 03:55:04.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:04.5964]
[*04/08/2020 03:55:07.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:07.4455]
[*04/08/2020 03:55:10.2946] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:10.2946]
[*04/08/2020 03:55:10.2946] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:55:10.3046]
[*04/08/2020 03:55:10.3046] CAPWAP State: DTLS Teardown
[*04/08/2020 03:55:15.1831] Discovery Response from 192.168.1.3
[*04/08/2020 03:55:15.2031] Discovery Response from 192.168.1.3
[*04/08/2020 03:55:15.2231] Discovery Response from 192.168.1.3
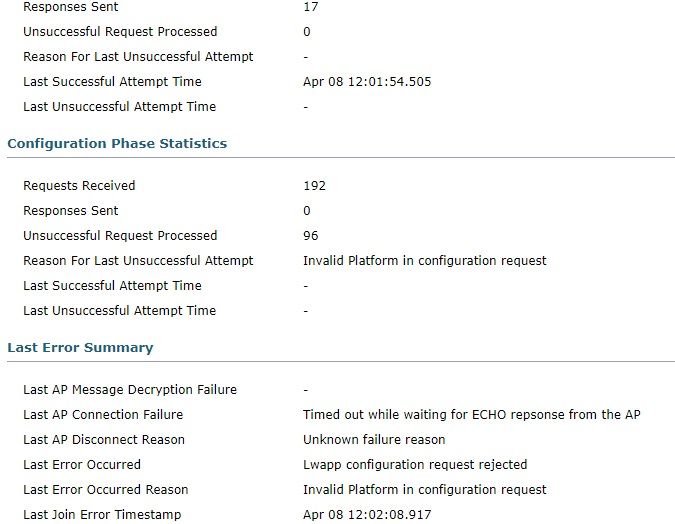

最后这个log一直反复:*spamApTask2: Apr 08 14:18:43.394: %CAPWAP-3-POST_DECODE_ERR: capwap_ac_sm.c:6548 Post decode processing failed for Config status from AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 14:18:43.394: %LOG-3-Q_IND: spam_lrad.c:13481 APs 00:b0:e1:88:99:80 country code changed from (UX) to (US )
不知道什么意思,我的设置是US。
console口输出显示在下方,vWLC虚拟控制器版本为: 8.5.161,AP为AIR-OEAP1810-CRD,在控制器内识别为AIR-OEAP1810-B-K9,恢复出厂后,它会自动升级适合控制器的固件版本,自动加入等等一切正常,但是加入后很快它又会闪红黄绿三色灯,表示又在重新连接控制器,而这时候它在控制器的状态是加入中,而等上一会,它就会成功地加入到控制器,并且在控制器的已加入AP列表中出现,那时候会闪绿灯,但很快又会回到闪红黄绿三色灯的状态去。这样反反复复。
其他连在这控制器的几个3602正常工作没有问题。尝试过capwap ap erase all 命令恢复出厂,它也能自动加入到控制器,但加入控制器后就开始断开,然后反复加入。看console口输出显示看不到有什么问题。
以下是console口输出显示,后面那些相同的部分就是一直在反复加入和断开。附图为控制器上的出错信息。
Welcome to Cisco.
Usage of this device is governed by Cisco's End User License Agreement,
available at:
http://www.cisco.com/c/en/us/td/docs/general/warranty/English/EU1KEN_.html.
Restricted Rights Legend
Use, duplication, or disclosure by the Government is subject to
restrictions as set forth in subparagraph (c) of the Commercial
Computer Software - Restricted Rights clause at FAR sec. 52.227-19 and
subparagraph (c) (1) (ii) of the Rights in Technical Data and Computer
Software clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
This product contains cryptographic features and is subject to United
States and local country laws governing import, export, transfer and
use. Delivery of Cisco cryptographic products does not imply
third-party authority to import, export, distribute or use encryption.
Importers, exporters, distributors and users are responsible for
compliance with U.S. and local country laws. By using this product you
agree to comply with applicable laws and regulations. If you are unable
to comply with U.S. and local laws, return this product immediately.
A summary of U.S. laws governing Cisco cryptographic products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by sending email to
export@cisco.com.
This product contains some software licensed under the
"GNU General Public License, version 2" provided with
ABSOLUTELY NO WARRANTY under the terms of
"GNU General Public License, version 2", available here:
http://www.gnu.org/licenses/old-licenses/gpl-2.0.html
This product contains some software licensed under the
"GNU Library General Public License, version 2" provided
with ABSOLUTELY NO WARRANTY under the terms of "GNU Library
General Public License, version 2", available here:
http://www.gnu.org/licenses/old-licenses/lgpl-2.0.html
This product contains some software licensed under the
"GNU Lesser General Public License, version 2.1" provided
with ABSOLUTELY NO WARRANTY under the terms of "GNU Lesser
General Public License, version 2.1", available here:
http://www.gnu.org/licenses/old-licenses/lgpl-2.1.html
This product contains some software licensed under the
"GNU General Public License, version 3" provided with
ABSOLUTELY NO WARRANTY under the terms of
"GNU General Public License, Version 3", available here:
http://www.gnu.org/licenses/gpl.html.
This product contains some software licensed under the
"GNU Affero General Public License, version 3" provided
with ABSOLUTELY NO WARRANTY under the terms of
"GNU Affero General Public License, version 3", available here:
http://www.gnu.org/licenses/agpl-3.0.html.
init started: BusyBox v1.23.2 (2020-02-17 12:14:41 PST)
[*01/01/1970 00:00:28.2913] GCM-128 POST passed
[*01/01/1970 00:00:28.2913] GCM-256 POST passed
[*01/01/1970 00:00:28.4113] === 5G radio domain is 41, COPY 5G BDF files from non_ETSI_BDF folder ===
[*01/01/1970 00:00:28.4612] 0
[*01/01/1970 00:00:28.6712] Active version: 8.5.161.0
[*01/01/1970 00:00:28.6712] Backup version: 8.5.151.0
Jan 1 00:00:28 FIPS[1659]: *** shell: FIPS Mode = disabled ***
[*01/01/1970 00:00:28.8611]
[*01/01/1970 00:00:28.8611] led pattern module start
User Access Verification
Username: [*01/01/1970 00:00:28.9211] AP1810
[*01/01/1970 00:00:29.0111] nss_driver - Turbo Support 1
[*01/01/1970 00:00:29.0111] Supported Frequencies - 110Mhz 550Mhz 733Mhz
[*01/01/1970 00:00:29.0411] NSS firmware booted
[*01/01/1970 00:00:29.0611] NSS firmware booted
[*01/01/1970 00:00:35.1891] ssdk_plat_init start
[*01/01/1970 00:00:35.1891] Register QCA PHY driver
[*01/01/1970 00:00:35.1991] PHY ID is 0x4dd036
[*01/01/1970 00:00:35.3691] qca probe f1 phy driver succeeded!
[*01/01/1970 00:00:35.3691] qca-ssdk module init succeeded!
[*01/01/1970 00:00:35.3791] Chip version 0x1302
[*01/01/1970 00:00:35.9789]
[*01/01/1970 00:00:35.9789] Swtich config done.
[*01/01/1970 00:00:37.9183] Current value of FACTORY_RESET=0
[*11/08/2016 23:59:59.0099] Last reload time: Apr 8 03:50:37 2020
[*04/08/2020 03:50:37.0000] Setting system time Wed Apr 8 03:50:37 UTC 2020
[*04/08/2020 03:50:37.0599] device wired0 entered promiscuous mode
[*04/08/2020 03:50:37.0899] device eth1 entered promiscuous mode
[*04/08/2020 03:50:38.6595] stile module dp init successfully
[*04/08/2020 03:50:38.6595] NBAR Label:BLD_V155_3_S_XE316_THROTTLE_LATEST_20180404_162221 NBAR VERSION:module build date: Feb 17 2020 at 12:28:56
[*04/08/2020 03:50:39.2993] miibus get dd50fc00!
[*04/08/2020 03:50:39.3293]
[*04/08/2020 03:50:39.3393] boot 26 build T-eaf8c9a5819ff90fa88df9b4045e20adf0d0a259-geaf8c9a5-vipendya board corsica mac 00:B0:E1:88:0C:C0
[*04/08/2020 03:50:39.3393] Module: mbedtls .text=0xbf000000 data=0xbf007e18 bss=0xbf008070
[*04/08/2020 03:50:39.3393] Module: aptrace .text=0xbf00c000 data=0xbf018834 bss=0xbf018cc0
[*04/08/2020 03:50:39.3393] Module: led_module .text=0xbf020000 data=0xbf0204e0 bss=0xbf020b48
[*04/08/2020 03:50:39.3393] Module: qca_nss_gmac .text=0xbf024000 data=0xbf02abd4 bss=0xbf02b098
[*04/08/2020 03:50:39.3393] Module: qca_nss_drv .text=0xbf034000 data=0xbf04f9e8 bss=0xbf050798
[*04/08/2020 03:50:39.3393] Module: qca_nss_capwapmgr .text=0xbf071000 data=0xbf075ad4 bss=0xbf075c28
[*04/08/2020 03:50:39.3393] Module: nssmgrctl .text=0xbf07c000 data=0xbf07d728 bss=0xbf07da4c
[*04/08/2020 03:50:39.3393] Module: qca_nss_portifmgr .text=0xbf083000 data= bss=0xbf083dcc
[*04/08/2020 03:50:39.3393] Module: qca_ssdk .text=0xbf088000 data=0xbf11e544 bss=0xbf123ecc
[*04/08/2020 03:50:39.3393] Module: proclikefs .text=0xbf172000 data= bss=0xbf172b40
[*04/08/2020 03:50:39.3393] Module: stile_lm_ft .text= data= bss=
[*04/08/2020 03:50:39.3393] Module: stile_lm_dp .text= data= bss=
[*04/08/2020 03:50:39.3393] Module: ipv6 .text=0xbfb01000 data=0xbfb31fc0 bss=0xbfb3386c
[*04/08/2020 03:50:39.3393] Module: bonding .text=0xbfb4d000 data=0xbfb5e640 bss=0xbfb5ea6c
[*04/08/2020 03:50:39.3393] Module: lowmemorykiller .text=0xbfb6b000 data=0xbfb6b2c0 bss=0xbfb6b44c
[*04/08/2020 03:50:39.3393] Module: qca_nss_profile:41.3886] ol_transfer_bin_file: flash data file defined
[*04/08/2020 03:50:41.3886] Cal location [0]: 00000000
[*04/08/2020 03:50:41.3886]
[*04/08/2020 03:50:41.3886] Wifi0 NAND FLASH Select OFFSET 0x1000
[*04/08/2020 03:50:41.4086] qc98xx_verify_checksum: flash checksum passed: 0xd618
[*04/08/2020 03:50:41.4086] ol_transfer_bin_file 3979: Download Flash data len 12064
[*04/08/2020 03:50:41.4286]
[*04/08/2020 03:50:41.4286] Board data initialized
[*04/08/2020 03:50:41.4786] ol_ath_download_firmware :First OTP download and Execute is good address:0xd800 return param 4660
[*04/08/2020 03:50:41.4786] ol_ath_download_firmware:##Board Id 22 , CHIP Id 1
[*04/08/2020 03:50:41.4786] ol_transfer_bin_file: Board Data File download to address=0xc0000 file name=AR900B/hw.2/boardData_AR900B_CUS260_negative_pwr_offset_2G_2X2_022.bin
[*04/08/2020 03:50:41.5586]
[*04/08/2020 03:50:41.5586] [Flash] : Ignore Module param
[*04/08/2020 03:50:41.5586] ol_ath_download_firmware : Second OTP download and Execute is good, param=0x0
[*04/08/2020 03:50:41.5786] ol_transfer_bin_file: Downloading firmware file: AR900B/hw.2/athwlan.bin
[*04/08/2020 03:50:42.7482] HTC Rx: insufficient length, got:4 expected =8
[*04/08/2020 03:50:42.7482] Startup Mode-0 set
[*04/08/2020 03:50:42.7482] HTC Service:0x0300 ep:1 TX flow control disabled
[*04/08/2020 03:50:42.7482] HTC Service:0x0100 ep:2 TX flow control disabled
[*04/08/2020 03:50:42.7482] Firmware_Build_Number:70
[*04/08/2020 03:50:42.7482] num_rf_chain:0x00000002 ht_cap_info:0x0000185b vht_cap_info:0x339979b2 vht_supp_mcs:0x0000fffa
[*04/08/2020 03:50:42.7482]
[*04/08/2020 03:50:42.7482] RES CFG Support wmi_service_bitmap 9778
[*04/08/2020 03:50:42.7482]
[*04/08/2020 03:50:42.7482] Sending Ext resource cfg: HOST PLATFORM as 0 and fw_feature_bitmap as 50 to TGT
[*04/08/2020 03:50:42.7482] ol_ath_service_ready_event: sw_cal_support_check_flag: 1
[*04/08/2020 03:50:42.8282] wmi_ready_event_rx: WMI UNIFIED READY event
[*04/08/2020 03:50:42.8282] htt_h2t_frag_desc_bank_cfg_msg - HTT_H2T_MSG_TYPE_FRAG_DESC_BANK_CFG sent to FW for radio ID = 0
[*04/08/2020 03:50:42.8282] ACS not enabled
[*04/08/2020 03:50:42.8282] ol_ath_thermal_mitigation_attach: --
[*04/08/2020 03:50:42.8282]
[*04/08/2020 03:50:42.8282] __ol_ath_attach() Allocated scn d7a40480
[*04/08/2020 03:50:42.8382] ol_ath_attach interface_id 1
[*04/08/2020 03:50:42.8482] Chip id: 0x9, chip version: 0x1000000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] Target Version is 1000000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] Flash Download Address c0000
[*04/08/2020 03:50:42.8482] ol_transfer_bin_file: flash data file defined
[*04/08/2020 03:50:42.8482] Cal location [1]: 00004000
[*04/08/2020 03:50:42.8482]
[*04/08/2020 03:50:42.8482] wifi1 NAND FLASH Select OFFSET 0x5000
[*04/08/2020 03:50:42.8682] qc98xx_verify_checksum: flash checksum passed: 0xae3f
[*04/08/2020 03:50:42.8682] ol_transfer_bin_file 3979: Download Flash data len 12064
[*04/08/2020 03:50:42.8882]
[*04/08/2020 03:50:42.8882] Board data initialized
[*04/08/2020 03:50:42.9381] ol_ath_download_firmware :First OTP download and Execute is good address:0xd400 return param 4660
[*04/08/2020 03:50:42.9381] ol_ath_download_firmware:##Board Id 21 , CHIP Id 1
[*04/08/2020 03:50:42.9381] ol_transfer_bin_file: Board Data File download to address=0xc0000 file name=AR900B/hw.2/boardData_AR900B_CUS239_negative_pwr_offset_5G_2X2_021.bin
[*04/08/2020 03:50:43.0081]
[*04/08/2020 03:50:43.0081] [Flash] : Ignore Module param
[*04/08/2020 03:50:43.0081] ol_ath_download_firmware : Second OTP download and Execute is good, param=0x0
[*04/08/2020 03:50:43.0281] ol_transfer_bin_file: Downloading firmware file: AR900B/hw.2/athwlan.bin
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x3, 0xdeb001, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x12, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x45, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:43.7479] FWLOG: [44601] WAL_DBGID_TX_AC_BUFFER_SET ( 0x67, 0x1e, 0x94c, 0x94c, 0x0 )
[*04/08/2020 03:50:44.1977] HTC Rx: insufficient length, got:4 expected =8
[*04/08/2020 03:50:44.1977] Startup Mode-0 set
[*04/08/2020 03:50:44.1977] HTC Service:0x0300 ep:1 TX flow control disabled
[*04/08/2020 03:[*04/08/2020 03:51:01.0625] Loading sha2...
[*04/08/2020 03:51:01.0625] Dumpping sha1...
[*04/08/2020 03:51:02.5421] Loading MIC cert and key
[*04/08/2020 03:51:02.5421] Dumpping sha2...
[*04/08/2020 03:51:04.0216] Loading MIC cert and key
[*04/08/2020 03:51:04.4315] Generating key, this may take a while...
[*04/08/2020 03:51:08.7301] Public key portion is:
[*04/08/2020 03:51:08.7301] ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC26TxfEJHrGWUvetqKwWdOtKvFydoMRSV565vNfaCsIQonXzYM/JroWmHml2X7BhlcCRiT29xCRXhoYXEgqIz53t2VyAzU1zjAg/NSqUB/3N753WMkD35fCXN0oW8KsIZmCI48wOZc/kU8JpkzujaMPiow3A/kQ+/a8g6bAiFiAr2whntoyvmc57VuB8IKeWU1wBpKp5uOqns8ZXconFo2cyjBwubEg60h+5OKq8t6VXlYt7tBZbzVoF9XKiAA/zpVF73m04wem5Aq+GNHnEmiJjMW9Tk7a/Fm5/b9k8Vsxt1ddm3bUkTu5f4I4UVY1Hl1Ykfeg7shYxIGVa3mBC4V root@m00B0E1880CC0
[*04/08/2020 03:51:08.7301] Fingerprint: sha1!! b4:84:be:2f:dc:01:71:16:e8:fd:9f:7b:57:c0:1e:8d:13:1f:35:7a
[*04/08/2020 03:51:08.7701] pid 3997's current affinity mask: 3
[*04/08/2020 03:51:08.7701] pid 3997's new affinity mask: 1
[*04/08/2020 03:51:09.2800] Password for user changed
[*04/08/2020 03:51:09.4299] gzip -dc /etc/wcp.usermodule.template.gz | sed -e 's/__TX_POWER_2G_FILE__/\/radio_fw\/H2.csv/g' -e 's/__TX_POWER_5G_FILE__/\/radio_fw\/H5.csv/g' -e 's/__EVM_POWER_2G_FILE__/\/radio_fw\/EVM_2.csv/g' -e 's/__EVM_POWER_5G_FILE__/\/radio_fw\/EVM_5.csv/g' -e 's/__DOMAIN_2G__/0/g' -e 's/__DOMAIN_5G__/41/g' -e 's/__PWR_TABLE_49G__/0/g' -e 's/__PRODUCT_ID__/AIR-OEAP1810-B-K9/g' -e 's/__AP_TYPE__/63/g' -e 's/__WIRELESS_MAC__/00:B0:E1:88:99:80/g' -e 's/__WIRED_MAC__/00:B0:E1:88:0C:C0/g' -e 's/__WIRED1_MAC__/00:B0:E1:88:0C:C0/g' | DMALLOC_OPTIONS=debug=0x400003,inter=1000,log=/tmp/wcp.dmalloc.log,limit=40000000 wcpd &
[*04/08/2020 03:51:11.0094] DOT11_DRV[1]: Init Radio1
[*04/08/2020 03:51:11.0294] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:11.0394] DOT11_DRV[1]: set_channel Channel set to 36
[*04/08/2020 03:51:11.0494] DOT11_DRV[0]: Init Radio0
[*04/08/2020 03:51:11.0794] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.0794] DOT11_DRV[0]: set_channel Channel set to 6
[*04/08/2020 03:51:11.5293] DOT11_CFG[0] Radio Mode is changed from Local to FlexConnect
[*04/08/2020 03:51:11.5393] DOT11_DRV[0]: Start Radio0
[*04/08/2020 03:51:11.5393] DOT11_CFG[1] Radio Mode is changed from Local to FlexConnect
[*04/08/2020 03:51:11.5393] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:11.5592] ADDRCONF(NETDEV_CHANGE): wired3: link becomes ready
[*04/08/2020 03:51:11.5692] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.7592] DOT11_DRV[0]: set_channel Channel set to 1
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Start Radio0
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:51:11.7692] DOT11_DRV[0]: Stop Radio0
[*04/08/2020 03:51:11.9891] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:51:11.9991] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.0091] DOT11_DRV[1]: set_channel Channel set to 36
[*04/08/2020 03:51:12.0091] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:12.0191] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Start Radio1
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:51:12.1990] DOT11_DRV[1]: Stop Radio1
[*04/08/2020 03:51:12.2090] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:51:12.2290] /usr/sbin/capwapd: opening /click/cli_h/apr_bypass/active failed!: No such file or directory
[*04/08/2020 03:51:12.2290]
[*04/08/2020 03:51:12.2290] !!!!! {/usr/sbin/capwapd} failed writing /click/cli_h/apr_bypass/active len 1 data: "1"
[*04/08/2020 03:51:16.9875] Waiting for uplink IPv4 configuration
[*04/08/2020 03:51:21.9860] Waiting for uplink IPv4 configuration
[*04/08/2020 03:51:22.7657] ethernet_port wired0, ip 192.168.1.247, netmask 255.255.255.0, gw 192.168.1.1, mtu 1500, bcast 192.168.1.255, dns1 192.168.1.1, domain lan, vid 0, static_ip_failover false, dhcp_vlan_failover false
[*04/08/2020 03:51:28.1141] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:51:28.1141] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:51:28.1641] AP IPv4 Address updated from 0.0.0.0 to 192.168.1.247
[*04/08/2020 03:51:28.1840] dtls_init: Use MIC certificate
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] CAPWAP State: Init
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] PNP is not required,
[*04/08/2020 03:51:28.1840] Starting CAPWAP discovery
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840]
[*04/08/2020 03:51:28.1840] CAPWAP State: Discovery
[*04/08/2020 03:51:28.1940] Discovery Request sent to 192.168.1.3, discovery type STATIC_CONFIG(1)
[*04/08/2020 03:51:28.1940] IP DNS query for CISCO-CAPWAP-CONTROLLER.lan
[*04/08/2020 03:51:28.6639] Discovery Request sent to 192.168.1.3, discovery type STATIC_CONFIG(1)
[*04/08/2020 03:51:28.6739] Discovery Request sent to 255.255.255.255, discovery type UNKNOWN(0)
[*04/08/2020 03:51:28.6739]
[*04/08/2020 03:51:28.6739] CAPWAP State: Discovery
[*04/08/2020 03:51:28.6739] Discovery Response from 192.168.1.3
[*04/08/2020 03:51:28.7039] Discovery Response from 192.168.1.3
[*04/08/2020 03:51:28.7239] Discovery Response from 192.168.1.3
[*04/08/2020 03:53:49.0000]
[*04/08/2020 03:53:49.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:53:49.0199] First connect to vWLC, accept vWLC by default
[*04/08/2020 03:53:49.0199]
[*04/08/2020 03:53:49.0399]
[*04/08/2020 03:53:49.0399] CAPWAP State: Join
[*04/08/2020 03:53:49.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:53:49.0599] Join Response from 192.168.1.3
[*04/08/2020 03:53:49.1499] nss_capwapmgr_enable_tunnel[1661]:ddf0e000: tunnel 0 is already enabled
[*04/08/2020 03:53:49.1699]
[*04/08/2020 03:53:49.1699] CAPWAP State: Image Data
[*04/08/2020 03:53:49.2099] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:53:49.2199]
[*04/08/2020 03:53:49.2199] CAPWAP State: Configure
[*04/08/2020 03:53:49.2199] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:53:49.2199] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:53:52.0390] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:52.0390]
[*04/08/2020 03:53:54.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:54.8882]
[*04/08/2020 03:53:57.7473] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:53:57.7473]
[*04/08/2020 03:54:00.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:00.5964]
[*04/08/2020 03:54:03.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:03.4455]
[*04/08/2020 03:54:06.3046] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:06.3046]
[*04/08/2020 03:54:06.3046] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:54:06.3146] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:54:06.3146] DOT11_DRV[0]: Channel set to 1, width 20
[*04/08/2020 03:54:06.3246] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:54:06.3246] DOT11_DRV[1]: Channel set to 36, width 80
[*04/08/2020 03:54:06.4345] Flexconnect Switching to Standalone Mode!
[*04/08/2020 03:54:06.7145]
[*04/08/2020 03:54:06.7145] CAPWAP State: DTLS Teardown
[*04/08/2020 03:54:11.5729] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:11.5929] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:11.6129] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:22.0000]
[*04/08/2020 03:54:22.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:54:22.0399]
[*04/08/2020 03:54:22.0399] CAPWAP State: Join
[*04/08/2020 03:54:22.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:54:22.0499] Join Response from 192.168.1.3
[*04/08/2020 03:54:22.1499]
[*04/08/2020 03:54:22.1499] CAPWAP State: Image Data
[*04/08/2020 03:54:22.1999] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:54:22.1999]
[*04/08/2020 03:54:22.1999] CAPWAP State: Configure
[*04/08/2020 03:54:22.1999] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:22.1999] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:25.0291] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:25.0291]
[*04/08/2020 03:54:27.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:27.8882]
[*04/08/2020 03:54:30.7473] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:30.7473]
[*04/08/2020 03:54:33.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:33.5964]
[*04/08/2020 03:54:36.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:36.4455]
[*04/08/2020 03:54:39.3046] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:39.3046]
[*04/08/2020 03:54:39.3046] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:54:39.3046]
[*04/08/2020 03:54:39.3046] CAPWAP State: DTLS Teardown
[*04/08/2020 03:54:44.1931] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:44.2231] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:44.2330] Discovery Response from 192.168.1.3
[*04/08/2020 03:54:53.0000]
[*04/08/2020 03:54:53.0000] CAPWAP State: DTLS Setup
[*04/08/2020 03:54:53.0399]
[*04/08/2020 03:54:53.0399] CAPWAP State: Join
[*04/08/2020 03:54:53.0399] Sending Join request to 192.168.1.3 through port 5248
[*04/08/2020 03:54:53.0399] Join Response from 192.168.1.3
[*04/08/2020 03:54:53.1599]
[*04/08/2020 03:54:53.1599] CAPWAP State: Image Data
[*04/08/2020 03:54:53.2099] do NO_UPGRADE, part2 is active part
[*04/08/2020 03:54:53.2099]
[*04/08/2020 03:54:53.2099] CAPWAP State: Configure
[*04/08/2020 03:54:53.2099] DOT11_CFG[0] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:53.2099] DOT11_CFG[1] Radio Mode is changed from FlexConnect to FlexConnect
[*04/08/2020 03:54:56.0390] Re-Tx Count=1, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:56.0390]
[*04/08/2020 03:54:58.8882] Re-Tx Count=2, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:54:58.8882]
[*04/08/2020 03:55:01.7373] Re-Tx Count=3, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:01.7373]
[*04/08/2020 03:55:04.5964] Re-Tx Count=4, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:04.5964]
[*04/08/2020 03:55:07.4455] Re-Tx Count=5, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:07.4455]
[*04/08/2020 03:55:10.2946] Re-Tx Count=6, Max Re-Tx Value=5, SendSeqNum=1, NumofPendingMsgs=1
[*04/08/2020 03:55:10.2946]
[*04/08/2020 03:55:10.2946] Max retransmission count exceeded, going back to DISCOVER mode.
[*04/08/2020 03:55:10.3046]
[*04/08/2020 03:55:10.3046] CAPWAP State: DTLS Teardown
[*04/08/2020 03:55:15.1831] Discovery Response from 192.168.1.3
[*04/08/2020 03:55:15.2031] Discovery Response from 192.168.1.3
[*04/08/2020 03:55:15.2231] Discovery Response from 192.168.1.3
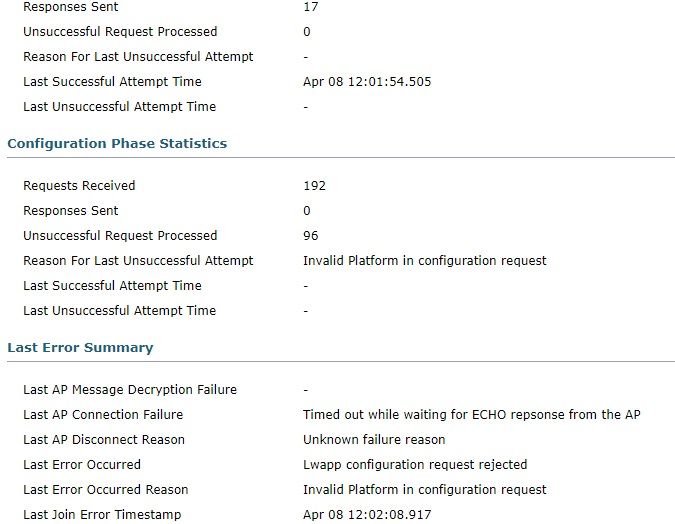

最后这个log一直反复:*spamApTask2: Apr 08 14:18:43.394: %CAPWAP-3-POST_DECODE_ERR: capwap_ac_sm.c:6548 Post decode processing failed for Config status from AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 14:18:43.394: %LOG-3-Q_IND: spam_lrad.c:13481 APs 00:b0:e1:88:99:80 country code changed from (UX) to (US )
不知道什么意思,我的设置是US。
标签:
- 标签:
-
无线
27 条回复27
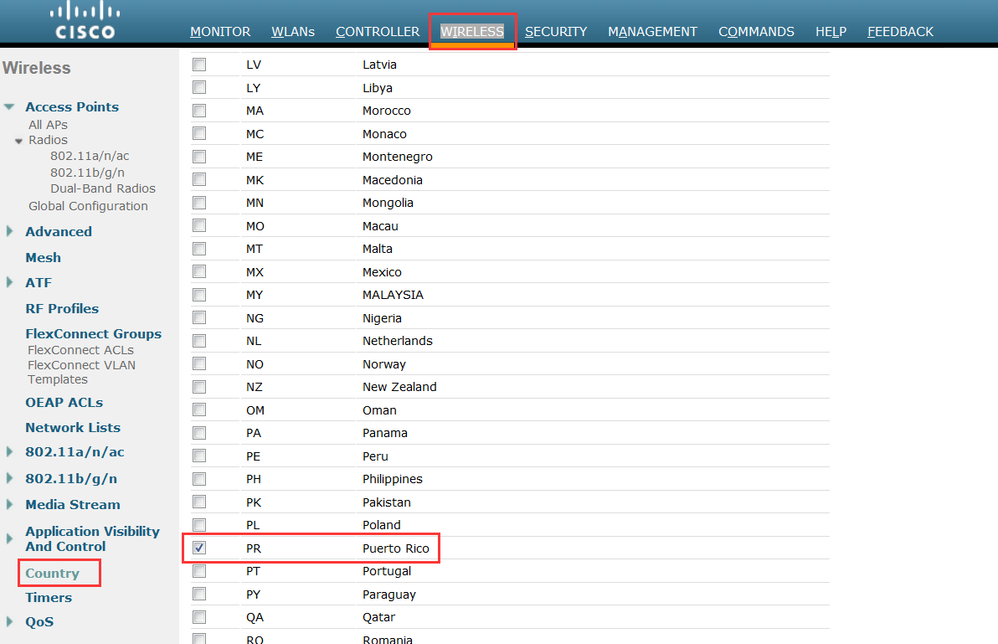
Post decode processing failed for Config status from AP
看看WLC的country code呢?把这个添加上试试看。
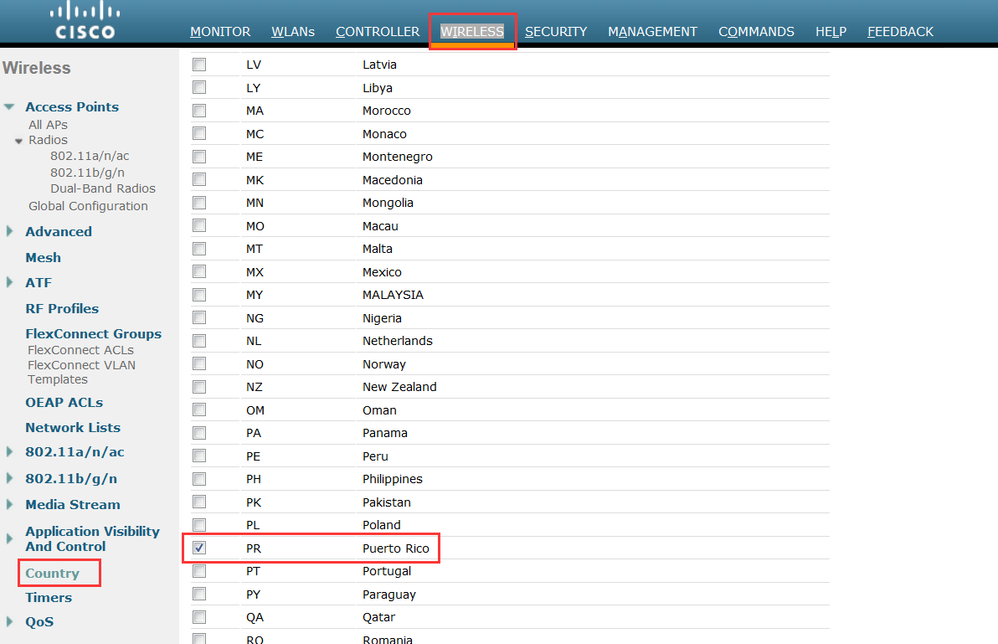
看看WLC的country code呢?把这个添加上试试看。
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
AlexChan21895 发表于 2020-4-8 17:00
你好,感谢您的及时回复,为什么会是波多黎各呢?这个AP在控制器里被识别为AIR-OEAP1810-B-K9。
AIR-OEAP1810-B-K9的话检查根据官网AP合规性,可以是USA 、Puerto Rico
麻烦将完整的show msglog共享一下呢,再看看两边的debug?
WLC> debug capwap errors enable
WLC> debug capwap events enable
WLC> debug dtls all enable
关闭debug:debug disable-all
AP# debug capwap client detail
AP# debug dtls client error
AP# debug dtls client event
关闭debug:un all
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
你好,我尝试加入了RP,情况一样.
下面是LOG:
(Cisco Controller) >debug capwap errors enable
(Cisco Controller) >*spamApTask1: Apr 08 18:01:44.257: 30:f7:0d:f6:eb:93 Discarding CAPWAP packet not for this WLC 192.168.1.188:61114 --> 10.9.250.27:5246
*spamApTask1: Apr 08 18:01:44.257: 30:f7:0d:f6:eb:93 Discarding CAPWAP packet not for this WLC 192.168.1.188:61114 --> 10.9.250.29:5246
*spamApTask1: Apr 08 18:01:44.258: 88:75:56:1f:76:10 ApModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:01:46.339: 34:bd:c8:bf:54:20 ApModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:01:46.340: 34:bd:c8:bf:54:20 ApModel: AIR-CAP3602I-A-K9
*spamApTask2: Apr 08 18:01:48.162: 00:b0:e1:88:99:80 Unable to get Ap mode in Join request
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 5 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
下面是LOG:
(Cisco Controller) >debug capwap errors enable
(Cisco Controller) >*spamApTask1: Apr 08 18:01:44.257: 30:f7:0d:f6:eb:93 Discarding CAPWAP packet not for this WLC 192.168.1.188:61114 --> 10.9.250.27:5246
*spamApTask1: Apr 08 18:01:44.257: 30:f7:0d:f6:eb:93 Discarding CAPWAP packet not for this WLC 192.168.1.188:61114 --> 10.9.250.29:5246
*spamApTask1: Apr 08 18:01:44.258: 88:75:56:1f:76:10 ApModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:01:46.339: 34:bd:c8:bf:54:20 ApModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:01:46.340: 34:bd:c8:bf:54:20 ApModel: AIR-CAP3602I-A-K9
*spamApTask2: Apr 08 18:01:48.162: 00:b0:e1:88:99:80 Unable to get Ap mode in Join request
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:48.427: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 5 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:51.162: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:54.013: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:54.014: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:56.865: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:01:59.722: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:01:59.723: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:02:02.573: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:02:02.574: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:55.930: 00:b0:e1:88:99:80 DTLS connection was closed
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP Country changed from:(UX) to (PR ).
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 00:b0:e1:88:99:80 AP DISABLED. In what country is the AP located?: PR,US.
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 State machine handler: Failed to process msg type = 5 state = 8 from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:53.073: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:08:55.930: 00:b0:e1:88:99:80 DTLS connection was closed
本帖最后由 AlexChan21895 于 2020-4-8 18:54 编辑
OEAP1810的MAC是:00:b0:e1:88:0c:c0, IP地址是:192.168.1.247
(Cisco Controller) >debug capwap events enable
(Cisco Controller) >*spamApTask2: Apr 08 18:50:28.153: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:15.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343075
*spamApTask1: Apr 08 18:51:16.490: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343076
*spamApTask1: Apr 08 18:51:16.491: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:16.850: 00:b0:e1:88:0c:c0 DTLS connection not found, creating new connection for 192.168.1.247 (5264) 192.168.1.3 (5246)
*spamApTask2: Apr 08 18:51:16.878: 00:b0:e1:88:0c:c0 DTLS Session established server (192.168.1.3:5246), client (192.168.1.247:5264)
*spamApTask2: Apr 08 18:51:16.878: 00:b0:e1:88:0c:c0 Starting wait join timer for AP: 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 Join Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 Allocate database entry for AP 192.168.1.247:5264, already allocated index 65535
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 AP Allocate request at index 76 (local)
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:0c:c0 Deleting AP entry 192.168.1.247:5264 from temporary database.
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:99:80 Dropping request or response packet to AP :192.168.1.247 (5264) by Controller: 192.168.1.3 (5246), message Capwap_wtp_event_response, state Capwap_no_state
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:99:80 Message type Capwap_wtp_event_response is not allowed to send in state Capwap_no_state for AP 192.168.1.247
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join Version: = 134586624
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join resp: CAPWAP Maximum Msg element len = 81
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join Response sent to 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 CAPWAP State: Join
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 capwap_ac_platform.c:2076 - Operation State 0 ===> 4
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:16.919: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.919: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.919: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.919: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 SSID LEDE_FT is not advertised on AP for radio 802.11B due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 SSID LEDE_2.4G is not advertised on AP for radio 802.11A due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:16.920: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.920: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.920: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.920: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:17.287: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343077
*spamApTask1: Apr 08 18:51:17.287: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:17.726: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343077
*spamApTask1: Apr 08 18:51:17.726: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask2: Apr 08 18:51:22.742: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:22.754: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343082
*spamApTask1: Apr 08 18:51:22.754: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:23.070: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343083
*spamApTask1: Apr 08 18:51:23.070: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*apf80211vTask: Apr 08 18:51:25.533: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:25.534: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:25.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343085
*spamApTask2: Apr 08 18:51:25.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:26.490: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343086
*spamApTask1: Apr 08 18:51:26.490: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:27.287: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343087
*spamApTask1: Apr 08 18:51:27.287: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:27.726: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343087
*spamApTask1: Apr 08 18:51:27.726: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:28.452: 00:b0:e1:88:99:80 Setting MTU to 1485
*apf80211vTask: Apr 08 18:51:28.679: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:28.680: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*apf80211vTask: Apr 08 18:51:29.285: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:29.286: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:30.202: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343090
*spamApTask1: Apr 08 18:51:30.203: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:30.301: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343090
*spamApTask2: Apr 08 18:51:30.301: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:31.302: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:32.750: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343092
*spamApTask1: Apr 08 18:51:32.750: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:33.066: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343093
*spamApTask1: Apr 08 18:51:33.066: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 DTLS connection closed event receivedserver (192.168.1.3/5246) client (192.168.1.247/5264)
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Entry exists for AP (192.168.1.247/5264)
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 AP Delete request
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 No AP entry exist in temporary database for 192.168.1.247:5264
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:35.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343095
*spamApTask2: Apr 08 18:51:35.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:36.486: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343096
*spamApTask1: Apr 08 18:51:36.486: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:37.286: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343097
*spamApTask1: Apr 08 18:51:37.286: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:37.722: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343097
*spamApTask1: Apr 08 18:51:37.722: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Join Priority Processing status = 0, Incoming Ap's Priority 1, MaxLrads = 200, MaxLicense=128 joined Aps =3
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Response sent to 192.168.1.247 port 5264
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Response sent to 192.168.1.247:5264
*spamApTask1: Apr 08 18:51:39.398: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343099
*spamApTask1: Apr 08 18:51:39.398: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:39.399: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343099
*spamApTask1: Apr 08 18:51:39.399: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:42.750: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343102
*spamApTask1: Apr 08 18:51:42.750: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:43.066: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343103
*spamApTask1: Apr 08 18:51:43.066: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 Primary Discovery Request from 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 Primary Discovery Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:45.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343105
*spamApTask2: Apr 08 18:51:45.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Request from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Request from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.486: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343106
*spamApTask1: Apr 08 18:51:46.486: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:47.286: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343107
*spamApTask1: Apr 08 18:51:47.286: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:47.613: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.613: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:47.721: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343107
*spamApTask1: Apr 08 18:51:47.722: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.781: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.781: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:48.423: 00:b0:e1:88:0c:c0 DTLS connection not found, creating new connection for 192.168.1.247 (5264) 192.168.1.3 (5246)
*spamApTask2: Apr 08 18:51:48.445: 00:b0:e1:88:0c:c0 DTLS Session established server (192.168.1.3:5246), client (192.168.1.247:5264)
*spamApTask2: Apr 08 18:51:48.445: 00:b0:e1:88:0c:c0 Starting wait join timer for AP: 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Join Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Allocate database entry for AP 192.168.1.247:5264, already allocated index 65535
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 AP Allocate request at index 77 (local)
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:0c:c0 Deleting AP entry 192.168.1.247:5264 from temporary database.
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Dropping request or response packet to AP :192.168.1.247 (5264) by Controller: 192.168.1.3 (5246), message Capwap_wtp_event_response, state Capwap_no_state
*spamApTask2: Apr 08 18:51:48.466: 00:b0:e1:88:99:80 Message type Capwap_wtp_event_response is not allowed to send in state Capwap_no_state for AP 192.168.1.247
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join Version: = 134586624
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join resp: CAPWAP Maximum Msg element len = 81
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join Response sent to 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 CAPWAP State: Join
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 capwap_ac_platform.c:2076 - Operation State 0 ===> 4
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 SSID LEDE_FT is not advertised on AP for radio 802.11B due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 SSID LEDE_2.4G is not advertised on AP for radio 802.11A due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.479: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.479: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.479: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*apf80211vTask: Apr 08 18:51:48.508: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:48.509: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:49.149: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.149: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.394: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.394: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.395: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.395: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.396: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.396: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:52.749: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343112
*spamApTask1: Apr 08 18:51:52.749: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:53.065: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343113
*spamApTask1: Apr 08 18:51:53.065: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:54.209: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343114
*spamApTask1: Apr 08 18:51:54.209: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:54.288: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343114
*spamApTask2: Apr 08 18:51:54.288: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask2: Apr 08 18:51:55.572: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343115
*spamApTask2: Apr 08 18:51:55.572: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:56.485: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343116
*spamApTask1: Apr 08 18:51:56.485: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:57.285: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343117
*spamApTask1: Apr 08 18:51:57.285: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:57.721: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343117
*spamApTask1: Apr 08 18:51:57.721: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:52:00.138: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
*spamApTask1: Apr 08 18:52:00.138: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
OEAP1810的MAC是:00:b0:e1:88:0c:c0, IP地址是:192.168.1.247
(Cisco Controller) >debug capwap events enable
(Cisco Controller) >*spamApTask2: Apr 08 18:50:28.153: 00:b0:e1:88:99:80 Failed to parse CAPWAP packet from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:15.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343075
*spamApTask1: Apr 08 18:51:16.490: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343076
*spamApTask1: Apr 08 18:51:16.491: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:16.850: 00:b0:e1:88:0c:c0 DTLS connection not found, creating new connection for 192.168.1.247 (5264) 192.168.1.3 (5246)
*spamApTask2: Apr 08 18:51:16.878: 00:b0:e1:88:0c:c0 DTLS Session established server (192.168.1.3:5246), client (192.168.1.247:5264)
*spamApTask2: Apr 08 18:51:16.878: 00:b0:e1:88:0c:c0 Starting wait join timer for AP: 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 Join Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 Allocate database entry for AP 192.168.1.247:5264, already allocated index 65535
*spamApTask2: Apr 08 18:51:16.899: 00:b0:e1:88:99:80 AP Allocate request at index 76 (local)
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:0c:c0 Deleting AP entry 192.168.1.247:5264 from temporary database.
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:99:80 Dropping request or response packet to AP :192.168.1.247 (5264) by Controller: 192.168.1.3 (5246), message Capwap_wtp_event_response, state Capwap_no_state
*spamApTask2: Apr 08 18:51:16.900: 00:b0:e1:88:99:80 Message type Capwap_wtp_event_response is not allowed to send in state Capwap_no_state for AP 192.168.1.247
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join Version: = 134586624
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join resp: CAPWAP Maximum Msg element len = 81
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Join Response sent to 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 CAPWAP State: Join
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 capwap_ac_platform.c:2076 - Operation State 0 ===> 4
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*spamApTask2: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:16.919: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.919: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.919: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.919: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.919: 00:b0:e1:88:99:80 SSID LEDE_FT is not advertised on AP for radio 802.11B due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 SSID LEDE_2.4G is not advertised on AP for radio 802.11A due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:16.920: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.920: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.920: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:16.920: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:16.920: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:17.174: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:17.287: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343077
*spamApTask1: Apr 08 18:51:17.287: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:17.726: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343077
*spamApTask1: Apr 08 18:51:17.726: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:19.891: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask2: Apr 08 18:51:22.742: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:22.743: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:22.754: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343082
*spamApTask1: Apr 08 18:51:22.754: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:23.070: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343083
*spamApTask1: Apr 08 18:51:23.070: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*apf80211vTask: Apr 08 18:51:25.533: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:25.534: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:25.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343085
*spamApTask2: Apr 08 18:51:25.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:25.594: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:26.490: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343086
*spamApTask1: Apr 08 18:51:26.490: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:27.287: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343087
*spamApTask1: Apr 08 18:51:27.287: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:27.726: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343087
*spamApTask1: Apr 08 18:51:27.726: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:28.451: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:28.452: 00:b0:e1:88:99:80 Setting MTU to 1485
*apf80211vTask: Apr 08 18:51:28.679: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:28.680: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*apf80211vTask: Apr 08 18:51:29.285: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:29.286: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:30.202: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343090
*spamApTask1: Apr 08 18:51:30.203: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:30.301: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343090
*spamApTask2: Apr 08 18:51:30.301: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:31.301: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:31.302: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:32.750: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343092
*spamApTask1: Apr 08 18:51:32.750: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:33.066: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343093
*spamApTask1: Apr 08 18:51:33.066: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 DTLS connection closed event receivedserver (192.168.1.3/5246) client (192.168.1.247/5264)
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Entry exists for AP (192.168.1.247/5264)
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Capwap State Change Event (DeReg) from capwap_ac_sm.c 1787
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 apfSpamProcessStateChangeInSpamContext: Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 AP Delete request
*spamApTask2: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 No AP entry exist in temporary database for 192.168.1.247:5264
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:34.152: 00:b0:e1:88:99:80 Deregister LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*spamApTask2: Apr 08 18:51:35.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343095
*spamApTask2: Apr 08 18:51:35.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:36.486: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343096
*spamApTask1: Apr 08 18:51:36.486: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:37.286: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343097
*spamApTask1: Apr 08 18:51:37.286: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:37.722: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343097
*spamApTask1: Apr 08 18:51:37.722: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Join Priority Processing status = 0, Incoming Ap's Priority 1, MaxLrads = 200, MaxLicense=128 joined Aps =3
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Response sent to 192.168.1.247 port 5264
*spamApTask2: Apr 08 18:51:39.035: 00:b0:e1:88:99:80 Discovery Response sent to 192.168.1.247:5264
*spamApTask1: Apr 08 18:51:39.398: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343099
*spamApTask1: Apr 08 18:51:39.398: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:39.399: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343099
*spamApTask1: Apr 08 18:51:39.399: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:42.750: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343102
*spamApTask1: Apr 08 18:51:42.750: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:43.066: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343103
*spamApTask1: Apr 08 18:51:43.066: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 Primary Discovery Request from 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:44.102: 88:75:56:1f:76:10 Primary Discovery Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:45.573: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343105
*spamApTask2: Apr 08 18:51:45.573: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Request from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Request from 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType = 25 apModel: AIR-CAP3602I-A-K9
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 apType: Ox19 bundleApImageVer: 8.5.161.0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 version:8 release:5 maint:161 build:0
*spamApTask1: Apr 08 18:51:46.154: 34:bd:c8:bf:54:20 Primary Discovery Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:46.486: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343106
*spamApTask1: Apr 08 18:51:46.486: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:47.286: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343107
*spamApTask1: Apr 08 18:51:47.286: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:47.613: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.613: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.614: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:47.721: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343107
*spamApTask1: Apr 08 18:51:47.722: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.780: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:47.781: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343107
*spamApTask2: Apr 08 18:51:47.781: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:48.423: 00:b0:e1:88:0c:c0 DTLS connection not found, creating new connection for 192.168.1.247 (5264) 192.168.1.3 (5246)
*spamApTask2: Apr 08 18:51:48.445: 00:b0:e1:88:0c:c0 DTLS Session established server (192.168.1.3:5246), client (192.168.1.247:5264)
*spamApTask2: Apr 08 18:51:48.445: 00:b0:e1:88:0c:c0 Starting wait join timer for AP: 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Join Request from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Allocate database entry for AP 192.168.1.247:5264, already allocated index 65535
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 AP Allocate request at index 77 (local)
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:0c:c0 Deleting AP entry 192.168.1.247:5264 from temporary database.
*spamApTask2: Apr 08 18:51:48.465: 00:b0:e1:88:99:80 Dropping request or response packet to AP :192.168.1.247 (5264) by Controller: 192.168.1.3 (5246), message Capwap_wtp_event_response, state Capwap_no_state
*spamApTask2: Apr 08 18:51:48.466: 00:b0:e1:88:99:80 Message type Capwap_wtp_event_response is not allowed to send in state Capwap_no_state for AP 192.168.1.247
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join Version: = 134586624
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 apType = 63 apModel: AIR-OEAP1810-B-K9
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 apType: Ox3f bundleApImageVer: 8.5.161.0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 version:8 release:5 maint:161 build:0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join resp: CAPWAP Maximum Msg element len = 81
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Join Response sent to 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 CAPWAP State: Join
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 capwap_ac_platform.c:2076 - Operation State 0 ===> 4
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 0
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*spamApTask2: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Capwap State Change Event (Reg) from capwap_ac_platform.c 2117
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 SSID LEDE_FT is not advertised on AP for radio 802.11B due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 1
*apfReceiveTask: Apr 08 18:51:48.478: 00:b0:e1:88:99:80 SSID LEDE_2.4G is not advertised on AP for radio 802.11A due to the radio policy of the WLAN.
*apfReceiveTask: Apr 08 18:51:48.478: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.478: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.479: WARP IEs: (12)
*apfReceiveTask: Apr 08 18:51:48.479: [0000] dd 0a 00 c0 b9 01 00 00 00 08 01 01
*apfReceiveTask: Apr 08 18:51:48.479: 00:b0:e1:88:99:80 Register LWAPP event for AP 00:b0:e1:88:99:80 slot 2
*apf80211vTask: Apr 08 18:51:48.508: 34:bd:c8:bf:54:20 Configuration update request for DMS Sent To34:bd:c8:bf:54:20
*spamApTask1: Apr 08 18:51:48.509: 34:bd:c8:bf:54:20 Configuration Update Response from 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:48.721: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:49.149: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.149: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.150: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.394: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.394: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.395: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.395: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:49.396: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343109
*spamApTask1: Apr 08 18:51:49.396: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:51.469: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:52.749: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343112
*spamApTask1: Apr 08 18:51:52.749: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:53.065: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343113
*spamApTask1: Apr 08 18:51:53.065: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:51:54.209: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343114
*spamApTask1: Apr 08 18:51:54.209: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask2: Apr 08 18:51:54.288: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343114
*spamApTask2: Apr 08 18:51:54.288: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:54.321: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask2: Apr 08 18:51:55.572: 7c:95:f3:c0:3a:c0 WTP Event Request from 192.168.1.229:63353 epoch 1586343115
*spamApTask2: Apr 08 18:51:55.572: 7c:95:f3:c0:3a:c0 WTP Event Response sent to 192.168.1.229:63353
*spamApTask1: Apr 08 18:51:56.485: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343116
*spamApTask1: Apr 08 18:51:56.485: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:51:57.172: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:51:57.285: 34:bd:c8:bf:54:20 WTP Event Request from 192.168.1.214:57663 epoch 1586343117
*spamApTask1: Apr 08 18:51:57.285: 34:bd:c8:bf:54:20 WTP Event Response sent to 192.168.1.214:57663
*spamApTask1: Apr 08 18:51:57.721: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343117
*spamApTask1: Apr 08 18:51:57.721: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Configuration Status from 192.168.1.247:5264
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 CAPWAP State: Configure
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updating IP info for AP 00:b0:e1:88:99:80 -- static 0, 192.168.1.247/255.255.255.0, gtw 192.168.1.1
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updating IP 192.168.1.247 ===> 192.168.1.247 for AP 00:b0:e1:88:99:80
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Updated IP Domain info for AP 00:b0:e1:88:99:80 -- set 0, Domain
*spamApTask2: Apr 08 18:52:00.023: 00:b0:e1:88:99:80 Setting MTU to 1485
*spamApTask1: Apr 08 18:52:00.138: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
*spamApTask1: Apr 08 18:52:00.138: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Response sent to 192.168.1.188:61114
*spamApTask1: Apr 08 18:52:00.139: 88:75:56:1f:76:10 WTP Event Request from 192.168.1.188:61114 epoch 1586343120
debug dtls all enable的LOG
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL_state_string=SSLv3 read client key exchange A
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL state = 0x21a0; where = 0x2002; ret = 0xffffffff
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL_state_string=SSLv3 read certificate verify A
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 Handshake in progress... check for bufferred msgs
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 checkAndHandleBufferredMsgs called for con 0xa457078 in status 2
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 No pending Cert Verify in Client Key Exchange done state.
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Buffer length 285, alloc_len 289
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=Handshake epoch=0 seq=6
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 seq_num 6 epoch 0con->rx_seq 5 con->rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 5 rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg=CertificateVerify len=260 seq=4 frag_off=0 frag_len=260
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Rcvd CertificateVerify in connStatus 2
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Received CERTIFICATE_VERIFY in connStatus 2. processing...
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 CertificateVerify can be processed
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 local_openssl_dtls_handshake_replay_detection:
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg_seq:4,msg_len:260,frag_len:260,frag_off: 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Allow: CertificateVerify in status 3
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 272
*spamApTask2: Apr 08 18:55:29.869: 00000000: 16 fe fd 00 00 00 00 00 00 00 06 01 10 0f 00 01 ................
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 285
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21a0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read certificate verify A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21c0; where = 0x2002; ret = 0xffffffff
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read finished A
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Handshake in progress... check for bufferred msgs
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 checkAndHandleBufferredMsgs called for con 0xa457078 in status 3
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 No Change Cipher Spec pending Cert Verify done state.
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Buffer length 91, alloc_len 95
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=ChangeCipherSpec epoch=0 seq=7
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 seq_num 7 epoch 0con->rx_seq 6 con->rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 6 rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Got DTLS_RECORD_CHANGE_CIPHER_SPEC
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Received CHANGE_CIPHER_SPEC in connStatus 3. processing...
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS_RECORD_CHANGE_CIPHER_SPEC can be processed
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=Handshake epoch=1 seq=0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 updated con with rx_seq_valid 255 rx_seq 0 rx_epoch 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg=Unknown or Encrypted
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 64
*spamApTask2: Apr 08 18:55:29.869: 00000000: 14 fe fd 00 00 00 00 00 00 00 07 00 01 01 16 fe ................
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 91
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21c0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read finished A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21d0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 write change cipher spec A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21e0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 write finished A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x2100; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSLv3 flush data
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL state = 0x3; where = 0x20; ret = 0x1
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSL negotiation finished successfully
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL state = 0x3; where = 0x2002; ret = 0x1
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSL negotiation finished successfully
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Connection established!
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 reset/free pending message buffers
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS Connection 0xa457078 established
*spamApTask2: Apr 08 18:55:29.870: openssl_dtls_mtu_update: Called...
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Setting DTLS MTU for link to peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Sending 91 bytes
*spamApTask2: Apr 08 18:55:29.870: 00000000: 14 fe fd 00 00 00 00 00 00 00 0a 00 01 01 16 fe ................
*spamApTask2: Apr 08 18:55:29.870: 00000010: fd 00 01 00 00 00 00 00 00 00 40 e7 ce a9 ca 4c ..........@....L
*spamApTask2: Apr 08 18:55:29.870: 00000020: c2 8b ca 2e 70 ea ba 61 43 76 43 3c 2c 27 6c 52 ....p..aCvC<,'lR
*spamApTask2: Apr 08 18:55:29.870: 00000030: 6a bf f9 1c 32 97 93 e5 de 50 0b 15 59 4c 35 bf j...2....P..YL5.
*spamApTask2: Apr 08 18:55:29.870: 00000040: 95 e8 7a dc f9 fd 92 f5 c1 8e 05 35 86 23 d1 01 ..z........5.#..
*spamApTask2: Apr 08 18:55:29.870: 00000050: cb 11 03 a4 6f fb be 73 7d ba d6 ....o..s}..
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.870: __dtls_timer_stop: Called...
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Buffer length 1437, alloc_len 1441
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 record=ApplicationData epoch=1 seq=1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 handshake_done
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 seq_num 1 epoch 1con->rx_seq 0 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 0 rx_epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 record length 1424
*spamApTask2: Apr 08 18:55:29.894: 00000000: 17 fe fd 00 01 00 00 00 00 00 01 05 90 8a 62 ac ..............b.
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 1437
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 1384 bytes decrypted
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 Called...
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Sending 1453 bytes
*spamApTask2: Apr 08 18:55:29.920: 00000000: 17 fe fd 00 01 00 00 00 00 00 01 05 a0 2b e2 29 .............+.)
*spamApTask2: Apr 08 18:55:29.920: 00000010: 3c 54 be 9c d8 5c af 5c df f3 85 a4 a8 3f 21 e8
*spamApTask2: Apr 08 18:55:29.920: 00000030: 50 25 14 f2 87 9a bc 92 29 2a 2f 48 5a 56 45 e0 P%......)*/HZVE.
*spamApTask2: Apr 08 18:55:29.920: 00000040: 96 dd a7 7b 47 0d d8 42 76 8c b4 05 87 5b 04 59 ...{G..Bv....[.Y
*spamApTask2: Apr 08 18:55:29.920: 00000050: c2 fc 00 5e 49 3c a1 95 ab 87 4e 4d fa c5 c1 e3 ...^I<....NM....
*spamApTask2: Apr 08 18:55:29.920: 00000060: 16 eb 86 f2 06 de 54 50 a9 66 aa 07 32 52 3b ca ......TP.f..2R;.
*spamApTask2: Apr 08 18:55:29.920: 00000070: fb 76 11 4b cb 93 30 b6 5c fa 80 d9 3a 14 69 0a .v.K..0.\...:.i.
*spamApTask2: Apr 08 18:55:29.920: 00000080: bf c2 d3 ac 8a 23 8a 43 14 f2 e6 ac 5e e4 3d f3 .....#.C....^.=.
*spamApTask2: Apr 08 18:55:29.920: 00000090: ed 81 77 ad d5 95 c9 8d a4 a6 20 46 4c 88 d2 8a ..w........FL...
*spamApTask2: Apr 08 18:55:29.920: 000000a0: ae f0 83 ea 05 e9 6c 9a b8 41 a3 d7 cf 66 92 b0 ......l..A...f..
*spamApTask2: Apr 08 18:55:29.920: 000000b0: 54 6c 8c 19 6b 8c 35 ba 30 33 e9 ea c4 16 f6 a2 Tl..k.5.03......
*spamApTask2: Apr 08 18:55:29.920: 000000c0: da 8e 38 a3 fc 72 17 4a 55 f9 19 62 f2 6a 4c 75 ..8..r.JU..b.jLu
*spamApTask2: Apr 08 18:55:29.920: 000000d0: 36 39 b7 11 39 71 d4 18 09 5f 00 99 10 67 07 a3 69..9q..._...g..
*spamApTask2: Apr 08 18:55:29.920: 000000e0: 27 4d b5 8d aa eb dd 4f 54 2a bc 27 52 3d d9 25 'M.....OT*.'R=.%
*spamApTask2: Apr 08 18:55:29.920: 000000f0: 70 63 e8 fb 4b 17 c5 84 b0 79 e2 0d 31 bc 36 3b pc..K....y..1.6;
*spamApTask2: Apr 08 18:55:29.920: 00000100: 75 a7 6e 9a 6c 7d 6c d4 9c 3e 0f 98 56 6b af 0a u.n.l}l..>..Vk..
*spamApTask2: Apr 08 18:55:29.920: 00000110: c4 46 d2 64 fe fb 26 d7 c1 9c 08 a1 e0 a6 04 81 .F.d..&.........
*spamApTask2: Apr 08 18:55:29.920: 00000120: fd 01 5e 0e d1 7e fa f5 b3 6d c8 6a ba c7 53 dd ..^..~...m.j..S.
*spamApTask2: Apr 08 18:55:29.920: 00000130: 11 a4 66 96 51 36 ce c5 9e 88 57 cd 90 6a 3b d8 ..f.Q6....W..j;.
*spamApTask2: Apr 08 18:55:29.920: 00000140: af 17 1e ab 96 9c 07 95 54 ed 51 0c 60 5e 9f 0b ........T.Q.`^..
*spamApTask2: Apr 08 18:55:29.920: 00000150: 0f c6 a5 a1 3d 8f 00 fd a4 38 23 88 3d e5 d9 31 ....=....8#.=..1
*spamApTask2: Apr 08 18:55:29.920: 00000160: c8 05 ee d2 46 ab 25 20 ea c2 a0 36 9e 53 c2 c1 ....F.%....6.S..
*spamApTask2: Apr 08 18:55:29.920: 00000170: 90 b7 15 ae 42 91 b6 85 77 55 8d 15 eb 97 3a 29 ....B...wU....:)
*spamApTask2: Apr 08 18:55:29.920: 00000180: e8 12 8b fe 75 6c c1 1b 4d e6 1f e4 f6 98 34 69 ....ul..M.....4i
*spamApTask2: Apr 08 18:55:29.920: 00000190: 03 72 ec 7f 46 02 0c 99 df ee f9 c3 17 b2 b7 bd .r..F...........
*spamApTask2: Apr 08 18:55:29.920: 000001a0: f0 cf 88 88 4d ec 4a d8 dd 6a 87 6a d1 ff 14 94 ....M.J..j.j....
*spamApTask2: Apr 08 18:55:29.920: 000001b0: fb b1 8a 24 e2 5c e4 2c ab 4d 64 ff 22 f6 f8 bc ...$.\.,.Md."...
*spamApTask2: Apr 08 18:55:29.920: 000001c0: 51 aa 04 6d 6b 95 5d cd 1e 6f 53 00 01 93 3a 75 Q..mk.]..oS...:u
*spamApTask2: Apr 08 18:55:29.920: 000001d0: 70 b3 05 bb c5 a6 f0 97 17 fd e9 35 45 a6 6e 42 p..........5E.nB
*spamApTask2: Apr 08 18:55:29.920: 000001e0: e3 cd 90 8b c2 84 dd 34 33 2a c7 72 11 74 a3 3d .......43*.r.t.=
*spamApTask2: Apr 08 18:55:29.920: 000001f0: e2 b6 28 f0 e4 23 0e 85 dd fa fc d2 4e d1 fc 9a ..(..#......N...
*spamApTask2: Apr 08 18:55:29.920: 00000200: c0 a0 c1 0c 3c 69 36 90 7d 17 ef 61 72 63 3b b1 ....
*spamApTask2: Apr 08 18:55:29.920: 00000220: 18 01 79 41 7a 88 4b c2 0f 2b 72 88 91 74 f6 5e ..yAz.K..+r..t.^
*spamApTask2: Apr 08 18:55:29.920: 00000230: 40 46 88 39 dc ca bf b3 3f a0 ef d5 c1 b3 32 51 @F.9....?.....2Q
*spamApTask2: Apr 08 18:55:29.920: 00000240: ff e1 33 84 97 26 f5 69 f5 fd 5f bd d7 df 16 e5 ..3..&.i.._.....
*spamApTask2: Apr 08 18:55:29.920: 00000250: 0c aa 6b 26 1f 50 77 ec 4d 26 03 97 1c b2 32 ae ..k&.Pw.M&....2.
*spamApTask2: Apr 08 18:55:29.920: 00000260: de 16 6c ef b3 b6 06 92 95 81 45 fc 39 ff 2f e8 ..l.......E.9./.
*spamApTask2: Apr 08 18:55:29.920: 00000270: 91 a4 cf 3c 71 99 ec 9b 0c b7 67 2b 61 d8 ba a7 ...
*spamApTask2: Apr 08 18:55:29.920: 00000290: 8f 02 e5 72 98 48 3a 6b 24 44 17 68 2c e5 e0 37 ...r.H:k$D.h,..7
*spamApTask2: Apr 08 18:55:29.920: 000002a0: 59 17 c3 f5 a2 ac 81 ee 5d d6 3c 4f 16 3e a6 45 Y.......]..E
*spamApTask2: Apr 08 18:55:29.920: 000002b0: a7 9f 63 c4 a5 e3 61 71 bb d5 7e cd d7 73 2e 0f ..c...aq..~..s..
*spamApTask2: Apr 08 18:55:29.920: 000002c0: 1d 44 03 52 33 29 05 42 dc 5e 09 70 05 19 bd 70 .D.R3).B.^.p...p
*spamApTask2: Apr 08 18:55:29.920: 000002d0: 3b 30 c8 1c bd cf a5 a9 85 95 b3 f3 d5 f8 85 32 ;0.............2
*spamApTask2: Apr 08 18:55:29.920: 000002e0: 55 87 63 99 7b 00 51 0a c2 9b 42 08 05 c9 d4 20 U.c.{.Q...B.....
*spamApTask2: Apr 08 18:55:29.920: 000002f0: e9 87 c7 86 49 57 68 89 3b 74 4a e2 3e db e9 0b ....IWh.;tJ.>...
*spamApTask2: Apr 08 18:55:29.920: 00000300: 5a b2 86 90 8b b7 39 e2 f9 8d 18 59 bd 4a 5c d1 Z.....9....Y.J\.
*spamApTask2: Apr 08 18:55:29.920: 00000310: 56 25 43 97 c3 a3 51 38 80 f3 89 21 e5 31 22 cb V%C...Q8...!.1".
*spamApTask2: Apr 08 18:55:29.920: 00000320: e4 e3 3b 62 07 61 88 78 ed e0 a5 00 7e 6f 1a 7e ..;b.a.x....~o.~
*spamApTask2: Apr 08 18:55:29.920: 00000330: 46 16 b4 1a e8 9c c2 bc 93 15 e5 95 ef 86 af 0a F...............
*spamApTask2: Apr 08 18:55:29.920: 00000340: 8d 85 d2 8c ad 2d 3b 13 fe 80 d9 78 cc 53 0f d2 .....-;....x.S..
*spamApTask2: Apr 08 18:55:29.920: 00000350: fc 08 a6 8a 93 54 0d 0e 2d f9 3e d9 d4 c8 b6 30 .....T..-.>....0
*spamApTask2: Apr 08 18:55:29.920: 00000360: 5e 3a 9f e8 21 77 78 e6 99 01 10 6e 43 f7 7c 90 ^:..!wx....nC.|.
*spamApTask2: Apr 08 18:55:29.920: 00000370: 55 36 f8 c3 6a 9e 7d 0b f7 95 8d d8 7c d0 66 62 U6..j.}.....|.fb
*spamApTask2: Apr 08 18:55:29.920: 00000380: 18 d4 25 5f 7b 65 3a c2 84 0f 80 9f 41 d9 da e5 ..%_{e:.....A...
*spamApTask2: Apr 08 18:55:29.920: 00000390: 99 dd fc 05 3b 7d 3f 33 cb 87 1b fa 4c d2 e9 f7 ....;}?3....L...
*spamApTask2: Apr 08 18:55:29.920: 000003a0: d1 f0 de b0 3b 29 df fb 3f d8 02 14 c9 bf 20 00 ....;)..?.......
*spamApTask2: Apr 08 18:55:29.920: 000003b0: 79 7e 4c 54 1f df e5 29 73 5c 31 9d 49 4a 8d 01 y~LT...)s\1.IJ..
*spamApTask2: Apr 08 18:55:29.920: 000003c0: 17 df 07 87 94 17 ff 69 25 59 18 0f a6 2d da 1f .......i%Y...-..
*spamApTask2: Apr 08 18:55:29.920: 000003d0: e4 ce 8c c1 f6 4a 45 d1 2d ec 48 f2 09 04 28 d0 .....JE.-.H...(.
*spamApTask2: Apr 08 18:55:29.920: 000003e0: 83 d5 b9 a8 86 71 af bf 49 c6 51 ce 63 9b ea 5a .....q..I.Q.c..Z
*spamApTask2: Apr 08 18:55:29.920: 000003f0: 5d 22 c6 f2 f3 88 65 77 55 64 1f e7 67 5d 97 7c ]"....ewUd..g].|
*spamApTask2: Apr 08 18:55:29.920: 00000400: 13 47 d6 2d 3f ce 7b d0 1d 71 26 30 a8 75 f7 0c .G.-?.{..q&0.u..
*spamApTask2: Apr 08 18:55:29.920: 00000410: 52 10 f9 c2 ee 8f 14 f5 e3 01 7d 0b a8 d2 39 7c R.........}...9|
*spamApTask2: Apr 08 18:55:29.920: 00000420: 84 1b 51 92 53 41 86 66 e5 63 26 00 92 f7 76 2f ..Q.SA.f.c&...v/
*spamApTask2: Apr 08 18:55:29.920: 00000430: d6 7f 60 ba d0 0a 9d c2 8e 85 72 95 02 4e c9 c5 ..`.......r..N..
*spamApTask2: Apr 08 18:55:29.920: 00000440: 1d 38 fc 96 4a 07 ff 33 d7 c4 2f 6b 7f 76 33 95 .8..J..3../k.v3.
*spamApTask2: Apr 08 18:55:29.920: 00000450: ab 5a f4 29 23 3e 59 8c a8 e8 86 52 9d fd af f4 .Z.)#>Y....R....
*spamApTask2: Apr 08 18:55:29.920: 00000460: 0c 47 50 92 3b 69 e7 52 26 20 65 35 f6 60 22 a4 .GP.;i.R&.e5.`".
*spamApTask2: Apr 08 18:55:29.920: 00000470: 68 2d e8 a0 9a 84 00 c4 76 99 22 78 f3 cc 58 07 h-......v."x..X.
*spamApTask2: Apr 08 18:55:29.920: 00000480: 64 59 ba f9 d3 2a a5 1b ed 66 cb d4 cf 55 fa 6e dY...*...f...U.n
*spamApTask2: Apr 08 18:55:29.920: 00000490: e3 69 87 2b 38 f1 0a e2 82 b5 cd 80 aa 85 ff 16 .i.+8...........
*spamApTask2: Apr 08 18:55:29.920: 000004a0: 16 71 75 21 e4 33 6b cb 9d 84 db e3 12 68 e0 6f .qu!.3k......h.o
*spamApTask2: Apr 08 18:55:29.920: 000004b0: 76 78 a6 12 45 e2 7a cc 5a 22 d7 40 30 13 69 cc vx..E.z.Z".@0.i.
*spamApTask2: Apr 08 18:55:29.920: 000004c0: 2e cb c4 e1 47 ef 27 45 16 28 53 60 56 e9 fd 44 ....G.'E.(S`V..D
*spamApTask2: Apr 08 18:55:29.920: 000004d0: e9 0e bf d8 d1 79 7e 14 68 f9 3b 4a 40 5d cf b1 .....y~.h.;J@]..
*spamApTask2: Apr 08 18:55:29.920: 000004e0: d5 d8 c7 a9 a8 ec 1c 3f 8f f6 09 19 be d0 b4 a5 .......?........
*spamApTask2: Apr 08 18:55:29.920: 000004f0: a8 9c 6d 2f 5a 3f 51 01 d1 af 7c 37 01 92 c7 8a ..m/Z?Q...|7....
*spamApTask2: Apr 08 18:55:29.920: 00000500: 54 3e 7e fa 78 95 30 d5 36 0e 69 72 b9 d5 ca 09 T>~.x.0.6.ir....
*spamApTask2: Apr 08 18:55:29.920: 00000510: 61 46 c6 46 1a 9f 2b 93 64 1b c0 52 0c 09 d4 e1 aF.F..+.d..R....
*spamApTask2: Apr 08 18:55:29.920: 00000520: 4b c8 05 6c 78 d1 bc e7 3b 14 51 bb 42 36 f5 c9 K..lx...;.Q.B6..
*spamApTask2: Apr 08 18:55:29.920: 00000530: 34 f9 22 12 6d 1a e7 3b c4 1c 9b 92 5d a3 3f ce 4.".m..;....].?.
*spamApTask2: Apr 08 18:55:29.920: 00000540: 0b be ad fb 3d 8d cd ac b2 d7 da ec 75 2f 2f 13 ....=.......u//.
*spamApTask2: Apr 08 18:55:29.920: 00000550: 2c 99 fe b2 c9 33 82 d5 c3 1f dd c6 b2 c5 39 73 ,....3........9s
*spamApTask2: Apr 08 18:55:29.920: 00000560: 50 9f 60 47 e1 10 3e 79 2c d9 9e b1 27 60 33 52 P.`G..>y,...'`3R
*spamApTask2: Apr 08 18:55:29.920: 00000570: c1 51 fe 0f 2f a6 56 d7 0d 64 38 02 62 a8 ca 41 .Q../.V..d8.b..A
*spamApTask2: Apr 08 18:55:29.920: 00000580: 3c 6c 50 8c 4d b9 b1 68 32 b2 80 16 25 62 02 1e
*spamApTask2: Apr 08 18:55:29.920: 000005a0: 12 90 dc ea 99 fe cd 9f 09 82 64 03 77 ..........d.w
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 No data to send
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Buffer length 1405, alloc_len 1409
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=2
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 seq_num 2 epoch 1con->rx_seq 1 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 1 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record length 1392
*spamApTask2: Apr 08 18:55:30.160: 00000000: 17 fe fd 00 01 00 00 00 00 00 02 05 70 53 44 9a ............pSD.
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1405
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 1352 bytes decrypted
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Buffer length 1357, alloc_len 1361
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=3
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 seq_num 3 epoch 1con->rx_seq 2 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 2 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record length 1344
*spamApTask2: Apr 08 18:55:30.160: 00000000: 17 fe fd 00 01 00 00 00 00 00 03 05 40 05 b1 a7 ............@...
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1357
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 1295 bytes decrypted
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.214:57663
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection found! Acquiring lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Called... for connection 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Buffer length 93, alloc_len 97
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 record=ApplicationData epoch=1 seq=14307
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 handshake_done
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 seq_num 14307 epoch 1con->rx_seq 14306 con->rx_epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 con rx_seq_valid 255 rx_seq 14306 rx_epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 record length 80
*spamApTask1: Apr 08 18:55:30.187: 00000000: 17 fe ff 00 01 00 00 00 00 37 e3 00 50 42 cf 76 .........7..PB.v
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Calling BIO_write! 0xa44b730, buflen 93
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 38 bytes decrypted
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Releasing lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.214:57663
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection found! Acquiring lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Called...
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Sending 77 bytes
*spamApTask1: Apr 08 18:55:30.187: 00000000: 17 fe ff 00 01 00 00 00 00 32 5d 00 40 8f e5 53 .........2].@..S
*spamApTask1: Apr 08 18:55:30.187: 00000010: 89 cf f9 aa 98 e1 0a 28 f8 dc 95 ed b4 83 87 3e .......(.......>
*spamApTask1: Apr 08 18:55:30.187: 00000020: 11 6e 31 3a 0c 18 a8 f7 fd 0f 6c de 10 85 5f d0 .n1:......l..._.
*spamApTask1: Apr 08 18:55:30.187: 00000030: bd 04 e9 7e 9e 88 f6 49 c5 bf 55 bb f7 f1 f4 b9 ...~...I..U.....
*spamApTask1: Apr 08 18:55:30.187: 00000040: 4c c7 35 3a bf 48 14 5c 28 f2 d6 04 ef L.5:.H.\(....
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 No data to send
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Releasing lock for 0xa44b730
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.229:63353
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection found! Acquiring lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Called... for connection 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Buffer length 93, alloc_len 97
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 record=ApplicationData epoch=1 seq=22926
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 handshake_done
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 seq_num 22926 epoch 1con->rx_seq 22925 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 con rx_seq_valid 255 rx_seq 22925 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 record length 80
*spamApTask2: Apr 08 18:55:30.295: 00000000: 17 fe ff 00 01 00 00 00 00 59 8e 00 50 28 ba e7 .........Y..P(..
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Calling BIO_write! 0xa44b4c8, buflen 93
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 38 bytes decrypted
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Releasing lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.229:63353
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection found! Acquiring lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Called...
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Sending 77 bytes
*spamApTask2: Apr 08 18:55:30.295: 00000000: 17 fe ff 00 01 00 00 00 00 54 09 00 40 ac 0b 58 .........T..@..X
*spamApTask2: Apr 08 18:55:30.295: 00000010: fd 18 4d 51 f3 13 92 85 47 ed 3f 8a 8f 6c 01 34 ..MQ....G.?..l.4
*spamApTask2: Apr 08 18:55:30.295: 00000020: 81 5e 84 11 82 67 08 1f 50 15 6e 97 02 07 d1 03 .^...g..P.n.....
*spamApTask2: Apr 08 18:55:30.295: 00000030: fa 08 18 a7 cd 57 19 bf f1 6a 2c 93 2c f2 ce a4 .....W...j,.,...
*spamApTask2: Apr 08 18:55:30.295: 00000040: 59 30 f3 57 86 0a 45 26 06 6c 44 f8 25 Y0.W..E&.lD.%
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 No data to send
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Releasing lock for 0xa44b4c8
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection found! Acquiring lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Called... for connection 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Buffer length 109, alloc_len 113
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 record=ApplicationData epoch=1 seq=26003
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 handshake_done
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 seq_num 26003 epoch 1con->rx_seq 26002 con->rx_epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 con rx_seq_valid 255 rx_seq 26002 rx_epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 record length 96
*spamApTask1: Apr 08 18:55:32.739: 00000000: 17 fe ff 00 01 00 00 00 00 65 93 00 60 9c ee d2 .........e..`...
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Calling BIO_write! 0xa44ad90, buflen 109
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 47 bytes decrypted
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Releasing lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection found! Acquiring lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Called...
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Sending 77 bytes
*spamApTask1: Apr 08 18:55:32.739: 00000000: 17 fe ff 00 01 00 00 00 00 5d 45 00 40 71 04 53 .........]E.@q.S
*spamApTask1: Apr 08 18:55:32.739: 00000010: be 67 20 75 cf 11 8d 6b 8e c1 3f 34 e3 13 fb d9 .g.u...k..?4....
*spamApTask1: Apr 08 18:55:32.739: 00000020: b5 c4 55 a4 06 ed 4c c6 1a 67 31 44 50 21 75 24 ..U...L..g1DP!u$
*spamApTask1: Apr 08 18:55:32.739: 00000030: a2 af bf 1c 1b 4f d6 0e 09 f8 9f 3a 62 c6 70 93 .....O.....:b.p.
*spamApTask1: Apr 08 18:55:32.739: 00000040: d1 ae f2 37 f7 b0 53 db ff 41 74 45 d0 ...7..S..AtE.
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 No data to send
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Releasing lock for 0xa44ad90
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Buffer length 1405, alloc_len 1409
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=4
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 seq_num 4 epoch 1con->rx_seq 3 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 3 rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record length 1392
*spamApTask2: Apr 08 18:55:32.882: 00000000: 17 fe fd 00 01 00 00 00 00 00 04 05 70 fa b1 c2 ............p...
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1405
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 1352 bytes decrypted
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Buffer length 1357, alloc_len 1361
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=5
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 seq_num 5 epoch 1con->rx_seq 4 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 4 rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record length 1344
*spamApTask2: Apr 08 18:55:32.882: 00000000: 17 fe fd 00 01 00 00 00 00 00 05 05 40 23 bb 50 ............@#.P
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1357
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 1295 bytes decrypted
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask1: Apr 08 18:55:33.055: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL_state_string=SSLv3 read client key exchange A
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL state = 0x21a0; where = 0x2002; ret = 0xffffffff
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: SSL_state_string=SSLv3 read certificate verify A
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 Handshake in progress... check for bufferred msgs
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 checkAndHandleBufferredMsgs called for con 0xa457078 in status 2
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 No pending Cert Verify in Client Key Exchange done state.
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.856: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Buffer length 285, alloc_len 289
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=Handshake epoch=0 seq=6
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 seq_num 6 epoch 0con->rx_seq 5 con->rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 5 rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg=CertificateVerify len=260 seq=4 frag_off=0 frag_len=260
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Rcvd CertificateVerify in connStatus 2
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Received CERTIFICATE_VERIFY in connStatus 2. processing...
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 CertificateVerify can be processed
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 local_openssl_dtls_handshake_replay_detection:
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg_seq:4,msg_len:260,frag_len:260,frag_off: 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Allow: CertificateVerify in status 3
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 272
*spamApTask2: Apr 08 18:55:29.869: 00000000: 16 fe fd 00 00 00 00 00 00 00 06 01 10 0f 00 01 ................
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 285
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21a0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read certificate verify A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21c0; where = 0x2002; ret = 0xffffffff
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read finished A
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Handshake in progress... check for bufferred msgs
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 checkAndHandleBufferredMsgs called for con 0xa457078 in status 3
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 No Change Cipher Spec pending Cert Verify done state.
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Buffer length 91, alloc_len 95
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=ChangeCipherSpec epoch=0 seq=7
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 seq_num 7 epoch 0con->rx_seq 6 con->rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 6 rx_epoch 0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Got DTLS_RECORD_CHANGE_CIPHER_SPEC
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Received CHANGE_CIPHER_SPEC in connStatus 3. processing...
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 DTLS_RECORD_CHANGE_CIPHER_SPEC can be processed
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record=Handshake epoch=1 seq=0
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 0 epoch 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 updated con with rx_seq_valid 255 rx_seq 0 rx_epoch 1
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 msg=Unknown or Encrypted
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 record length 64
*spamApTask2: Apr 08 18:55:29.869: 00000000: 14 fe fd 00 00 00 00 00 00 00 07 00 01 01 16 fe ................
*spamApTask2: Apr 08 18:55:29.869: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 91
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21c0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 read finished A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21d0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 write change cipher spec A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x21e0; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL_state_string=SSLv3 write finished A
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: SSL state = 0x2100; where = 0x2001; ret = 0x1
*spamApTask2: Apr 08 18:55:29.869: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSLv3 flush data
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL state = 0x3; where = 0x20; ret = 0x1
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSL negotiation finished successfully
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL state = 0x3; where = 0x2002; ret = 0x1
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_type_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: ret_desc_string=unknown
*spamApTask2: Apr 08 18:55:29.870: openssl_shim_info_callback: SSL_state_string=SSL negotiation finished successfully
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Connection established!
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 reset/free pending message buffers
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS Connection 0xa457078 established
*spamApTask2: Apr 08 18:55:29.870: openssl_dtls_mtu_update: Called...
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Setting DTLS MTU for link to peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Sending 91 bytes
*spamApTask2: Apr 08 18:55:29.870: 00000000: 14 fe fd 00 00 00 00 00 00 00 0a 00 01 01 16 fe ................
*spamApTask2: Apr 08 18:55:29.870: 00000010: fd 00 01 00 00 00 00 00 00 00 40 e7 ce a9 ca 4c ..........@....L
*spamApTask2: Apr 08 18:55:29.870: 00000020: c2 8b ca 2e 70 ea ba 61 43 76 43 3c 2c 27 6c 52 ....p..aCvC<,'lR
*spamApTask2: Apr 08 18:55:29.870: 00000030: 6a bf f9 1c 32 97 93 e5 de 50 0b 15 59 4c 35 bf j...2....P..YL5.
*spamApTask2: Apr 08 18:55:29.870: 00000040: 95 e8 7a dc f9 fd 92 f5 c1 8e 05 35 86 23 d1 01 ..z........5.#..
*spamApTask2: Apr 08 18:55:29.870: 00000050: cb 11 03 a4 6f fb be 73 7d ba d6 ....o..s}..
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 No data to send
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.870: __dtls_timer_stop: Called...
*spamApTask2: Apr 08 18:55:29.870: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Buffer length 1437, alloc_len 1441
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 record=ApplicationData epoch=1 seq=1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 handshake_done
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 seq_num 1 epoch 1con->rx_seq 0 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 con rx_seq_valid 255 rx_seq 0 rx_epoch 1
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 record length 1424
*spamApTask2: Apr 08 18:55:29.894: 00000000: 17 fe fd 00 01 00 00 00 00 00 01 05 90 8a 62 ac ..............b.
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Calling BIO_write! 0xa457078, buflen 1437
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 1384 bytes decrypted
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:0c:c0 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.894: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.919: 00:b0:e1:88:99:80 Called...
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Sending 1453 bytes
*spamApTask2: Apr 08 18:55:29.920: 00000000: 17 fe fd 00 01 00 00 00 00 00 01 05 a0 2b e2 29 .............+.)
*spamApTask2: Apr 08 18:55:29.920: 00000010: 3c 54 be 9c d8 5c af 5c df f3 85 a4 a8 3f 21 e8
*spamApTask2: Apr 08 18:55:29.920: 00000030: 50 25 14 f2 87 9a bc 92 29 2a 2f 48 5a 56 45 e0 P%......)*/HZVE.
*spamApTask2: Apr 08 18:55:29.920: 00000040: 96 dd a7 7b 47 0d d8 42 76 8c b4 05 87 5b 04 59 ...{G..Bv....[.Y
*spamApTask2: Apr 08 18:55:29.920: 00000050: c2 fc 00 5e 49 3c a1 95 ab 87 4e 4d fa c5 c1 e3 ...^I<....NM....
*spamApTask2: Apr 08 18:55:29.920: 00000060: 16 eb 86 f2 06 de 54 50 a9 66 aa 07 32 52 3b ca ......TP.f..2R;.
*spamApTask2: Apr 08 18:55:29.920: 00000070: fb 76 11 4b cb 93 30 b6 5c fa 80 d9 3a 14 69 0a .v.K..0.\...:.i.
*spamApTask2: Apr 08 18:55:29.920: 00000080: bf c2 d3 ac 8a 23 8a 43 14 f2 e6 ac 5e e4 3d f3 .....#.C....^.=.
*spamApTask2: Apr 08 18:55:29.920: 00000090: ed 81 77 ad d5 95 c9 8d a4 a6 20 46 4c 88 d2 8a ..w........FL...
*spamApTask2: Apr 08 18:55:29.920: 000000a0: ae f0 83 ea 05 e9 6c 9a b8 41 a3 d7 cf 66 92 b0 ......l..A...f..
*spamApTask2: Apr 08 18:55:29.920: 000000b0: 54 6c 8c 19 6b 8c 35 ba 30 33 e9 ea c4 16 f6 a2 Tl..k.5.03......
*spamApTask2: Apr 08 18:55:29.920: 000000c0: da 8e 38 a3 fc 72 17 4a 55 f9 19 62 f2 6a 4c 75 ..8..r.JU..b.jLu
*spamApTask2: Apr 08 18:55:29.920: 000000d0: 36 39 b7 11 39 71 d4 18 09 5f 00 99 10 67 07 a3 69..9q..._...g..
*spamApTask2: Apr 08 18:55:29.920: 000000e0: 27 4d b5 8d aa eb dd 4f 54 2a bc 27 52 3d d9 25 'M.....OT*.'R=.%
*spamApTask2: Apr 08 18:55:29.920: 000000f0: 70 63 e8 fb 4b 17 c5 84 b0 79 e2 0d 31 bc 36 3b pc..K....y..1.6;
*spamApTask2: Apr 08 18:55:29.920: 00000100: 75 a7 6e 9a 6c 7d 6c d4 9c 3e 0f 98 56 6b af 0a u.n.l}l..>..Vk..
*spamApTask2: Apr 08 18:55:29.920: 00000110: c4 46 d2 64 fe fb 26 d7 c1 9c 08 a1 e0 a6 04 81 .F.d..&.........
*spamApTask2: Apr 08 18:55:29.920: 00000120: fd 01 5e 0e d1 7e fa f5 b3 6d c8 6a ba c7 53 dd ..^..~...m.j..S.
*spamApTask2: Apr 08 18:55:29.920: 00000130: 11 a4 66 96 51 36 ce c5 9e 88 57 cd 90 6a 3b d8 ..f.Q6....W..j;.
*spamApTask2: Apr 08 18:55:29.920: 00000140: af 17 1e ab 96 9c 07 95 54 ed 51 0c 60 5e 9f 0b ........T.Q.`^..
*spamApTask2: Apr 08 18:55:29.920: 00000150: 0f c6 a5 a1 3d 8f 00 fd a4 38 23 88 3d e5 d9 31 ....=....8#.=..1
*spamApTask2: Apr 08 18:55:29.920: 00000160: c8 05 ee d2 46 ab 25 20 ea c2 a0 36 9e 53 c2 c1 ....F.%....6.S..
*spamApTask2: Apr 08 18:55:29.920: 00000170: 90 b7 15 ae 42 91 b6 85 77 55 8d 15 eb 97 3a 29 ....B...wU....:)
*spamApTask2: Apr 08 18:55:29.920: 00000180: e8 12 8b fe 75 6c c1 1b 4d e6 1f e4 f6 98 34 69 ....ul..M.....4i
*spamApTask2: Apr 08 18:55:29.920: 00000190: 03 72 ec 7f 46 02 0c 99 df ee f9 c3 17 b2 b7 bd .r..F...........
*spamApTask2: Apr 08 18:55:29.920: 000001a0: f0 cf 88 88 4d ec 4a d8 dd 6a 87 6a d1 ff 14 94 ....M.J..j.j....
*spamApTask2: Apr 08 18:55:29.920: 000001b0: fb b1 8a 24 e2 5c e4 2c ab 4d 64 ff 22 f6 f8 bc ...$.\.,.Md."...
*spamApTask2: Apr 08 18:55:29.920: 000001c0: 51 aa 04 6d 6b 95 5d cd 1e 6f 53 00 01 93 3a 75 Q..mk.]..oS...:u
*spamApTask2: Apr 08 18:55:29.920: 000001d0: 70 b3 05 bb c5 a6 f0 97 17 fd e9 35 45 a6 6e 42 p..........5E.nB
*spamApTask2: Apr 08 18:55:29.920: 000001e0: e3 cd 90 8b c2 84 dd 34 33 2a c7 72 11 74 a3 3d .......43*.r.t.=
*spamApTask2: Apr 08 18:55:29.920: 000001f0: e2 b6 28 f0 e4 23 0e 85 dd fa fc d2 4e d1 fc 9a ..(..#......N...
*spamApTask2: Apr 08 18:55:29.920: 00000200: c0 a0 c1 0c 3c 69 36 90 7d 17 ef 61 72 63 3b b1 ....
*spamApTask2: Apr 08 18:55:29.920: 00000220: 18 01 79 41 7a 88 4b c2 0f 2b 72 88 91 74 f6 5e ..yAz.K..+r..t.^
*spamApTask2: Apr 08 18:55:29.920: 00000230: 40 46 88 39 dc ca bf b3 3f a0 ef d5 c1 b3 32 51 @F.9....?.....2Q
*spamApTask2: Apr 08 18:55:29.920: 00000240: ff e1 33 84 97 26 f5 69 f5 fd 5f bd d7 df 16 e5 ..3..&.i.._.....
*spamApTask2: Apr 08 18:55:29.920: 00000250: 0c aa 6b 26 1f 50 77 ec 4d 26 03 97 1c b2 32 ae ..k&.Pw.M&....2.
*spamApTask2: Apr 08 18:55:29.920: 00000260: de 16 6c ef b3 b6 06 92 95 81 45 fc 39 ff 2f e8 ..l.......E.9./.
*spamApTask2: Apr 08 18:55:29.920: 00000270: 91 a4 cf 3c 71 99 ec 9b 0c b7 67 2b 61 d8 ba a7 ...
*spamApTask2: Apr 08 18:55:29.920: 00000290: 8f 02 e5 72 98 48 3a 6b 24 44 17 68 2c e5 e0 37 ...r.H:k$D.h,..7
*spamApTask2: Apr 08 18:55:29.920: 000002a0: 59 17 c3 f5 a2 ac 81 ee 5d d6 3c 4f 16 3e a6 45 Y.......].
*spamApTask2: Apr 08 18:55:29.920: 000002b0: a7 9f 63 c4 a5 e3 61 71 bb d5 7e cd d7 73 2e 0f ..c...aq..~..s..
*spamApTask2: Apr 08 18:55:29.920: 000002c0: 1d 44 03 52 33 29 05 42 dc 5e 09 70 05 19 bd 70 .D.R3).B.^.p...p
*spamApTask2: Apr 08 18:55:29.920: 000002d0: 3b 30 c8 1c bd cf a5 a9 85 95 b3 f3 d5 f8 85 32 ;0.............2
*spamApTask2: Apr 08 18:55:29.920: 000002e0: 55 87 63 99 7b 00 51 0a c2 9b 42 08 05 c9 d4 20 U.c.{.Q...B.....
*spamApTask2: Apr 08 18:55:29.920: 000002f0: e9 87 c7 86 49 57 68 89 3b 74 4a e2 3e db e9 0b ....IWh.;tJ.>...
*spamApTask2: Apr 08 18:55:29.920: 00000300: 5a b2 86 90 8b b7 39 e2 f9 8d 18 59 bd 4a 5c d1 Z.....9....Y.J\.
*spamApTask2: Apr 08 18:55:29.920: 00000310: 56 25 43 97 c3 a3 51 38 80 f3 89 21 e5 31 22 cb V%C...Q8...!.1".
*spamApTask2: Apr 08 18:55:29.920: 00000320: e4 e3 3b 62 07 61 88 78 ed e0 a5 00 7e 6f 1a 7e ..;b.a.x....~o.~
*spamApTask2: Apr 08 18:55:29.920: 00000330: 46 16 b4 1a e8 9c c2 bc 93 15 e5 95 ef 86 af 0a F...............
*spamApTask2: Apr 08 18:55:29.920: 00000340: 8d 85 d2 8c ad 2d 3b 13 fe 80 d9 78 cc 53 0f d2 .....-;....x.S..
*spamApTask2: Apr 08 18:55:29.920: 00000350: fc 08 a6 8a 93 54 0d 0e 2d f9 3e d9 d4 c8 b6 30 .....T..-.>....0
*spamApTask2: Apr 08 18:55:29.920: 00000360: 5e 3a 9f e8 21 77 78 e6 99 01 10 6e 43 f7 7c 90 ^:..!wx....nC.|.
*spamApTask2: Apr 08 18:55:29.920: 00000370: 55 36 f8 c3 6a 9e 7d 0b f7 95 8d d8 7c d0 66 62 U6..j.}.....|.fb
*spamApTask2: Apr 08 18:55:29.920: 00000380: 18 d4 25 5f 7b 65 3a c2 84 0f 80 9f 41 d9 da e5 ..%_{e:.....A...
*spamApTask2: Apr 08 18:55:29.920: 00000390: 99 dd fc 05 3b 7d 3f 33 cb 87 1b fa 4c d2 e9 f7 ....;}?3....L...
*spamApTask2: Apr 08 18:55:29.920: 000003a0: d1 f0 de b0 3b 29 df fb 3f d8 02 14 c9 bf 20 00 ....;)..?.......
*spamApTask2: Apr 08 18:55:29.920: 000003b0: 79 7e 4c 54 1f df e5 29 73 5c 31 9d 49 4a 8d 01 y~LT...)s\1.IJ..
*spamApTask2: Apr 08 18:55:29.920: 000003c0: 17 df 07 87 94 17 ff 69 25 59 18 0f a6 2d da 1f .......i%Y...-..
*spamApTask2: Apr 08 18:55:29.920: 000003d0: e4 ce 8c c1 f6 4a 45 d1 2d ec 48 f2 09 04 28 d0 .....JE.-.H...(.
*spamApTask2: Apr 08 18:55:29.920: 000003e0: 83 d5 b9 a8 86 71 af bf 49 c6 51 ce 63 9b ea 5a .....q..I.Q.c..Z
*spamApTask2: Apr 08 18:55:29.920: 000003f0: 5d 22 c6 f2 f3 88 65 77 55 64 1f e7 67 5d 97 7c ]"....ewUd..g].|
*spamApTask2: Apr 08 18:55:29.920: 00000400: 13 47 d6 2d 3f ce 7b d0 1d 71 26 30 a8 75 f7 0c .G.-?.{..q&0.u..
*spamApTask2: Apr 08 18:55:29.920: 00000410: 52 10 f9 c2 ee 8f 14 f5 e3 01 7d 0b a8 d2 39 7c R.........}...9|
*spamApTask2: Apr 08 18:55:29.920: 00000420: 84 1b 51 92 53 41 86 66 e5 63 26 00 92 f7 76 2f ..Q.SA.f.c&...v/
*spamApTask2: Apr 08 18:55:29.920: 00000430: d6 7f 60 ba d0 0a 9d c2 8e 85 72 95 02 4e c9 c5 ..`.......r..N..
*spamApTask2: Apr 08 18:55:29.920: 00000440: 1d 38 fc 96 4a 07 ff 33 d7 c4 2f 6b 7f 76 33 95 .8..J..3../k.v3.
*spamApTask2: Apr 08 18:55:29.920: 00000450: ab 5a f4 29 23 3e 59 8c a8 e8 86 52 9d fd af f4 .Z.)#>Y....R....
*spamApTask2: Apr 08 18:55:29.920: 00000460: 0c 47 50 92 3b 69 e7 52 26 20 65 35 f6 60 22 a4 .GP.;i.R&.e5.`".
*spamApTask2: Apr 08 18:55:29.920: 00000470: 68 2d e8 a0 9a 84 00 c4 76 99 22 78 f3 cc 58 07 h-......v."x..X.
*spamApTask2: Apr 08 18:55:29.920: 00000480: 64 59 ba f9 d3 2a a5 1b ed 66 cb d4 cf 55 fa 6e dY...*...f...U.n
*spamApTask2: Apr 08 18:55:29.920: 00000490: e3 69 87 2b 38 f1 0a e2 82 b5 cd 80 aa 85 ff 16 .i.+8...........
*spamApTask2: Apr 08 18:55:29.920: 000004a0: 16 71 75 21 e4 33 6b cb 9d 84 db e3 12 68 e0 6f .qu!.3k......h.o
*spamApTask2: Apr 08 18:55:29.920: 000004b0: 76 78 a6 12 45 e2 7a cc 5a 22 d7 40 30 13 69 cc vx..E.z.Z".@0.i.
*spamApTask2: Apr 08 18:55:29.920: 000004c0: 2e cb c4 e1 47 ef 27 45 16 28 53 60 56 e9 fd 44 ....G.'E.(S`V..D
*spamApTask2: Apr 08 18:55:29.920: 000004d0: e9 0e bf d8 d1 79 7e 14 68 f9 3b 4a 40 5d cf b1 .....y~.h.;J@]..
*spamApTask2: Apr 08 18:55:29.920: 000004e0: d5 d8 c7 a9 a8 ec 1c 3f 8f f6 09 19 be d0 b4 a5 .......?........
*spamApTask2: Apr 08 18:55:29.920: 000004f0: a8 9c 6d 2f 5a 3f 51 01 d1 af 7c 37 01 92 c7 8a ..m/Z?Q...|7....
*spamApTask2: Apr 08 18:55:29.920: 00000500: 54 3e 7e fa 78 95 30 d5 36 0e 69 72 b9 d5 ca 09 T>~.x.0.6.ir....
*spamApTask2: Apr 08 18:55:29.920: 00000510: 61 46 c6 46 1a 9f 2b 93 64 1b c0 52 0c 09 d4 e1 aF.F..+.d..R....
*spamApTask2: Apr 08 18:55:29.920: 00000520: 4b c8 05 6c 78 d1 bc e7 3b 14 51 bb 42 36 f5 c9 K..lx...;.Q.B6..
*spamApTask2: Apr 08 18:55:29.920: 00000530: 34 f9 22 12 6d 1a e7 3b c4 1c 9b 92 5d a3 3f ce 4.".m..;....].?.
*spamApTask2: Apr 08 18:55:29.920: 00000540: 0b be ad fb 3d 8d cd ac b2 d7 da ec 75 2f 2f 13 ....=.......u//.
*spamApTask2: Apr 08 18:55:29.920: 00000550: 2c 99 fe b2 c9 33 82 d5 c3 1f dd c6 b2 c5 39 73 ,....3........9s
*spamApTask2: Apr 08 18:55:29.920: 00000560: 50 9f 60 47 e1 10 3e 79 2c d9 9e b1 27 60 33 52 P.`G..>y,...'`3R
*spamApTask2: Apr 08 18:55:29.920: 00000570: c1 51 fe 0f 2f a6 56 d7 0d 64 38 02 62 a8 ca 41 .Q../.V..d8.b..A
*spamApTask2: Apr 08 18:55:29.920: 00000580: 3c 6c 50 8c 4d b9 b1 68 32 b2 80 16 25 62 02 1e
*spamApTask2: Apr 08 18:55:29.920: 000005a0: 12 90 dc ea 99 fe cd 9f 09 82 64 03 77 ..........d.w
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 No data to send
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:29.920: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Buffer length 1405, alloc_len 1409
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=2
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 seq_num 2 epoch 1con->rx_seq 1 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 1 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record length 1392
*spamApTask2: Apr 08 18:55:30.160: 00000000: 17 fe fd 00 01 00 00 00 00 00 02 05 70 53 44 9a ............pSD.
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1405
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 1352 bytes decrypted
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Buffer length 1357, alloc_len 1361
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=3
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 seq_num 3 epoch 1con->rx_seq 2 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 2 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 record length 1344
*spamApTask2: Apr 08 18:55:30.160: 00000000: 17 fe fd 00 01 00 00 00 00 00 03 05 40 05 b1 a7 ............@...
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1357
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 1295 bytes decrypted
*spamApTask2: Apr 08 18:55:30.160: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.214:57663
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection found! Acquiring lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Called... for connection 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Buffer length 93, alloc_len 97
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 record=ApplicationData epoch=1 seq=14307
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 handshake_done
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 seq_num 14307 epoch 1con->rx_seq 14306 con->rx_epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 con rx_seq_valid 255 rx_seq 14306 rx_epoch 1
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 record length 80
*spamApTask1: Apr 08 18:55:30.187: 00000000: 17 fe ff 00 01 00 00 00 00 37 e3 00 50 42 cf 76 .........7..PB.v
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Calling BIO_write! 0xa44b730, buflen 93
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 38 bytes decrypted
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Releasing lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.214:57663
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 DTLS connection found! Acquiring lock for 0xa44b730
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Called...
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Sending 77 bytes
*spamApTask1: Apr 08 18:55:30.187: 00000000: 17 fe ff 00 01 00 00 00 00 32 5d 00 40 8f e5 53 .........2].@..S
*spamApTask1: Apr 08 18:55:30.187: 00000010: 89 cf f9 aa 98 e1 0a 28 f8 dc 95 ed b4 83 87 3e .......(.......>
*spamApTask1: Apr 08 18:55:30.187: 00000020: 11 6e 31 3a 0c 18 a8 f7 fd 0f 6c de 10 85 5f d0 .n1:......l..._.
*spamApTask1: Apr 08 18:55:30.187: 00000030: bd 04 e9 7e 9e 88 f6 49 c5 bf 55 bb f7 f1 f4 b9 ...~...I..U.....
*spamApTask1: Apr 08 18:55:30.187: 00000040: 4c c7 35 3a bf 48 14 5c 28 f2 d6 04 ef L.5:.H.\(....
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 No data to send
*spamApTask1: Apr 08 18:55:30.187: 34:bd:c8:bf:54:20 Releasing lock for 0xa44b730
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.229:63353
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection found! Acquiring lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Called... for connection 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Buffer length 93, alloc_len 97
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 record=ApplicationData epoch=1 seq=22926
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 handshake_done
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 seq_num 22926 epoch 1con->rx_seq 22925 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 con rx_seq_valid 255 rx_seq 22925 rx_epoch 1
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 record length 80
*spamApTask2: Apr 08 18:55:30.295: 00000000: 17 fe ff 00 01 00 00 00 00 59 8e 00 50 28 ba e7 .........Y..P(..
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Calling BIO_write! 0xa44b4c8, buflen 93
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 38 bytes decrypted
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Releasing lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.229:63353
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 DTLS connection found! Acquiring lock for 0xa44b4c8
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Called...
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Sending 77 bytes
*spamApTask2: Apr 08 18:55:30.295: 00000000: 17 fe ff 00 01 00 00 00 00 54 09 00 40 ac 0b 58 .........T..@..X
*spamApTask2: Apr 08 18:55:30.295: 00000010: fd 18 4d 51 f3 13 92 85 47 ed 3f 8a 8f 6c 01 34 ..MQ....G.?..l.4
*spamApTask2: Apr 08 18:55:30.295: 00000020: 81 5e 84 11 82 67 08 1f 50 15 6e 97 02 07 d1 03 .^...g..P.n.....
*spamApTask2: Apr 08 18:55:30.295: 00000030: fa 08 18 a7 cd 57 19 bf f1 6a 2c 93 2c f2 ce a4 .....W...j,.,...
*spamApTask2: Apr 08 18:55:30.295: 00000040: 59 30 f3 57 86 0a 45 26 06 6c 44 f8 25 Y0.W..E&.lD.%
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 No data to send
*spamApTask2: Apr 08 18:55:30.295: 7c:95:f3:c0:3a:c0 Releasing lock for 0xa44b4c8
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection found! Acquiring lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Called... for connection 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Buffer length 109, alloc_len 113
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 record=ApplicationData epoch=1 seq=26003
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 handshake_done
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 seq_num 26003 epoch 1con->rx_seq 26002 con->rx_epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 con rx_seq_valid 255 rx_seq 26002 rx_epoch 1
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 record length 96
*spamApTask1: Apr 08 18:55:32.739: 00000000: 17 fe ff 00 01 00 00 00 00 65 93 00 60 9c ee d2 .........e..`...
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Calling BIO_write! 0xa44ad90, buflen 109
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 47 bytes decrypted
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Releasing lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 DTLS connection found! Acquiring lock for 0xa44ad90
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Called...
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Sending 77 bytes
*spamApTask1: Apr 08 18:55:32.739: 00000000: 17 fe ff 00 01 00 00 00 00 5d 45 00 40 71 04 53 .........]E.@q.S
*spamApTask1: Apr 08 18:55:32.739: 00000010: be 67 20 75 cf 11 8d 6b 8e c1 3f 34 e3 13 fb d9 .g.u...k..?4....
*spamApTask1: Apr 08 18:55:32.739: 00000020: b5 c4 55 a4 06 ed 4c c6 1a 67 31 44 50 21 75 24 ..U...L..g1DP!u$
*spamApTask1: Apr 08 18:55:32.739: 00000030: a2 af bf 1c 1b 4f d6 0e 09 f8 9f 3a 62 c6 70 93 .....O.....:b.p.
*spamApTask1: Apr 08 18:55:32.739: 00000040: d1 ae f2 37 f7 b0 53 db ff 41 74 45 d0 ...7..S..AtE.
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 No data to send
*spamApTask1: Apr 08 18:55:32.739: 88:75:56:1f:76:10 Releasing lock for 0xa44ad90
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Buffer length 1405, alloc_len 1409
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=4
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 seq_num 4 epoch 1con->rx_seq 3 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 3 rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record length 1392
*spamApTask2: Apr 08 18:55:32.882: 00000000: 17 fe fd 00 01 00 00 00 00 00 04 05 70 fa b1 c2 ............p...
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1405
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 1352 bytes decrypted
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.247:5264
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 DTLS connection found! Acquiring lock for 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Called... for connection 0xa457078
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Buffer length 1357, alloc_len 1361
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record=ApplicationData epoch=1 seq=5
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 handshake_done
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con->rx_seq_valid 255 con->rx_epoch 1 epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 seq_num 5 epoch 1con->rx_seq 4 con->rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 con rx_seq_valid 255 rx_seq 4 rx_epoch 1
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Got DTLS_RECORD_APPLICATION_DATA
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 record length 1344
*spamApTask2: Apr 08 18:55:32.882: 00000000: 17 fe fd 00 01 00 00 00 00 00 05 05 40 23 bb 50 ............@#.P
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Calling BIO_write! 0xa457078, buflen 1357
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 1295 bytes decrypted
*spamApTask2: Apr 08 18:55:32.882: 00:b0:e1:88:99:80 Releasing lock for 0xa457078
*spamApTask1: Apr 08 18:55:33.055: 88:75:56:1f:76:10 DTLS connection find by 0xb3701e with Local 192.168.1.3:5246 Peer 192.168.1.188:61114
老铁,能否加下微信交流一思科无线控制器的问题 ziyoufeix01
1540488497lcj 发表于 2020-4-8 17:31
AIR-OEAP1810-B-K9的话检查根据官网AP合规性,可以是USA 、Puerto Rico
麻烦将完整的show msglog共享一 ...
不会停止console口输出的命令,所以AP的消息截取不了,抱歉。
老铁,有QQ或者微信交流一下无线的问题可以吗?我微信为ziyoufeix01,谢谢老铁
本帖最后由 1540488497lcj 于 2020-4-8 23:24 编辑
你好,我怀疑这个问题中了如下这个Bug:Cisco does not support the ap1810 with the vWLC
1810 OEAP cannot join vWLC
CSCvb29354
Description
Symptom:
vWLC rejects the 1810 OEAP configuration request giving error that its unsupported platform:
*spamApTask1: xx:xx:xx:xx:xx:xx Unsupported Platform, Config Request Rejected
AP Name - APNAME
Conditions:
vWLC and 1810 OEAP
Workaround:
None
Further Problem Description:
Cisco does not support the ap1810 with the vWLC. This bug CSCvb29354 is a documentation bug, and it is marked Fixedin that this limitation is now docuumented.
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvb29354/?rfs=iqvred
AlexChan21895 发表于 2020-4-8 19:53
不会停止console口输出的命令,所以AP的消息截取不了,抱歉。
你好,我怀疑这个问题中了如下这个Bug:Cisco does not support the ap1810 with the vWLC
1810 OEAP cannot join vWLC
CSCvb29354
Description
Symptom:
vWLC rejects the 1810 OEAP configuration request giving error that its unsupported platform:
*spamApTask1: xx:xx:xx:xx:xx:xx Unsupported Platform, Config Request Rejected
AP Name - APNAME
Conditions:
vWLC and 1810 OEAP
Workaround:
None
Further Problem Description:
Cisco does not support the ap1810 with the vWLC. This bug CSCvb29354 is a documentation bug, and it is marked Fixedin that this limitation is now docuumented.
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvb29354/?rfs=iqvred
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
老铁,有QQ或者微信交流一下无线的问题可以吗?我微信为ziyoufeix01,谢谢老铁
AlexChan21895 发表于 2020-4-8 19:00
debug dtls all enable的LOG
*spamApTask2: Apr 08 18:55:29.856: openssl_shim_info_callback: ret_des ...
关键的log信息:
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Unsupported Platform, Config Request Rejected
AP Name - AP00B0.E188.0CC0
*spamApTask2: Apr 08 18:01:48.428: 00:b0:e1:88:99:80 Failed post decode processing of config status from 192.168.1.247:5264
bug信息:
1810 OEAP cannot join vWLC
CSCvb29354
Description
Symptom:
vWLC rejects the 1810 OEAP configuration request giving error that its unsupported platform:
*spamApTask1: xx:xx:xx:xx:xx:xx Unsupported Platform, Config Request Rejected
AP Name - APNAME
Conditions:
vWLC and 1810 OEAP
Workaround:
None
Further Problem Description:
Cisco does not support the ap1810 with the vWLC. This bug CSCvb29354 is a documentation bug, and it is marked Fixedin that this limitation is now docuumented.
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvb29354/?rfs=iqvred
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !
Rps-Cheers | If it solves your problem, please mark as answer. Thanks !





